HiddenSearcher browser hijacker (Free Instructions)
HiddenSearcher browser hijacker Removal Guide
What is HiddenSearcher browser hijacker?
HiddenSearcher is a potentially unwanted extension that replaces your browser settings to insert ads

HiddenSearcher is a browser hijacker that manifests in the form of a browser extension. While some people might install it intentionally due to its rather exceptional promises of “a secure, bing-based lighting fast search engine,” others might find it installed on their browsers without doing so intentionally. This can be easily explained by its deceptive distribution method known as software bundling,[1] which many potentially unwanted program authors use.
Once installed on the system, the app would immediately change the homepage and the new tab address to hiddensearcher.com. While initially seen as insignificant, this change completely changes the way users browse the web. First of all, the new homepage cannot be altered to the default one unless the extension is removed, hence users are forced to use the fake search engine for as long as the HiddenSearcher is installed.
The searches are then redirected to an alternative search provider, such as Yahoo, Bing, or another (depending on some personal settings and location). This would also allow the hijacker to insert ads directly into the search results, and they would be shown at the top. We recommend not clicking on any of the promotional links, as they might be misleading.
| Name | HiddenSearcher |
| Type | Browser hijacker, potentially unwanted browser extension |
| Distribution | Bundled software, third party websites, fake ads |
| Symptoms | New extension installed on the browser; homepage and new tab set to hiddensearcher.com; redirects searches to another provider and inserts ads |
| Risks | Data tracking from various third parties, exposure to malicious ads, redirects to phishing sites |
| Removal | To remove the unwanted browser extension, you should access your browser's settings. Checking the system with SpyHunter 5Combo Cleaner security software can also ensure that there is no adware or malware running in the background |
| Other tips | After removing all potentially unwanted applications, we recommend you employ the FortectIntego utility to clean your web browsers and repair any damaged system files |
Unintentional installation of potentially unwanted programs
As mentioned, some users do not install HiddenSearcher on purpose and even believe that it just appeared by itself. However, this is not the case, as browser hijackers are always installed by users themselves, even though they are doing so unconsciously.
As we already mentioned, software bundling is commonly used to deliver potentially unwanted applications to users' machines. Third-party websites are known to practice this technique all the time, as it brings pay-per-install money to them. Unfortunately, this results in users installing applications on their systems they never asked for or wanted.
First of all, you should always take precautions when dealing with third-party websites – they might include insecure ads or fake download links. When the installation wizard is launched, it is important to keep in mind that all third-party websites have an incentive to spread additional apps, so they bundle them into a standalone installer.
If users are not careful enough and don't withdraw from the installation offer, they end up installing the promoted app, such as HiddenSearcher browser hijacker only to later see that their browser settings have been altered seemingly without permission. In order to avoid that, you should always pay attention to the installation steps and never rush the process – choose Advanced/Custom settings instead of Recommended ones, read the fine print, remove ticks from pre-ticked checkboxes, and watch out for misplaced “Accept offer” buttons.
Removal of HiddenSearcher
Browser hijackers usually come in the form of an extension that is much easier to remove compared to malicious programs installed on the system level. In order to uninstall a potentially unwanted app, you can click the “Extensions” button located next to the settings menu/profile picture. If that is impossible for some reason, you can do the same thing via the settings as follows:
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.
![Remove extensions from Firefox Remove extensions from Firefox]()
MS Edge
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
MS Edge (legacy)
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.
![Remove extensions from Edge Remove extensions from Edge]()
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
Other security measures and tips
Most browser hijackers are more of nuisances rather than real threats such as Trojans or RATs.[2] However, they shouldn't be dismissed as completely harmless – they can lead to websites that can be deceptive thanks to insecure advertising networks used by PUP authors regularly. Thus, proper removal of such apps is recommended.
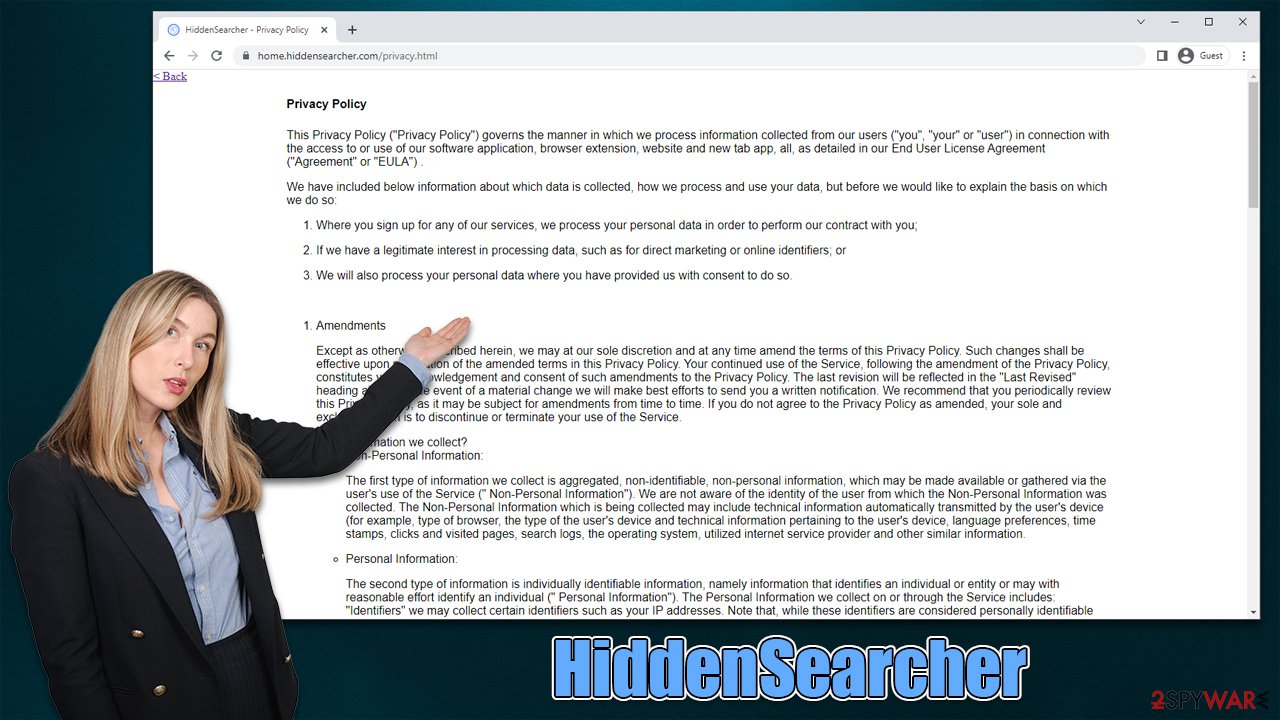
If you have already eliminated the HiddenSearcher browser extension, your next task is to ensure that the application no longer tracks you. According to the privacy policy of the hijacker, various information is collected automatically, including the type of browser, the type of the user's device and technical information pertaining to the user's device, language preferences, time stamps, clicks and visited pages, search logs, the operating system, IP address, and more.[3]
In order to stop these tracking processes, you should delete cookies and other locally-stored items from your system. You can either do it automatically with FortectIntego or refer to these steps:
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content, and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
MS Edge (legacy)
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.
![Clear Edge browsing data Clear Edge browsing data]()
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
Finally, we recommend you scan your system with SpyHunter 5Combo Cleaner, Malwarebytes, or another reputable anti-malware software to confirm the absence of other potentially unwanted or malicious programs. If found, security software can quickly and easily remove malware and all its components effectively.
How to prevent from getting browser hijacker
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Bundled Software. Techopedia. Professional IT insight.
- ^ Remote Access Trojan. Imperva. Data and application security.
- ^ Privacy Policy. Privacy Policy.










