Eqew ransomware (virus) - Recovery Instructions Included
Eqew virus Removal Guide
What is Eqew ransomware?
Eqew ransomware is a dangerous virus that locks users' personal files unless a ransom is paid
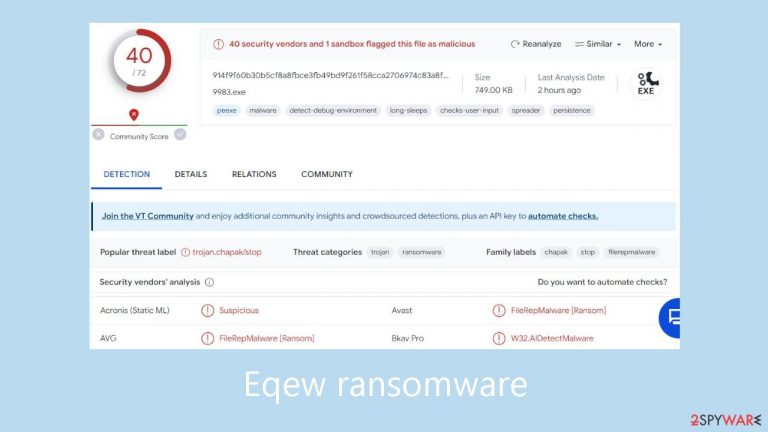
Eqew ransomware is a malicious computer virus designed to coerce users into paying money by locking their data. This specific attack uses software cracks and other illegal tools to target Windows computers. After gaining access to the system, the malware encrypts all user data using a powerful RSA encryption and appends the .eqew file extension for identification.
Although the data is not permanently damaged by this encryption method, access is blocked unless a special key that functions similarly to inputting a password is supplied. To guarantee that every victim receives a specially created key, the malware makes use of an online identity system. As a result, obtaining files without the appropriate decryption software turns into a very difficult task.
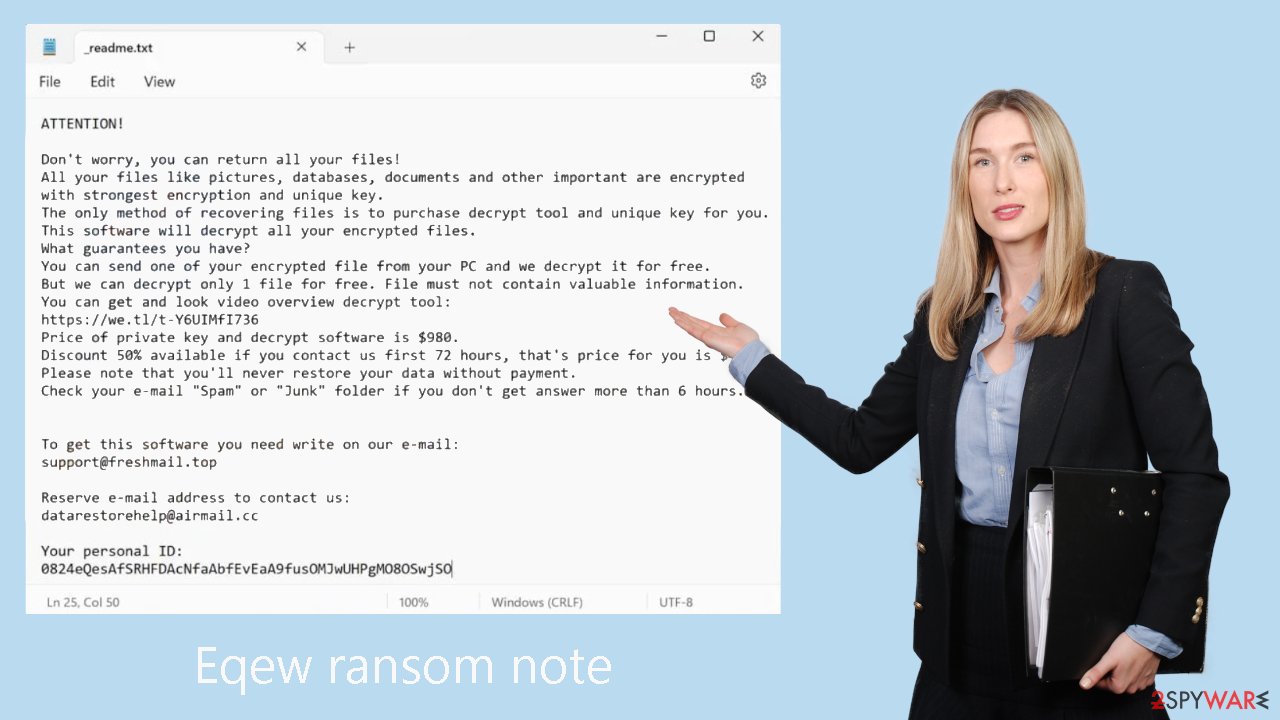
Unfortunately, the key to decryption is solely in the hands of the cybercriminals that spread the Eqew malware. Soon after data encryption, a message with the file name _readme.txt appears, explaining that victims need to pay $490 or $980 in Bitcoins to receive a decryption tool and get access to their files again. For the purpose of bargaining, the offenders offer contact information such as support@freshmail.top and datarestorehelp@airmail.cc.
Even if attackers are the only ones with the ability to grant access to the decryption tool, there is a way to retrieve data without giving in to their demands. Thankfully, security experts have created other decryption methods that are available, however, their efficacy may differ, for those affected by this strain of Djvu. For people without backups, there are still other choices available; further information is accessible below.
| NAME | Eqew |
| TYPE | Ransomware, file-locking malware |
| MALWARE FAMILY | Djvu ransomware |
| FILE EXTENSION | .eqew |
| RANSOM NOTE | _readme.txt |
| CONTACT | support@freshmail.top, datarestorehelp@airmail.cc |
| RANSOM AMOUNT | $490/$980 |
| FILE RECOVERY | There is no guaranteed way to recover locked files without backups. Other options include paying cybercriminals (not recommended, might also lose the paid money), using Emisoft's decryptor (works for a limited number of victims), or using third-party recovery software |
| MALWARE REMOVAL | After disconnecting the computer from the network and the internet, do a complete system scan using a security program |
| SYSTEM FIX | As soon as it is installed, malware has the potential to severely harm some system files, causing instability problems, including crashes and errors. Any such damage can be automatically repaired by using FortectIntego PC repair |
The ransom note
Eqew ransomware drops a _readme.txt ransom note:
ATTENTION!
Don't worry, you can return all your files!
All your files like pictures, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
hxxps://we.tl/t-Y6UIMfI736
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that's price for you is $490.
Please note that you'll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don't get answer more than 6 hours.To get this software you need write on our e-mail:
support@freshmail.topReserve e-mail address to contact us:
datarestorehelp@airmail.ccYour personal ID:
–
Ransomware distribution techniques
Malicious software cracks and pirated software installers are two primary ways that ransomware spreads. Cybercriminals utilize these strategies to fool people into downloading and installing their harmful software which frequently poses as legitimate. The virus encrypts the user's personal files and demands a ransom to unlock them as soon as the corrupted program is installed.
Downloading software only from reliable sources is essential to reducing the risk of ransomware and other malware infections. Avoid downloading installers that are pirated or cracked software since they often contain viruses that might compromise the security of your system. When downloading software, only download it from official websites or reliable third-party sources.
Updating software and operating systems is also essential. Cybercriminals usually use weaknesses in out-of-date software as a springboard to spread malware. As a result, keeping your software updated with the most recent security patches is a good way to guard against such vulnerabilities being exploited.
An additional line of security is provided by using trustworthy antivirus software and keeping it updated. Malware can be found and eliminated by antivirus software before it has a chance to damage your device. Updating your antivirus program on a regular basis guarantees that it will detect and remove the newest dangers. Following these guidelines lessens your chance of being a victim of the Eqew ransomware and other types of malware.
Remove the Eqew virus carefully
Before encrypting data, ransomware makes a number of changes to the Windows operation system. These changes include things like erasing Shadow Volume Copies to prevent files from being recovered, modifying the Windows Registry to allow malicious files to persist, dropping malicious files into various folders, blocking access to cybersecurity websites by altering the “hosts” file, and installing modules designed to steal sensitive data, such as credentials, passwords, and bitcoin wallets.
As such, it is crucial to ensure that the Eqew ransomware eradication process is correctly followed and that the sequence is followed precisely. If this isn't done, the likelihood of recovering data without caving in to ransom demands may be greatly reduced.
Disconnecting your system from any network or internet connection is the first step in starting the removal process. All you need to do to accomplish this is disconnect the Ethernet cord or turn off your WiFi. After ensuring this isolation, you can move forward with the next procedures for eliminating the infection.
Because it is not practical to remove the infection manually, security software like SpyHunter 5Combo Cleaner or Malwarebytes must help. It's crucial to remember that ransomware may cause disruptions to these apps, therefore in order to avoid any issues, you must enter Safe Mode and perform the scan from there.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on the Start button and select Settings.
- Scroll down to pick Update & Security.
- On the left side of the window, pick Recovery.
- Now scroll down to find the Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Click Restart.
- Press 5 or click 5) Enable Safe Mode with Networking.
Delete the “hosts” file
As mentioned, Eqew ransomware may alter your “hosts” file in a way that would prevent you from visiting certain websites related to security. In order to stop this, you have to delete the file – it will be later recreated by Windows, and restrictions to access certain websites will be lifted. Go to the following location (note: make sure Hidden files are visible):
C:\Windows\System32\drivers\etc\
There, find the file titled “hosts” and delete it by pressing Shift + Del on your keyboard.
Repair your system after a malware infection
FortectIntego is a software tool intended to mitigate malware-induced damage. The program works by first performing a full system scan in order to locate any missing or corrupted data. The files are then replaced with their original, undamaged copies. This procedure works especially well for repairing damage caused by malware, such as changes made to the Windows Registry and the deletion of important system files.
In addition, the program scans for and fixes issues related to the operating system, like missing or corrupted DLL files, and it can even fix problems with the boot process. The computer need to be returned to a stable and healthy state when the extensive repair process is finished.
Recover .eqew files
One common fallacy is the idea that security software can instantly fix problems with encrypted files on a device. Unfortunately, this presumption is false. It is not practicable for anti-malware solutions to recover ransomware-encrypted data because they are primarily focused on removing infected files from your computer and avoiding future infections. Recovery of encrypted data necessitates a completely different methodology.
Upon the deployment of ransomware, it encrypts segments of data within each file, generating a unique ID along with an encryption/decryption key pair. The assailants behind the attack receive this vital fact. When they match a decryption key with its matching ID, they can access users' files thanks to this information. Because hackers are typically unscrupulous, victims of their services typically have to pay a fee in order to obtain the decryption key.
It is highly recommended that you avoid interacting with the attackers due to their dubious credibility. It is advised to investigate alternate file recovery techniques instead. Among the options are using the Emisoft decryptor, using specialist data-recovery software, or holding off until more recovery tools become available. You may read more about these options in detail below.
Getting rid of Eqew virus. Follow these steps
Use Emsisoft decrytor for Djvu/STOP
If your computer got infected with one of the Djvu variants, you should try using Emsisoft decryptor for Djvu/STOP. It is important to mention that this tool will not work for everyone – it only works if data was locked with an offline ID due to malware failing to communicate with its remote servers.
Even if your case meets this condition, somebody from the victims has to pay criminals, retrieve an offline key, and then share it with security researchers at Emsisoft. As a result, you might not be able to restore the encrypted files immediately. Thus, if the decryptor says your data was locked with an offline ID but cannot be recovered currently, you should try later. You also need to upload a set of files – one encrypted and a healthy one to the company's servers before you proceed.
- Download the app from the official Emsisoft website.

- After pressing Download button, a small pop-up at the bottom, titled decrypt_STOPDjvu.exe should show up – click it.

- If User Account Control (UAC) message shows up, press Yes.
- Agree to License Terms by pressing Yes.

- After Disclaimer shows up, press OK.
- The tool should automatically populate the affected folders, although you can also do it by pressing Add folder at the bottom.

- Press Decrypt.

From here, there are three available outcomes:
- “Decrypted!” will be shown under files that were decrypted successfully – they are now usable again.
- “Error: Unable to decrypt file with ID:” means that the keys for this version of the virus have not yet been retrieved, so you should try later.
- “This ID appears to be an online ID, decryption is impossible” – you are unable to decrypt files with this tool.
Restore files using data recovery software
Since many users do not prepare proper data backups prior to being attacked by ransomware, they might often lose access to their files permanently. Paying criminals is also very risky, as they might not fulfill the promises and never send back the required decryption tool.
While this might sound terrible, not all is lost – data recovery software might be able to help you in some situations (it highly depends on the encryption algorithm used, whether ransomware managed to complete the programmed tasks, etc.). Since there are thousands of different ransomware strains, it is immediately impossible to tell whether third-party software will work for you.
Therefore, we suggest trying regardless of which ransomware attacked your computer. Before you begin, several pointers are important while dealing with this situation:
- Since the encrypted data on your computer might permanently be damaged by security or data recovery software, you should first make backups of it – use a USB flash drive or another storage.
- Only attempt to recover your files using this method after you perform a scan with anti-malware software.
Install data recovery software
- Download Data Recovery Pro.
- Double-click the installer to launch it.

- Follow on-screen instructions to install the software.

- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders where you want the files to be recovered from.

- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.

- Press Scan and wait till it is complete.

- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.

Find a working decryptor for your files
File encryption is a process that is similar to applying a password to a particular file or folder. However, from a technical point of view, encryption is fundamentally different due to its complexity. By using encryption, threat actors use a unique set of alphanumeric characters as a password that can not easily be deciphered if the process is performed correctly.
There are several algorithms that can be used to lock data (whether for good or bad reasons); for example, AES uses the symmetric method of encryption, meaning that the key used to lock and unlock files is the same. Unfortunately, it is only accessible to the attackers who hold it on a remote server – they ask for a payment in exchange for it. This simple principle is what allows ransomware authors to prosper in this illegal business.
While many high-profile ransomware strains such as Djvu or Dharma use immaculate encryption methods, there are plenty of failures that can be observed within the code of some novice malware developers. For example, the keys could be stored locally, which would allow users to regain access to their files without paying. In some cases, ransomware does not even encrypt files due to bugs, although victims might believe the opposite due to the ransom note that shows up right after the infection and data encryption is completed.
Therefore, regardless of which crypto-malware affects your files, you should try to find the relevant decryptor if such exists. Security researchers are in a constant battle against cybercriminals. In some cases, they manage to create a working decryption tool that would allow victims to recover files for free.
Once you have identified which ransomware you are affected by, you should check the following links for a decryptor:
- No More Ransom Project
- Free Ransomware Decryptors by Kaspersky
- Free Ransomware Decryption Tools from Emsisoft
- Avast decryptors

If you can't find a decryptor that works for you, you should try the alternative methods we list below. Additionally, it is worth mentioning that it sometimes takes years for a working decryption tool to be developed, so there are always hopes for the future.
Report the incident to your local authorities
Ransomware is a lucrative, highly illegal business, and authorities are actively targeting ransomware operators. The level of investigation and follow-up depends on the country, the scale of the incident, and whether the attack is linked to known ransomware groups. To increase the likelihood of identifying the culprits, the agencies need information. In many cases, reports are used primarily for intelligence gathering, trend analysis, and victim support rather than immediate identification of attackers.
Therefore, by reporting the crime, you could help stop the cybercriminal activities and catch the threat actors. Reporting does not guarantee investigation or recovery of data, but it contributes to broader efforts to track ransomware campaigns. Make sure you include all the possible details, including how did you notice the attack, when it happened, etc. Relevant details may also include affected systems, ransom demands, cryptocurrency wallet addresses, and any communication with the attackers. Additionally, providing documents such as ransom notes, encrypted files, or malware executables would be beneficial.
Law enforcement agencies typically deal with online fraud and cybercrime, although it depends on where you live. Here is the list of local authority groups that handle incidents like ransomware attacks, sorted by country:
- USA – Internet Crime Complaint Center IC3
- United Kingdom – ActionFraud
- Canada – Canadian Anti-Fraud Centre
- Australia – ScamWatch
- New Zealand – ConsumerProtection
- Germany – Polizei
- France – Ministère de l'Intérieur

If your country is not listed above, you should contact the local police department or communications center.
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
