CXK-NMSL ransomware (Free Instructions) - Improved Guide
CXK-NMSL virus Removal Guide
What is CXK-NMSL ransomware?
CXK-NMSL ransomware – a ransom-demanding virus that aims to eliminate a big number of data files instead of encrypting them

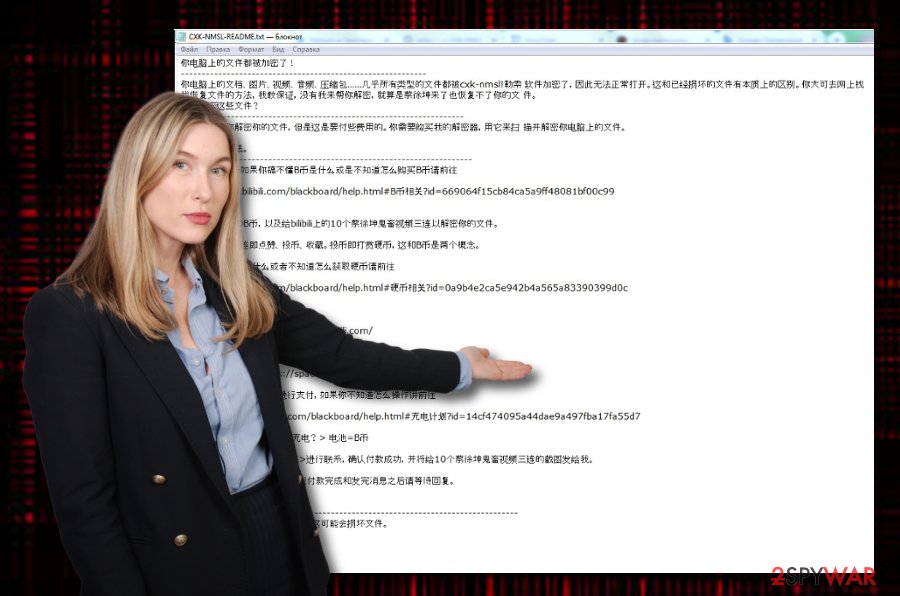
CXK-NMSL ransomware, also described as ChineseBAT ransomware, is a notorious malware string that tends to delete files rather than locking them because of an error in the encryption code. The cyber threat targets Chinese or Chinese-speaking people regarding the CXK-NMSL-README.txt ransom message which is written in the Chinese language. Once CXK-NMSL virus enters the Windows system, it might modify the hosts file,[1] insert hazardous keys into the Windows Registry and Task Manager sections. Afterward, the corrupted encryption process will begin and those files which did not get deleted will end up with the .cxk_nmsl appendix. Furthermore, the criminals will pass ransom demands through the text message and urge for 100 BTC which needs to be transferred via the Bilibili platform.
| Name | CXK-NMSL ransomware |
|---|---|
| Alternative name | ChineseBAT ransomware |
| Detection names | AV engines detect this bogus malware strain by these names: Trojan.BAT.Ransom.C (BitDefender), BAT.Encoder.82 (DrWeb) |
| Appendix | Once the malware infiltrates the system and launches its generated encryption algorithms, all touched files are locked by adding the .cxk_nmsl appendix to each filename |
| About the encryption | Even though this ransomware strain aims to encrypt all files that are found on the system, it deletes a big number of data instead of locking it due to a bug in the encryption key |
| Target(s) | According to the written information in the ransom note, CXK-NMSL virus targets people from China or those who speak in the Chinese language |
| Ransom message | It is known that the malware provides users with the CXK-NMSL-README.txt ransom note and places a copy of it on the desktop and one in each folder that contains corrupted files |
| Demanded price | This time crooks are very greedy – they demand a price of 100 BTC be transferred via the Bilibili platform in order to bring files back to their primary states |
| Related files | The ransomware brings CXK-NMSL.bat and CXK-NMSL-README.txt .exe files to the system. It also might add bogus products to the Windows Registry/Task Manager |
| Related malware | According to some research, CXK-NMSL ransomware might have some relations with ExpBoot but it is not yet officially approved |
| System scanning | Use FortectIntego as additional optimization software to perform a thorough system check-up and detect components that might be hiding in your Windows OS system after the malware attack |
According to cybersecurity experts, there might be some relation strings between CXK-NMSL ransomware and ExpBoot ransomware. However, due to the fact that there are no particular details about the similarity between these two viruses, their relation still remains just speculation between Internet security specialists.
CXK-NMSL ransomware will supposedly hide several malicious entries and keys on your Windows computer system after it secretly invades your computer system. Malware-laden content is known to be usually hidden somewhere on the Desktop, User_folders, or % TEMP% folders. For example, the ransom message often is placed on the desktop and a single copy is also planted in each folder that holds encrypted/corrupted data.
In addition, CXK-NMSL ransomware brings two bogus files named CXK-NMSL.bat and CXK-NMSL-README.txt .exe to the Windows operating system. All processes are related and some of them even allow the malware to boot itself automatically within each time when the user accesses his/her Windows machine.
Continuously, if the ransomware virus[2] aims to corrupt the Windows hosts file, you will need to eliminate it when performing CXK-NMSL ransomware removal, otherwise, you will receive blocked access to various websites and networks that are related to cybersecurity, for example, offer to purchase strong antivirus software.
Despite all of these activities, CXK-NMSL ransomware might carry and bring additional malware to the system. Malware often comes more than one in a package as the more the better (for developers only, of course). Various Trojan horses, worms, and similar parasites might end up on your system if you do not take proper care of the ransomware.
To remove CXK-NMSL ransomware safely and effectively, you will have to employ reliable antimalware tools. However, before reaching for the elimination, you should complete a thorough system scan with a tool such as FortectIntego. The scan results will provide you with a list of infected directories and show which places in your system need cleaning.
In addition, ransom demands that are placed by CXK-NMSL ransomware spreaders should not be fulfilled. Regarding the fact that the criminals urge for a huge price (100 BTC), you might lose a big sum of money for completely nothing. We state this fact as it is widely known about ransom-demanding crooks that tend to scam their victims at the end.
Major companies all around the world suffer from ransomware; some ransoms are agreed to be paid
Ransomware is a wide category that included numerous file-encrypting and ransom-demanding threats in its database. News reports about a new ransomware attack are released every week and seem to alert the lack of cybersecurity that later on affects numerous employers, employees, customers/clients, and random users.
Various news sources rushed to release their reports about Sodinokibi ransomware attacking multiple dental health-based offices in the United States this summer. This dangerous malware string manages to lack a big amount of important data and it had to be restored somehow. Regarding the fact that the platform that was responsible for protecting the clients failed to do its job, the official provider PercSoft agreed to pay the ransom in exchange for the decryption software.
Some decide to pay the demanded price as very important data might be in the hands of criminals, some deny the crooks' urges, and some even try to negotiate the ransom terms and conditions. For example, when bad actors hacked a large network of computers New Bedford city in Massachusetts and demanded to be paid $5.3 million for decryption, the city offered them $400K. However, the hackers declined the offer and were left with nothing.
Protect your personal files and valuable information
A ransomware attack can hit anyone and especially those who are careless with their online activities and drop personal files anywhere or just leave it on their primary computer. Our suggestion would be to always store backups of important data in case of a malware incident.
There are many ways to keep your data secured. For example, you can purchase a USB drive and store copies of important files there. However, make sure to keep the devices unplugged when it is out of usage, otherwise, the ransomware might still reach your files if the drive is kept connected during the attack.
In addition, you can use some data-storing services such as iCloud and Dropbox where you can also keep your personal files. At least, keep valuable documents on more than one computer so if one gets infected, the others will supposedly remain safe.
Hacked RDP, vulnerable networks, email spam, and exploit kits – ransomware residence place
Technology experts from Virusai.lt[3] state that there is more than one way how ransomware might have reached your computer system. However, the most popular ways for this malware to enter the computer system are:
- Hacked RDP (for example, TCP port 3389);
- Exploit kits;[4]
- Vulnerable networks (p2p sites such as The Pirate Bay);
- Email spam messages.
Some good news is that there are effective ways to protect yourself from ransomware attacks. First of all, ensure that you are running a reliable antimalware program on your computer and it includes as many protective features as possible. Continuously, avoid all websites that are marked as unsafe or give you a concerning feeling.
In addition, always sort out your received emails. Messages that fall into your spam section or were not expected to be received should be eliminated together with all of their attachments. Criminals like to fake senders from FedEx, DHL, and other shipping companies and pretend to send shipment information via an infected attachment or hyperlink.
Removal possibilities for CXK-NMSL ransomware
If you have been searching for manual ways how to remove CXK-NMSL ransomware, you should forget it as this type of removal is not possible in this case. Ransomware viruses come to complex and might leave hazardous products all over your Windows computer system.
Discover malicious entries and keys with tools such as FortectIntego, SpyHunter 5Combo Cleaner, or Malwarebytes. Once the program is finished, it will show you all the locations that were infected by CXK-NMSL ransomware. Later on, you can employ automatical software and complete the entire elimination process by preventing yourself from making crucial mistakes.
After the CXK-NMSL ransomware removal is finished, you should go and one more time review all the prevention and safety tips that we have written. Knowing how to protect yourself, important data, and your computer system will bring you the best success of avoiding similar malware attacks throughout the upcoming future.
Getting rid of CXK-NMSL virus. Follow these steps
Manual removal using Safe Mode
Activate Safe Mode with Networking to disable all malicious changes that were performed during the active period of CXK-NMSL ransomware virus
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove CXK-NMSL using System Restore
Boot up with System Restore to deactivate all bogus modifications and processes. If you do not know how to do that, follow the below-provided lines
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of CXK-NMSL. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove CXK-NMSL from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by CXK-NMSL, you can use several methods to restore them:
Try Data Recovery Pro to restore some data
If the ransomware virus has encrypted, corrupted, or deleted your files, there is a chance that you would be capable of recovering some individual components with the help of this software
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by CXK-NMSL ransomware;
- Restore them.
Activate Windows Previous Versions feature for file restoring
Make sure that you have enabled System Restore before using this tool. Afterward, use the software to bring some of your data back to its starter position
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Shadow Explorer might help you with data recovery
Before using this tool, you have to make sure that the ransomware virus did not eliminate Shadow Volume Copies of your locked/deleted files. If the Shadow Copies remain safe, use the following instructions for employing this software
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Currently, there is no official decryptor released for .cxk_nmsl files
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from CXK-NMSL and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ hosts (file). Wikipedia. The free encyclopedia.
- ^ Margaret Rouse. Ransomware. Search Security. Tech Target.
- ^ Virusai.lt. Virusai.lt. Spyware news.
- ^ What is an Exploit Kit?. Palo Alto Networks. Cybersecurity.





















