Lostdata ransomware (virus) - Free Guide
Lostdata virus Removal Guide
What is Lostdata ransomware?
Lostdata ransomware replaces the names of original files with long strings, making them inaccessible
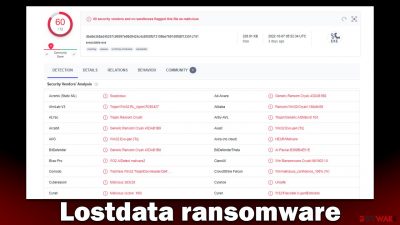
Lostdata ransomware is a devastating computer virus that you may get infected by accident. Once installed, malware would alter the way Windows operates to successfully begin the main purpose of the infection – data locking. During this time, various files located on the system (pictures, documents, databases, videos, etc.) would get locked, which would then prevent users from opening them. All affected files have their names changed and replaced with “email-lostdata1@qq.com.ver-CL 1.2.0.0.id-[ID].cbf.” Unfortunately, this issue may become permanent.
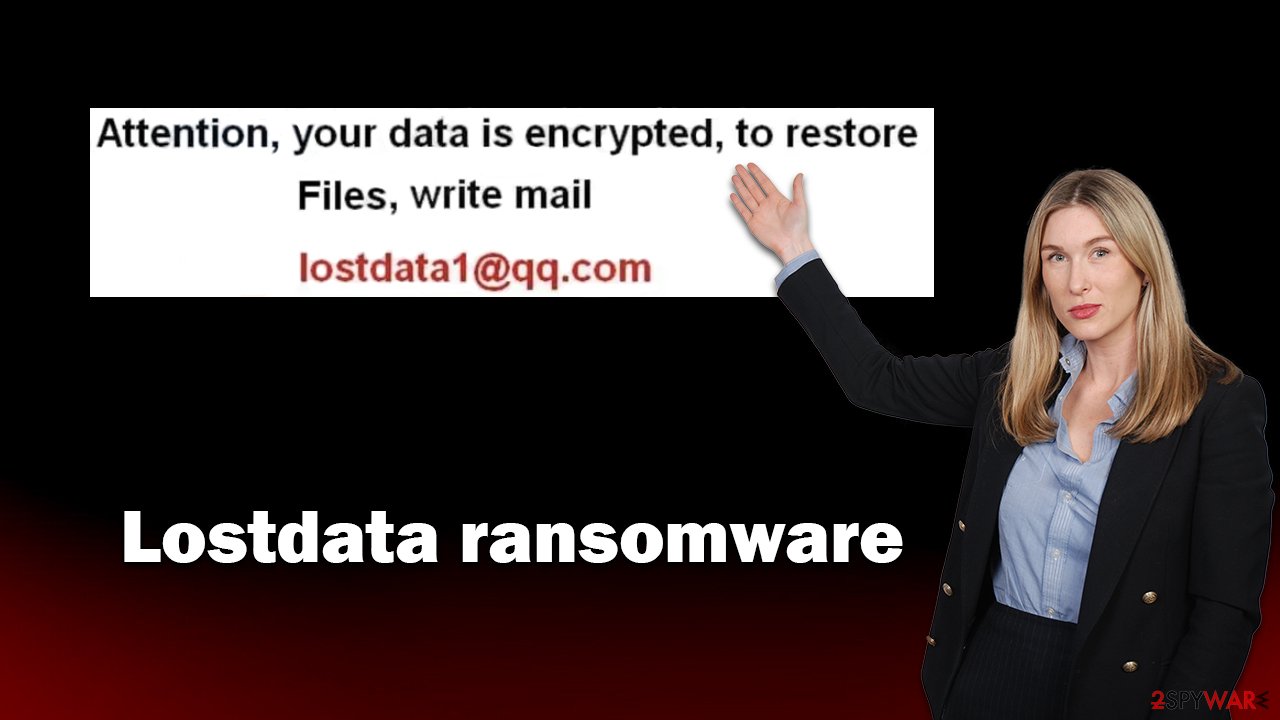
After the Lostdata virus is finished with the encryption process, it would then change the wallpaper on the PC. Unlike other similar malware, it would not deliver a ransom note and use the wallpaper instead. It would only contain a brief message which says that files have been encrypted and that users need to write an email to lostdata1@qq.com. We do not recommend doing so, and instead, follow the instructions below that would guide you through the recovery process.
| Name | Lostdata virus |
|---|---|
| Type | Ransomware, file-locking malware, cryptovirus |
| File extension | Replaces names of files with “email-lostdata1@qq.com.ver-CL 1.2.0.0.id-ID.cbf” |
| Ransom note | Replaces default wallpaper with a contact email |
| Data Recovery | If no backups are available, recovering data is almost impossible. However, we suggest you try the alternative methods that could help you in some cases – we list them below |
| Malware removal | Manual virus removal is not recommended, as it might be difficult for regular users. Instead, SpyHunter 5Combo Cleaner or other anti-malware tools should be used |
| System fix | Malware can seriously impact a Windows computer's performance and stability after it is removed. We recommend scanning the system with FortectIntego to remedy it and avoid significant stability issues |
Malware delivers a wallpaper change
As mentioned, ransomware is among the most dangerous malware types out there. It enters computers after users get tricked by some type of phishing – they either open a contaminated email attachment, have vulnerable software on their devices, or install it via software cracks/repacked installers.
While the infiltration of the virus is sneaky, its effects are visible almost immediately. The most common sign of the Lostdata ransomware is that files lose their original icons and appear to have changed names completely. Also, the most virtually significant change would be that of the original wallpaper, as it is immediately replaced by that one of the hackers'.
There, in the white background, the message is straightforward – it reads:
Attention, your data is encrypted, to restore Files, write mail lostdata1@qq.com
While it may not seem like much, the main goal of a ransom note is to deliver contact information, even though many other ransomware authors tend to explain a little bit more about the attack, such as that users have to pay a ransom in bitcoin, where to get them or how to pay. Nevertheless, it is likely that this information would be conveyed after users write an email to the attacks, which we recommend avoiding doing at all costs.
There is never a way to be sure that the attackers would provide the working decryptor, which would result in the loss of money paid in addition to files. You should avoid paying cybercriminals and relying on an alternative solution we provide below.
Remove Lostdata ransomware
It is very important how those affected by ransomware proceed, as it may impact how likely they are to recover their files. The very first thing that the affected users should do is to remove the computer from the network and internet connection so that the attackers wouldn't be able to send commands to malware via the Command & Control server.[1]
You can either do so by pulling your ethernet cable from the PC, disconnecting from WiFi from the taskbar, or employing the following method:
- Type in Control Panel in Windows search and press Enter
- Go to Network and Internet
- Click Network and Sharing Center
- On the left, pick Change adapter settings
![Network and internet 3 Network and internet 3]()
- Right-click on your connection (for example, Ethernet), and select Disable
![Network and internet 4 Network and internet 4]()
- Confirm with Yes.
You may then run a comprehensive system scan using SpyHunter 5Combo Cleaner, Malwarebytes, or another potent security program to get rid of the virus after disconnecting your PC from the machine. Although it is true that ransomware frequently self-destructs after encrypting data, this may not always be the case. Ransomware frequently spreads alongside other computer viruses (mainly data-stealing Trojans), which can harm computer security and privacy even more.
In some cases, malware may interfere with the removal process and tamper with the anti-malware operation. If you come across this issue, you can always access the Safe Mode and then perform the removal:
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.
![Windows XP/7 Windows XP/7]()
Windows 10 / Windows 8
- Right-click on the Start button and select Settings.
- Scroll down to pick Update & Security.
- On the left side of the window, pick Recovery.
- Now scroll down to find the Advanced Startup section.
- Click Restart now.
![Recovery Recovery]()
- Select Troubleshoot.
- Go to Advanced options.
- Select Startup Settings.
![Startup settings Startup settings]()
- Click Restart.
- Press 5 or click 5) Enable Safe Mode with Networking.
![Press F5 to enable Safe Mode with Networking Press F5 to enable Safe Mode with Networking]()
Fixing system issues
A computer's operating system is changed when it becomes infected with malware. For instance, an infection may damage bootup and other registry database components or destroy important DLL[2] files. As soon as system components are affected by malware, users may experience issues with performance or stability as well as usability. These problems cannot be fixed by antivirus software, and users may need to reinstall Windows entirely.
We suggest doing a scan utilizing powerful PC repair software to identify any damaged components and repair them all at once. The tool may also clean the computer of junk files and third-party trackers, as well as help with a variety of technical issues unrelated to malware threats.
- Download FortectIntego
- Click on the ReimageRepair.exe
![Reimage download Reimage download]()
- If User Account Control (UAC) shows up, select Yes
- Press Install and wait till the program finishes the installation process
![Reimage installation Reimage installation]()
- The analysis of your machine will begin immediately
![Reimage scan Reimage scan]()
- Once complete, check the results – they will be listed in the Summary
- You can now click on each of the issues and fix them manually
- If you see many problems that you find difficult to fix, we recommend you purchase the license and fix them automatically.
![Reimage results Reimage results]()
Recovering data using alternative methods
Once the infection has been removed, it is time to try to restore the files. You must create backups of the encrypted files you value before continuing since any effort at data recovery might result in irreversible file damage. You can start once you have copied them to an external media or cloud storage.
Many people think that after running an anti-malware check on their computers, they will be able to recover the encrypted data. Sadly, this is impossible since security software is not made for this purpose. It is best to use specialized recovery software. Remember that while not impossible, the likelihood of successfully retrieving files encrypted by ransomware using this approach is relatively low, although trying it is highly worth it.
- Download Data Recovery Pro.
- Double-click the installer to launch it.
![Lostdata ransomware Lostdata ransomware]()
- Follow on-screen instructions to install the software.
![Install program Install program]()
- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders where you want the files to be recovered from.
- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.
![Select Deep scan Select Deep scan]()
- Press Scan and wait till it is complete.
- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.
![Recover files Recover files]()
Thanks to the work of security experts, decryption solutions may potentially be developed for specific ransomware strains. The keys can sometimes be made public by trustworthy security companies once law enforcement agencies confiscate the criminal actors' servers[3]. You might find the following links useful:
- No More Ransom Project
- Free Ransomware Decryptors by Kaspersky
- Free Ransomware Decryption Tools from Emsisoft
- Avast decryptors

How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Command and Control [C&C] Server. Trend Micro. Security research blog.
- ^ Tim Fisher. What Is a DLL File?. Lifewire. Tech News, Reviews, Help & How-Tos.
- ^ DarkSide Ransomware Gang Quits After Servers, Bitcoin Stash Seized. KrebsonSecurity. Security news and investigation.














