Fast_Decrypt_and_Protect@Tutanota.com ransomware / virus (Virus Removal Guide) - updated May 2018
Fast_Decrypt_and_Protect@Tutanota.com virus Removal Guide
What is Fast_Decrypt_and_Protect@Tutanota.com ransomware virus?
Fast_Decrypt_and_Protect@Tutanota.com is a file encrypting virus that is used to blackmail people
Fast_Decrypt_and_Protect@Tutanota.com is a ransomware virus,[1] and its primary goal is to encrypt certain computer files. This crypto-locker is a part of Xorist ransomware family that been lurking around the world wide web since 2016. It uses XOR or TEA cipher to encrypt data and appends .fast_decrypt_and_protect@tutanota.com file extension. The virus then drops ransom note HOW TO DECRYPT FILES.txt which explains that payment of 3 BTC should be transferred to crooks in order to obtain a decryption key. Nevertheless, victims can use a free Xorist decryptor that might be useful for data recovery.
| SUMMARY | |
| Name | Fast_Decrypt_and_Protect@Tutanota.com |
| Type | Ransomware |
| Encryption algorithm | XOR or TEA |
| Family | Xorist ransomware |
| Demanded ransom | 3 BTC |
| Contact email | fast_decrypt_and_protect@tutanota.com |
| Distribution | Spam emails, software vulnerabilities, malicious websites, etc. |
| Elimination | Automatic only – use FortectIntego or SpyHunter 5Combo Cleaner |
Criminals put victims under time pressure and give mere 24 hours to make the payment. If the ransom isn’t transferred within this time, the extortionists threaten with the complete destruction of the encrypted data. This way, different documents, files archives, video and audio material will supposedly be destroyed. We don’t know whether the criminals stick to this promise, but it is definitely not worth risking it. A safer solution is to remove Fast_Decrypt_and_Protect@Tutanota.com virus from the PC and prevent further data encryption.
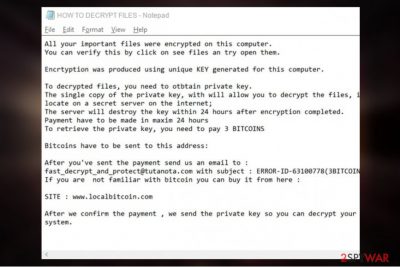
The ransom note states the following [sic]:
All your important files were encrypted on this computer. You can verify this by click on see files an try open them. Encryption was produced using unique KEY generated for this computer.
To decrypt files, you need to obtain private key. The single copy of the private key, with will allow you to decrypt the files, is locate on a secret server on the internet; The server will destroy the key within 24 hours after encryption completed. Payment have to be made in maxim 24 hours. To retrieve the private key, you need to pay 3 BITCOINS.
Bitcoins have to be sent to this address:
After you've sent the payment send us email to: fast_decrypt_and_protect@tutanota.com with subject : ERROR-ID-random(3BITCOINS) . If you are not familiar with bitcoin you can buy it from here: SITE : www.localbitcoin.com.
After we confirm the payment, we send the private key so you can decrypt your system.
Security specialists[2] advise not to contact Fast_Decrypt_and_Protect@Tutanota.com malware creators under any circumstances. Even if you manage to get the decryptor, you will be doing a big favor to cybercriminals and encourage them to produce more viruses. Thus, instead stick to Xorist decryptor or use third-party software to recover your files.
There is no much that the cybersecurity experts know about this virus. Its distribution is rather low, and it is quite challenging to come across its samples. Judging from the ransom note, it is clear that hackers are not native English speakers, as the message is littered with mistakes.
Nevertheless, what the experts do know is how to recognize the threat once it is on the computer. The infected device starts working slower, its RAM and CPU utilization[3] will increase to the highest levels, and different strange processes will show up in the Windows Task Manager. Additionally, ransomware viruses are known to weaken the system which allows other infections to slip through into machines easily.
Even if you don’t notice the initial processes of the ransomware attack, you will inevitably become aware of this problem after you unexpectedly lose access your files and find a ransom note on your PC demanding you to pay. Of course, you should refuse any collaboration with the cybercriminals and perform Fast_Decrypt_and_Protect@Tutanota.com removal instead. Fix your PC with FortectIntego or similar antivirus software. Professional tools will make sure that the virus is banished from the system to the last bit of its malicious components.
Ransomware distribution: spam emails dominate
There are a few techniques that modern ransomware use for the system infiltration. One of these methods relies on spam emails and their attachments. Malicious spam campaigns send around counterfeited emails with an attached files disguised as invoice or tax information. The virus payload is activated once the victim opens an infected attachment.
Another way that crypto-ransomware can infiltrate computer is through brute force attacks. Weak passwords of RDP[4] networks and outdated software vulnerabilities highly increase the chances of ransomware attack.
Finally, ransomware developers may employ exploit kits and Trojans to deploy their malicious creations on the victim’s computer. Typically such infectious programs will be delivered through Torrent networks or other peer-to-peer file sharing domains as well as unsafe websites.
As you can see, file-encrypting malware can easily catch you off guard. Thus, we highly recommend following these simple precautions:
- Install a reputable anti-malware software and keep it up to date;
- Always update your software and operating system as soon as new patches are out;
- Only download updates from trusted sources;
- Protect your RDP with a strong password;
- Do not open spam emails (especially attachments);
- Avoid suspicious websites, such as porn, gambling, file-sharing and other similar domains.
Quick suggestions for Fast_Decrypt_and_Protect@Tutanota.com removal
If you find yourself in a situation when you have to remove Fast_Decrypt_and_Protect@Tutanota.com virus from your PC but have no experience in any malware elimination whatsoever, you should not panic and trust this job to the specialized antivirus software, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes. These tools will locate hazardous components on your computer and expose virtual threats, including exploits, rootkits, and trojans.
After Fast_Decrypt_and_Protect@Tutanota.com removal, you will then be able to attempt data recovery. Though there is official decryption tool for Xorist invented, it might not help with this version of ransomware. Nevertheless, you should be able to restore at least some of your files using alternative recovery suggestions below.
Getting rid of Fast_Decrypt_and_Protect@Tutanota.com virus. Follow these steps
Manual removal using Safe Mode
Some users may encounter problems removing this parasite from their computers. To make the elimination procedure easier, experts recommend running the system scan with an antivirus utility in Safe Mode. Learn to activate this mode below:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Fast_Decrypt_and_Protect@Tutanota.com using System Restore
If the Safe Mode does not help decontaminate the virus, you may try the following steps:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Fast_Decrypt_and_Protect@Tutanota.com. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Fast_Decrypt_and_Protect@Tutanota.com from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Fast_Decrypt_and_Protect@Tutanota.com, you can use several methods to restore them:
Recovery with Data Recovery Pro
Go through the guidelines below to learn how to use Data Recovery Pro and recover your files
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Fast_Decrypt_and_Protect@Tutanota.com ransomware;
- Restore them.
Windows Previous Versions feature recovery option
If you had System Restore feature enabled prior malware attack, you should have no problems recovering your important files using Windows Previous Versions feature.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Recover files with Shadow Explorer
If you aren't sure how to use Shadow Explorer, follow the instructions below.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Try Xorist decryptor
You can use Xorist decryptor by Emisoft and see if it can be useful for you.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Fast_Decrypt_and_Protect@Tutanota.com and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Anatomy of a crypto-ransomware attack. Sophos. Centralize Your Network Security with Sophos.
- ^ Viirused. Viirused. Estonian cybersecurity experts.
- ^ Nathan Bookshire. How to spot Ransomware before it encrypts your computer. VirusRemoval. Virus & Malware Removal.
- ^ Remote Desktop Protocol. Wikipedia. The Free Encyclopedia.





















