Flash-Search browser hijacker (virus) - Free Instructions
Flash-Search browser hijacker Removal Guide
What is Flash-Search browser hijacker?
Flash-Search is a plugin created by crooks that changes the main browser settings
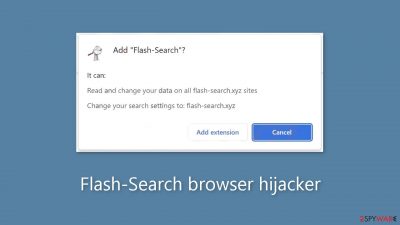
Flash-Search is a browser hijacker that can alter important settings such as the homepage, new tab address, and search engine. More specifically, it redirects to flash-search.xyz and its bogus search engine. The hijacker's developers want to force people to use only specific channels for browsing in order to generate revenue through PPC advertising and data collection.
The browser extension provides no additional benefits to users that are not available in the default browser. The add-on exists solely to allow fraudsters to profit. Users may notice an increase in commercial content as well as pop-ups, banners, and surveys while the machine is affected.
The app may also cause redirects to dangerous websites, which may trick users into providing personal information or downloading PUPs (potentially unwanted programs)[1] and malware. This is because the creators are unconcerned about user privacy or security and rely on rogue advertising networks to deliver advertisements.
You should be concerned about more than just modified settings. The application may also use cookies[2] to collect information about your browsing activities. This information can then be sold to the same advertising networks or other third parties and used to target you with even more advertisements. Use a maintenance tool like FortectIntego to automatically clear your browsers' cookies and cache.
| NAME | Flash-Search |
| TYPE | Browser hijacker; potentially unwanted program |
| SYMPTOMS | The main settings of the browser get changed, like the homepage, new tab address, and search engine |
| DISTRIBUTION | Shady websites, deceptive ads, software bundling, web stores |
| DANGERS | The extension may lead to dangerous websites; display misinformation, inaccurate search results; track browsing, and collect data |
| ELIMINATION | Remove the extension by going to your browser settings |
| FURTHER STEPS | Use FortectIntego to fix any remaining damage and optimize the machine |
Distribution dangers
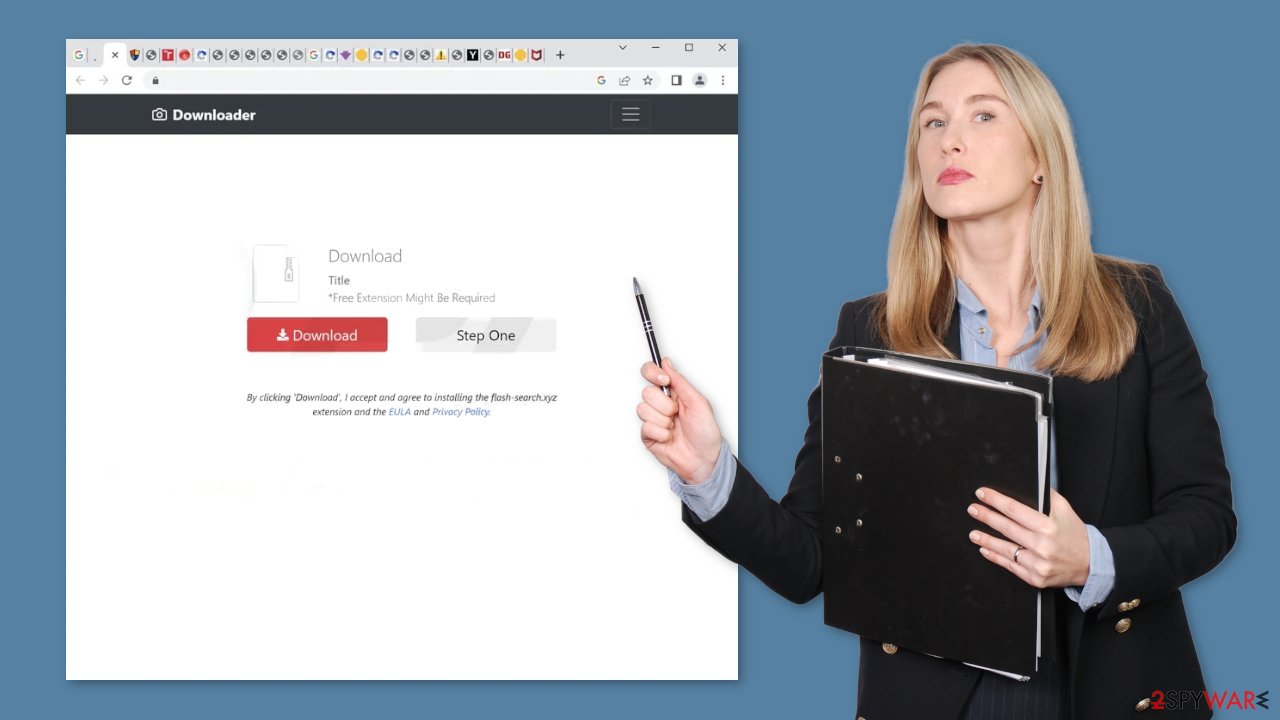
You may have downloaded the add-on on your own, believing it would assist you with daily tasks, or you may have added it by accident without realizing it. Leaving that aside, how could you have discovered it? Users are frequently infected with hijackers while browsing shady websites that engage in illegal activities. Because they are unregulated, such pages are full of deceptive ads and sneaky redirects.
You may have come across a Flash-Search promotional page that talked about all the amazing functions and features, and you believed it. Fraudsters have learned how to create professional-looking websites and write persuasive messages, so it is now up to users to determine whether the programs they want to use are safe. That is why it is critical to conduct thorough research.
Enter the name of the promoted plugin into the search box and see what results you get. You may have noticed that when you search the names of hijackers, there aren't many results. Check to see if the add-on is listed on official websites, and look for reviews, ratings, and how many users it has. If you cannot find any of this information, it is best to be cautious and instead select an extension with a lot of feedback.
Your browser could also have been hijacked by a PUA that is hiding in your system and making all of the changes invisible. These programs are typically downloaded from freeware distribution platforms. They make money by including additional programs in the installers and failing to disclose this clearly on the website, hoping that most people will not notice.
Remove the unwanted extension
You can remove browser add-ons by going to your settings. Find the list of extensions installed in your browser and remove the Flash-Search. We show how to do that in the guide below:
How to prevent from getting browser hijacker
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Potentially unwanted program. Wikipedia, the free encyclopedia.
- ^ What are Cookies?. Kaspersky. Home Security Blog.
- ^ Will Dormann. Bundled Software and Attack Surface. Cmu. Carnegie Mellon University Software Engineering Institute Blog.










