Find-it.pro browser hijacker (virus) - Chrome, Firefox, IE, Edge
Find-it.pro browser hijacker Removal Guide
What is Find-it.pro browser hijacker?
Find-it.pro is an insecure browsing tool you should avoid

A browser hijacker such as Find-it.pro is a type of program that is usually spread via software bundles or other deceptive methods, which results in people not installing them intentionally. This is one of the main reasons why it is categorized as a potentially unwanted program besides the fact that it is relatively useless in the first place.
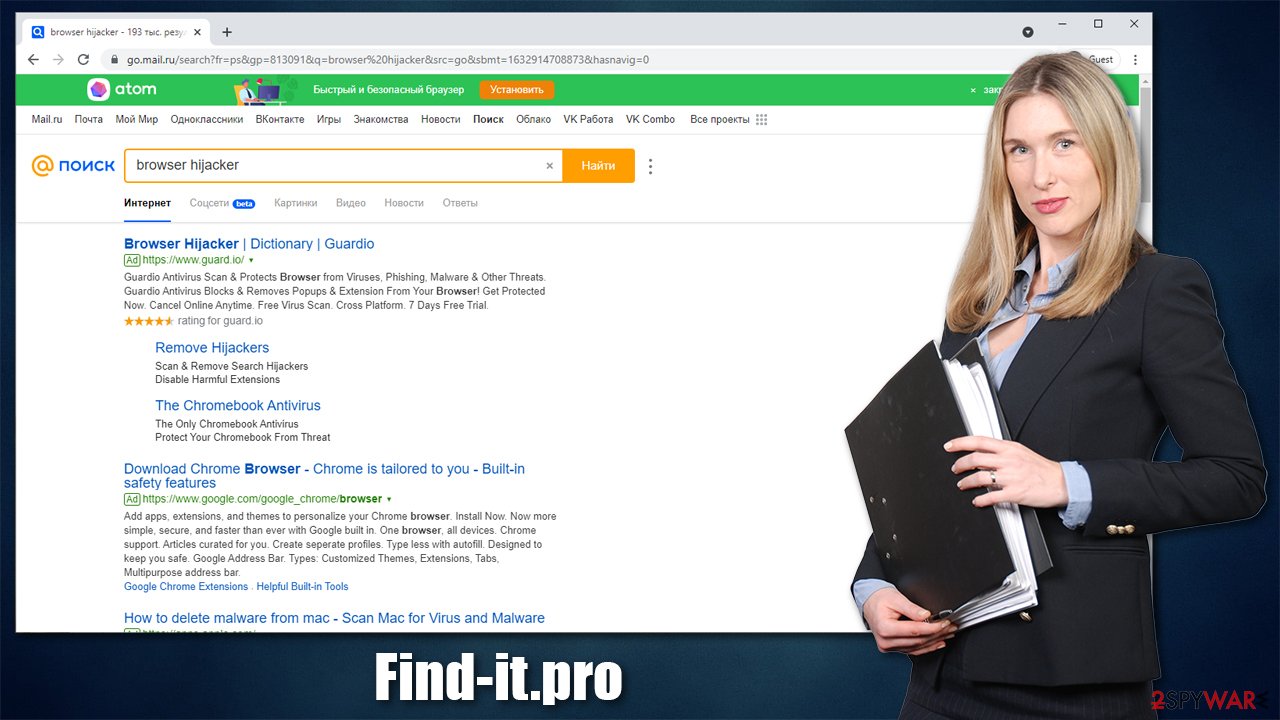
Once installed, the app would immediately take over Google Chrome, Mozilla Firefox, MS Edge, or any other used browser. One of the most distinctive changes people would notice is that the homepage gets set to Find-it.pro, and they no longer see google.com or another preferred URL. Additionally, this activity repeats when a new tab of the browser is opened, so the only way to go back to the intended homepage is by typing it out in the omnibar, which makes it rather uncomfortable.
Changes are made to the way the search works as well. Regardless if the search term is typed in the provided search box or the URL bar, a different provider is used – namely that of a hijacker. It can be immediately noticed that the search provider is Russian and also brings up very questionable search results. All top results are also sponsored links and ads, which makes the results not be genuine in the first place.
Additionally, as long as the PUP is installed on the system, tracking activities are being conducted. Therefore, if you want to take control over your web browsing, you should immediately get rid of the app immediately. In this article, we will explain how to do this in the most efficient way.
| Name | Find-it.pro |
|---|---|
| Type | Browser hijacker, potentially unwanted program |
| IP address | 104.248.38.210 |
| Distribution | Software bundles, deceptive ads, fake update prompts |
| Symptoms | Unknown extension or application is installed on the system; homepage and new tab address are changed to Find-it.pro; a customized search engine is appended to the homepage; search results are littered with sponsored links and ads |
| Risks | Installation of other potentially unwanted programs, privacy risks due to information gathering practices, financial losses |
| Elimination | To uninstall the PUP, you need to find it within your system – it can be placed on your browser or in the installed applications section. For a quicker option, use the virus removal tool |
| Additional steps | Computer infections can cause significant damage to system files or disrupt normal settings. To revert these changes and remediate the OS, perform a full system scan with FortectIntego repair software |
Browser hijackers: how do they work
Browser hijackers have been around for many years now, and they keep evolving even currently. Previously, they were much more malicious in general – users were struggling with their removal due to elevated permissions they got installed with, or they used to gather all sorts of personal information such as emails to send spam. While the situation drastically improved thanks to various regulations put in place, they are still considered to be unwanted software, and there are plenty of reasons for that.
It all starts with PUP distribution methods, which are far from fair. One of the main delivery methods is software bundling[1] – a type technique that compiles several programs into a standalone installer. While there is nothing wrong with offering people to try other software, it is commonly done deceptively – the optional apps are not adequately exposed (for example, pre-ticked boxes, fine print text, and other tricks are used) to people, hence they end up installing them unknowingly.
In order to avoid being a victim of this, you should always be careful and attentive while installing freeware on your device. Always read the installation instructions, never skip through steps, and, most importantly, always pick the Advanced settings if available to be in control of what is actually being installed. Also, have an anti-malware apps like SpyHunter 5Combo Cleaner, Malwarebytes installed on your system to avoid malware and PUPs more effectively.
Once Find-it.pro is installed on the system, it begins to change various settings within the web browsers in order to perform its tasks. As already mentioned, the homepage and new tab changes are meant for users to be using them. By clicking on sponsored links and ads, they generate easy money for browser hijacker developers.
However, it doesn't mean that the hijacker is beneficial or brings anything to the table to users. In fact, developers often advertise PUPs as tools that could enhance or improve search results, which is far from the truth. In reality, all they do is insert ads and home that users click on them. Some of these ads might also be misleading or insecure.
In the background, the browser hijacker also users cookies, web beacons,[2] and other tracking technologies to spy on people's browsing activities. Typically, the following data is collected:
- IP address and ISP
- Technical device data, including device identifiers
- Browser type, language, and other preferences
- Search terms, links clicked, bookmarks added, etc.
Thus, not only doesn't browser hijacker provide anything useful, but it also puts user privacy at risk, all while meddling with search results. This is why security experts[3] recommend eliminating potentially unwanted programs from the system immediately.
Remove the browser hijacker
Potentially unwanted programs are nowhere near as dangerous as Trojans, ransomware, or other malware – they are more of a nuisance, if anything. Most of the time, browser hijackers get attached to browsers as extensions, as it is the main space they operate in. So if you found your device affected, you should first check for suspicious browser extensions.
Check for unwanted browser extensions
Uninstalling extensions is easy – all you have to do is access your browser settings. If you need help, proceed with the instructions below.
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the window's top-right).
- Select Add-ons.
- In here, select the unwanted plugin and click Remove.
![Remove extensions from Firefox Remove extensions from Firefox]()
MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
Remove the installed apps
Some browser hijackers might be installed on the system level. In order to uninstall such programs, you have to access the Control Panel (Windows) or Applications section (Mac).
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
Mac
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)
![Uninstall from Mac 1 Uninstall from Mac 1]()
To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
![Uninstall from Mac 2 Uninstall from Mac 2]()
Clean your browsers
As already mentioned before, browser hijackers use various tracking technologies to harvest information about users in order to deliver targeted ads. These tiny items remain on your browser even if you remove the unwanted extension, so it is a good idea to clean them. If you want to skip this step and rather do it automatically, you can opt for using FortectIntego repair and maintenance utility.
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content, and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
How to prevent from getting browser hijacker
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Bundled Software. Webopedia. The Online Tech Dictionary for Students, Educators and IT Professionals.
- ^ Find-it.pro. Wikipedia. The free encyclopedia.
- ^ Novirus. Novirus. Security advice and malware insights.












