Globe Earth browser hijacker (Free Guide)
Globe Earth browser hijacker Removal Guide
What is Globe Earth browser hijacker?
Globe Earth is a browser hijacker that changes your homepage and other browser parameters

Globe Earth is a potentially unwanted application that can take over your homepage, new tab, and other browser settings as soon as it is installed on Google Chrome, Mozilla Firefox, MS Edge, or another compatible browser. If that happened to you unexpectedly, that means that your browser has been hijacked.
Users typically don't install browser hijackers intentionally, although the installation is always performed manually – either after they are tricked by a dubious ad, get tricked by promising features, or come with freeware[1] from third-party sources.
While Globe Earth is advertised as an app that can allow you to change the wallpaper of the front page, show time, and weather. However, the main goal of it is to make sure that users are exposed to as many advertisements as possible, and they do that by inserting promotional links and ads at the top of search results and other places.
| Name | Globe Earth |
| Type | Browser hijacker, potentially unwanted application |
| Distribution | Bundled software, third-party websites, misleading ads |
| Symptoms | The extension takes over your homepage and new tab address, placing promotional links as the top search results. It also displays intrusive ads on various websites you visit |
| Risks | Installation of other potentially unwanted programs/malware, personal data disclosure to unknown parties, monetary loss |
| Removal | You can eliminate the browser extension by accessing your browser's settings. A scan with powerful security software SpyHunter 5Combo Cleaner is also recommended |
| Other tips | After removing all browser hijackers and other PUPs from your computer, clean your web browsers and repair any damaged system files. You may accomplish everything automatically with FortectIntego |
Spreading techniques
A browser hijacker's developers largely rely on how the software is promoted and spread for its popularity. The Globe Earth, unfortunately, employs fraudulent distribution practices common among potentially unwanted programs.
Most people prefer to download software for free from third-party websites, not realizing that this is where most malicious or unwanted apps originate. Oftentimes, installation steps and clickthrough stages are skipped without reading the instructions, allowing optional components to enter the system. This practice is referred to as software bundling.[2]
If you want to avoid this, never take your eyes off the installation process of any apps you download from unofficial sources. And when there's an opportunity to do so, always select Advanced/Custom options and uncheck all of the pre-ticked checkboxes. You should also be aware of deceitful components such as fine-print text or buttons that are strategically placed out of sight.
However, you should always avoid using software cracks and other sites that offer pirated software because you might end up infected with ransomware[3] or other dangerous malware. Not only is this methodology illegal, but it's also incredibly unsafe for your computer system. Pirated websites are insecure and often cause more harm than good.

Removal of Globe Earth browser hijacker
Although browser hijackers are unlikely to infect your computer with malware, the top-of-the-page ads might include advertisements for potentially unwanted programs. So, if you have a PUP on your device, you might start seeing ads for other browser hijackers or adware.
Not only does Globe Earth shows ads, but it also monitors your data. This surveillance can include anything from search queries and websites visited to clicked links and technical device information. While this might not be a problem for some people, others may want to avoid using this type of software due to privacy concerns.
Therefore, we highly recommend removing the browser hijacker, along with any other potentially unwanted or malicious applications. You can start by checking your browser's unwanted extensions – you can access them as follows:
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.
![Remove extensions from Firefox Remove extensions from Firefox]()
MS Edge
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
Internet Explorer
- Open Internet Explorer, click on the Gear icon (IE menu) on the top-right corner of the browser
- Pick Manage Add-ons.
- You will see a Manage Add-ons window. Here, look for suspicious plugins. Click on these entries and select Disable.
![Remove add-ons from Internet Explorer Remove add-ons from Internet Explorer]()
Some potentially unwanted programs might be installed on the system level, which would make their presence much more impactful. For example, a browser extension only affects the browser it is installed on, while a program on the system level might install that same extension to all used browsers and perform background tasks that might be invisible to the user.
In most cases, such dangerous applications can be quickly and easily terminated with the help of SpyHunter 5Combo Cleaner or Malwarebytes security software. By scanning your system with anti-malware, you can be sure that it's secure and that all the malicious components are removed at once. If you would like to remove system-level apps manually, please follow these steps (although keep in mind that it might not be as effective as the automatic method):
Windows
- Enter Control Panel into the Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till the uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
Mac
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)
![Uninstall from Mac 1 Uninstall from Mac 1]()
To thoroughly remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
![Uninstall from Mac 2 Uninstall from Mac 2]()
Finally, you should do something about data monitoring, as even after the Globe Earth browser hijacker removal, its placed cookies and other trackers may remain on your device. Therefore, you should make sure that all these leftover files are eliminated, and the easiest way to do it is by employing FortectIntego repair and maintenance app. For a manual solution, follow these steps:
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content, and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
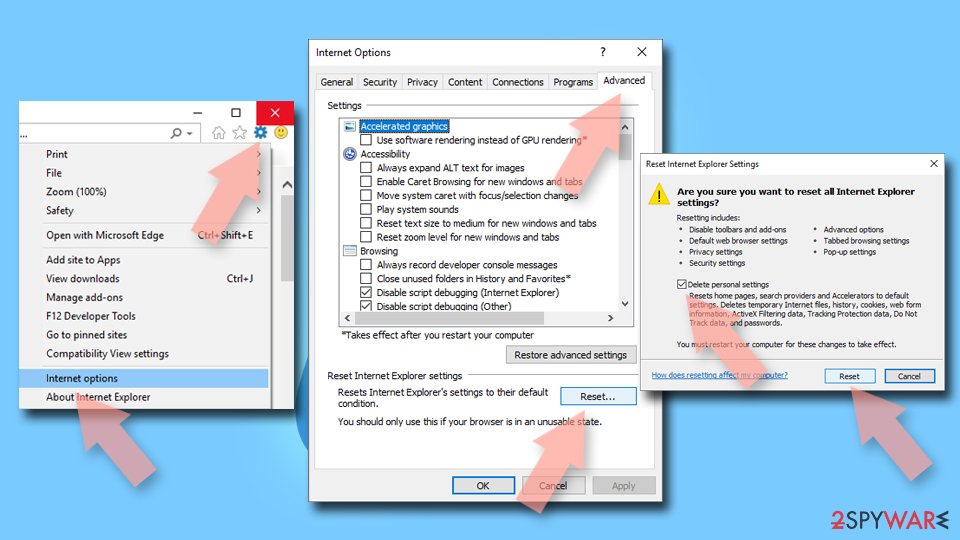
Internet Explorer
- Click on the Gear icon > Internet options and select the Advanced tab.
- Select Reset.
- In the new window, check Delete personal settings and select Reset.
![Reset Internet Explorer Reset Internet Explorer]()
How to prevent from getting browser hijacker
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ What Is Freeware?. Lifewire. Tech News, Reviews, Help & How-Tos.
- ^ Bundled software. Computer Hope. Free computer help.
- ^ Ransomware. Imperva. Application and data protection.