Hgfu ransomware (virus) - Free Instructions
Hgfu virus Removal Guide
What is Hgfu ransomware?
Hgfu is a file-encrypting virus that demands money for its victims
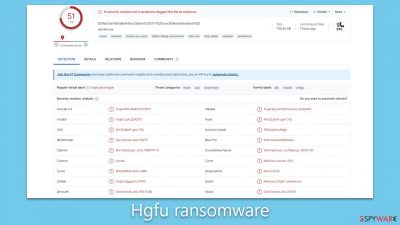
Hgfu ransomware is a menacing derivative of the widely recognized Djvu ransomware lineage, which is known for its potent threat to digital data. Like its predecessors, this virus typically gains unauthorized access to computer systems. The primary avenues for its infiltration are through unofficial software downloads and counterfeit software activation tools.
Once the Hgfu ransomware finds its way into a system, it swiftly initiates an exhaustive file encryption operation. Key targets include essential files such as documents, multimedia content, and other significant data. To lock users out of their files, it uses the intricate RSA encryption algorithm, ensuring that without a distinct decryption key, the files remain unreachable. After the encryption, all affected files receive an “.hgfu” extension. In tandem with this, a ransom message named “_readme.txt” manifests, urging victims to pay a ransom, usually ranging between $980 and $490, in hopes of regaining access to their files.
For those who encounter the Hgfu ransomware, immediate response is crucial. It's recommended to isolate the infected device from any networks promptly and to execute a comprehensive system analysis using sophisticated security tools. The most effective strategy for safeguarding against such threats lies in routine data backups and stringent security protocols.
| Name | Hgfu virus |
|---|---|
| Type | Ransomware, file-locking malware |
| File extension | Malware appends .Hgfu extension to all affected files |
| Family | Djvu |
| Ransom note | _readme.txt dropped at every location where encrypted files are located |
| Contact | support@freshmail.top and datarestorehelp@airmail |
| File Recovery | There is no guaranteed way to recover locked files without backups. Other options include paying cybercriminals (not recommended, might also lose the paid money), using Emisoft's decryptor (works for a limited number of victims), or using third-party recovery software |
| Malware removal | After disconnecting the computer from the network and the internet, do a complete system scan using the SpyHunter 5Combo Cleaner security program |
| System fix | As soon as it is installed, malware has the potential to severely harm some system files, causing instability problems, including crashes and errors. Any such damage can be automatically repaired by using FortectIntego PC repair |
Ransom note demands payment
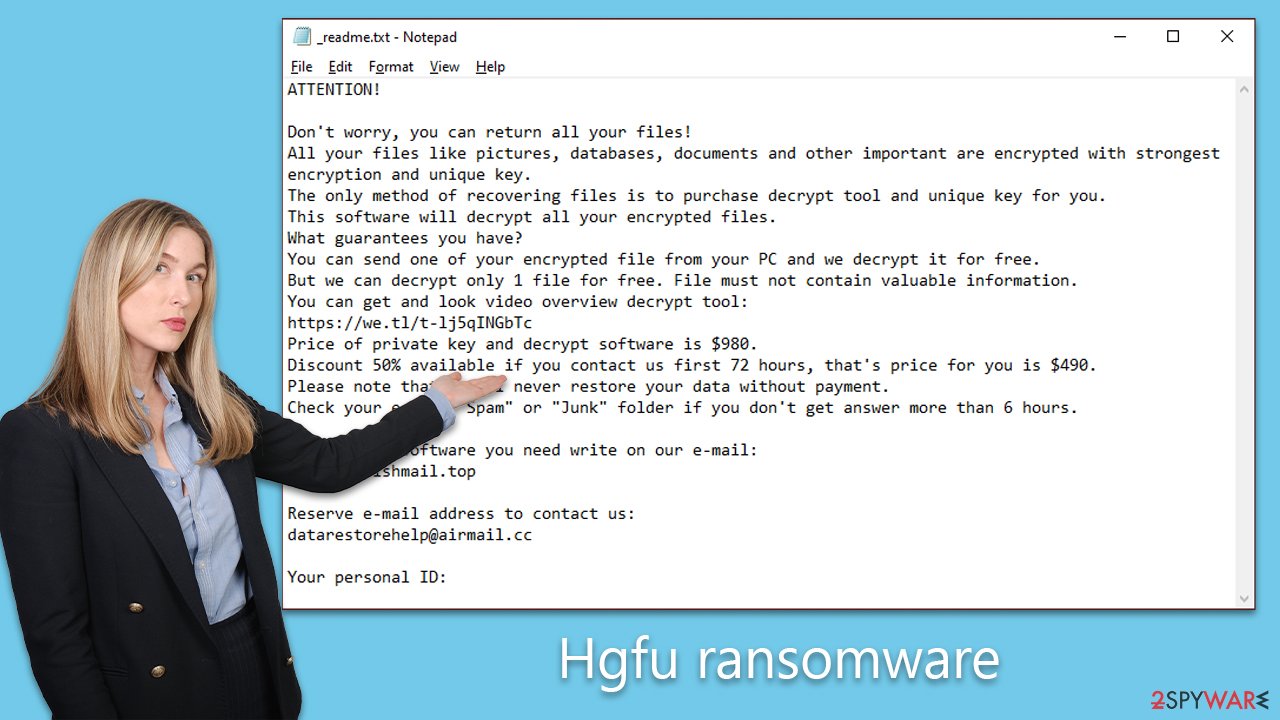
A ransomware attack is not just a silent infiltration; it comes with a stark reminder of the intrusion: a ransom note. This message serves as the primary conduit between the victim and the attacker, detailing the conditions under which the encrypted data may be released.
The communication typically outlines the process for the victim to pay the demanded ransom in exchange for the decryption tool. It's not uncommon for some ransom notes to incorporate a ticking clock, threatening escalating damages or the complete obliteration of data if the deadline isn't met. Yet, Djvu-related strains, like the Hgfu, often adopt a less menacing, seemingly more professional demeanor. These messages often materialize as text documents, visuals, or even accessible web pages on the infiltrated device.
For those unfortunate enough to be targeted by the Hgfu virus, a jarring ransom note appears soon after their files are encrypted. The note's content broadly communicates the following:
ATTENTION!
Don't worry, you can return all your files!
All your files like pictures, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-sD0OUYo1Pd
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that's price for you is $490.
Please note that you'll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don't get answer more than 6 hours.To get this software you need write on our e-mail:
support@freshmail.topReserve e-mail address to contact us:
datarestorehelp@airmail.ccYour personal ID:
Cyber attackers, in an attempt to appear credible, might offer gestures like discounted payments or even a trial decryption service. Such strategies aim to sedate the victim's apprehensions, leading them into the mirage of trust and collaboration.
Yet, it's imperative to maintain skepticism. Even with the Hgfu ransomware, there's an absence of guaranteed reciprocity post-payment. These cybercriminals navigate the murky waters of illicit activities, prioritizing their interests, which renders their guarantees dubious at best.
Malware removal
When confronted with Hgfu or similar ransomware, it's vital to recognize that merely addressing the encryption might not cleanse the system of the malware entirely. Residual components could linger, maintaining a latent threat, and it's not rare for such ransomware to be paired with additional malicious entities. For instance, certain Djvu variants had been observed to be packaged with the malicious Vidar Trojan, introducing another dimension of risk to the compromised machine.
The foremost step in the malware cleansing process should be severing the system's internet connection. This move curtails any further malicious activities or spread. Subsequently, users should perform a comprehensive system sweep using trusted security software like SpyHunter 5Combo Cleaner or Malwarebytes. Such tools come fortified with mechanisms tailored to pinpoint and eradicate a spectrum of malware, spanning ransomware to Trojans.
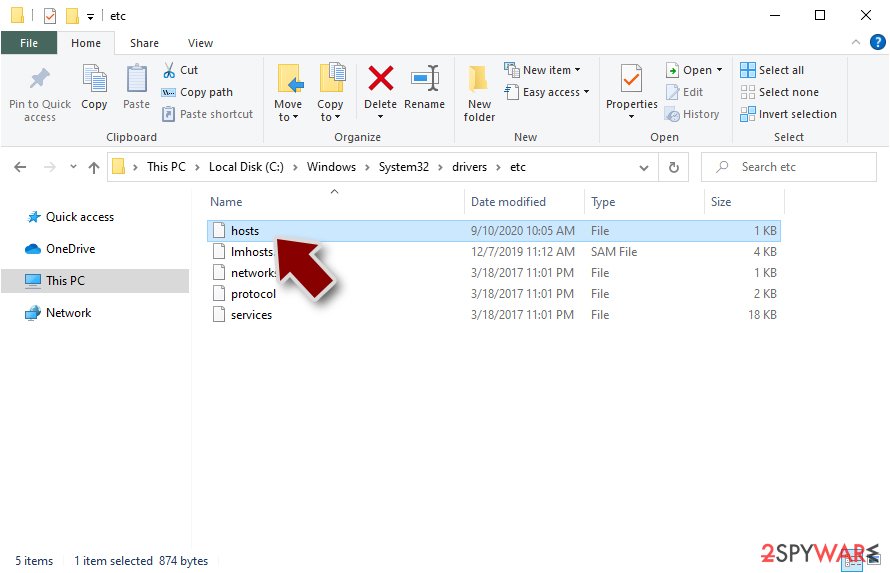
A proactive measure involves venturing into:
- C:\Windows\System32\drivers\etc
Within this directory, it's imperative to identify and excise the “hosts” file. This file often undergoes alterations by ransomware to obstruct users from accessing certain web portals, predominantly those proffering malware mitigation or data salvage solutions. To further bolster system health, consider deploying a robust PC repair application FortectIntego. Such utilities excel at mending compromised Windows components, ensuring an error-free, stable operating environment, and minimizing hazards like system crashes.
Once convinced of the comprehensive eviction of the ransomware and its potential allies, the spotlight can shift to data restoration. Before embarking on this recovery phase, affirming the total absence of any malware trace is paramount. This wards off potential setbacks like further data compromise or repeat encryptions.
The realm of ransomware is often shrouded in misconceptions, particularly concerning the dynamics of data encryption and the functioning of such malware. A common notion harbored by many ransomware victims is the presumption that a comprehensive system scan using security tools is a panacea for their encrypted files. Some even embark on manual interventions, like renaming and re-extending files, hoping this would miraculously restore their data. However, the reality is considerably more intricate.
The encryption deployed by ransomware, including the Hgfu variant, is built on sophisticated algorithms. These tools generate cryptographic sequences that are Herculean to decipher or bypass, dispelling the idea of tricking ransomware into releasing files. Exorcising the malware doesn't liberate the files; they remain encrypted and unreachable sans the decryption key—a piece of information zealously guarded by cyber adversaries.
Ransomware's modus operandi involves encrypting data, associating each with a distinctive identifier and a convoluted encryption key. This data is relayed to the malicious actors, empowering them with the tools needed to produce a decryption key, subsequently granting them unfettered access to the entrapped data. Their objective is lucid: capitalize on the victim's desperation, transforming it into monetary gains, underscoring why ransomware is a goldmine for cybercriminal syndicates.
While the allure of paying ransoms might seem compelling, we advocate for alternative avenues, delineated below. Prior to venturing into any recovery techniques, it's pivotal to have a backup of the ensnared data. This prudence prevents further data degradation during restoration attempts.
A logical starting point would be the Emsisoft decryption utility. However, it's paramount to acknowledge its efficacy is contingent on the specific ransomware strain and an array of other determinants.
- Download the app from the official Emsisoft website.
![Hgfu ransomware Hgfu ransomware]()
- After pressing Download button, a small pop-up at the bottom, titled decrypt_STOPDjvu.exe should show up – click it.
![Hgfu ransomware Hgfu ransomware]()
- If User Account Control (UAC) message shows up, press Yes.
- Agree to License Terms by pressing Yes.
![Hgfu ransomware Hgfu ransomware]()
- After Disclaimer shows up, press OK.
- The tool should automatically populate the affected folders, although you can also do it by pressing Add folder at the bottom.
![Hgfu ransomware Hgfu ransomware]()
- Press Decrypt.
![Hgfu ransomware Hgfu ransomware]()
From here, there are three available outcomes:
- “Decrypted!” will be shown under files that were decrypted successfully – they are now usable again.
- “Error: Unable to decrypt file with ID:” means that the keys for this version of the virus have not yet been retrieved, so you should try later.
- “This ID appears to be an online ID, decryption is impossible” – you are unable to decrypt files with this tool.
If your data was encrypted with an online ID, Emsisoft's tool won't work. In such a case, we recommend trying specialized data recovery software instead.
- Download Data Recovery Pro.
- Double-click the installer to launch it.
![Hgfu ransomware Hgfu ransomware]()
- Follow on-screen instructions to install the software.
- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders which you want the files to be recovered from.
![Select what to recover Select what to recover]()
- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.
![Select Deep scan Select Deep scan]()
- Press Scan and wait till it is complete.
![Scan Scan]()
- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.
Check out the instructions below for more tips and troubleshooting.
Getting rid of Hgfu virus. Follow these steps
Find a working decryptor for your files
File encryption is a process that is similar to applying a password to a particular file or folder. However, from a technical point of view, encryption is fundamentally different due to its complexity. By using encryption, threat actors use a unique set of alphanumeric characters as a password that can not easily be deciphered if the process is performed correctly.
There are several algorithms that can be used to lock data (whether for good or bad reasons); for example, AES uses the symmetric method of encryption, meaning that the key used to lock and unlock files is the same. Unfortunately, it is only accessible to the attackers who hold it on a remote server – they ask for a payment in exchange for it. This simple principle is what allows ransomware authors to prosper in this illegal business.
While many high-profile ransomware strains such as Djvu or Dharma use immaculate encryption methods, there are plenty of failures that can be observed within the code of some novice malware developers. For example, the keys could be stored locally, which would allow users to regain access to their files without paying. In some cases, ransomware does not even encrypt files due to bugs, although victims might believe the opposite due to the ransom note that shows up right after the infection and data encryption is completed.
Therefore, regardless of which crypto-malware affects your files, you should try to find the relevant decryptor if such exists. Security researchers are in a constant battle against cybercriminals. In some cases, they manage to create a working decryption tool that would allow victims to recover files for free.
Once you have identified which ransomware you are affected by, you should check the following links for a decryptor:
- No More Ransom Project
- Free Ransomware Decryptors by Kaspersky
- Free Ransomware Decryption Tools from Emsisoft
- Avast decryptors

If you can't find a decryptor that works for you, you should try the alternative methods we list below. Additionally, it is worth mentioning that it sometimes takes years for a working decryption tool to be developed, so there are always hopes for the future.
Restore Windows "hosts" file to its original state
Some ransomware might modify Windows hosts file in order to prevent users from accessing certain websites online. For example, Djvu ransomware variants add dozens of entries containing URLs of security-related websites, such as 2-spyware.com. Each of the entries means that users will not be able to access the listed web addresses and will receive an error instead.
Here's an example of “hosts” file entries that were injected by ransomware:
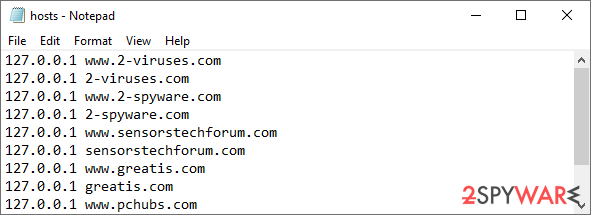
In order to restore your ability to access all websites without restrictions, you should either delete the file (Windows will automatically recreate it) or remove all the malware-created entries. If you have never touched the “hosts” file before, you should simply delete it by marking it and pressing Shift + Del on your keyboard. For that, navigate to the following location:
C:\\Windows\\System32\\drivers\\etc\\
Create data backups to avoid file loss in the future
One of the many countermeasures for home users against ransomware is data backups. Even if your Windows get corrupted, you can reinstall everything from scratch and retrieve files from backups with minimal losses overall. Most importantly, you would not have to pay cybercriminals and risk your money as well.
Therefore, if you have already dealt with a ransomware attack, we strongly advise you to prepare backups for future use. There are two options available to you:
- Backup on a physical external drive, such as a USB flash drive or external HDD.
- Use cloud storage services.
The first method is not that convenient, however, as backups need to constantly be updated manually – although it is very reliable. Therefore, we highly advise choosing cloud storage instead – it is easy to set up and efficient to sustain. The problem with it is that storage space is limited unless you want to pay for the subscription.
Using Microsoft OneDrive
OneDrive is a built-in tool that comes with every modern Windows version. By default, you get 5 GB of storage that you can use for free. You can increase that storage space, but for a price. Here's how to setup backups for OneDrive:
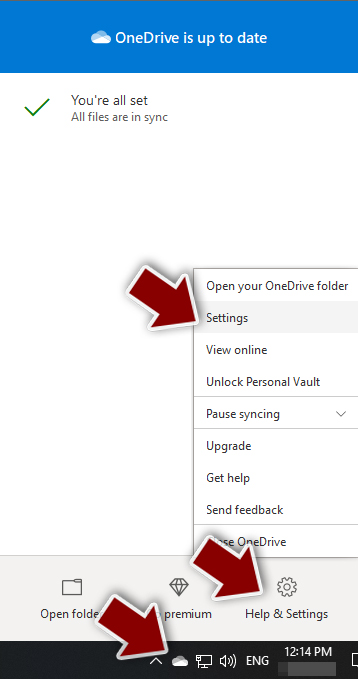
- Click on the OneDrive icon within your system tray.
- Select Help & Settings > Settings.

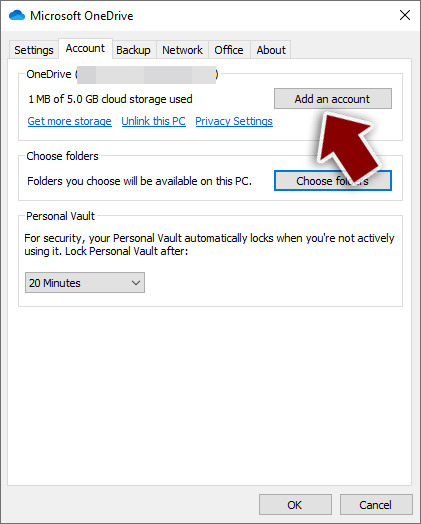
- If you don't see your email under the Account tab, you should click Add an account and proceed with the on-screen instructions to set yourself up.

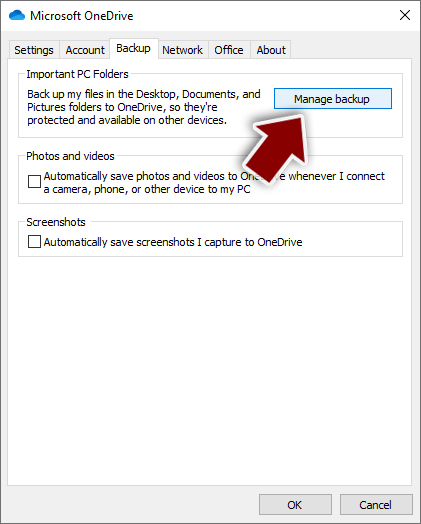
- Once done, move to the Backup tab and click Manage backup.

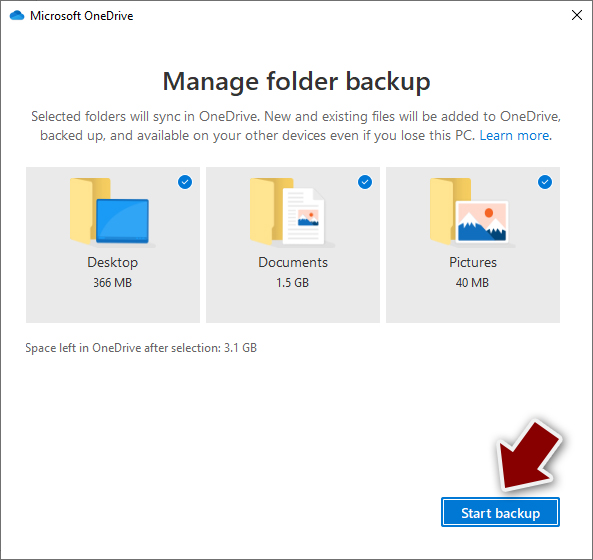
- Select Desktop, Documents, and Pictures, or a combination of whichever folders you want to backup.
- Press Start backup.

After this, all the files that are imported into the above-mentioned folders will be automatically backed for you. If you want to add other folders or files, you have to do that manually. For that, open File Explorer by pressing Win + E on your keyboard, and then click on the OneDrive icon. You should drag and drop folders you want to backup (or you can use Copy/Paste as well).
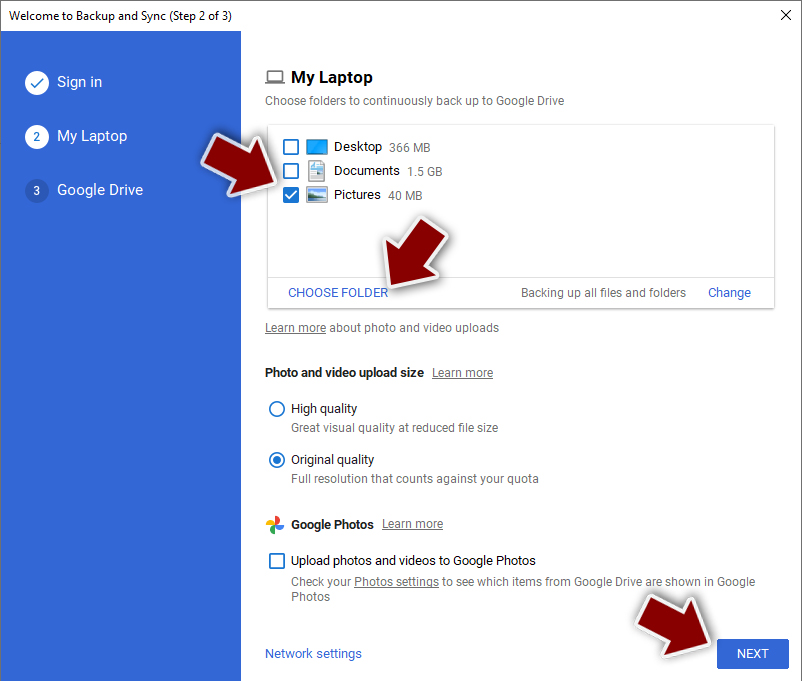
Using Google Drive
Google Drive is another great solution for free backups. The good news is that you get as much as 15GB for free by choosing this storage. There are also paid versions available, with significantly more storage to choose from.
You can access Google Drive via the web browser or use a desktop app you can download on the official website. If you want your files to be synced automatically, you will have to download the app, however.
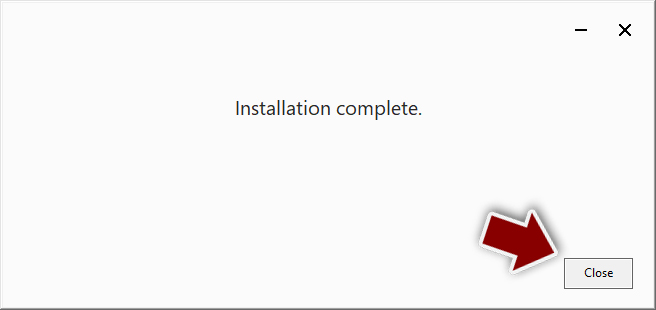
- Download the Google Drive app installer and click on it.

- Wait a few seconds for it to be installed.

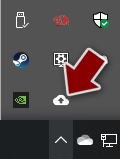
- Now click the arrow within your system tray – you should see Google Drive icon there, click it once.

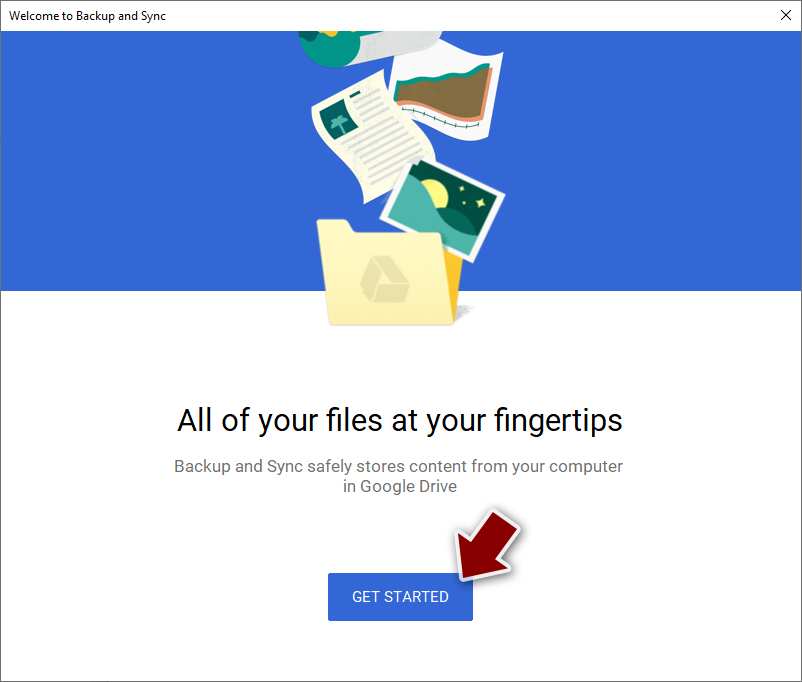
- Click Get Started.

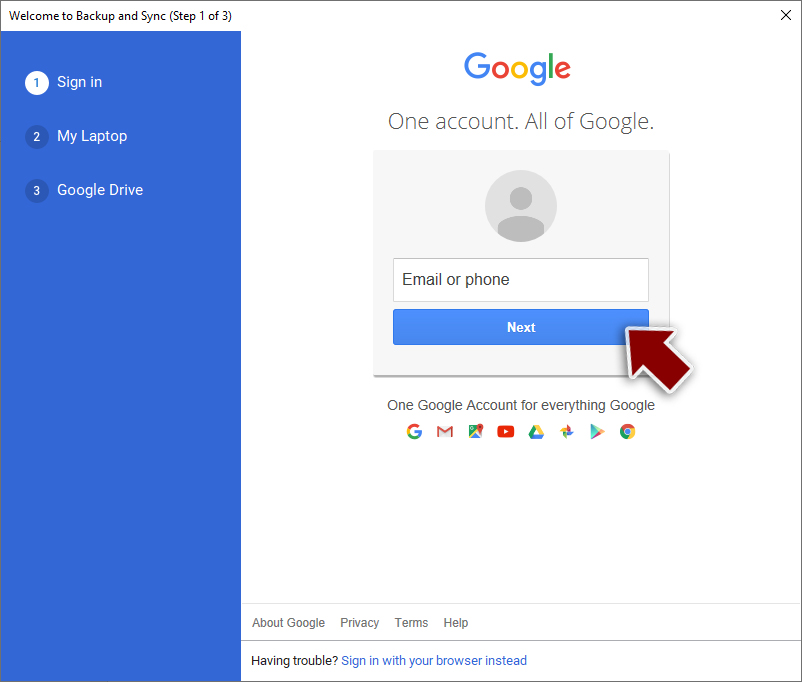
- Enter all the required information – your email/phone, and password.

- Now pick what you want to sync and backup. You can click on Choose Folder to add additional folders to the list.
- Once done, pick Next.

- Now you can select to sync items to be visible on your computer.
- Finally, press Start and wait till the sync is complete. Your files are now being backed up.
Report the incident to your local authorities
Ransomware is a huge business that is highly illegal, and authorities are very involved in catching malware operators. To have increased chances of identifying the culprits, the agencies need information. Therefore, by reporting the crime, you could help with stopping the cybercriminal activities and catching the threat actors. Make sure you include all the possible details, including how did you notice the attack, when it happened, etc. Additionally, providing documents such as ransom notes, examples of encrypted files, or malware executables would also be beneficial.
Law enforcement agencies typically deal with online fraud and cybercrime, although it depends on where you live. Here is the list of local authority groups that handle incidents like ransomware attacks, sorted by country:
- USA – Internet Crime Complaint Center IC3
- United Kingdom – ActionFraud
- Canada – Canadian Anti-Fraud Centre
- Australia – ScamWatch
- New Zealand – ConsumerProtection
- Germany – Polizei
- France – Ministère de l'Intérieur

If your country is not listed above, you should contact the local police department or communications center.
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.