GermanWiper (Improved Instructions) - Removal Guide
GermanWiper Removal Guide
What is GermanWiper?
GermanWiper – a new kind of ransomware that executes itself via PowerShell and destroys file data

GermanWiper is a ransomware-type virus that targets companies and users based in Germany via the spam email attachments which come with names such as ctNfy_Entschluesselungs_Anleitung.html, eRq7E_Entschluesselungs_Anleitung.html, RadEW_Entschluesselungs_Anleitung.html, Unterlaged_Lena_Kretschmer.zip,[1] and others.
As soon as the malicious file attached to the email is launched, it calls up a PowerShell[2] command that executes the main malware program on the computer. GermanWiper ransomware then rewrites all the files located on the system with zero-based code, which consequently corrupts them.
Despite that, GermanWiper virus appends fake extensions (for example, .ctNfy, .eRq7E, .RadEW, .08kJA, .AVco3)to make victims believe that an actual encryption algorithm was used to encrypt data. However, paying the ransom is useless, as the files get corrupted as soon as the first PowerShell command is launched. Attackers ask for 0.15 BTC for the alleged file decryption tool that actually does not even exist in the ransom note that is named after the bogus file extension and comes in HTML format.
| Name | GermanWiper |
|---|---|
| Type | Ransomware |
| Target | German and English-speaking people |
| Aim | To destroy files and urge ransom for the fake decryption software |
| Fake extensions | Even though the malware does not encrypt data, it adds appendixes for confusing victims. Examples: ctNfy, .eRq7E, .RadEW, .08kJA, .AVco3 |
| Ransom note | ctNfy_Entschluesselungs_Anleitung.html, eRq7E_Entschluesselungs_Anleitung.html, RadEW_Entschluesselungs_Anleitung.html |
| Price | 0.15 BTC ($1500) |
| Detection names | Win32:Malware-gen, Ransom.FileCryptor, RDN/Generic PWS.y, Trojan.Win32.Yakes.ywph, Trojan.GenericKD.32208067 (B), TR/AD.MalwareCrypter.sbepq, etc. |
| Distribution | Via email messages. A fake CV is sent carrying the malicious payload in a ZIP file |
| Identification | Use FortectIntego software to find malicious content on the infected system |
A large number of reports have already echoed throughout the Internet claiming about the surprising appearance of GermanWiper. Several news sources have commented that the malicious payload is distributed via email messages and pretends to be a CV from “Lena Kretschmer” which is provided as a ZIP file that carries the malware in an LNK file.[3]
Victims worries about the activities of GermanWiper have also flooded the Web. People claim that the find files locked with rogue appendixes and receive huge ransom demands. Even though the messages are written in the German or English languages, some victims have found the IP address of the ransomware activity coming even from France.
It seems that the main targets of GermanWiper are German-speaking users but this malware supposedly has been distributed and controlled from more countries, not only Germany. However, we urge all users to be careful and try not to fall for these crooks' tricks. Note that data decryption is not a necessity as there is NOTHING to decrypt!
As long as GermanWiper virus wipes out all file information but does not encrypt it, decryption software will not help you here and the only slight possibility of recovering your documents is by restoring your infected system. Do not keep the malware on the system for a longer time as it might initiate other malicious actions, for example, inject a trojan infection.

If GermanWiper is placed on a computer system, various antivirus engines can detect the ransomware differently. According to Virus Total file information,[4] the most popular variants are Win32:Malware-gen, Ransom.FileCryptor, RDN/Generic PWS.y, Trojan.Win32.Yakes.ywph, Trojan.GenericKD.32208067 (B), TR/AD.MalwareCrypter.sbepq.
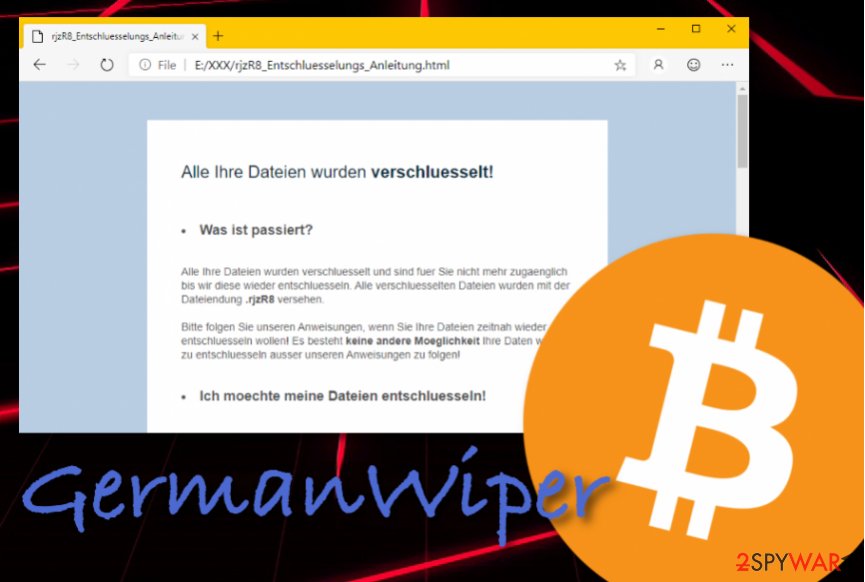
If you happened to be unlucky and got GermanWiper installed on your computer system, you will supposedly be provided with a message looking like this or something very similar:
Alle Dateien Ihre wurden verschluesselt!
Was ist passiert?
Alle Ihre Dateien wurden verschluesselt und sind fuer Sie nicht mehr zugaenglich bis wir diese wieder entschluesseln. Verschluesselten Dateien wurden alle mit der Dateiendung .ctNfy Versehen.
Bitte folgen Sie unseren Anweisungen, wenn Sie Ihre Dateien zeitnah wieder entschluesseln wollen! Es besteht keine andere Moeglichkeit Ihre Daten wieder zu entschluesseln ausser unseren Anweisungen zu folgen!
Ich moechte meine Dateien entschluesseln!
Kein Problem! Um Ihre Dateien zu entschluesseln, benoetigen Sie unsere Entschluesselungssoftware, diese steht zum Kauf fuer umgerechnet ca. $ 1,500 bereit.
Der Betrag ist ausschliesslich in Bitcoin an die untenstehende Adresse zu zahlen.
Welche Garantien habe ich?
Uns interessiert nicht wer Sie sind oder was fuer Dateien Sie auf Ihrem Computer haben, wir sind ausschliesslich daran interessiert Ihnen die Entschluesselungssoftware zu verkaufen. Schlechtes Business spricht sich herum, sollten wir Ihre Dateien nicht entschluesseln, wuerde in Zukunft niemand unsere Entschluesselungssoftware kaufen – Was nicht in unserem Interesse liegt.
Wo bekomme ich Bitcoins?
Bitcoin koennen Sie schnell und einfach kaufen, zB mit Kreditkarte, GiroPay oder (SOFORT) Ueberweisung. Folgt eine Auflistung es populaerer Tauschboersen und the Bitcoin Marktplaetzen:
Coinmama – https://coinmama.com/
Bitpanda – https://www.bitpanda.com/
AnyCoinDirect – https://anycoindirect.eu/
Bitcoin.de – https://www.bitcoin.de/
The BTC the Direct – https://btcdirect.eu/de-at
Es gibt noch weitere moeglichkeiten the Bitcoin zu erwerben, sollte der keine gelisteten fuer Sie funktionieren, hilft Ihnen eine kurze Google Suche.
Bitcoins habe die ich gekauft
Senden Sie den folgenden Betrag an fuer die Sie generierte the Bitcoin Adresse is:
Betrag
0.15038835 the Bitcoin<…>
GermanWiper removal is a necessity that you need to complete as soon as possible if you want to bring your computer back to its previous condition. We suggest using a piece of reputable software for detecting malicious components on your system that were brought by the ransomware virus. An antivirus tool such as FortectIntego should be helpful.
Note that you CANNOT remove GermanWiper on your own as there are too many risks of completing damaging mistakes or skipping malicious content. Ransomware infections can leave harmful keys in the Registry section or plant several hazardous processes in the Task Manager that need to be terminated for full virus elimination.
Knowing ransomware distribution techniques helps to protect yourself from cyber attacks
Ransomware viruses are one of the sneakiest and dangerous cyber threats distributed throughout the cybersphere. This type of malware comes delivered in email spam campaigns. Criminals pretend to be from reputable organizations, for example, banks, or some types of companies that offer great deals, etc.
Mostly, these messages come with an additional file or hyperlink that needs to be entered for “further information”. This is the exact location where the malicious payload is hidden and waiting for the user to access it. Our suggestion would be not to open any attached components before scanning them with reputable anti-malware software.
Continuously, ransomware might have more than one spreading directory. Some of this malware is also found on secondary networks, especially, piracy ones. Sources such as The Pirate Bay, Torrents, eMule, and similar need to be avoided at all costs. Better download videos and products from reliable locations only.
The termination of the GermanWiper ransomware
Even though GermanWiper ransomware does not encrypt files and documents, it is still very dangerous in its own way. Components affected by this malware are CORRUPTED and can easily be permanently lost. However, if you want to have a chance of recovering your losses, you can try booting your computer with System Restore or Safe Mode with Networking.
If you want to prevent the same activities from appearing again, you need to remove GermanWiper from your Windows computer system and this needs to be done IMMEDIATELY after the malware is detected. If you are likely to locate infected objects automatically, you can do this by downloading software such as FortectIntego, SpyHunter 5Combo Cleaner, or Malwarebytes.
After GermanWiper removal is successfully carried out, it is about time to take good care of your future data. If you have any important files left or are going to create some soon, you should store copies of them on remote servers or devices. Specialists from LosVirus.es[5] suggest using USB drives, iCloud or Dropbox services.
Getting rid of GermanWiper. Follow these steps
Manual removal using Safe Mode
If you want to try to disable malware-laden processes on your machine, you should boot the system by using Safe Mode with Networking:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove GermanWiper using System Restore
Try restoring lost settings and data by using System Restore on your Windows computer. You can find the instructions here:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of GermanWiper. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from GermanWiper and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Catalin Cimpanu. GermanWiper ransomware hits Germany hard, destroys files, asks for ransom. ZDNet. Technology News, Analysis, Comments and Product Reviews.
- ^ Margaret Rouse. PowerShell. Search Security. Tech Target.
- ^ Catalin Cimpanu. GermanWiper ransomware hits Germany hard, destroys files, asks for ransom. ZDNet.com. News articles.
- ^ 45 engines detected this file. Virus Total. File information.
- ^ NOTICIAS SOBRE SEGURIDAD Y VIRUS. LosVirus. Virus and cybersecurity information.





















