Koxic ransomware (virus) - Recovery Instructions Included
Koxic virus Removal Guide
What is Koxic ransomware?
Koxic ransomware is a severe threat to people who do not have their files backed up
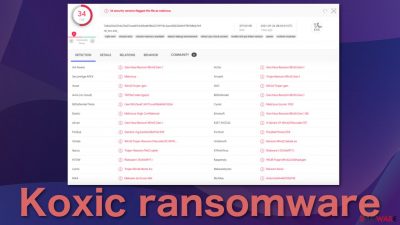
Ransomware is one of the most devastating virus infections there is. That's because it makes users' personal files impossible to open or view and changes their icons to blank pages. So those who have not backed up their files potentially lost them forever. Koxic data locking malware was detected by 34 security vendors[1] and classified as malicious.
This particular malicious program encrypts the files and appends them with the .KOXIC_PLCAW extension. If the file was previously named picture.jpg, after encryption, it would look like picure.jpg.KOXIC_PLCAW. The virus encrypts files almost immediately after it infiltrates the system. Shortly after that, a ransom note is generated by the name WANNA_RECOVER_KOXIC_FILEZ_PLCAW.txt which informs victims of what the attackers want them to do.
The purpose of locking people's files is to later ask for a ransom in exchange for a decryption key. Usually, ransomware developers ask to be paid in cryptocurrencies. It is not known how much exactly these particular threat actors want as they do not specify that in the note. Besides locking photos, videos, documents, and other personal. files, ransomware is known to sometimes also engage in cryptojacking[2] because of high CPU usage.
| NAME | Koxic |
| TYPE | Ransomware, cryptovirus, data locking malware |
| DISTRIBUTION | Email attachments, peer-to-peer file sharing platforms, malicious ads |
| FILE EXTENSION | .KOXIC_PLCAW |
| RANSOM NOTE | WANNA_RECOVER_KOXIC_FILEZ_PLCAW.txt |
| FILE RECOVERY | It is almost impossible to recover the files if users do not have backups; we provide third-party solutions that might help you in this article |
| MALWARE REMOVAL | Scanning your machine with anti-malware software is the best option to eliminate the malicious files |
| SYSTEM FIX | Windows reinstallation can be avoided with FortectIntego maintenance tool, which can fix damaged files, system errors and prevent Windows reinstallation |
How file locking viruses are spread?
There are many ways you could have been infected with this malicious program. One of the most common is by email. Cybercriminals send phishing emails with infected attachments that people open or download. Other methods include fake software updaters, “cracked” software, and malicious links.
Threat actors could use your friend list to appear like an email is sent from someone you know. If you were not expecting to receive an attachment, double-check with that person through another platform just to be sure. Also, you should never trust random websites or prompts that say that your software is out-of-date and you cannot reach some type of content. One of the most popular examples of this scheme is Flash Player updates. Users should note that Flash Player is no longer used since 2020 and was replaced by HTML5[3] because of many vulnerabilities.
Websites that distribute “cracked” software are known to be full of malicious software bundled together into the installers.[4] These sites are rarely regulated, so the owners generate revenue by including potentially unwanted programs and malware. You should avoid these shady websites and use official sources for your software, although we know it might get costly.
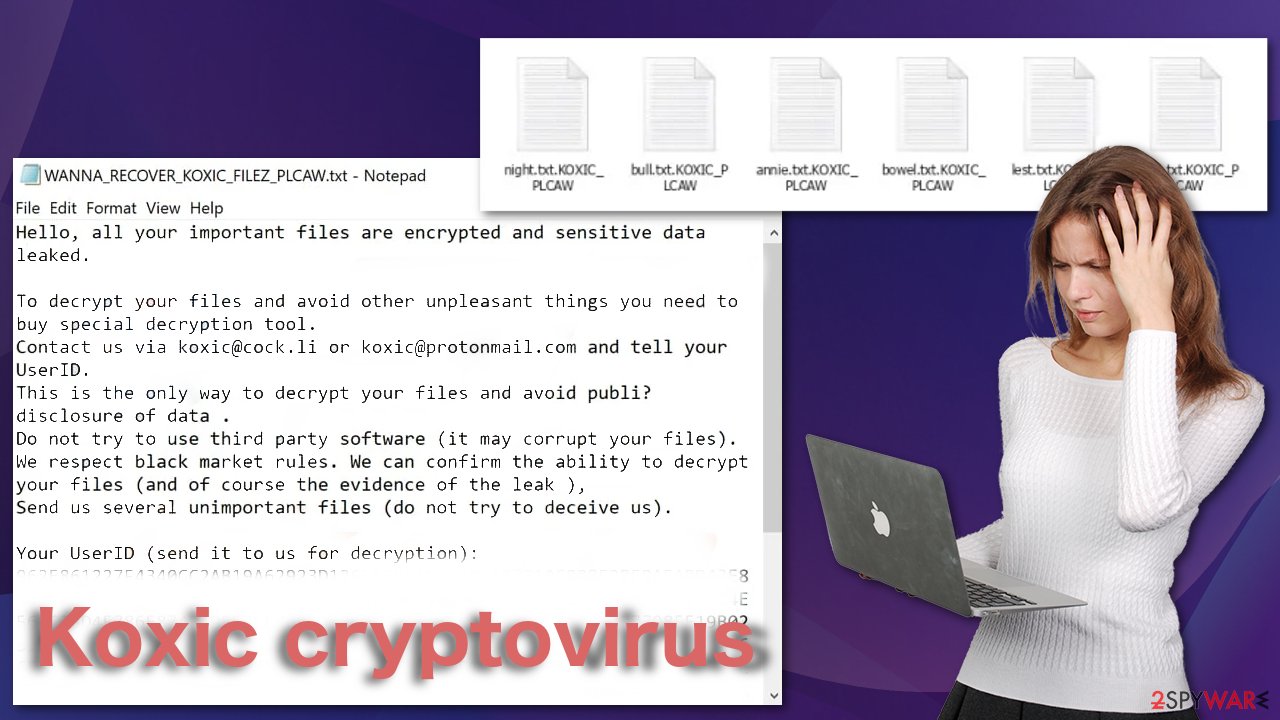
The ransom note
This is the full message in the WANNA_RECOVER_KOXIC_FILEZ_PLCAW.txt file:
Hello, all your important files are encrypted and sensitive data leaked.
To decrypt your files and avoid other unpleasant things you need to buy special decryption tool.
Contact us via koxic@cock.li or koxic@protonmail.com and tell your UserID.
This is the only way to decrypt your files and avoid publi? disclosure of data .
Do not try to use third party software (it may corrupt your files).
We respect black market rules. We can confirm the ability to decrypt your files (and of course the evidence of the leak ),
Send us several unimportant files (do not try to deceive us).Your UserID (send it to us for decryption):
–
You can see, in the note cybercriminals provide their contact details and give instructions. We advise against contacting them, as many ransomware victims have shared their experiences. Many say that they never heard back from threat actors after sending them the money, so you not only lose your data but run the risk of losing your money too.
Developers also try to use scare tactics to prevent victims from searching for other solutions. They want people to act without thinking and contact them as soon as possible. They also try to gain trust by saying that they can prove that they have software that is capable of decrypting affected files.
Start the removal process
If you try to recover your data first, it can result in permanent loss. It can also encrypt your files the second time. It will not stop until you remove the malicious files causing it first. You should not attempt removing the malicious program yourself. Use anti-malware tools like SpyHunter 5Combo Cleaner or Malwarebytes to scan your system. This security software should find all the related files and entries and remove them automatically for you. Automatic removal is the best option because there is less risk of leaving some of the traces behind.
Malware could prevent you from using antivirus software by turning it off. In that case, you should proceed with accessing Safe Mode first:
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.
![Windows XP/7 Windows XP/7]()
Windows 10 / Windows 8
- Right-click on Start button and select Settings.
- Scroll down to pick Update & Security.
![Update & Security Update & Security]()
- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.
![Recovery Recovery]()
- Select Troubleshoot.
![Choose an option Choose an option]()
- Go to Advanced options.
- Select Startup Settings.
- Click Restart.
- Press 5 or click 5) Enable Safe Mode with Networking.
![Press F5 to enable Safe Mode with Networking Press F5 to enable Safe Mode with Networking]()
File recovery using third-party software
Only hackers hold the decryption key, which can unlock your files, so if you did not back them up previously, you possibly lost your files forever. You can try using data recovery software, but third-party programs cannot always decrypt the files. We suggest at least trying this method. Before proceeding, you have to copy the corrupted files and place them in a USB flash drive or another storage. And remember – only do this if you have already removed Koxic ransomware.
- Download Data Recovery Pro.
- Double-click the installer to launch it.
![Koxic ransomware Koxic ransomware]()
- Follow on-screen instructions to install the software.
- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders where you want the files to be recovered from.
![Select what to recover Select what to recover]()
- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.
- Press Scan and wait till it is complete.
- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.
![Recover files Recover files]()
Fix the damaged OS
Performance, stability, and usability issues, to the point where a full Windows reinstall is required, are expected after malware infection. These types of infections can alter the Windows registry database, damage vital bootup and other sections, delete or corrupt DLL files, etc. Once a system file is damaged by malware, antivirus software is not able to repair it.
This is why FortectIntego was developed. It can fix a lot of the damage caused by an infection like this. Blue Screen errors, freezes, registry errors, damaged DLLs, etc., can make your computer completely unusable. By using this maintenance tool, you could avoid Windows reinstallation.
- Download the application by clicking on the link above
- Click on the ReimageRepair.exe
![Reimage download Reimage download]()
- If User Account Control (UAC) shows up, select Yes
- Press Install and wait till the program finishes the installation process
- The analysis of your machine will begin immediately
![Reimage scan Reimage scan]()
- Once complete, check the results – they will be listed in the Summary
- You can now click on each of the issues and fix them manually
- If you see many problems that you find difficult to fix, we recommend you purchase the license and fix them automatically.
![Reimage results Reimage results]()
How to protect yourself from ransomware attacks?
There are a lot of different ways you could improve your routine to improve your security. These measures are not difficult to take and need some getting used to:
- Do not disclose your personal information if you receive a call, text message, or email from an unknown source. If you have any doubt about the legitimacy, you should contact the sender in another way directly.
- Download files only from known and trusted sources. You can use the Google Play Store or the Apple App Store, depending on your device, to get a lot of different applications.
- Use VPN services to hide your IP address and mask your location, especially while using public Wi-Fi for sensitive transactions.
- Be wary of email attachments because they can be infected, and opening them could run a malicious macro. If you were not expecting files on email from anyone you know, double-check with them through another source.
- Update your operating system and software regularly. Developers release security patches for vulnerabilities known or unknown to hackers, so it is less likely they will exploit the system.
Getting rid of Koxic virus. Follow these steps
Isolate the infected computer
Some ransomware strains aim to infect not only one computer but hijack the entire network. As soon as one of the machines is infected, malware can spread via network and encrypt files everywhere else, including Network Attached Storage (NAS) devices. If your computer is connected to a network, it is important to isolate it to prevent re-infection after ransomware removal is complete.
The easiest way to disconnect a PC from everything is simply to plug out the ethernet cable. However, in the corporate environment, this might be extremely difficult to do (also would take a long time). The method below will disconnect from all the networks, including local and the internet, isolating each of the machines involved.
- Type in Control Panel in Windows search and press Enter
- Go to Network and Internet

- Click Network and Sharing Center

- On the left, pick Change adapter settings

- Right-click on your connection (for example, Ethernet), and select Disable

- Confirm with Yes.
If you are using some type of cloud storage you are connected to, you should disconnect from it immediately. It is also advisable to disconnect all the external devices, such as USB flash sticks, external HDDs, etc. Once the malware elimination process is finished, you can connect your computers to the network and internet, as explained above, but by pressing Enable instead.
Report the incident to your local authorities
Ransomware is a huge business that is highly illegal, and authorities are very involved in catching malware operators. To have increased chances of identifying the culprits, the agencies need information. Therefore, by reporting the crime, you could help with stopping the cybercriminal activities and catching the threat actors. Make sure you include all the possible details, including how did you notice the attack, when it happened, etc. Additionally, providing documents such as ransom notes, examples of encrypted files, or malware executables would also be beneficial.
Law enforcement agencies typically deal with online fraud and cybercrime, although it depends on where you live. Here is the list of local authority groups that handle incidents like ransomware attacks, sorted by country:
- USA – Internet Crime Complaint Center IC3
- United Kingdom – ActionFraud
- Canada – Canadian Anti-Fraud Centre
- Australia – ScamWatch
- New Zealand – ConsumerProtection
- Germany – Polizei
- France – Ministère de l'Intérieur

If your country is not listed above, you should contact the local police department or communications center.
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ DETECTION. VirusTotal. Free virus analysis service.
- ^ Cryptojacking. Interpol. International Criminal Police Organization Website.
- ^ Carrie Marshall. HTML5: what is it?. TechRadar. Tech Buying Advise.
- ^ James Sanders. Software bundled by OEMs an increasing security concern: How to reduce your risks. TechRepublic. Technology Advice.















