Comadshome.com ads (fake) - Free Instructions
Comadshome.com ads Removal Guide
What is Comadshome.com ads?
Comadshome.com asks users to confirm they aren't robots only to deliver intrusive ads later

If you've been noticing Comadshome.com ads suddenly appearing on your device, don't worry – you can remove them easily enough. These ads primarily show up in web browsers like Google Chrome, Mozilla Firefox, and MS Edge on various operating systems, including Windows, macOS, and mobile devices running Android or iOS. To get rid of the ads for good, simply change some settings in your browser of choice.
Many people think Comadshome.com ads are the result of a computer virus. While it's true that adware[1] might be the root cause of browser redirects and increased ad activity, the real issue is allowing a malicious website to show push notifications without any restrictions. Therefore, removing push notifications can only be done manually, as we explain in more detail below.
| Name | Comadshome.com |
| Type | Push notifications, pop-ups, ads, scam |
| Distribution | After users click the “Allow” button within the prompt upon site entry |
| Symptoms | Pop-ups show up on a regular basis on the screen – these ads often include inappropriate, scam, phishing, or other similar content |
| Risks | Links from the site might cause you to go to harmful websites, which may result in malware infections, financial losses, or personal data exposure. |
| Removal | To prevent the site from displaying notifications to you, access the site permission section via your web browser settings – you can find more details below. We also recommend checking the system for adware with SpyHunter 5Combo Cleaner security software |
| Other tips | Delete web caches and other data from your browsers to protect your privacy and prevent information leaks – FortectIntego can quicken this process |
Fake messages used by scammers
Online scammers use schemes in which they present users with information that can be misinterpreted to help them achieve their goals. For example, by using unexpected redirect routes, crooks can catch people off guard, and better exploit them. When people land on Comadshome.com, they're immediately met with one of the following fake messages:
- Please tap Allow to continue
- Click “Allow” to start downloading
- Press “Allow” to verify, that you are not a robot
- Can't play this video! Perhaps your browser doesn't allow video playback. Please click the Allow button to watch the video
- If you are 18+, click Allow
- Click “Allow” to win a prize and get it in our shop!
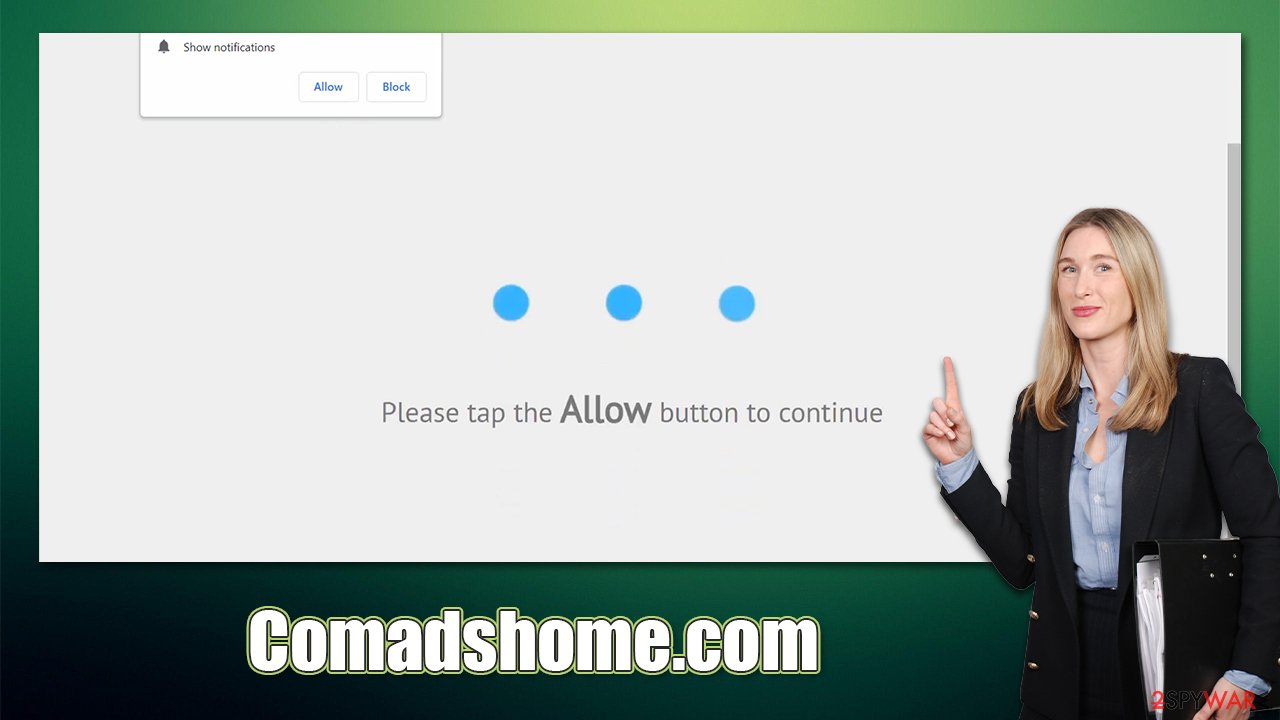
Because many users are already familiar with captchas and age-restricted sites, social engineering techniques used here can seem like nothing more than a hindrance that needs to be bypassed. The familiarity people have with these types of checks is one of the main benefits of using social engineering in this way.
As soon as users press the “Allow” button, they will permit Comadshome.com to deliver any kind of information via the push notification API[2] within the browser. Thus, as long as it is running, these messages can be delivered at any time without warning.
How users encounter malicious content online
Cybercriminals are fully conscious that very few individuals would deliberately access websites that might threaten their safety and the security of their computers. In fact, it is unlikely (but not inconceivable) to encounter a harmful website by using a search engine like Google or casually browsing sites deemed reputable.
When users go to websites with origins that can't be verified, problems occur. For example, people who want to get around paying for Windows or other software by finding cracks could end up on fraudulent sites and getting their computers infected with harmful malware – like ransomware. This would encrypt all personal files and then demand payment to decrypt them, resulting in serious damage to victims.
The adware problem
Adware might also force users to go to Comadshome.com or a related site. This type of software specializes in advertising, often at the cost of the app's functionality. As a result, people can be diverted to potentially dangerous or misleading websites, such as those specializing in push notification scams.
Since adware is often unknowingly installed on devices via software bundling[3] and other misleading means, many people may not realize it's there. SpyHunter 5Combo Cleaner and Malwarebytes are both excellent tools for removing adware – but first, you need to make sure that anti-malware is brought to the latest version.
We recommend scanning the computer with a repair and maintenance tool FortectIntego after removing any malware, as this can help fix system damage and remove leftover files. The app can also clear browser caches for better privacy and remove junk from the system.
Removal of Comadshome.com ads
To discontinue those pesky pop-up ads, you will need to go into the settings part of your internet browser. Although push notifications aren't themselves harmful, they might have links that are malicious based on the website they're coming from. That being said, anti-malware software wouldn't be able to find and get rid of them for you, so it's something you'll have to take care of yourself.
Therefore, access the settings section of the browser you are using, locate the Comadshome.com entry under the websites allowed to deliver push notifications, and block them as follows:
Google Chrome
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Google Chrome (Android)
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off position).
![Stop notifications on Chrome Android Stop notifications on Chrome Android]()
Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.
![Stop notifications on Edge Chromium Stop notifications on Edge Chromium]()
Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
![Stop notifications on Internet Explorer Stop notifications on Internet Explorer]()
- Locate the web address in question under Allowed sites and pick Remove.
How to prevent from getting adware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Adware. Investopedia. Source of financial content on the web.
- ^ Application Programming Interface (API). IBM. Cloud Learn Hub.
- ^ Bundled software. Computer Hope. Free computer help.






