Gatq ransomware (Free Guide)
Gatq virus Removal Guide
What is Gatq ransomware?
Gatq – a malicious Windows virus that could result in personal data loss

Gatq ransomware represents a dangerous computer virus that threatens its victims with the locking of their personal data as a way to extort funds. Typically, this malware finds its way into Windows systems through dubious software cracks and other unauthorized applications. Once it gains a foothold, it swiftly encrypts all personal files on the machine using a complex RSA algorithm and stamps them with the .gatq extension for easy identification.
This procedure does not result in irreversible data damage, but it effectively bars the user from accessing the content without the use of a unique decryption key, which is akin to entering a password. The ransomware employs an online ID protocol ensuring each victim receives a distinct, specifically crafted key. Consequently, the retrieval of encrypted files without the appropriate decryption tools becomes exceedingly challenging.
Regrettably, the decryption keys are securely held only by the cybercriminals orchestrating the Gatq ransomware attack. Upon successful data encryption, the miscreants relay their demands in a note labeled _readme.txt, stating that the victims must pay either $980 or $490 in Bitcoin to procure the decryption software needed to restore access to their files. For the purposes of negotiation, they provide the following email addresses:
- support@freshmail.top
- datarestorehelp@airmail.cc.
While these cyber felons may be the sole parties capable of delivering the required decryption tool, it does not mean that there are no alternatives for data recovery that don't involve parting with your hard-earned money. Thankfully, this particular strain of Djvu can be combated by security experts who have developed alternate decryption tools. These may not prove successful for all, but they're certainly worth a shot. Additionally, there are other recovery options available if no prior backups were made – see the information below for further details.
| Name | Gatq virus |
|---|---|
| Type | Ransomware, file-locking malware |
| File extension | .vvoo extension affixed to all personal files, rendering them useless |
| Family | Djvu |
| Ransom note | _readme.txt dropped at every location where encrypted files are located |
| Contact | support@fishmail.top and datarestorehelp@airmail.cc |
| File Recovery | Without backups, there's no foolproof recovery method for encrypted files. Options include: paying the ransom (not advised due to potential monetary loss), using Emisoft's decryptor tool (limited success) or third-party recovery software |
| Malware removal | After disconnecting the computer from the network and the internet, do a complete system scan using the SpyHunter 5Combo Cleaner security program |
| System fix | Upon installation, the malware can inflict significant damage to critical system files, leading to system instability issues like crashes and errors. The automatic repair of any such damage is feasible with the use of FortectIntego PC repair |
Extortion presented as a service
Upon falling into the trap of a ransomware attack, victims are typically confronted with a communication often referred to as a ransom note. This note usually provides directions about how the victim can remit a ransom to the attackers as a favor for the decryption of their data, which the ransomware has encrypted.
In these ransom notes, there may be a stipulated time limit for the ransom payment, with potential threats of escalated harm or data annihilation if the payment is not made timely. However, Djvu variants refrain from resorting to such tactics, opting for a more professional approach. These ransom notes usually manifest as text files, images, or web pages on the victim's computer or device.
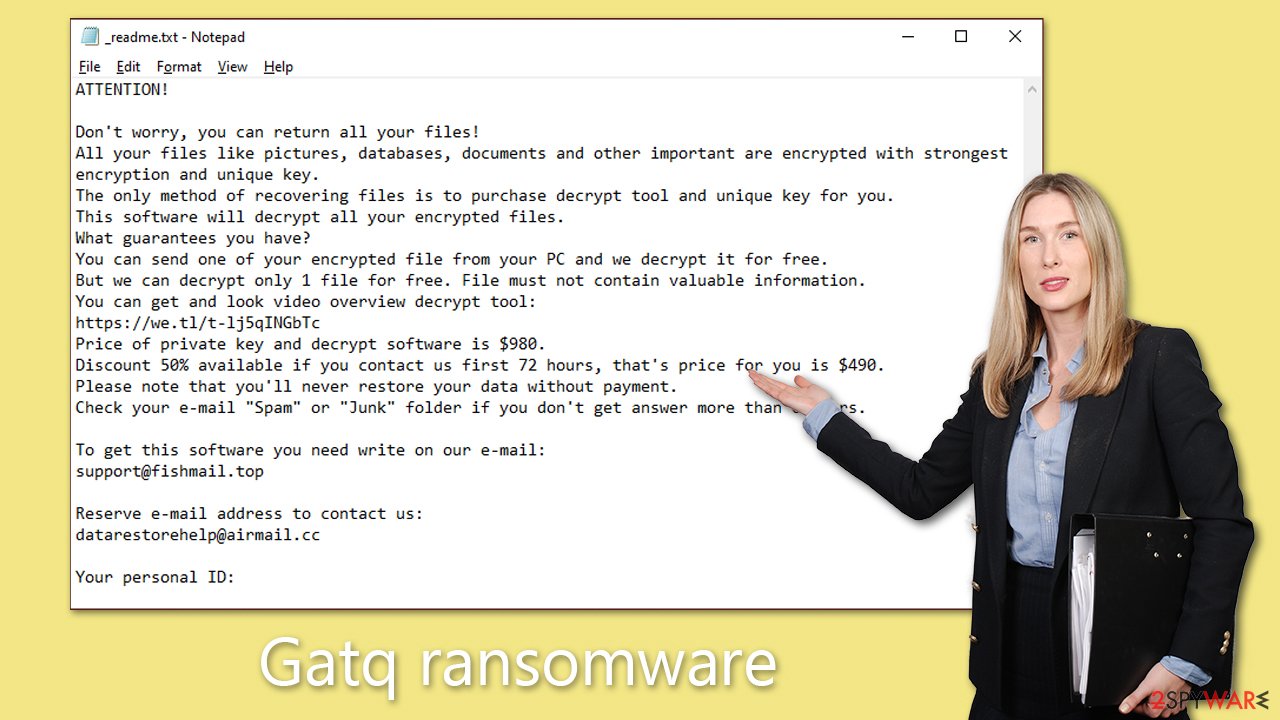
With the Gatq ransomware, the ransom note pops up immediately after the encryption of files is completed. The message reads as follows:
ATTENTION!
Don't worry, you can return all your files!
All your files like pictures, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-sD0OUYo1Pd
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that's price for you is $490.
Please note that you'll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don't get answer more than 6 hours.To get this software you need write on our e-mail:
support@freshmail.topReserve e-mail address to contact us:
datarestorehelp@airmail.ccYour personal ID:
Cybercriminals often employ various strategies to gain the trust of their victims, such as offering discounts on the cost of decryption tools or providing a “complimentary” test decryption service. These tactics, however, are deceptive maneuvers designed to lure victims into a false sense of security and cooperation.
Despite these seemingly considerate gestures, it is critically important to remember that such offers do not guarantee any reliable or ethical conduct from these attackers. Specifically, in the case of the Gatq ransomware, there is no concrete assurance that the perpetrators will hold true to their promises and deliver the necessary recovery tool after payment is made. These hackers operate within an illegal framework, and their primary goal is personal gain, making their assurances highly unreliable.
Malware removal and data recovery
The understanding of ransomware's encryption process and the functioning of malware is often skewed with misinformation. It's a common misconception that simply running a full system scan with security software or trying to rename files to their original state by adding back the original extension can help restore encrypted files.
However, the reality of the situation is more complex. Ransomware cleverly locks bits of data within each file using a sophisticated alphanumeric sequence that's virtually impossible to decipher. This is what makes a ransomware attack such a grave concern, as it can lead to the irreversible loss of data.
That said, falling into despair won't help, as it is not a lost cause. There's always a glimmer of hope that data recovery could be possible, perhaps not immediately, but potentially in the future. Regardless, your initial move towards recovery should be to ensure the complete removal of Gatq ransomware using trusted security software like SpyHunter 5Combo Cleaner or Malwarebytes. If malware continues to disrupt this process, you could switch to the Safe Mode environment and carry out the removal from there (you'll find instructions on how to achieve this at the end of this article).
After successfully removing the malware, you can then shift your focus toward data recovery. We recommend beginning with Emsisoft's decryption tool. This tool has proven successful in certain cases for decrypting files that were encrypted by Djvu variants. However, keep in mind that it may take a while before this recovery method becomes available to you.
- Download the app from the official Emsisoft website.
![Gatq ransomware Gatq ransomware]()
- After pressing Download button, a small pop-up at the bottom, titled decrypt_STOPDjvu.exe should show up – click it.
![Gatq ransomware Gatq ransomware]()
- If User Account Control (UAC) message shows up, press Yes.
- Agree to License Terms by pressing Yes.
![Gatq ransomware Gatq ransomware]()
- After Disclaimer shows up, press OK.
- The tool should automatically populate the affected folders, although you can also do it by pressing Add folder at the bottom.
![Gatq ransomware Gatq ransomware]()
- Press Decrypt.
![Gatq ransomware Gatq ransomware]()
From here, there are three available outcomes:
- “Decrypted!” will be shown under files that were decrypted successfully – they are now usable again.
- “Error: Unable to decrypt file with ID:” means that the keys for this version of the virus have not yet been retrieved, so you should try later.
- “This ID appears to be an online ID, decryption is impossible” – you are unable to decrypt files with this tool.
You could always resort to specialized data recovery software if this method is unsuccessful.
- Download Data Recovery Pro.
- Double-click the installer to launch it.
![Gatq ransomware Gatq ransomware]()
- Follow on-screen instructions to install the software.
- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders which you want the files to be recovered from.
![Select what to recover Select what to recover]()
- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.
![Select Deep scan Select Deep scan]()
- Press Scan and wait till it is complete.
![Scan Scan]()
- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.
Other tips
The Gatq ransomware might tamper with your “hosts” file, creating barriers to accessing websites dedicated to security. To counter this problem, you must remove the said file. Upon deletion, Windows will recreate it, thus lifting the imposed limitations on specific website access. Here are the necessary steps:
- Make sure that “Hidden files” are set to be visible.
- Navigate to this directory: C:\Windows\System32\drivers\etc.
- Find the “hosts” file and eliminate it by using the keyboard shortcut Shift + Del.
Now, it's crucial to attend to any system damages incurred due to the malware. FortectIntego is a robust software utility designed to address the damages caused by malicious software. It achieves this by executing an in-depth scan of your computer to identify corrupted or missing files, replacing them with their functional counterparts. This process aids in mitigating the negative impacts caused by malware, including alterations to the Windows Registry or the disappearance of essential system files.
Moreover, this utility examines and rectifies any operating system-related issues, such as faulty or missing DLL files. It's also equipped to fix complications arising from the boot process. Once the repair process is concluded, your computer should regain its stability and optimal performance level.
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.









