FLKR ransomware / virus (Removal Guide) - May 2019 update
FLKR virus Removal Guide
What is FLKR ransomware virus?
FLKR ransomware is a crypto malware that is seeking to make victims' files useless

FLKR ransomware – a malicious cryptovirus which has been targeting victims from all around the world. It is designed to encrypt files with Blowfish symmetric-key block cipher[1] and make them inaccessible. Additionally, all encrypted files are marked with the following extensions:
- ._morf56@meta.ua_
- .+jabber-theone@safetyjabber.com
- .__murzik@jabber.mipt.ru
Victims who want to get their files back are urged to reach the hackers via morf56@meta.ua or fhmjfjf@default.rs email addresses. However, if you don't want to get scammed, use anti-malware software to remove the virus and then recover your files from backup.
| Name | FLKR |
|---|---|
| Type | Ransomware |
| Extension |
|
| Ransom Note | INSTRUCT.txt; INSTRUCTIONS.txt |
| Email address | morf56@meta.ua; fhmjfjf@default.rs; murzik@jabber.mipt.ru |
| Decryptable | No |
| Distribution | Malspam campaigns, rogue websites |
| Elimination | FortectIntego is the best tool to uninstall FLKR virus |
Unlike other viruses, FLKR doesn’t pay much attention to .txt, .mp3, and .avi files, as it doesn’t consider them valuable. However, it can encrypt documents, databases, programs and other data. Once the main programs’ component – flkr.exe file finishes its dirty job, an INSTRUCT.txt file is created.
This file stores the short message from authors of the virus, which state that all information on the compromised computer is encrypted “with a strong” password, and those who want FLKR decryptor should get in touch with the criminals via indicated email addresses and be prepared to pay the ransom.
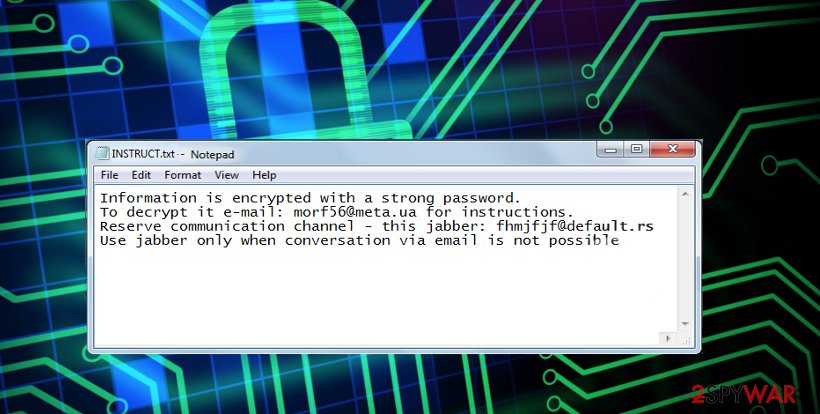
In case the victim doesn’t get a response from criminals after writing to the given email, one can use an alternative communication channel and get in touch with culprits via Jabber, also known as an IM service which is based on XMPP[2]. Here is the extract of the ransom note by FLKR virus:
Information is encrypted with a strong password.
To decrypt it e-mail: morf56@meta.ua for instructions.
Reserve communication channel – this jabber: fhmjfjf@default.rs
Use jabber only when conversation via email is not possible
However, we can save you some time and inform you about what is going to happen next. Criminals will ask you to buy digital currency, usually, Bitcoins, and send them to them as a ransom. The ransom price is likely to be high (starting with $500 or so and up), but chances to recover files will be low.
First of all, criminals rarely decide to help victims and do anything to restore their files. Besides, by paying the ransom, you would encourage them to spread the virus further — so please, do not do that! Victims already are getting aware of ransomware menace and paying less ransom than before, so it would be great if you would join this fight against ransomware as well.

Therefore, instead of wasting your hard-earned money on criminals, consider removing the virus with a proper anti-malware tool. For FLKR removal, use a good anti-malware program, for instance, FortectIntego. This is the safest method to get rid of this dangerous cyber threat as it is sophisticated and designed to corrupt Windows Registry. This results in more complicated elimination procedure.
We do not recommend you remove FLKR virus manually since it will most likely result in computer damage. However, if you are unable to download security software, immediately check the instructions below showing how to deactivate the ransomware. Additionally, there are ways how you can get back the access to your files without paying the ransom.
The new version of the ransomware targets Russian-speaking computer users
Cybersecurity researchers have recently noticed a new version of FLKR ransomware which is designed to infect computers in Russia particularly. According to the analysis, it appends .__murzik@jabber.mipt.ru extension after the data is encrypted and drops INSTRUCTIONS.txt ransom note.
The message is written in Russian language as the following:
Хотите расшифровать Ваши файлы? Пишите на джаббер (xmpp): murzik@jabber.mipt.ru (можете писать в оффлайн если нас нет в онлайне) Ваш PIN: [redacted 2 numbers]
Once again, the hackers encourage their victims to reach them via murzik@jabber.mipt.ru on Jabber. Although, now people can also get in touch with them offline, by using the indicated PIN. Despite the fact that it is currently unknown how much money the attackers demand to pay, we want to warn you not to pay the ransom!
Ransomware distribution techniques explained
Even though there are numerous information sources, saying how to protect against ransomware attacks, people continue to stay inattentive and infect their computers with this dangerous threat. Likewise, we want to explain you one of the most common ways how ransomware spreads. Here are some of the distribution techniques:
- Exploit kits;
- Malicious online ads;
- Malspam campaigns;
- Infected software-bundles.
Most of the cyber threats are distributed via malicious spam emails. Therefore, computer users should be extremely cautious when opening and clicking on the content of the letter. There is a high risk that it might hold an innocent looking file which is, in fact, the payload of the ransomware.
Also, BedyNet.ru[3] experts encourage you to stay away from shady-looking websites that aggressively suggest you play a particular game, fill out a survey, or install specific plug-ins or applications. If you feel that a particular Internet site desperately wants you to do something or add something to your computer, better be careful. You risk installing untrustworthy programs and infecting your computer with useless apps!
Learn how to uninstall FLKR virus safely
If you believe that you can remove FLKR on your own, we would like to warn you about the potential threats and encourage to choose a more reliable way — automatic elimination. Unfortunately, this dangerous malware can be programmed to infiltrate the system with other malicious programs that you will not be able to identify.
Therefore, complete FLKR removal requires not only specific IT skills and knowledge but also time. For this reason, we suggest you save your precious time and ensure the malware elimination to professional security software. These products are designed to help novice computer users and protect their systems at all times.
You can uninstall FLKR virus with FortectIntego, SpyHunter 5Combo Cleaner, or Malwarebytes. However, if you cannot install the antivirus, the malware might be still active. Learn how to deactivate the ransomware by following the instructions below and later you will be able to recover the encrypted data without paying the ransom.
Getting rid of FLKR virus. Follow these steps
Manual removal using Safe Mode
Here is the way how you can deactivate FLKR virus by booting your computer into Safe Mode with Networking.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove FLKR using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of FLKR. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove FLKR from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by FLKR, you can use several methods to restore them:
Run Data Recovery Pro
If you have allowed the virus to encrypt your files (we are sure you did that unintentionally), now you need to do something to restore them. Bear in mind that it is nearly impossible to recover encrypted data, so methods and tools we suggest trying MIGHT help to recover files, but if they do not, do not be disappointed. Data Recovery Pro should help you to recover at least some of your data.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by FLKR ransomware;
- Restore them.
Find those Previous File Versions
You are lucky if you enabled System restore function before the ransomware attack. It means that you can restore your files now. Follow these easy steps to restore your data:
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from FLKR and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.





















