Erebus ransomware / virus (Removal Instructions) - Jun 2017 update
Erebus virus Removal Guide
What is Erebus ransomware virus?
Erebus Linux ransomware targets servers

Erebus ransomware is a malicious program that aims to compromise Linux systems and especially servers. Just like any other ransomware[1], Erebus' primary goal is to corrupt as many machines as possible and demand an enormous ransom afterward.
The initial version of Erebus used RSA-2048 encryption, appended .ecrypt file extensions to files and leaved two files as ransom notes: YOUR_FILES_HAS_BEEN_ENCRYPTED.txt” and “YOUR_FILES_HAS_BEEN_ENCRYPTED.html. The virus was using hacked websites in South Korea as its Command and Control (C&C) servers. The version was able to encrypt over 423 different file types.
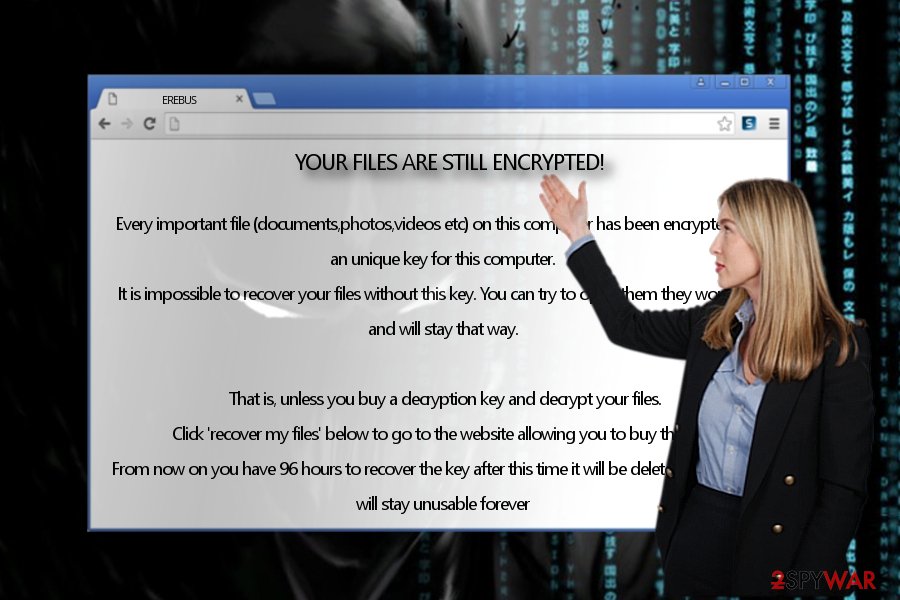
The subsequent version of the ransomware was designed to bypass User Account Control (UAC) feature to launch itself with higher privileges. The virus stated that if the victim fails to comply with its demands and pay 0.085 BTC within 96 hours, the files stored on the computer will be deleted. The updated version of Erebus virus deleted victim's Volume Shadow Copies to prevent him from restoring encrypted files for free.
Although keeping a copy of personal files on an external storage device can help you to save part of your work in case of a ransomware attack, the majority of computer users do not feel the need to create them. Consequently, they have to sorrow over lost files later and desperately look for data recovery methods.
It doesn't matter whether you are a Windows, Mac or Linux user, you must take preventative measures to ward of malicious attacks. We suggest using software like FortectIntego or SpyHunter 5Combo Cleaner for ransomware removal. To remove Erebus, you must use a software that is compatible with Linux.
Update February 2017: Erebus improves, demands a smaller ransom
In February, cyber security experts noticed a new version of this virus that encrypts target files with AES encryption[2] and then modifies their file extensions using ROT-23 cipher. After that, it saves the README.html file on the desktop. The file contains instructions on how to recover the files.
As common for this type of virus, it urges victims to pay within 96 hours. There has been a tendency among hackers to use single-use email addresses for contacting with the victims. However, there is too little information whether the cyber criminals respond to victims and transfer the files. If you have fallen into the trap of this ransomware as well, concentrate on Erebus removal.
Now the current edition bypasses User Account Control[3] window, or in other words, disables the function which initiates dialogue boxes before installing a new program. Likewise, the cryptomalware deprives a victim of ceasing the infection manually. Besides, the virus modifies registry keys to accelerate its functionality.
The ransomware launches eventvwr.msc file, which then opens eventvwr.msc file. The EventViewer is no longer associated with mmc.exe file, therefore it launches a randomly entitled executable of the virus. Thanks to EventViewer's capabilities to run in elevated mode, the virus' executable will be launches with similar permissions.
Afterward, Erebus connects http://ipecho.net/plain and http://ipinfo.io/ to identify the geographical location of a user. Later on, the virus will also access Tor network and connect to its Command and Control server.
Do not underestimate the ransomware as it deletes shadow volume copies leaving fewer chances for its victims to recover data. At the moment, it demands quite a small amount of ransom – 0,85 BTC (90 USD). Lastly, it launches an additional message which once again informs users about the ransomware attack.
Files crypted!
Every important file on this computer was crypted. Please look on your documents or desktop folder for a file called README.html for instructions on how to decrypt them.
Update June 2017: Erebus malware strikes to South Korean web hosting company
Erebus successfully infected a web hosting company Nayana in South Korea[4], which allowed the malware to compromise thousands of websites. The ransomware attack affected over hundred Linux servers and it seems that it encouraged the cybercriminals to demand for a ridiculously high ransom – 10 Bitcoins, which is nearly $26k. Later on, frauds realized that the ransom sum was too high and lowered it to 5.4 Bitcoin – approximately $14k.
The ransomware locked databases, images and videos. The company has published several notes on its official website, suggesting that it is sorry for the inconvenience and that legal authorities are investigating the case at the moment. In the meantime, Nayana employees are working hard to respond to customers and restore backup files provided by them. It is also known that the company is currently negotiating the ransom price with cyber criminals.
The notices posted on company's official website suggest that cybercriminals may have given the company quite a good discount – one of provided noticed contain a piece of message from cyber criminals, asking for 550 BTC. Frauds even provide a calculation proving that the company can pay it.
Distribution tricks
Unlike other ransomware infections, the virus concentrates on malvertising to deliver its attacks. Specifically, it works through ads which users carelessly click on. Afterward, they get redirected to the domain which is infected with RIG exploit kit [5].
Likewise, when a victim finds himself in such website, it becomes a matter of seconds until Erebus strikes. In order to avoid or at least lower the risk of a cyber attack, install a proper security program and let it deal with the virtual threat. It also comes in handy detecting such threats as trojans or smaller threats – hijackers.
Remove Erebus virus
In order to successfully remove Erebus virus, you will need a malware elimination utility. For that purpose, use practical tools that are compatible with Linux system. Keep in mind that they need to be updated in order for them to detect all components and registry entries of the threat.
After the elimination of Erebus, remember to follow safe browsing rules to prevent attackers from infecting your PC ever again. In the end, beware of spam emails since they also often happen to be harbingers of file-encrypting threats. By keeping updated software and cautiously surfing the Web, you might lower the risk not only of Erebus ransomware attack but other crypto-virus as well.
Getting rid of Erebus virus. Follow these steps
Manual removal using Safe Mode
Some file-encrypting threats are known to lock computer screen or cease other important system functionalities. It is likely that the current threat might be one of them. As a result, it is likely that you may encounter Erebus removal problems. Thus, these instructions (designed for Windows users) will help you regain access.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Erebus using System Restore
In case automatic elimination does not go as planned, opt for the latter method.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Erebus. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Erebus from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.Unfortunately, files locked on Linux systems can be recovered using data backups only. If you do not have it, your files might be unrecoverable.
If your files are encrypted by Erebus, you can use several methods to restore them:
No Erebus decryption tools available
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Erebus and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Jack Wallen. Ransomware: The most important thing you can do not to be a victim. TechRepublic. News, Tips, and Advice for Technology Professionals.
- ^ Tom Henderson . Learn AES256 on Your Lunch Break. SmartBear. Resources for Mobile, Agile, and Cloud.
- ^ What is UAC (User Account Control) & Why You Should Not Turn it Off. DigitalCitizen. Tutorials, Reviews, News and Other Articles.
- ^ South Korean web hosting company infected by Erebus ransomware. Network World. Network News, Trend Analysis, Product Testing and the Industry's Most Important Blogs.
- ^ Tom Spring. Inside the RIG exploit kit. ThreadPost. The first stop for security news.





















