(Fixed) Google chrome critical error red screen scam
Google Chrome Critical Error Removal Guide
What is Google Chrome Critical Error?
Google Chrome Critical Error – is the message that is a part of a tech support scam campaign
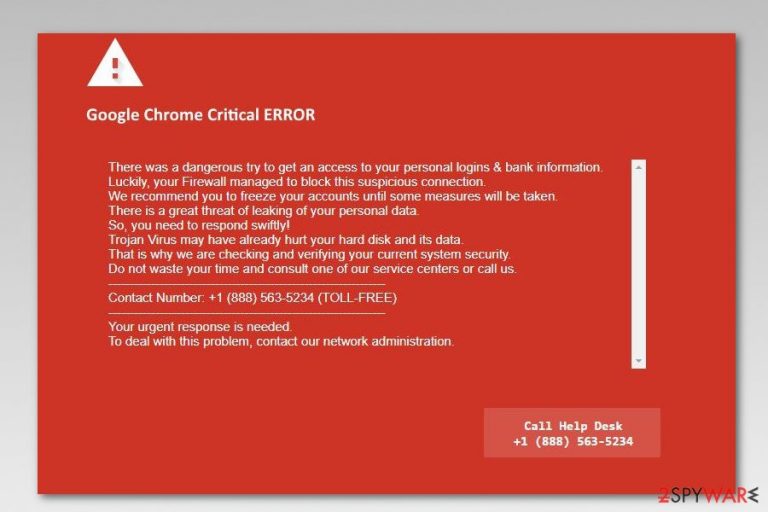
Google Chrome Critical Error is a fake pop-up alert that may appear when you're browsing the internet. Visually, the red page resembles a legitimate warning that appears when users try entering a dangerous domain. Instead, users are presented with a lengthy message, claiming that a trojan horse may have already damaged their hard disk and some of their personal data is at the risk of compromise.
To “fix” the issue, victims are then prompted to call the “Help Desk” via the provided phone number. No matter how convincing the Red screen virus seems, you should never fall for dialing the number given in the fake alert because scammers behind it can trick you into installing malware, paying for useless services, or giving them remote access to your PC.
| SUMMARY | |
| Name | Google Chrome Critical Error Red Screen |
|---|---|
| Type | Adware |
| Sub-type | Technical support scam |
| Related scams |
|
| Infiltration method | Software bundling, deceptive websites |
| Main dangers | Money loss, personal data exposure to cybercrooks |
| Elimination | Automatic – using anti-malware; manual – using instructions below |
| Optimization and recovery | Use FortectIntego to fix virus damage and restore corrupted system files (for example, Windows Registry) |
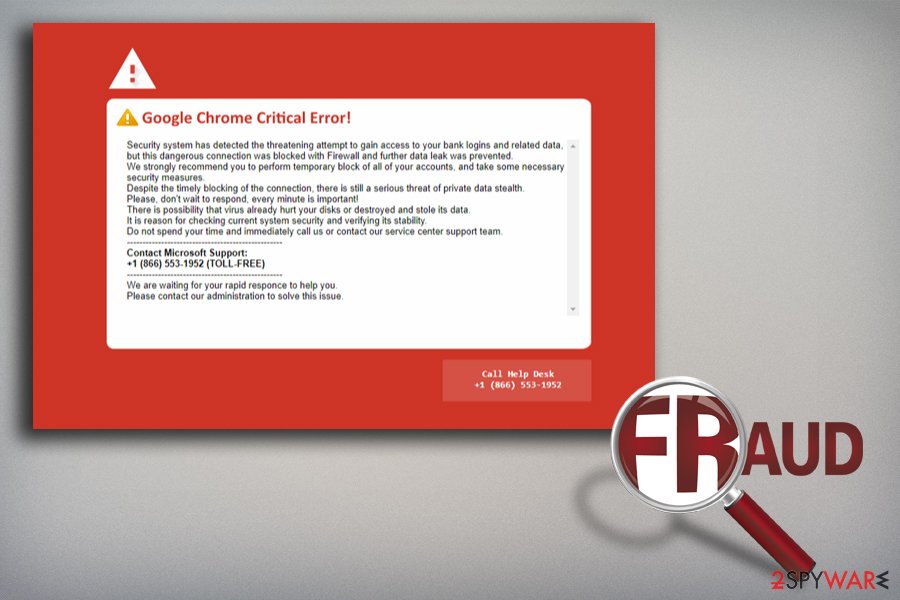
Google Chrome critical error red screen virus is a technical support scam that belongs to the group of Critical ERROR scam category that targets Google Chrome, Internet Explorer, Microsoft Edge, and Mozilla Firefox web browsers. Hence, Chrome users are also in the target eye of tech support scammers.
Just like many other online scams, this red screen error also aims to trick users into calling fake technicians due to computer infection or possible threats to their private information. Authors of this scam use the +1(888)-562-5234 phone number. However, security specialists from Los Virus[1] warn that crooks might use countless other numbers.
Most of the time, users encounter Red screen virus when their machines are infected with adware.[2] The ad-supported application, which may have arrived on the system in a software bundle, might also:
- redirect to other commercial or potentially dangerous websites;
- display ads, pop-ups or banners;
- turn random texts into hyperlinks;
- provide fake shopping offers or discounts;
- spread malware-laden ads.
However, the main task of this potentially unwanted program is to open the affected browser’s tab and shows the following error message:
Google Chrome Critical ERROR
There was a dangerous try to get an access to your personal information & bank information.
Luckily, your Firewall managed to block this suspicious connection.
We recommend you to freeze your accounts until some measures will be taken.
There is a great threat of leaking of your personal data.
So, you need to respond swiftly!
Trojan Virus may have already hurt your hard disk and its data.
That is why we are checking and verifying your current system security.
Do not waste your time and consult one of our service centers or call us.Contact number + 1 (888) 563-5234 (TOLL-FREE)
Your urgent response is needed.
To deal with this problem, contact our network administration.
However, calling the authors of this scam will bring you even more computer-related problems. Crooks might want to sell you useless security software, get remote access to your PC, install malware[3] or steal personal information. The main goal of tech support scams is to make victims call the provided number, and then it is relatively easy for crooks to convince users that their computer and personal safety is in grave danger.
If redirects to this site keep reappearing, you should remove Google Chrome Critical Error virus immediately. Keep in mind that this PUP may have arrived in your system as a browser extension or any other potentially unwanted program, so system investigation is highly recommended for the full virus removal. Possibly the most convenient way to get rid of unwanted apps and malware is by scanning the device with powerful security software, such as SpyHunter 5Combo Cleaner or Malwarebytes.
Additionally, you should eliminate the damage that was caused by the virus to your computer. For that, scan it with FortectIntego. This could save you hours of work when trying to deal with constant system crashing, severe lag, and other issues.
Keep in mind that the Red screen virus alert can occur due to a random redirect from a malicious website, so you can land on it at any time. Likewise, accidental clicks on suspicious pages would result in the same result. Therefore, if you encountered the scam, it does not necessarily mean that your computer is infected, although it is highly recommended to check it using the methods we listed below.
Incorrect software installation leads to PUP infections
Users typically call fake tech support because they get scared[4] that their computer and personal data may be at risk, especially if they never death with such a fake screen before (mind that some scams might lock the screen to make it more believable).
Victims typically have no idea that the fake pop-up message came from adware that infiltrated their machines via software bundling. That is why such scams can be hugely successful, and crooks will continue to abuse naive individuals.
Nevertheless, it is relatively easy to protect yourself from adware and other PUPs. Despite freeware developers' recommendations, never pick Recommended/Standard/Quick installation settings. Instead, opt for Advanced/Custom mode. This way you will be able to remove all the tick marks next to optional installs before the process is complete.
Additionally, we advise users to learn about scams, how to recognize[5] them and how to avoid them if the skimming attempt was made (as we already mentioned, people may be redirected to phishing sites even without their PC being affected by adware).
Ways to identify the tech support scam
Google Chrome Critical Error scam is not the only hoax of such type that has been plaguing the worldwide web – ERROR # 0x6a4-0xf9fx3999, Windows Error Code: DLL011150, and Microsoft Warning Alert, among others, are great examples of how cybercriminals exploit users' psychology and lack of technical computer knowledge in order to steal from them.
There have been several raids and arrests made,[6] particularly in India, where the illegal operations of scam call centers are mostly operated from. Unfortunately, there's a myriad of such organizations that preventing the scam schemes from running is almost impossible. As a result, scams such as Google Chrome Critical Error prevails on the web.
There are several ways on how such schemes can be recognized, however. Here are the main things to look out for to be scammed in the future:
- Microsoft, Apple, or any other reputable tech company will never provide you a contact number within an error or warning message. If you need to contact support, go to the official website and retrieve the number from there;
- Tech support scams are often operated by non-English-speaking individuals, so expect grammar and/or spelling mistakes;
- There is no way a browser-based alert could detect the security status of your machine – only anti-virus software installed on your computer can do that;
- Every logo, wording, and other attributes can be easily imitated;
- Always look at the URL (address bar) where the message is coming from. Typically, the delivery address is coming from a randomly-name URL, although crooks often use words that are familiar to users (e.g., “Microsoft,” “Google,” etc.)
Get rid of the Google Chrome Critical Error Red Screen by removing the infection
Redirects to technical support scams will stop when you remove the virus from the affected machine. For that, you have two options. The first one suggests locating and terminating adware manually by following the steps below. Beware that this method requires your full attention as the incorrect procedure might hurt your computer instead of fixing it. Also, be patient, as manual elimination of red screen virus requires some time to complete.
The second removal method is more straightforward than the first one. It requires obtaining an anti-malware program and scanning the device with an updated tool. If you have adware on your system, it would not be surprising if there would be other PUPs installed as well. Thus, automatic removal can also help you find additional unwanted applications quickly and get rid of them for good.
If you have already contacted cybercriminals, you can report the fraud to your local authorities. Additionally, in case you paid for something, contact your bank and ask if reverting payment(s) is possible.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Google Chrome Critical Error. Follow these steps
Uninstall from Windows
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Delete from macOS
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Google Chrome
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Remove from Microsoft Edge
Delete unwanted extensions from MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Clear cookies and other browser data:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Restore new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Disable if you found any suspicious domain.
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.

If this solution failed to help you, you need to use an advanced Edge reset method. Note that you need to backup your data before proceeding.
- Find the following folder on your computer: C:\\Users\\%username%\\AppData\\Local\\Packages\\Microsoft.MicrosoftEdge_8wekyb3d8bbwe.
- Press Ctrl + A on your keyboard to select all folders.
- Right-click on them and pick Delete

- Now right-click on the Start button and pick Windows PowerShell (Admin).
- When the new window opens, copy and paste the following command, and then press Enter:
Get-AppXPackage -AllUsers -Name Microsoft.MicrosoftEdge | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register “$($_.InstallLocation)\\AppXManifest.xml” -Verbose

Instructions for Chromium-based Edge
Delete extensions from MS Edge (Chromium):
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Clear cache and site data:
- Click on Menu and go to Settings.
- Select Privacy, search and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Reset Chromium-based MS Edge:
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Google Chrome Critical Error registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting adware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Los Virus. Los Virus. Spanish cyber security news.
- ^ Adware. Wikipedia. The free encyclopedia.
- ^ Robert Abel. Tech support scam used to spread cryptominer Coinhive's Monero. SC Magazine. Breaking news on cybersecurity, cybercrime, industry insight and security product reviews.
- ^ Scam Alert: Beware Scare Tactics. IDShield. Personal data leak prevention techniques.
- ^ Jonathan Strickland. How to Detect Online Scams. HowStuffWorks. Tech information site.
- ^ Ryan Flanagan. 32 arrested at Indian call centre that targeted Canadians. CTV News. Top Stories - Breaking News - Top News Headlines.
