Flame ransomware (virus) - Free Instructions
Flame virus Removal Guide
What is Flame ransomware?
Flame ransomware is a malicious Windows program that demands ransom after encrypting all files on the device
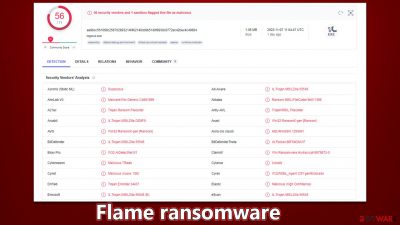
Flame is a ransomware-type virus that is considered to be dangerous to users' files since, once it manages to infiltrate the system, it locks all of them up. For that, it uses a combination of sophisticated encryption algorithms, AES and RSA,[1] making the data unreadable. During this process, all files acquire a randomized extension which consists of four random alphanumeric characters, for example, “63fe”.
The main goal of cybercriminals is to extort money from victims by offering to sell a decryption tool that is meant to decipher all files and make them readable again. It is unknown what kind of sum they would be asking for, as each instance can be different, but the delivery is always asked to be performed as a bitcoin transaction.
Flame ransomware swaps the desktop wallpaper, which includes the contact email b5cce0d45fd0@list.ru and also delivers a ransom note titled read_it.txt, which includes the description in Russian. Paying cybercriminals behind the attack is not recommended, as money loss is a probability, and malware authors should never be trusted.
| Name | Flame virus |
|---|---|
| Type | Ransomware, file-locking malware |
| Malware family | Chaos |
| File extension | A string of four random characters is appended to each file along with the cybercriminals' email address |
| Ransom note | read_it.txt, wallpaper |
| Contact | b5cce0d45fd0@list.ru |
| File Recovery | The only secure way to restore files is by using data backups. If such is not available or were encrypted as well, options for recovery are very limited – we provide all possible solutions below |
| Malware removal | After disconnecting the computer from the network and the internet, do a complete system scan using the SpyHunter 5Combo Cleaner security program. |
| System fix | As soon as it is installed, malware has the potential to severely harm some system files, causing instability problems, including crashes and errors. Any such damage can be automatically repaired by using FortectIntego PC repair |
The ransom note
Ransomware is a type of malware that attempts to make it obvious to the user that their system has been compromised and files encrypted. Ransom notes are an essential part of ransomware, as they provide information on how to pay the ransom and potentially recover data. Without a doubt, it's an important point for malware authors, as the probability of obtaining illegal money payments increases with the delivery of a ransom note.
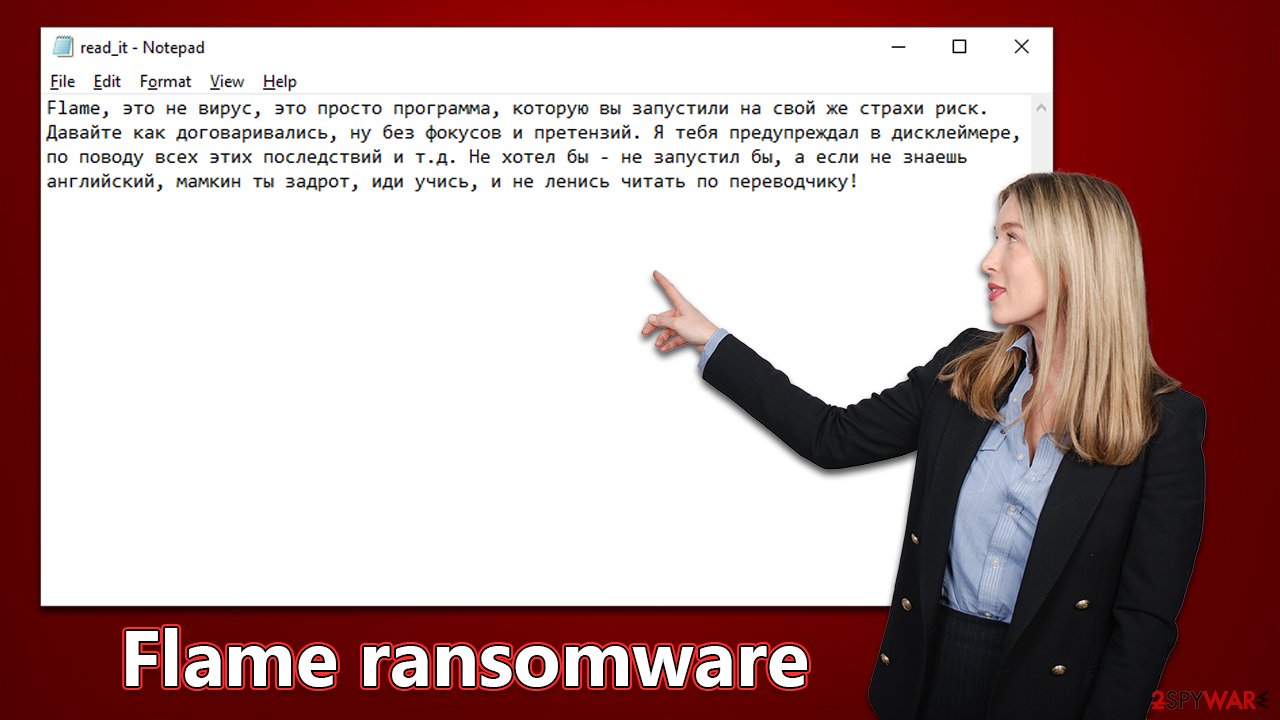
When speaking of this particular ransomware, it delivers the common TXT file as soon as it encrypts all data, although it is written in Russian, which might mean that perpetrators didn't bother to translate it or they aim to infect Russian users. Other Chaos ransomware variants that the Flame virus belongs to (such as Phreaker or OkHacked) have not used this language before in ransom notes, so this behavior is rather odd. The note says:
Flame, это не вирус, это просто программа, которую вы запустили на свой же страхи риск. Давайте как договаривались, ну без фокусов и претензий. Я тебя предупреждал в дисклеймере, по поводу всех этих последствий и т.д. Не хотел бы – не запустил бы, а если не знаешь английский, мамкин ты задрот, иди учись, и не ленись читать по переводчику!
The virus also alters the desktop wallpaper, which is shown in English this time. It reads as follows:
YOUR FILES HAVE BEEN ENCRYPTED*
YOUR FILES WERE ENCRYPTED BY THE FLAME UTILITY. TO DECRYPT YOUR FILES AND REMOVE THIS NOTIFICATION, CLICK ON THE “DECRYPT MY FILES” BUTTON. TECHNICAL SUPPORT – b5cce0d45fd0@list.ru
*Please read the disclaimer!
This program is not a virus, but just a utility that allows you to encrypt user data at will in one click.
Please do not follow the advice of cybercriminals, as they might not deliver the promised tool, or it may simply not work. Instead, we recommend employing the instructions below to remove Flame ransomware and then attempt to restore files using alternative methods.
How to deal with a ransomware attack
The importance of taking remediation actions in the proper order cannot be understated, as improper decisions could lead to data loss. As stated earlier, it's not recommended to trust cybercriminals, as it typically exacerbates losses. Disconnecting your device from the network or internet should be your priority so that malware can no longer spread laterally and crooks can't issue more commands via the internet/deliver additional payloads. You can either unplug the Ethernet cable or disconnect the WiFi connection, or follow the instructions below:
- Type in Control Panel in Windows search and press Enter
- Go to Network and Internet
![Network and internet Network and internet]()
- Click Network and Sharing Center
![Network and internet 2 Network and internet 2]()
- On the left, pick Change adapter settings
![Network and internet 3 Network and internet 3]()
- Right-click on your connection (for example, Ethernet), and select Disable
![Network and internet 4 Network and internet 4]()
- Confirm with Yes.
After you've disconnected your device, start the ransomware removal process. It's possible that some ransomware will delete itself once encryption is finished, in which case you might not find anything. However, this isn't always true since ransomware is commonly spread alongside other types of malware and may leave some additional modules behind.
Therefore, the only reliable way of eliminating all the malicious files and the infection from Windows is by performing a full system scan with security software, such as SpyHunter 5Combo Cleaner or Malwarebytes. Anti-malware can also serve as great aid when dealing with incoming attacks in the future, as long as it's updated on time.
In addition, we recommend you use the FortectIntego PC repair tool to scan for and fix any system files that might be damaged by malware. This will help you avoid having to reinstall your operating system.
How to restore data
Ransomware is malware that can be especially confusing and difficult for first-time victims to understand, as it usually involves data encryption. This means that the data will still be inaccessible even once the virus is gone. There are also many characteristics of ransomware that users don't know about – making mistakes could result in permanent data loss in some cases.
The ideal way to avoid your personal information from being taken hostage in a ransomware attack is to have backups for all your crucial files. If you don't possess any backups, trying to get back your data that has been encrypted by Flame ransomware might be tricky.
Ensure you have reliable backups before using data recovery software or waiting for a decryptor tool – the only two methods available now. If you don't already have working backups, be sure to make copies of all encrypted files so that you don't accidentally corrupt them while trying to recover them.
- Download Data Recovery Pro.
- Double-click the installer to launch it.
![Flame ransomware Flame ransomware]()
- Follow on-screen instructions to install the software.
![Install program Install program]()
- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders where you want the files to be recovered from.
- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.
![Select Deep scan Select Deep scan]()
- Press Scan and wait till it is complete.
- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.
If you're patient, another option for file restoration is waiting for security researchers to develop a decryption tool, which may or may not happen. In the past, malware analysts have managed to create decryptors that help users recover ransomware-encrypted files for free.[2] However, this process could take weeks, months, or even years, or may not even be possible at all. When looking for a decryptor tool, we recommend checking these links:
- No More Ransom Project
- Free Ransomware Decryptors by Kaspersky
- Free Ransomware Decryption Tools from Emsisoft
- Avast decryptors

Final tips
We also recommend reporting the incident to the authorities, which could be particularly helpful when trying to catch cybercriminals behind malware development and distribution. The below links can be useful with this:
- USA – Internet Crime Complaint Center IC3
- United Kingdom – ActionFraud
- Canada – Canadian Anti-Fraud Centre
- Australia – ScamWatch
- New Zealand – ConsumerProtection
- Germany – Polizei
- France – Ministère de l'Intérieur

You should contact the local police department or communications center if your country is not listed above.
Finally, you need to ensure that your files are always kept on backup servers to avoid the consequences of yet another ransomware attack. For that, you should follow the instructions below to back up files on popular services.
Using Microsoft OneDrive
OneDrive is a built-in tool that comes with every modern Windows version. By default, you get 5 GB of storage that you can use for free. You can increase that storage space, but for a price. Here's how to setup backups for OneDrive:
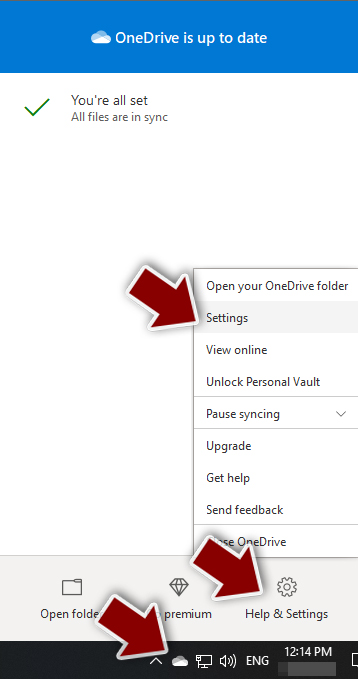
- Click on the OneDrive icon within your system tray.
- Select Help & Settings > Settings.
![Go to OneDrive settings Go to OneDrive settings]()
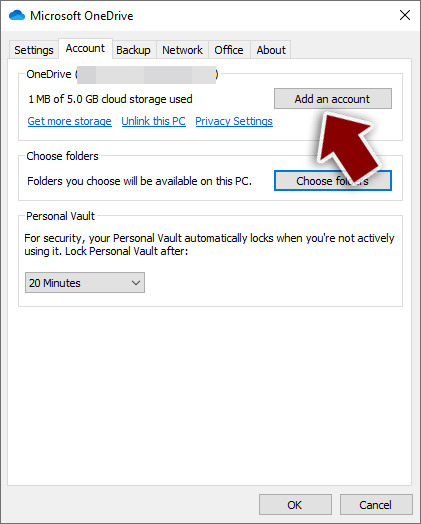
- If you don't see your email under the Account tab, you should click Add an account and proceed with the on-screen instructions to set yourself up.
![Add OneDrive account Add OneDrive account]()
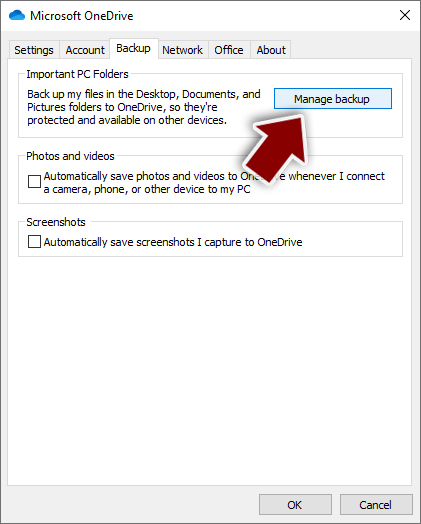
- Once done, move to the Backup tab and click Manage backup.
![Manage backup Manage backup]()
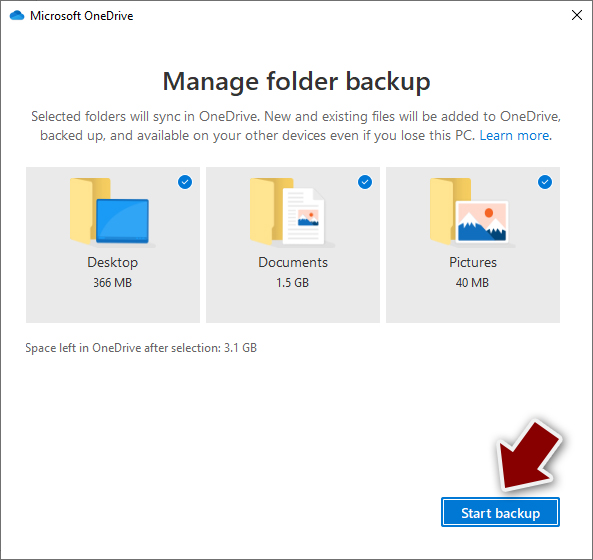
- Select Desktop, Documents, and Pictures, or a combination of whichever folders you want to backup.
- Press Start backup.
![Pick which folders to sync Pick which folders to sync]()
After this, all the files that are imported into the above-mentioned folders will be automatically backed for you. If you want to add other folders or files, you have to do that manually. For that, open File Explorer by pressing Win + E on your keyboard and then click on the OneDrive icon. You should drag and drop folders you want to backup (or you can use Copy/Paste as well).
Using Google Drive
Google Drive is another great solution for free backups. The good news is that you get as much as 15GB for free by choosing this storage. There are also paid versions available, with significantly more storage to choose from.
You can access Google Drive via the web browser or use a desktop app you can download from the official website. If you want your files to be synced automatically, you will have to download the app, however.
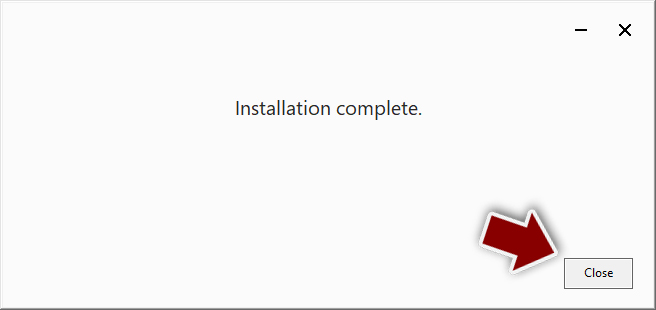
- Download the Google Drive app installer and click on it.
![Install Google Drive app Install Google Drive app]()
- Wait a few seconds for it to be installed.
![Complete installation Complete installation]()
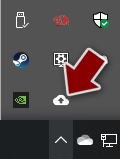
- Now click the arrow within your system tray – you should see the Google Drive icon there, click it once.
![Google Drive Sign in Google Drive Sign in]()
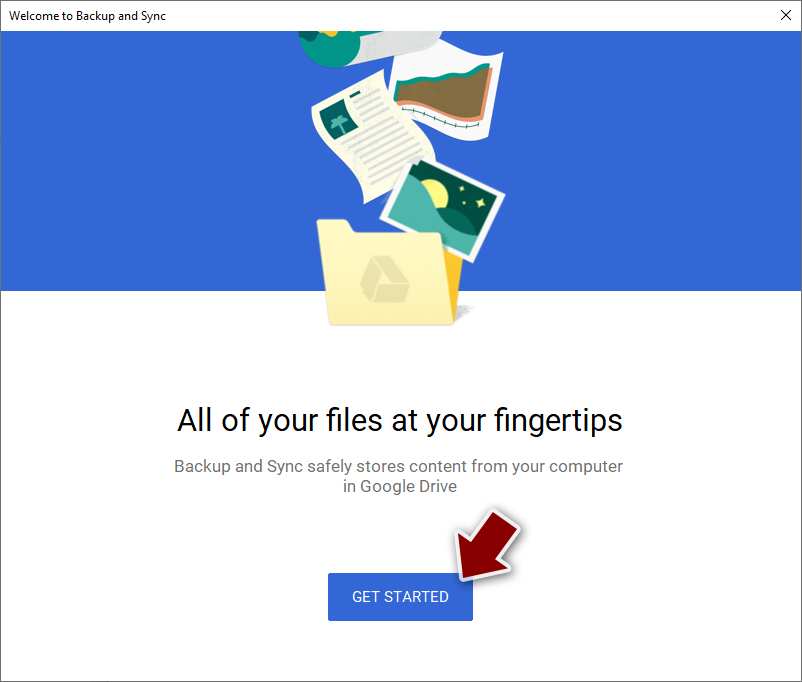
- Click Get Started.
![Backup and sync Backup and sync]()
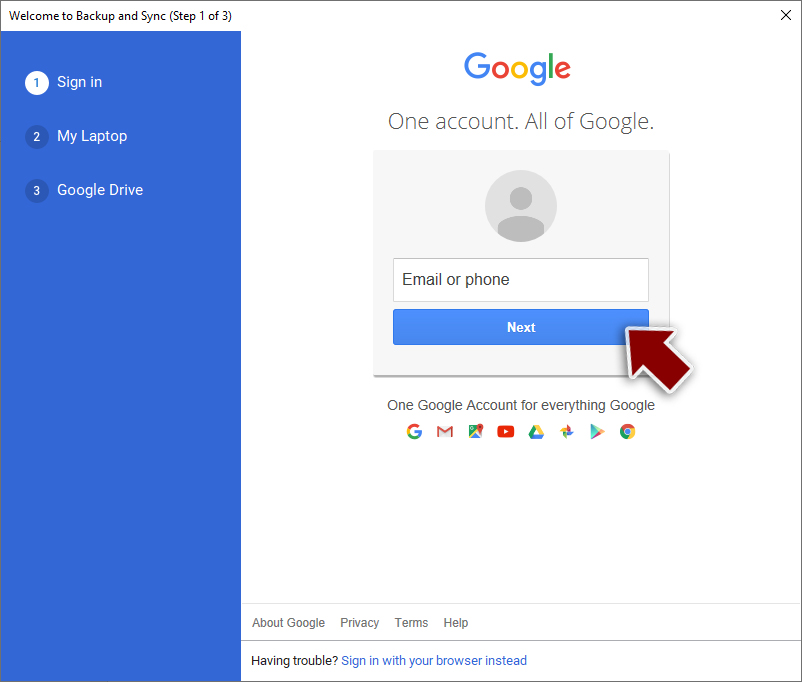
- Enter all the required information – your email/phone, and password.
![Enter email/phone Enter email/phone]()
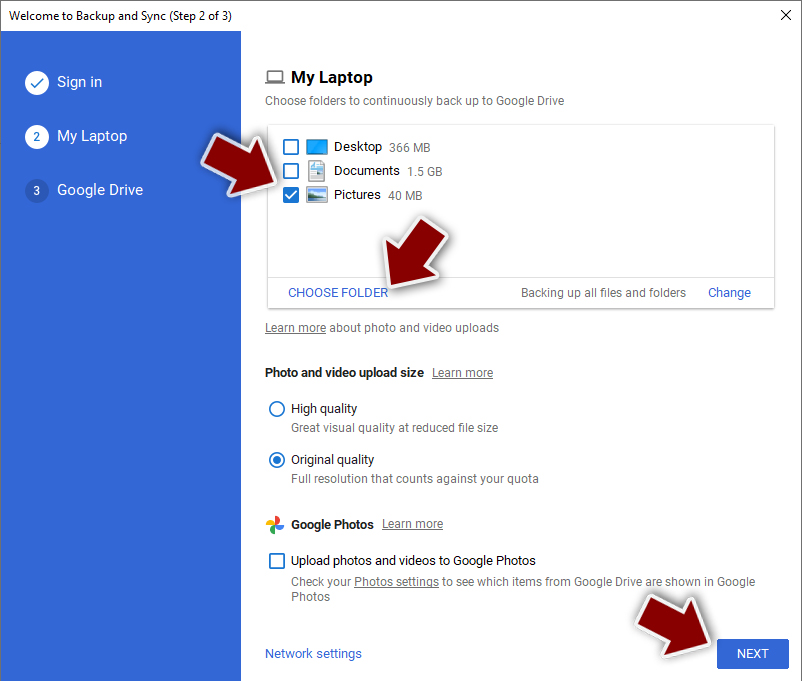
- Now pick what you want to sync and backup. You can click on Choose Folder to add additional folders to the list.
- Once done, pick Next.
![Choose what to sync Choose what to sync]()
- Now you can select to sync items to be visible on your computer.
- Finally, press Start and wait till the sync is complete. Your files are now being backed up.
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Ron Franklin. AES vs. RSA Encryption: What Are the Differences?. Precisely. CLM Software.
- ^ Sergiu Gatlan. Free decryptor released for AstraLocker, Yashma ransomware victims. Bleeping Computer. Cybersecurity and Technology News.