Ilitonline.com ads (fake) - Free Instructions
Ilitonline.com ads Removal Guide
What is Ilitonline.com ads?
Ilitonline.com ads might show fake virus infection alerts and other fake messages

Ilitonline.com is a fraudulent website that users may stumble upon when navigating through unsecured websites. These may include sites distributing illicit software or streaming copyrighted content. Having adware on your system could also lead to inadvertent encounters with this website during web browsing sessions.
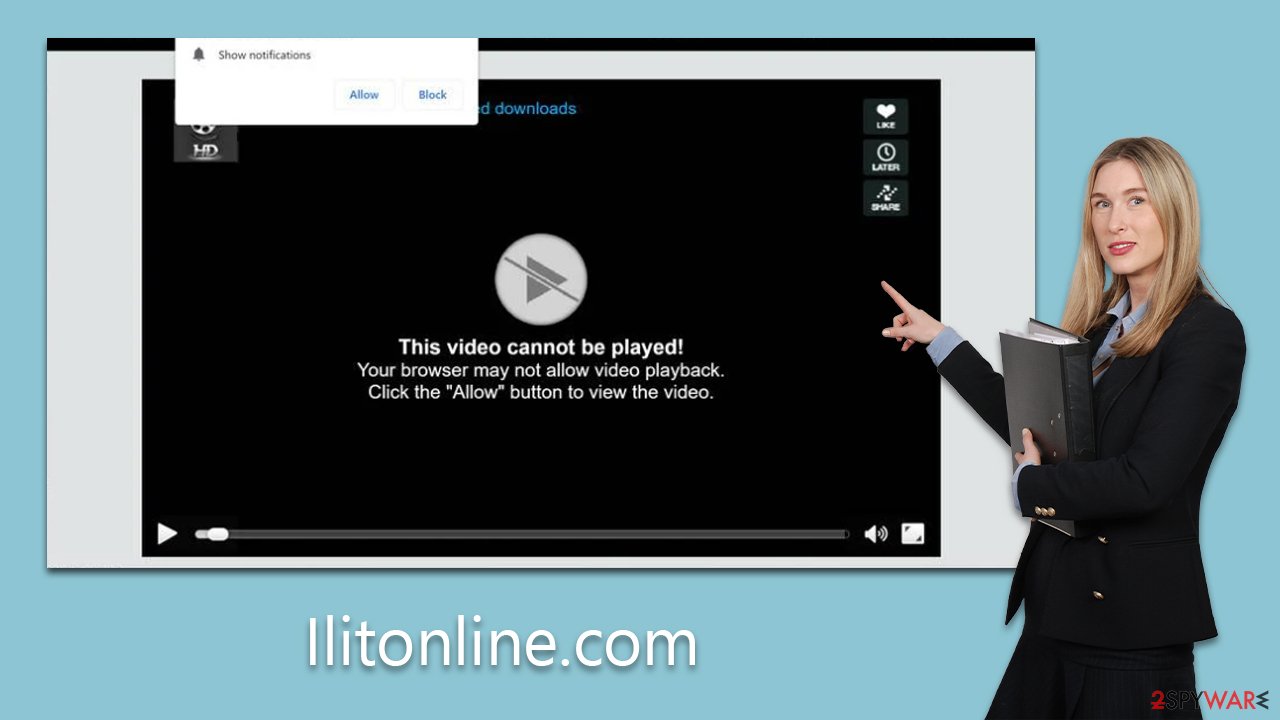
When accessing the site, users are confronted with a prompt urging them to allow notifications. This prompt is accompanied by an image carrying a persuasive message, inducing them to click the “Allow” button. However, the site employs cunning tactics and provides deceptive reasons to manipulate users into taking the suggested action. If a user succumbs to this ploy, they start encountering intrusive and unsolicited ads from Ilitonline.com. These pop-ups are not initiated by user activity but are prompted by the website's push notification requests.
This situation can pose significant risks, as users may be exposed to misleading messages and links that redirect to harmful websites. They could be tricked into subscribing to additional notifications, downloading malicious software, or even divulging sensitive personal information.
To guard against these threats, we strongly recommend steering clear of such deceptive websites. Furthermore, thorough removal instructions should be followed to eradicate Ilitonline.com ads from your system, along with any adware or malicious software that might have infiltrated your system.
| Name | Ilitonline.com |
| Type | Push notifications, pop-ups, ads, scam |
| Distribution | The website gains access to deliver any information as soon as the “Allow” button is pressed within the push notification prompt |
| Symptoms | Push notifications show on the desktop at random time intervals. These pop-ups show fake notices and push scams. Links can also lead to malware-laden sites |
| Risks | The ads shown within push notification prompts might include misleading messages and links to malicious websites. If clicked, you might end up infecting your system with malware, disclosing your personal information, or losing money |
| Removal | You can disable the push notifications from any website via browser settings. Scanning the system with SpyHunter 5Combo Cleaner can also ensure that it's clean and secure |
| Other checks | You should check your system with FortectIntego to fix virus damage and remove various trackers from your browsers |
Push notification scams are popular
Push notification scams, such as the one operated by Ilitonline.com, have seen a considerable rise in popularity over the past few years, primarily due to their remarkable efficacy in manipulating users into subscribing to push notifications. The initial and perhaps most crucial step in executing this scam is to lure users to the phishing site. This is often accomplished through insecure ad networks and websites with inadequate security measures.
Users may inadvertently land on Ilitonline.com by clicking links scattered across high-risk sites such as torrents and other similar platforms. These sites frequently feature deceptive “Download” buttons or employ malicious scripts that automatically redirect users to Ilitonline.com when they click on seemingly random areas on the page. Given this potential for exploitation, it is advisable to refrain from visiting illegal or unsecured websites. Instead, opt for reputable websites that prioritize user security.
Alternatively, users may experience redirects to Ilitonline.com due to adware covertly installed on their systems. This type of software is typically disseminated through bundled software packages or other misleading methods, leading to users being unaware of its presence on their systems. The insidious nature of such practices underscores the importance of vigilant and informed software installation and browsing habits, thereby mitigating the risk of falling victim to these scams.
Scammers use cheap techniques to trick users
The unexpected nature of landing on suspicious websites like Ilitonline.com often catches users off guard, making them susceptible to errors in judgment. The site capitalizes on this element of surprise, presenting what appear to be harmless prompts. Users are asked to verify their humanity or their age, seemingly innocent requests that are, in reality, well-honed social engineering tactics often deployed in online scams.
Scammers on Ilitonline.com have a singular aim: to deceive users into believing that clicking the “Allow” button serves a different purpose than what it truly does. To accomplish this, they resort to predetermined, manipulative messages and images that are widely used across numerous push notification scam sites. Some examples of these misleading prompts include:
- Click Allow to confirm that you are not a robot
- Can't play this video! Perhaps your browser doesn't allow video playback. Please click the Allow button to watch the video
- Click “Allow” to win the prize and get it in our shop!
- If you are 18+, click Allow
- Your file is ready to download – press Allow to continue.
Users should remember that approving a push notification prompt invariably results in the authorization of push notifications on their devices. This means that Ilitonline.com can freely send a variety of information, including misleading links and fake messages, via the browser's API, as long as the browser is open or running in the background.
Fortunately, managing these intrusive notifications is not a complex task once you know the steps to cease them. The subsequent section provides a detailed explanation of the process to follow to stop these notifications, ensuring a safer browsing experience.
How to remove unwanted push notifications and check for infections
Users often land on scam websites due to unexpected redirects. However, the frequency of such encounters might escalate when your system is compromised with adware. Indicators of such an infection could include persistent pop-ups, unsolicited offers, discount coupons, sponsored links, and sudden rerouting through questionable web addresses during internet browsing, among other aberrant behaviors.
Given these potential threats, conducting a comprehensive system scan using robust security software such as SpyHunter 5Combo Cleaner, Malwarebytes, or other reliable alternatives is highly recommended. Such a scan will ensure your system's cleanliness, freeing it from malware like adware, browser hijackers, trojans, backdoors, and other potential threats, but it will also make your system less prone to future malware attacks.
Once you've purged any potentially undesirable and harmful applications from your system, using a tool like FortectIntego to cleanse your browsers and rectify any potential virus-induced damage is suggested.
To rid yourself of the persistent annoyance of push notifications, you must modify your browser settings to block the Ilitonline.com URL. The process for this will vary depending on the browser you are using. The following steps will guide you through the process:
Google Chrome (desktop)
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Google Chrome (Android)
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).
![Stop notifications on Chrome Android Stop notifications on Chrome Android]()
Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.
![Stop notifications on Edge Chromium Stop notifications on Edge Chromium]()
Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
![Stop notifications on Internet Explorer Stop notifications on Internet Explorer]()
- Locate the web address in question under Allowed sites and pick Remove.
How to prevent from getting adware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.






