Load All Links adware (virus) - Free Instructions
Load All Links adware Removal Guide
What is Load All Links adware?
Load All Links is a browser extension that acts as adware and causes advertisement spam
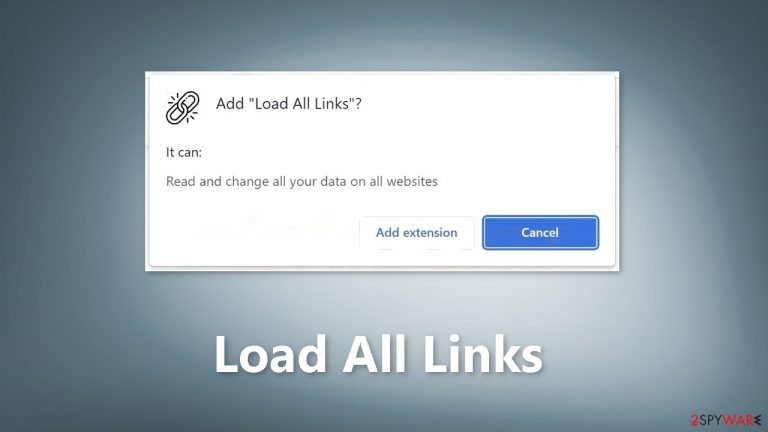
A new piece of software called Load All Links is circulating as a browser extension that promises to select all links within a webpage quickly. However, recent findings reveal that the Load All Links browser extension is actually an adware[1] that poses serious risks to users' devices and privacy.
Adware stands for advertising-supported software, designed to display advertisements on visited websites and/or interfaces. Load All Links is no exception, as it runs intrusive ad campaigns that can execute stealthy downloads and installations upon being clicked. This can lead to system infections and the spread of malware.
In addition to intrusive advertisements, Load All Links also collects private information through its data-tracking functionalities. This information can include URLs visited, webpages viewed, searched queries, personal details, and financial information, which can then be sold to third parties or abused for profit.
| NAME | Load All Links |
| TYPE | Adware |
| SYMPTOMS | Annoying pop-ups and other types of advertisements start appearing on the screen |
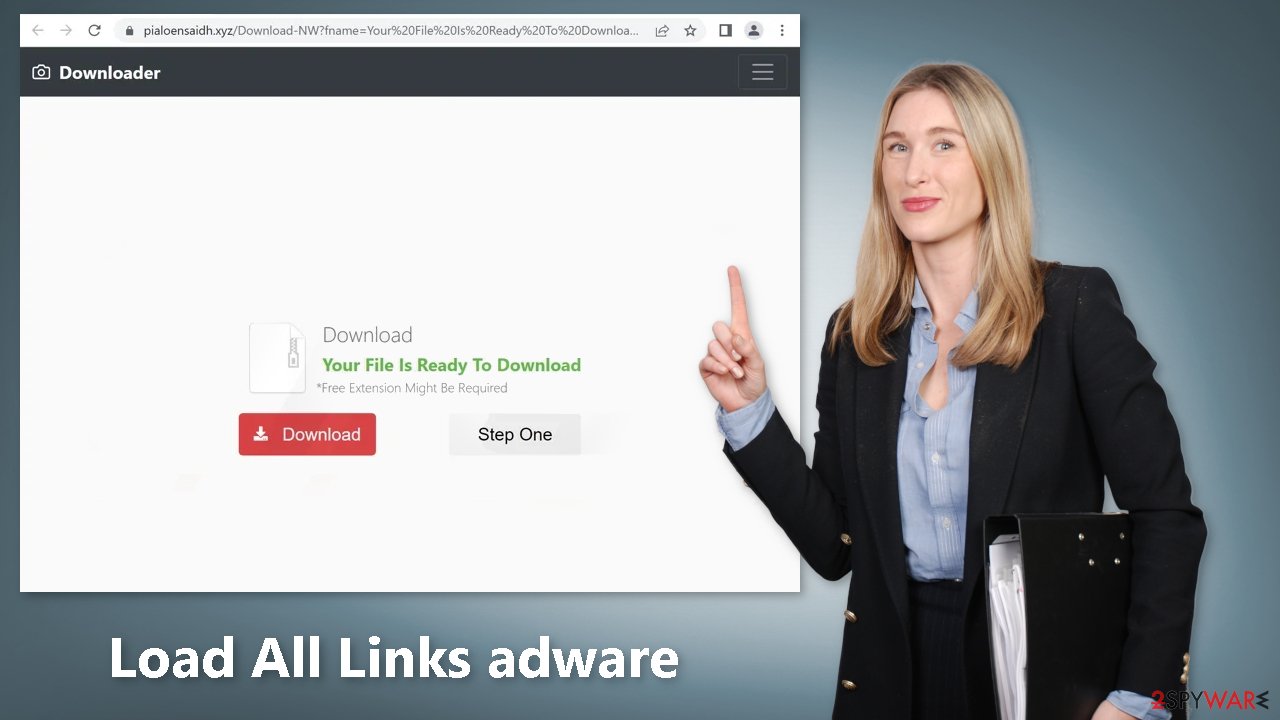
| DISTRIBUTION | Shady websites, deceptive ads, freeware installations |
| DANGERS | Links embedded in the ads might lead to dangerous websites |
| ELIMINATION | Eliminate the extension through your browser settings; scanning the machine with anti-malware tools is recommended |
| FURTHER STEPS | Use FortectIntego to get rid of any remaining damage and to optimize the machine |
How to stay safe?
The presence of Load All Links on devices can result in system infections, serious privacy issues, financial losses, and identity theft. Users are advised to be vigilant when browsing and to immediately remove all suspect applications and browser extensions upon encountering intrusive advertisements or redirects. By researching software and downloading only from trustworthy sources, users can protect themselves from the dangers of adware.
To stay safe from Load All Links and other adware, it is important to follow some key steps in order to protect your device and privacy. These include:
- Only download software from trusted sources: Download software only from official and verified sources such as app stores or the software manufacturer's website. Downloading software from dubious channels such as freeware sites or P2P sharing networks increases the risk of inadvertently allowing bundled content into your device.
- Take caution during installation: When installing software, take the time to read the terms and study possible options. Use the “Custom” or “Advanced” settings and opt out of additional apps, extensions, tools, and features. Skipping steps or using “Easy” or “Express” settings can lead to unwanted installations, including adware.
- Stay vigilant when browsing: Be mindful when browsing the web, as fake and malicious content often appears legitimate. Intrusive ads may look harmless but can redirect to questionable sites such as gambling, pornography, or adult dating sites.
- Regularly update software: Keeping your software and browser up-to-date is also crucial in protecting against adware and other cyber threats. Regular software updates often contain security patches and bug fixes that help secure your device.
Remove Load All Links adware
Load All Links adware can be removed by going to the browser settings and looking at the extension list. We recommend removing plugins one by one to see if you notice any changes.
How to prevent from getting adware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Adware. Malwarebytes. Cybersecurity Basics.
- ^ Dusan Vasic. What Are Cookies? The Good and the Bad of Browser Cookies. Dataprot. Security Solutions.
- ^ Potentially unwanted program. Wikipedia, the free encyclopedia.










