FedEx tracking email virus (Virus Removal Guide) - updated Feb 2019
FedEx tracking email virus Removal Guide
What is FedEx tracking email virus?
FedEx tracking virus is a malspam campaign that infects users' computers with the dangerous data-stealer Hancitor trojan

FedEx tracking email virus is a phishing email strain that is delivered to random computer users all over the world. The deceptive message pretends to be coming from FedEx delivery service and warns users about the alleged package. The attached document, which often comes as MS Word .doc file, is an obfuscated payload of data-stealing malware called Hancitor.[1] The virus is capable of recording keystrokes, harvesting personal information and installing additional payloads. FedEx (just as UPS and DHL[2]) is one of the biggest delivery services in the world and is often targeted by numerous scammers and hackers; some hoaxes being exceptionally believable, while others are poorly executed. However, users should be aware of FedEx tracking virus and not fall into a cleverly executed trap arranged by cybercriminals.
| SUMMARY | |
| Name | FedEx tracking email virus |
| Type | Phishing |
| Poses as | FedEx delivery service |
| Proliferates | Hancitor trojan |
| How to recognize? | Phishing email urges users to open the attachment or click on link in an aggressive manner, grammar and spelling mistakes, etc. |
| Trojan elimination | Use reliable anti-malware software |
| Optimization | Install FortectIntego to repair the system |
Users typically receive FedEx tracking email scam message which claims that the important information about the alleged package delivery is enclosed in the attached document. Because the email is sent to random users, it will reach those who are not expecting anything from FedEx, instantaneously raising suspicions.
However, because FedEx is such a widely used service around the world, among targeted victims there will always be those who are expecting a parcel, prompting people to believe in FedEx tracking virus scam.
Typically, users are asked to open an attachment which is a malicious document, .pdf, .html, .txt or other files. Cybercriminals are often employing social engineering tricks to make sure users open the attachment – they create a sense of urgency by using scare tactics. For example, “print this document, or your parcel will be returned to the sender.”
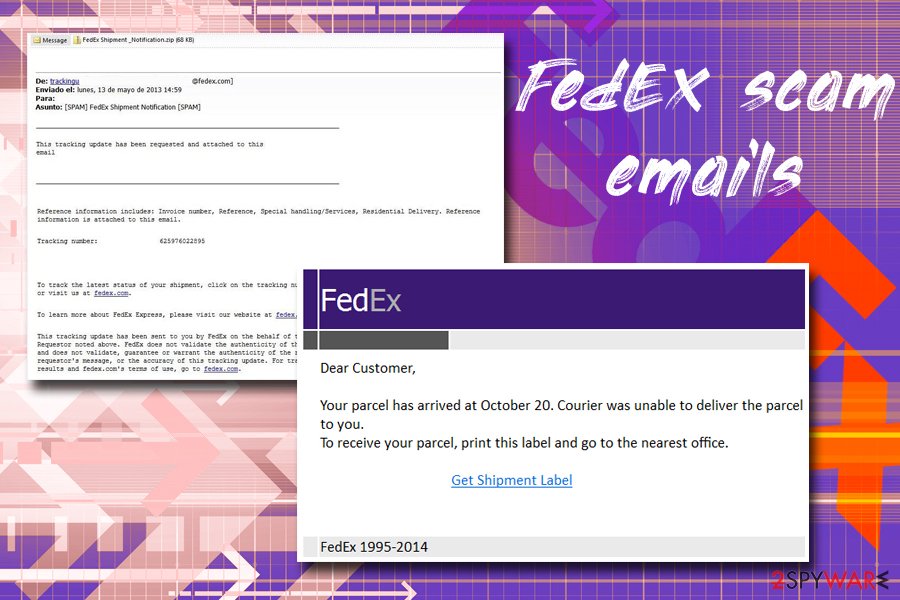
Here are several examples of malicious email messages:
This tracking update has been requested and attached to this email.
Reference information includes: Invoice number, Reference, Special handling/Services, Residential Delivery. Reference information is attached to this email.
Tracking number: 625976022895To track the latest status of your shipment, click on the tracking number above, or visit us at fedex.com
To find the latest state of your shipment, click the tracking # above.
The tracking update have been sent to you by FedEx.
Thank you for your business.
2018 FedEx. the written contact of this notification is safeguarded by copyright and trademark laws and regulations under United States andInternational laws. See our privacy policy. All right reserved.
Note that the sender's address is usually made to look legitimate. However, the trick is simple: hackers register domain addresses that look akin well-known companies like parcel delivery service FedEx or governmental institutions like Tax Office.[3] While in most cases deception can be spotted after looking closely at the delivery address, some crooks go an extra mile to make users see the real address of the impersonated company or institution.
As soon as users open the document attached to FedEx tracking email virus, the malicious macros ensure Hancitor is downloaded and installed into the machine. Unfortunately, victims might not even notice anything out of the ordinary, as no system changes are visible on the screen. After the infiltration, the only way to remove FedEx tracking virus is to use anti-virus software, such as FortectIntego or SpyHunter 5Combo Cleaner.
FedEx tracking virus performs a series of changes on the system which allows hackers to:
- Start or stop processes
- Schedule tasks
- Install additional applications
- Take screenshots
- Collect personal data and send it to a remote server, etc.
Additionally, FedEx tracking email virus serves as a botnet, resulting in the malware spreading fast and infecting more machines over time. Trojans are also often used as backdoors[4] for ransomware, so file loss is also likely.
To conclude, if you clicked on a malicious attachment, you are infected with a dangerous trojan, and you should take care of FedEx tracking virus removal immediately.
Never underestimate cybercriminals – they are capable of constructing a high quality phishing email
There is no surprise that spam emails are one of the most successful malware distribution methods out there. Sure, hackers also use such means as exploit kits, hacked websites, misconfigured RDP, and similar, but phishing emails were always their favorite, as automated botnets do the job quickly and efficiently. This ensures the stable infection rate all over the world.
Therefore, users should treat every email with suspicion, even if it looks legitimate. Watch out for these phishing email signs:
- The “From” address usually resembles the original company's one, although sometimes it can be completely random. Closely pay attention to this crucial element, you can almost always see the deception there;
- The subject field typically presents allegedly important information, such as “Delivery attempt,” “Shipping information,” “FedEx shipping,” “Your Invoice,” and similar;
- Phishers refer to victims as “Dear User,” “Dear Customer,” and similar. Large corporations know your name if you are using their service, and they will use it;
- The content of the email usually reports about some sort of problem, for example, wrong delivery address, insufficient information, account registration issue, etc. Immediately after that users are prompted to do something or face a consequence;
- After crooks present the problem, they ask users to click on hyperlinks embedded in the email or download the attachment. Put your cursor on top of the hyperlink and you will see the real URL it will bring you to. Before opening any attachments, scan them using security software or tools like Virus Total;
- And finally, watch out for grammar and spelling mistakes.
Get rid of FedEx tracking email virus using security software
Trojans are not that easy to detect, as they barely emit any symptoms. Nevertheless, FedEx tracking virus removal can be achieved with the help of security software. Experts suggest using FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes, although any other reputable tool will do.
Trojans are nasty infections, and sometimes might be hard to get rid of. Therefore, to remove FedEx tracking email virus fully, users should enter Safe Mode with Networking, as explained below. This way, only the necessary elements will be loaded, and trojan's functionality will be temporarily disabled.
Getting rid of FedEx tracking email virus. Follow these steps
Manual removal using Safe Mode
To remove FedEx tracking virus, enter Safe Mode with Networking as follows:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove FedEx tracking email using System Restore
You can also disable the virus by using System Restore:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of FedEx tracking email. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from FedEx tracking email and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting trojans
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Migo Kedem. Hancitor banking trojan is back. SentinelOne. Autonomous Endpoint Protection.
- ^ Alice Woods. Scammers preparing for Christmas - beware of the fake DHL parcel emails. 2-spyware. Cybersecurity news and articles.
- ^ Fake tax office scam robbed $800,000 from Australians in past month. The Guardian. News, sport and opinion from the Guardian's global edition.
- ^ Vangie Beal. Backdoor access (computing). Webopedia. Online Tech Dictionary.





















