DataBankasi ransomware (virus) - Recovery Instructions Included
DataBankasi virus Removal Guide
What is DataBankasi ransomware?
DataBankasi ransomware infection can result in permanent data loss if there are no backups
DataBankasi ransomware is a file-locking virus that can use complicated encryption algorithms to lock users' personal files, like photos, videos, and documents. The main goal of cybercriminals is to get paid for a decryption key.[1] If users do not have backups, it is almost impossible to get the data back.
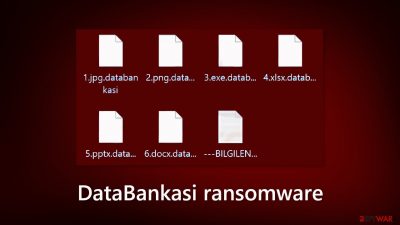
When ransomware infiltrates the system, the affected files are appended with the .databankasi extension. If a file was previously named picture.jpg, after encryption it would look like this picture.jpg.databankasi. The icons are also changed to white pages and the files become impossible to open.
| NAME | DataBankasi |
| TYPE | Ransomware, cryptovirus, data locking malware |
| DISTRIBUTION | Email attachments, peer-to-peer file sharing platforms, malicious ads |
| FILE EXTENSION | .databankasi |
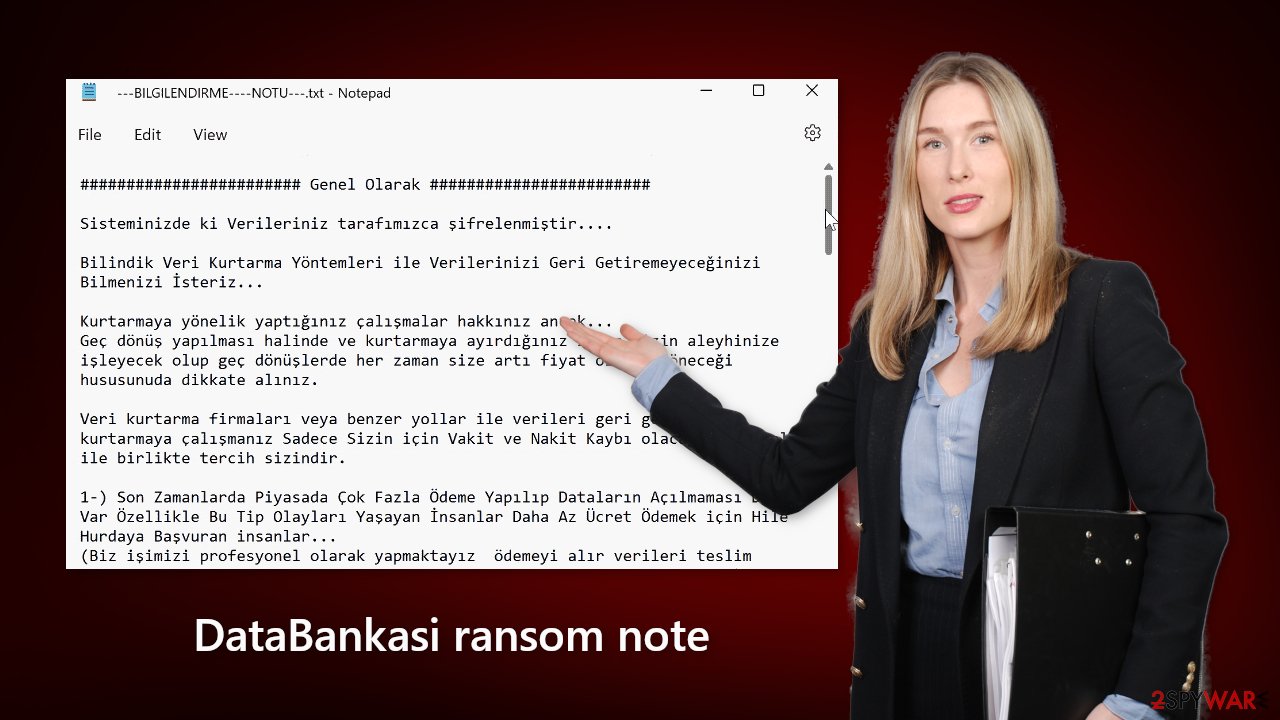
| RANSOM NOTE | —BILGILENDIRME—-NOTU—.txt |
| FILE RECOVERY | It is nearly impossible to recover the files if you do not have backups; we provide a third-party solution that has helped some users |
| MALWARE REMOVAL | Scan your machine with anti-malware software to eliminate all the malicious files |
| SYSTEM FIX | Windows reinstallation can be avoided with FortectIntego maintenance tool, which can fix damaged files, system errors, and more |
The ransom note
DataBankasi ransomware generates a ransom note —BILGILENDIRME—-NOTU—.txt on the machine:
######################## Genel Olarak ########################
Sisteminizde ki Verileriniz tarafımızca şifrelenmiştir….
Bilindik Veri Kurtarma Yöntemleri ile Verilerinizi Geri Getiremeyeceğinizi Bilmenizi İsteriz…
Kurtarmaya yönelik yaptığınız çalışmalar hakkınız ancak…
Geç dönüş yapılması halinde ve kurtarmaya ayırdığınız zaman sizin aleyhinize işleyecek olup geç dönüşlerde her zaman size artı fiyat olarak döneceği hususunuda dikkate alınız.Veri kurtarma firmaları veya benzer yollar ile verileri geri getirmeye – kurtarmaya çalışmanız Sadece Sizin için Vakit ve Nakit Kaybı olacağı kesin olmak ile birlikte tercih sizindir.
1-) Son Zamanlarda Piyasada Çok Fazla Ödeme Yapılıp Dataların Açılmaması Durumu Var Özellikle Bu Tip Olayları Yaşayan İnsanlar Daha Az Ücret Ödemek için Hile Hurdaya Başvuran insanlar…
(Biz işimizi profesyonel olarak yapmaktayız ödemeyi alır verileri teslim ederiz.Hiç Bir Zaman ödemesi alınmış bir veriyi açmamazlık yapmayız….)
bu açıklamayı mail ile dönüş yaparken net ve dürüst olmanızı beklediğimi iletmiş için yazdım. Unutmayın net ve dürüst yaklaşımlar işinizi kolaylaştırcaktır
Güven Konusunda ise, Daha Önce Şifrelediğim ve Verilerini Açtığım Bir Firmayı Referans Gösterebilirim Yada dilerseniz Örnek Dosya Çözümü Yapabiliriz….2 -) Yine istediğiniz Data Kurtarma Firmasına Gitmekte Özgürsünüz Bir Çoğu Hackerlarla Çalışyor.
Ama Ben Çalışmıyorum Data Kurtarma Firmalarına Giden Müşterilerin Verileri için Ekstra Ücret talep ettiğimi de bilmenizi isterim….3-) Yukarıda Bahsettiğim Sorunları Yaşamamak Adına Fake Mailler Açarak Bize Mail Atmayınız Cevap Vermiyoruz Firma Mailleri Dışından Gelen Hiç bir Mail Cevaplanmamaktadır.
4- ) Sizi Tanımıyorum, Dolayısıyla Size Karşı Kötü Duygular Beslememin Size Kötülük Yapmamın peşinde değiliz
işimiz ticaret olarak görüyoruz paramızı alırız verileri teslim ederiz tamamen profesyonel olarak Bu İşten Bir Gelir Elde Etmekteyiz.
Yaptığınız Ödeme Sonrasında En Kısa Zamanda Verilerinizi Eski Haline Getirmek İçin Decrypter ( Şifreli Dosyaları Çözme ) Programını Gönderiyorum…Aşağıdaki Referans Kodunuzla Birlikte Verilerinizi Almak isterseniz Lütfen SAAT 11:00 a Kadar Mail Atınız
Yinede Veri Kurtarma Firmaları, data kurtarma girişimleriniz veya Programları Denemek isterseniz Lütfen Dosyaların Aslı üzerinde Değil Bir Yere Kopyalayıp Onlar Üzerinde Deneme Yapınız.
Aksi halde bozulan dosyalardan siz sorumlu olursunuz.######################## Benimle iletişime Geçtiğinizde Dikkat Etmeniz Gerekenler ########################
1-) Size teklif ettiğimiz tutarın Üzerine Pazarlık Yapmayınız dikkate almadığınız gibi ısrarcı olunması halinde ekstra ekleme yapmaktayız.
Özetle bir siz değilsiniz Her Gün Onlarca iş yapmaktayız ve pazarlık için ayıracak vaktimiz de yoktur.2-) Yine bir Saat Öncesinin Yedeği Var bir Hafta Öncesinin Yedeği Var Gibi söylemler ile indirim vs talep etmeyiniz varsa böyle bir durum yedeğinizi kurun ve devam edin
bu gibi durumlara fiyat konusunda indirime konu olmamakla birlikte katiyen pazarlığa konu edilemez.3-) Çokça karşılaştığımız bizimle iletişime geçmek yerine Sağa Sola datanızı Kurtarırım Diyenler ile iletişim kurup üç beş gün sonra çözüm bulamadan en son bize gelmeniz sizin aleyhinize olacaktır,
gecikmeler size artı maliyet olarak yansıyacağı hususunu da dikkate alınız. Sıklıkla karşılaştığımız bir konuda,
Bir çok data kurtarmacı sizden aldığı bilgiler ile bize ulaşmaktadır ve size Vereceğimiz ücrete onlara veriyoruz onlarda üzerine koyup tekrar size veriyor 🙂
Biz kesinlikle firma veya kurum yetkili dışında kimseyle pazarlık yapmıyoruz ve veri teslimi yada veri açma yapmıyoruz..
Yine bu gibi girişimleriniz sonunda gelirseniz Ücretiniz talep ettiğim tutarın üstünde olacağını bilmenizi isteriz.4-) Zamanında net ve dürüst bir şekilde Gelip duygu sömürüsü gibi boş talepler ile değil de tam bir profesyonel gibi gelirseniz bizde size karşı gerekli hassasiyeti ve
profesyonelce ticaretimizi biri birimizi üzmeden tamamlarız. Bunu dışında mazeret mali gerekçe vb istekler ile indirim talebinde bulunmayınız,
bu gibi gerekçeleri kesinlikle dikkate almıyoruz işimizi duygularımızla yürütmüyoruz 10 yıllık tecrübemiz ile artık bu gibi durumlara pirim vermemekteyiz…5-) Bize ulaşırken Şirket Maili Dışında Mail göndermeyiniz dikkate almamaktayız. Nedeni ise Bir Çok Data Kurtarma Firması ve Verilerini Çözdüğünü iddia Eden Dolandırıcılar sizden aldıkları bilgiler ile
(Özellikle Youtube Üzerinden) Fake Mailler Açıp bize ulaşıyorlar ve sizden para alarak ortadan kaybolmaktadırlar.Bu yüzden sadece şirket maillerinden gelen yada sizin olduğunuza emin olduğumuz mail adreslerinden gelen iletilere cevap vermekteyiz.
Son olarak data kurtarmacılara ulaşsanız dahi onlar da verileri bizden talep etmektedirler bir nevi aracılıktan öte bir misyonları olmadığı gibi
son zamanlarda dolandırıcılık aracı olmuştur. Bizimle direk iletişime geçmeniz net ve profesyonelce yaklaşımınız işleminizin çok hızlı bir şekilde hatta gün içinde çözülmesini mümkün kılar.=> REFERANS KODUNUZ <=
–
=> MAİL ADRESİMİZ <=databankasi@mail.ru
databankasi@mail.ruYedek Email Adresimiz (Yukardakinden Cevap Alamadığınız Durumlarda)
databankasi@techmail.info######################## Bu Kısım Data Kurtarma Firmalarına Özel Nottur ########################
Yıllarca Sırtımızdan Para Kazandınız Kurtarmadığınız Verileri Kurtarıyormuş Gibi Lanse Ettiniz Bu Saatten Sonra Hiçbirinizle Çalışmıyorum…
Fake Mailler Açıp iletişime Geçemeyin Yakalarsam Anlarsam Firmalara İfşa Ederim
The ransom note is written in Turkish which may indicate that the threat actors are from Turkey. They want to get paid for a decryption key but the ransom amount is not specified. It depends on how fast victims contact them. They do not want to negotiate and are not interested in people's financial situation.
Ransomware developers always want to get paid in cryptocurrencies[2] because they provide anonymity. However, we strongly advise against contacting the threat actors because they cannot be trusted. Many previous ransomware attack victims say that they never received the promised decryption tools after paying.
Although it is almost impossible to get the data back without the key that only cybercriminals hold, it is a huge risk. You may lose your files and your money. First, we recommend trying third-party recovery solutions that help in some cases. You will find instructions on how to use them below.
Distribution methods
Most people get infected with ransomware by installing “cracked” software[3] from Torrent websites, and peer-to-peer file sharing platforms.[4] This activity is illegal so these platforms are unregulated. It is impossible to know if the packages you are downloading do not contain any malicious files.
It is best to use official web stores and developer websites for software installations. It may get costly, but you may save in the long run by keeping your system running smoothly. Besides, there are plenty of free apps to choose from so you should find something that suits your needs.
Another popular method used by cybercriminals is email. They use social engineering skills to create convincing letters that look like urgent messages from well-known companies. They include infected attachments or malicious links. That is why it is better to never open attachments from unknown senders.
Most importantly, keep your operating system and software updated. Hackers can use software vulnerabilities to deliver their malicious programs. Software developers regularly release security patches, They should be installed as soon as they come out to protect your system.
How to deal with ransomware?
If you try to recover your data first, it can result in permanent loss. It can also encrypt your files the second time. It will not stop until you remove the malicious files causing it first. You should not attempt removing the malicious program yourself. Use anti-malware tools like SpyHunter 5Combo Cleaner or Malwarebytes to scan your system.
This security software should find all the related files and entries and remove them automatically for you. Automatic removal is the best option because there is less risk of leaving some of the traces behind. Malware could prevent you from using antivirus software by turning it off. In that case, you should proceed with accessing Safe Mode first:
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.
![Windows XP/7 Windows XP/7]()
Windows 10 / Windows 8
- Right-click on Start button and select Settings.
- Scroll down to pick Update & Security.
![Update & Security Update & Security]()
- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.
![Recovery Recovery]()
- Select Troubleshoot.
![Choose an option Choose an option]()
- Go to Advanced options.
![Advanced options Advanced options]()
- Select Startup Settings.
![Startup settings Startup settings]()
- Click Restart.
- Press 5 or click 5) Enable Safe Mode with Networking.
![Press F5 to enable Safe Mode with Networking Press F5 to enable Safe Mode with Networking]()
File recovery using third-party software
Only hackers hold the decryption key, which can unlock your files, so if you did not back them up previously, you possibly lost your files forever. You can try using data recovery software, but third-party programs cannot always decrypt the files. We suggest at least trying this method. Before proceeding, you have to copy the corrupted files and place them in a USB flash drive or another storage. And remember – only do this if you have already removed DataBankasi ransomware.
- Download Data Recovery Pro.
- Double-click the installer to launch it.
![DataBankasi ransomware DataBankasi ransomware]()
- Follow on-screen instructions to install the software.
![Install program Install program]()
- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders where you want the files to be recovered from.
![Select what to recover Select what to recover]()
- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.
![Select Deep scan Select Deep scan]()
- Press Scan and wait till it is complete.
![Scan Scan]()
- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.
![Recover files Recover files]()
The operating system is left damaged after an attack
Performance, stability, and usability issues, to the point where a full Windows reinstall is required, are expected after malware infection. These types of infections can alter the Windows registry database, damage vital bootup, and other sections, delete or corrupt DLL files, etc. Once a system file is damaged by malware, antivirus software is not able to repair it.
This is why FortectIntego was developed. It can fix a lot of the damage caused by an infection like this. Blue Screen errors, freezes, registry errors, damaged DLLs, etc., can make your computer completely unusable. By using this maintenance tool, you could avoid Windows reinstallation.
- Download the application by clicking on the link above
- Click on the ReimageRepair.exe
![Reimage download Reimage download]()
- If User Account Control (UAC) shows up, select Yes
- Press Install and wait till the program finishes the installation process
![Reimage installation Reimage installation]()
- The analysis of your machine will begin immediately
![Reimage scan Reimage scan]()
- Once complete, check the results – they will be listed in the Summary
- You can now click on each of the issues and fix them manually
- If you see many problems that you find difficult to fix, we recommend you purchase the license and fix them automatically.
![Reimage results Reimage results]()
Getting rid of DataBankasi virus. Follow these steps
Isolate the infected computer
Some ransomware strains aim to infect not only one computer but hijack the entire network. As soon as one of the machines is infected, malware can spread via network and encrypt files everywhere else, including Network Attached Storage (NAS) devices. If your computer is connected to a network, it is important to isolate it to prevent re-infection after ransomware removal is complete.
The easiest way to disconnect a PC from everything is simply to plug out the ethernet cable. However, in the corporate environment, this might be extremely difficult to do (also would take a long time). The method below will disconnect from all the networks, including local and the internet, isolating each of the machines involved.
- Type in Control Panel in Windows search and press Enter
- Go to Network and Internet

- Click Network and Sharing Center

- On the left, pick Change adapter settings

- Right-click on your connection (for example, Ethernet), and select Disable

- Confirm with Yes.
If you are using some type of cloud storage you are connected to, you should disconnect from it immediately. It is also advisable to disconnect all the external devices, such as USB flash sticks, external HDDs, etc. Once the malware elimination process is finished, you can connect your computers to the network and internet, as explained above, but by pressing Enable instead.
Report the incident to your local authorities
Ransomware is a huge business that is highly illegal, and authorities are very involved in catching malware operators. To have increased chances of identifying the culprits, the agencies need information. Therefore, by reporting the crime, you could help with stopping the cybercriminal activities and catching the threat actors. Make sure you include all the possible details, including how did you notice the attack, when it happened, etc. Additionally, providing documents such as ransom notes, examples of encrypted files, or malware executables would also be beneficial.
Law enforcement agencies typically deal with online fraud and cybercrime, although it depends on where you live. Here is the list of local authority groups that handle incidents like ransomware attacks, sorted by country:
- USA – Internet Crime Complaint Center IC3
- United Kingdom – ActionFraud
- Canada – Canadian Anti-Fraud Centre
- Australia – ScamWatch
- New Zealand – ConsumerProtection
- Germany – Polizei
- France – Ministère de l'Intérieur

If your country is not listed above, you should contact the local police department or communications center.
How to prevent from getting ransomware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Key (cryptography). Wikipedia, the free encyclopedia.
- ^ James Royal. What Is Cryptocurrency? Here’s What You Should Know. NerdWallet. Investing Guides and Tips.
- ^ Georgina Torbet. 5 Security Reasons Not to Download Cracked Software. Makeuseof. Technology Blog.
- ^ Andrew Kalafut. A study of malware in peer-to-peer networks. ResearchGate. Scientific Papers.





















