Creeper ransomware (Virus Removal Guide) - Apr 2020 update
Creeper virus Removal Guide
What is Creeper ransomware?
Creeper ransomware – dangerous cryptovirus that demands a ransom in Monero
Creeper ransomware is a file locking malware which is a file-encrypting cyber infection, which seeks to lock personal files on victims' PC using a sophisticated AES encryption algorithm[1]. Initially discovered in early 2018, malware is not very prominent, although it comes back with new versions from time to time. Initially, malware appended .creeper or .crypton file extension to the encrypted data, although later attackers added .cripper, and, most recently, .rag2hdst to the list.
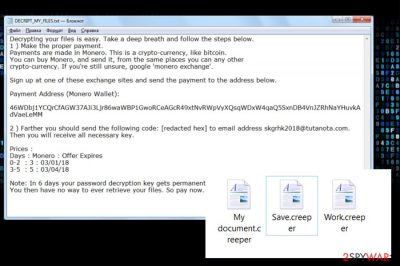
Once the Creeper virus encrypts all personal files on the computer, it also drops a ransom note DECRIPT_MY_FILES.txt or DECRIPT_FILES.txt, which demands to pay ransom for the decryption tool, which should be paid in Monero cryptocurrency, which sometimes reaches as much as $1,000. Attackers also provide contact email, which changed over time – the most recent one used is dfs20@keemail.me.
| Name | Creeper ransomware |
|---|---|
| Alternative names | Cripper ransomware |
| Type | Cryptovirus |
| Ransom note | DECRIPT_MY_FILES.txt; DECRIPT_FILES.txt |
| File extension | .creeper; .crypton, .cripper, .rag2hdst |
| Email address | skgrhk2018@tutanota.com, sqqsdr01@keemail.me, dfs20@keemail.me |
| Ransom currency | Monero |
| Elimination | Get rid of Creeper virus by running a full system scan with reputable anti-malware software |
| System fix | If you found Windows not to be working properly after malware removal, scan it with FortectIntego to fix system file damage |
Typically, hackers are requesting to send them a unique code that is indicated on a ransom note. The ransom message displayed by Creeper ransomware reads the following:
Decrypting your files is easy. Take a deep breath and follow the steps below.
1 ) Make the proper payment.
Payments are made in Monero. This is a crypto-currency, like bitcoin.
You can buy Monero, and send it, from the same places you can any other
crypto-currency. If you're still unsure, google 'monero exchange.'
Sign up at one of these exchange sites and send the payment to the address below.
Payment Address (Monero Wallet):
46WDbj1YCQrCfAGW37AJi3Ljr86waWBP1GwoRCeAGcR49xtNvRWpVyXQsqWDxW4qaQ5SxnDB4VnJZRhNaYHuvkAdVaeLeMM
2 ) Farther you should send the following code: *** to email address skgrhk2018@tutanota.com.
Then you will receive all necessary key.
Prices :
Days : Monero : Offer Expires
0-2 : 3 : 03/01/18
3-5 : 5 : 03/04/18
Note: In 6 days your password decryption key gets permanently deleted.
You then have no way to ever retrieve your files. So pay now.
In the text file, the ransomware does not indicate the particular amount of the ransom. The size of the redemption depends on how fast the victim reacts to the current situation. If the victim contacts the developers of the Creeper virus in two days or less, he or she will be asked to pay 3 Monero[2] coins, which is currently more than 800 USD. The price for those who respond within 3-5 days increases to 5 Monero coins, while the absolute deadline is six days. According to crooks, in 6 days the Creeper decryptor is permanently deleted.
All information related to this virus is originally written in English, so experts speculate that it's oriented to English-speaking users. Since English is a universal language, the prevalence of this crypto-extortionists is expected to be large.
Despite the fact that this file-encrypting virus is not yet decryptable, we strongly encourage you to remove Creeper using SpyHunter 5Combo Cleaner, Malwarebytes or another reputable anti-virus (also, we recommend using FortectIntego for virus damage fix). You should not pay the ransom due to two important reasons – money loss and future attacks. You can never know whether the felons creating ransomware virus are conscientious. They may not store a decryptor at all, so after transferring Monero, they may not send you a decryptor or send the one that is not working. Besides, paying the ransom is not a decent move as you will motive crooks to keep initiating their shady activities.
If you are not aware how to initiate Creeper removal or the ransomware keeps blocking your anti-virus continuously, you can follow the instructions provided at the end of this article. You will also find several alternative methods that can help you to decrypt files encrypted by Creeper virus.
Ransomware developers rely on the success of malspam campaigns
According to the latest reports, the usage of drive-by download attacks and exploit kits for ransomware distribution are falling since 2017.[3] Although some major attacks via RIG EK and other exploit kits have been revealed through the last year, the numbers are decreasing leaving malspam campaigns as the primary distributor of the file-encrypting virus.
However, the revelation of such a tendency does not mean that PC users can stop being careful with suspicious ads or start surfing on illegal and potentially dangerous websites. Precautionary measures have to be in mind all the time because hackers the old virus distribution methods are often refined coming back with the new strength.
One malware distribution strategy seems to be stable – that's spam emails. Hackers use various bots (Necurs most frequently) to disseminate tricky email messages with malicious email attachments. Such messages can mimic various authorities and indicate an attachment as invoice, report, or another official document. Usually, such attachments require to enable Macros and, if the potential victim, does that, he or she unintentionally activates the ransomware.
To protect yourself from similar cyber attacks, experts from virusi.bg[4] recommend you to keep a reputable anti-virus activated and update it regularly. Besides, avoid interaction with any content that looks suspicious to you. Although people often have a presentiment about email attachments or fake ads on the internet, curiosity often overcomes the fair of getting their PCs infected.
Learn how to remove Creeper virus quickly
Creeper removal can hardly be initiated without the assistance of the anti-virus tool. Unlike less dangerous viruses, ransomware is known for initiating multiple system's changes, including corruption of Registry Entries.
The problem is that you may not be able to remove Creeper virus with the help of an anti-virus. It may prevent the anti-malware tool from being launched and block the installation of a new one. In this kind of situation, you should initiate the steps that are given below.
Once you eliminate Creeper ransomware from the system, you should try to recover your files from Shadow Volume Copies, previous Windows version or use additional data recovery tools. Those who have file backups should skip data recovery steps and go ahead to the recovery from backups.
Getting rid of Creeper virus. Follow these steps
Manual removal using Safe Mode
Creeper removal can become a mission impossible if the virus blocks your anti-virus. If you are stuck on your PC with all the files encrypted, you should follow the steps below to reboot your PC into Safe Mode with Networking. This way, you should be able to run a scan with your anti-virus:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Creeper using System Restore
These steps apply for those who cannot launch anti-virus even when in Safe Mode with Networking or if they cannot access this mode:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Creeper. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Creeper from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.The methods that are given below can help you to recover files encrypted by Creeper ransomware.
If your files are encrypted by Creeper, you can use several methods to restore them:
Use Data Recovery Pro utility
Data Recovery Pro is a tool helping people to retrieve files after system's crash or accidental deletion. Nevertheless, it recovered millions of files encrypted by ransomware viruses, so it's worth giving a try:
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Creeper ransomware;
- Restore them.
Windows Previous Versions feature can recover the most important files
If you have enabled a Restore Point before Creeper virus attacked your PC, then you should try to recover the most important files with the following guide:
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Try ShadowExplorer
Once you remove Creeper ransomware, install ShadowExplorer and try to recover your files from Windows Shadow Volume Copies.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Creeper decryptor is not yet available
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Creeper and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Anand Mishra. How does RSA and AES differ?. Quora. Question and answer website.
- ^ Monero ransomware: new trend or test for delivery mechanism?. SocPrime. Security Quality Control.
- ^ Jake Doevan. The fall of Exploit Kits: RIG EK turns to cryptocurrency. 2-Spyware. Security and tech-related information.
- ^ Virusi. Virusi. Virus and Spyware news.





















