Crypt0r ransomware (Virus Removal Guide) - Decryption Steps Included
Crypt0r virus Removal Guide
What is Crypt0r ransomware?
Crypt0r ransomware – a new crypto malware string that implements EternalBlue exploit

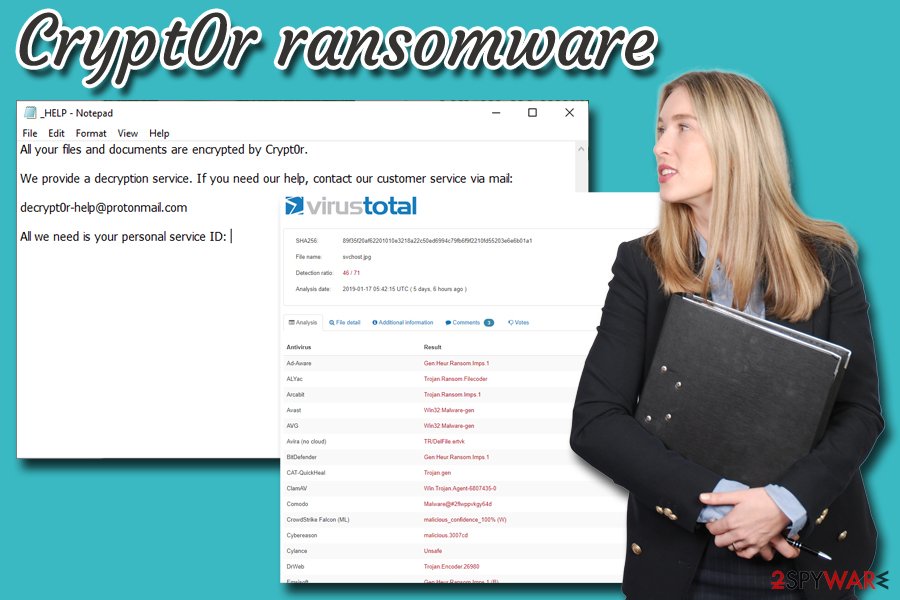
Crypt0r is a new ransomware family which was analyzed by Carbon Black security researchers.[1] According to researchers, the new strain of malware is relatively similar to the infamous WannaCry and NotPetya ransomware viruses because it has multiple similar functions, as well as implemented EternalBlue exploit. After performing multiple modifications to system files, Crypt0r ransomware scans the device for personal files, such as .jpg, .mp3, .avi, .html, .doc, .txt and many others. Once detected, the malware encrypts the data with the help of RSA and AES encryption algorithms and modifies files, making them unusable. To recover the access, victims are urged to contact cybercrooks via decrypt0r-help@protonmail.com – the email is included inside the ransom note _HELP.txt, which is dropped into each of the affected folders. Crypt0r virus uses a random generator for file extensions, for example, .qqjuBOaf, .2lwnPp2B, or .aqhATfjK.
| Name | Crypt0r |
| Type | Ransomware |
| Encryption algorithm | RSA and AES |
| Similar malware | WannaCry, NotPetya |
| Related files | crypt0r-mutex, notepad.vbs |
| File extension | Random combination of 8 characters |
| Ransom note | _HELP.txt |
| Contact | decrypt0r-help@protonmail.com |
| Elimination | Use security software like FortectIntego or SpyHunter 5Combo Cleaner |
In the first stages of the infection, Crypt0r ransomware copies notepad.vbs file into the Temp folder. It contains instructions written in Visual Basic script language and is later executed with the help of cmd.exe process, consequently removing Shadow Volume Copies. Due to this, users are unable to recover personal files after Crypt0r ransomware removal.
After system modification, Crypt0r ransomware contacts the C2[2] server with the help of eleven hard-coded .onion addresses via TOR network. It attempts to connect to the remote server in an endless loop until the connection is established, and then sends victim's ID and the encryption key to hackers.
Finally, Crypt0r virus drops a brief ransom note:
All your files and documents are encrypted by Crypt0r.
We provide a decryption service. If you need our help, contact our customer service via mail:
decrypt0r-help@protonmail.com
All we need is your personal service ID:
Experts do not recommend contacting cybercriminals, as they might simply ignore victims, even after the payment in Bitcoin or other cryptocurrency is transferred. Additionally, such act would prove Crypt0r ransomware authors that ransomware works, and it will consequently encourage them to produce more dangerous viruses.
Therefore, you should remove Crypt0r ransomware from your computer as soon as possible, and only then proceed with file recovery. You can use anti-malware software that is capable of detecting the threat – we recommend using FortectIntego pr SpyHunter 5Combo Cleaner.[3]
While there is a low chance of recovering your data without a personal key or backups, you can always try third-party software. Additionally, security researchers are always working on free decryptors, and new tools are being released for different ransomware viruses over time.
Lastly, Crypt0r ransomware is equipped with the EternalBlue MS17-010 exploit,[4] which was also used by WannaCry. Exploits allow cybercriminals to execute code remotely, so patching your software is essential.
Follow these simple tips if you want to protect your PC from ransomware viruses
Ransomware developers typically use multiple different distribution techniques to ensure the virus will affect as many victims as possible. Therefore, while browsing the internet, there are several things to look out for in order to avoid unwanted infections.
One of the best-known tactics to deliver ransomware is spam emails. Crooks often employ bots to send out thousands of phishing emails to potential victims. These messages either include a contaminated attachment or a malicious link. Therefore, be careful with all the emails from unknown sources – open them if you are sure they are legitimate.
Another ransomware distribution method which is becoming increasingly popular among cybercriminals is brute-force attacks. They use a preset list of most commonly used passwords and use a Remote Desktop Protocol to inject malware manually. Thus, use secure passwords an all your accounts, and also make use of a VPN.
Other tips would include:
- Employ anti-malware software and keep it up to date;
- Patch software as soon as updates are available;
- Avoid visiting high-risk sites, such as torrent, file-sharing, porn, gambling, etc.;
- Enable the ad-blocking plugin;
- Avoid internet connections that are not secured (HTTP instead of HTTPS).
Remove Crypt0r ransomware with the help of security software ASAP
Be aware that ransomware viruses can also travel with the help of backdoor- a specific malicious software that is created to download and install other malware, such as ransomware. For that reason, Crypt0r virus might be not the only infection present on your machine, which can result in personal information disclosure or even identity theft.
Thus, do not risk it and scan your device with reputable anti-virus software – it will be able to detect all the infections and remove Crypt0r ransomware in the process. Note that malware can hinder the operation of security application. In such a case, enter Safe Mode with Networking and perform Crypt0r ransomware removal from there.
Getting rid of Crypt0r virus. Follow these steps
Manual removal using Safe Mode
To remove Crypt0r virus from your device without disturbances, follow these steps to enter Safe Mode with Networking:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Crypt0r using System Restore
System Restore can also help you to get rid of the virus:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Crypt0r. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Crypt0r from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Crypt0r, you can use several methods to restore them:
Make use of Data Recovery Pro when trying to get files back
Initially, Data Recovery Pro is created to recover accidentally deleted or corrupted files. However, researchers noticed that it could sometimes help users whose data were affected by ransomware.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Crypt0r ransomware;
- Restore them.
Windows Previous Versions feature might be useful
The method requires you to have System Restore enabled (before the infection), and it can also restore individual files, so recovery of large amounts of data might be impossible.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Try ShadowExplorer when trying to recover files encrypted by Crypt0r
As we mentioned above, ransomware performs Shadow Volume removal upon infiltration. However, the virus might fail to do so. Then ShadowExplorer will be able to recover all of your data.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No decryptor is available yet
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Crypt0r and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ TAU Threat Intelligence Notification – Crypt0r Ransomware. Carbon Black. Security researchers.
- ^ Kashinath T. Command And Control Servers : Things You Should Know. SecPod. Endpoint Security and Management Platform.
- ^ 89f35f20af62201010e3218a22c50ed6994c79fb6f9f2210fd55203e6e6b01a1. Virus Total. File and URL scan engine.
- ^ Microsoft Security Bulletin MS17-010 - Critical. Microsoft. Docs.





















