MauriGo ransomware (Removal Guide) - Quick Decryption Solution
MauriGo virus Removal Guide
What is MauriGo ransomware?
MauriGo – a malicious crypto-ransomware virus targeting both home and enterprise users
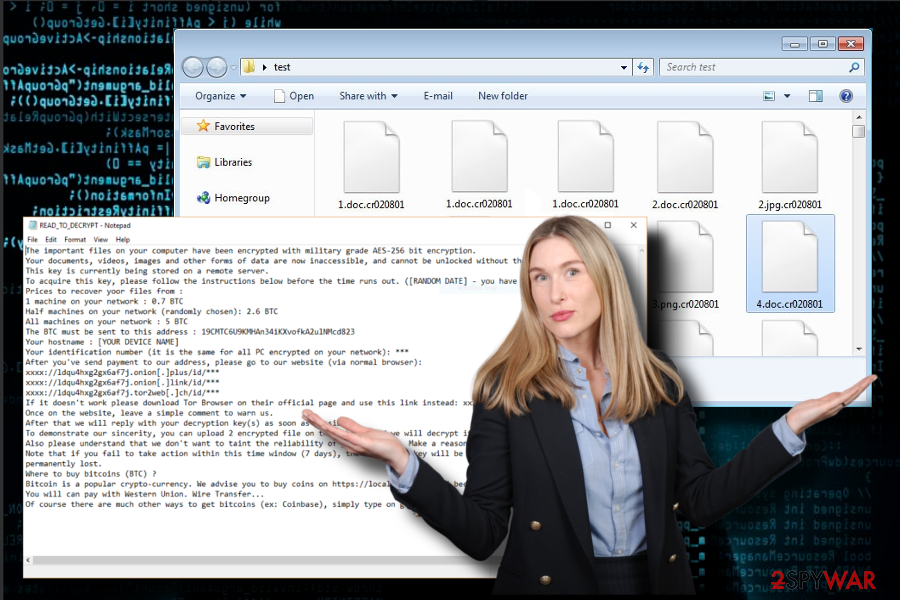
MauriGo ransomware is a severe cyber infection, which has been detected by ransomware researchers at the end of March 2018.[1] Its developers take advantage of systems' vulnerabilities and people's credulity by spreading it via spam, exploit kits, and rogue software updates. Upon infiltration, it enables AES-256 cipher to render personal files useless by appending the .encrypted file extension to each of them. Then the victim is urged to pay the ransom within seven days. The size of redemption depends on the number of PC's compromised maximizing to 5 BTC. Explicit guidance can be found in the READ_TO_DECRYPT.txt ransom note.
| MauriGo | |
|---|---|
| Malware type | Ransomware |
| Targets | Enterprise users |
| File extension | .encrypted |
| Related files | READ_TO_DECRYPT.txt |
| Cryptography | AES-256 |
| The size of redemption | 0.7, 2.6 or 5 BTC depending on the number of affected PCs. |
| Main dangers | Permanent data loss, money loss, system's crash |
| Download FortectIntego and run a full system scan to get rid of ransomware virus. Manual removal is not possible. | |
Ransomware researchers claim that MauriGo ransomware is not a newly developed cyber threat. Its strains go back to 2017, though no victims have been registered through the whole year. Nevertheless, it seems that malware developers aim to resurrect the virus for the second life.
As we have already pointed out, MauriGo spreads in the same way as other ransomware viruses. It can be dispersed under malicious spam email attachments, rogue software downloads or updates, as well as injected via hacked RDP[2] by initiating brute force attacks.
Regardless of the distribution technique, the MauriGo virus settles down quite easily by running multiple Command Prompt and PowerShell scripts under admin privileges. Then it injects malicious registry entries and starts encryption procedure.
To lock people's files, it eploys the prevailing AES-256 encryption algorithm and targets the most popular file types, including, but not limiting to .mp3, .mp4, .doc, .docx, .ibooks, .jpeg, .jpg, .torrent, .txt, and others. Upon encryption, each file is marked with .encrypted file extension.
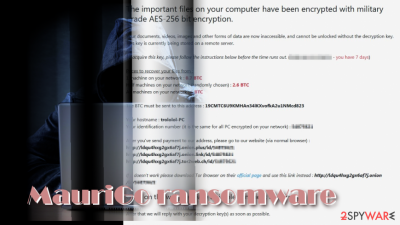
Apart from the compromised file extension, another symptom of MauriGo ransomware attack is the READ_TO_DECRYPT.txt ransom note on the desktop and most of the system's folders. The file contains the following information:
The important files on your computer have been encrypted with military-grade AES-256 bit encryption.
Your documents, videos, images and other forms of data are now inaccessible, and cannot be unlocked without the decryption key.This key is currently being stored on a remote server.
To acquire this key, please follow the instructions below before the time runs out. ([RANDOM DATE] – you have 7 days)Prices to recover yoor files from :
1 machine on your network : 0.7 BTC
Half machines on your network (randomly chosen): 2.6 BTC
All machines on your network : 5 BTC
The BTC must be sent to this address : 19CMTC6U9KMHAn34iKXvofkA2ulNMcd823
Your hostname : [YOUR DEVICE NAME]
Your identification number (it is the same for all PC encrypted on your network): ***
After you've send payment to our address, please go to our website (via normal browser):
xxxx://ldqu4hxg2gx6af7j.onion[.]plus/id/***
xxxx://ldqu4hxg2gx6af7j.onion[.]link/id/***
xxxx://ldqu4hxg2gx6af7j.tor2web[.]ch/id/***
If it doesn't work please download Tor Browser on their official page and use this link instead: xxxx://ldqu4hxg2gx6af7j[.]onion/id/***Once on the website, leave a simple comment to warn us.
After that we will reply with your decryption key(s) as soon as possible.
To demonstrate our sincerity, you can upload 2 encrypted file on the website and we will decrypt it.
Also please understand that we don't want to taint the reliability of your business. Make a reasonable choice.
Note that if you fail to take action within this time window (7 days), the decryption key will be destroyed and access to your files will be
permanently lost.Where to buy bitcoins (BTC) ?
Bitcoin is a popular crypto-currency. We advise you to buy coins on https://localbitcoins.com/ because of its speed and anonymity. You will can pay with Western Union. Wire Transfer…
Of course, there are many other ways to get bitcoins (ex: Coinbase), simply type on google “how to buy bitcoins.”
As you can see, crooks target both home users and enterprise users. Indeed, they prefer corporate networks as they can get up to 5 BTC (approximately 47 000 USD) ransom in exchange of a decryptor, while a home user is expected to transfer 0.7 BTC (approximately 6500 USD).
The PC's owner that wants to get his or her files back has to email criminals and send them a redemption to the 19CMTC6U9KMHAn34iKXvofkA2ulNMcd823 Bitcoin wallet using Tor browser. The deadline – 7 days. In case the victim fails to make the payment, the MauriGo decryptor is removed causing permanent data loss.
Nevertheless, Virukset.fi[3] together with our research team highly do not recommend paying the ransom. That's because no one can assure if the decryptor has been developed altogether. It might be that crooks don't have it at all and simply will run away with your money.
Instead of that, we recommend running a scan with FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes security tool and remove MauriGo virus asap. Following the encryption, you'll be able to take advantage of the alternative data recovery methods, such as Volume Shadow Copies or Previous Windows version.
Take precautionary measures while browsing online to protect yourself from ransomware attacks
Throughout a long time of practice, ransomware developers learned people's habits and behavior online. Consequently, they can create multiple catchy strategies to distribute ransomware viruses widely on the Internet. The following are the most frequently used techniques:
- Malicious spam email attachments;
- Exploit Kits;
- Hacked Remote Desktop apps;
- Fake software updates;
- Phishing websites;
- Infected links and advertisements;
For the past ten years, hackers take advantage of people's credulity and keep spreading hazardous cyber infections in the form of malicious email attachments. Rendering spam bots criminals spread legitimate-looking emails, which contain “urgent” information from Microsoft, Apple, IRS, FBI, and similar institutions. If the user opens the attachment, he or she inadvertently runs a ransomware payload, which is going to lock files soon after revelation.
Although there's no hundred percent ransomware protection, keeping a reputable anti-virus installed and updated minimizes the risk of getting infected significantly. Also, you should also download Windows updates to patch security vulnerabilities.
MauriGo removal options
In fact, there aren't many options for the MauriGo removal. All you can choose is an anti-virus program because manual ransomware removal is practically impossible. We would strongly recommend you to use FortectIntego or SpyHunter 5Combo Cleaner tool, but you are free to choose a program that you prefer.
As soon as you remove MauriGo virus, scroll down to the bottom to find out alternative data recovery methods. Try them one-by-one, and we are sure that you'll manage to retrieve at least the most significant part of files encrypted by MauriGo ransomware.
Getting rid of MauriGo virus. Follow these steps
Manual removal using Safe Mode
If you cannot launch your anti-virus, follow the below-given steps to bypass ransomware helper objects.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove MauriGo using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of MauriGo. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove MauriGo from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.Neither of the methods listed below is proved to be hundred percent working. Nevertheless, we highly recommend you to try them one-by-one because there's a high possibility to recover your files without paying thousands of US dollars for criminals.
If your files are encrypted by MauriGo, you can use several methods to restore them:
Data Recovery Pro
Data Recovery Pro – a free tool, which has been developers with an intention to recover accidentally deleted files. Soon after the release, it turned out to be useful when the data is lost during system's crash. Finally, cybersecurity experts found it capable of encrypting files locked by ransomware. Thus, give this tool a try.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by MauriGo ransomware;
- Restore them.
Enable Previous Windows Version
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Exploit Volume Shadow Copies
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
There's no MauriGo decryptor yet.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from MauriGo and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Michael Nadeau. 11 ransomware trends for 2018. CSO from IDG.
- ^ Dealing with ransomware and remote access hacking. Security Central. A one stop shop for individuals and small businesses in New Zealand.
- ^ Virukset. Virukset. Virus and spyware news.





















