Mirai virus (Removal Guide) - updated Nov 2018
Mirai virus Removal Guide
What is Mirai virus?
Mirai malware is a sophisticated botent launched by cybercriminals in 2016 and is still active today
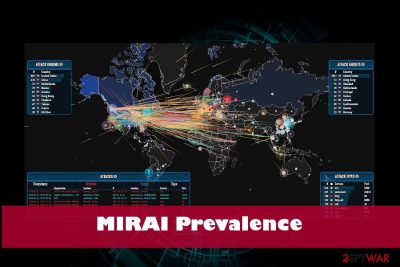
Mirai botnet or Mirai virus is sophisticated malicious software that was first potted by a whitehat malware research group MalwareMustDie in August 2016. The virus focuses on abusing vulnerabilities on IoT devices that run on Linux operating system. The primary goal of Mirai was to create a worldwide botnet which hosted DDoS attacks targeted towards large organizations like DNS provider Dyn and cloud computing company OVH, as well as security website Krebs on Security, although it was also used for fraud like click-bait. According to its creator, Anna-senpai, the name of the threat came from anime series Mirai Nikki and generally means “Future” in Japanese. At the end of 2016, Mirai malware was leaked to the public for everybody else to use. Since then, multiple attacks have been launched, and the most recent one seems to be utilizing Hadoop YARN vulnerability to attack Linux machines instead of IoT devices.
| Name | Mirai |
| Type | Malware/botnet |
| Symptoms | Causes massive DDoS attacks, outage of popular websites, disables the Internet for thousands of people |
| Distribution | Exploits IoT vulnerabilities |
| First detected | In 2016. Suspended in 2016 as well. The source code leaked allowed hackers to release altered Mirai malware versions |
| Versions known | Clickfraud, OMG, Okiru |
| Removal | Use a professional anti-virus tool. Our recommendation is FortectIntego |
In 2017, USA officials unsealed court document indicating the names of the three men responsible for the Mirai botnet development and massive DDoS attacks. Paras Jha, Josiah White, and Dalton Norman were indicted by Alaska court on multiple charges. All of them acknowledged the participation in the attacks and were plagued guilty. Each of them was imposed for up to five years imprisonment and a fine of at least $250,000.[1]
Mirai botnet and Mirai malware are the terms that are used interchangeably and can be. The core difference is that the system should initially be infected with Mirai malware to be connected to Mirai botnet later.
Mirai botnet refers to a “bot” of networked devices running Linux that are joint together and controlled remotely by a group of hackers. The interconnected devices are further scanned for IP address of Internet of things (IoT) devices. The scan allows the malware to identify the vulnerabilities in IoT devices (routers, cameras, DVRs, and other Internet of Things) by applying a table of 60 common factory default usernames and passwords.
Once the botnet detects vulnerable devices, they are infected with Mirai malware. Infected machines are initially hard to recognize as they keep working in a quite usual manner despite some periods of slowdowns or random crashes.
However, the Mirai is a severe IoT malware that can be used for launching DDoS attacks massively and causing real havoc on the Internet infrastructure worldwide.
Mirai botnet utilizes Hadoop vulnerability to attack Linux servers
Security researchers at NETSCOUT ASERT spotted[2] a new variant of Mirai which avoids IoT devices and seeks to infect Linux operated servers instead. It abuses Hadoop YARN vulnerability CVE-2017-15718[3] that can execute arbitrary shell commands on an unpatched server. According to research, there are over 1,000 vulnerable servers that are exposed.
In November alone, experts observed 225 unique attacks, from which 152 were delivered from one address. A large amount of exploit attempts coming from only a few sources led researchers to the conclusion that there is only a small number of attackers who are scanning the internet to exploit the vulnerable machines (Mirai does not rely on a botnet to propagate). This time, bad actors depend on x86 machines only, as Hadoop YARN (Yet Another Resource Negotiator) services are only running on x86 Linux servers.
Once injected, the payload then starts brute-forcing Telnet credentials, just as the original version did. Mirai virus also uploads DemonBot DDoS bot and cryptocurrency mining malware.
One of the variants observed by researchers was called VPNFilter, although it has nothing to do with the sophisticated malware that infected 500,000 devices in May.
Attacks against famous companies attract attention to Mirai botnet
Mirai virus[4] got into the spotlight again after disrupting the Internet connection for German telecommunication company, Deutsche Telecom, users[5]. While the virus occasionally appeared here and there since then, daily Internet users might not have worried about its threatening presence. However, the attack against Deutsche Telecom has been a serious warning for the entire virtual community.
After updating its source code, hackers employed the malware for disabling the Internet connection for about million users of Deutsche Telecom customers. Specialists suspect that the cyber criminals did not plan to shut down the connection but merely steal vital information from the affected devices. However, as the server was overloaded with malware signals, the campaign did not work out as expected.
Luckily, only 5% of all clientele might have suffered from the cyber attack. Zyxel routers happen to be one of the most vulnerable devices[6]. Though virus researchers expect the malware to slow down in the following days, signs of related DDoS attacks have been traced to Africa. What is more, the origin of September attacks on Japan’s defense and SDF (Self Defense Forces) and Korea’s military cyber systems are questioned as well. Such Internet disrupting cyber assaults were not the only ones recently. Last month, several US telecommunications companies experienced a similar attack.
The origin of the Mirai
Mirai malware is supposedly originated from Japan as the title means “future” in Japanese[7]. What is more, is an author is expected to be a user under the pseudonym “Anna-senpai”[8]. The very name originated from Japanese anime culture. Though daggers are pointed to Japanese hackers, these attacks are most likely the wrongdoings of foreign cyber criminals.
However, international racketeers have joined this ominous business as the latter version of Mirai (Linux.Gafgyt.B) might have come from Brazil. Brazilian hackers have been the primary suspects for launching banking trojans. The original version of Mirai malware targets mainly IoT technologies and Linux systems. By exploiting vulnerable IoT devices, the virus turns them into a virus-distributing botnet. Mirai network has been used for delivering massive DDoS (distributed-denial-of-services) attacks as well.

Clickfraud botnet allowed crooks to generate revenue artificially
Within a year since 2016 to 2017, the group of three American programmers managed to infect more than 100,000 computing devices and connected them to a bot, later named as Clickfraud.
The infamous Clickfraud bot[9] allowed crooks to generate revenue by scamming online ad networks and simulating clicks. After the attacks were unraveled, John Cronan, an assistant attorney general, stated:
The Mirai and Clickfraud botnet schemes are powerful reminders that as we continue on a path of a more interconnected world, we must guard against the threats posed by cybercriminals that can quickly weaponize technological developments to cause vast and varied types of harm.
The scheme earned Jha and his team nearly 100 bitcoin, which was worth then approximately $180,000. Currently, the earning would exceed $7.5 million
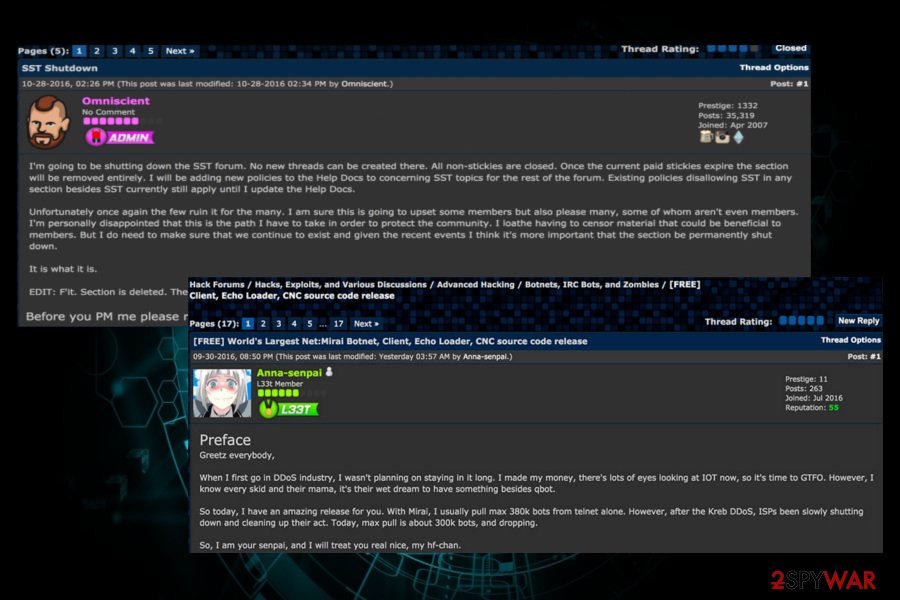
Mirai source code leaked after the massive DDoS attack
Jha, the developer of Mirai malware's source code, has released it publicly a week after the massive DDoS attack was being held. It has been first published in the English-language hacking community called Hackforums. Disguised under the nickname “Anna-senpai,” the Jhas told community members:
When I first go in the DDoS industry, I wasn’t planning on staying in it long,” Anna-senpai wrote. “I made my money, there are lots of eyes looking at IOT now, so it’s time to GTFO [link added]. So today, I have an amazing release for you. With Mirai, I usually pull max 380k bots from telnet alone. However, after the Kreb [sic] DDoS, ISPs been slowly shutting down and cleaning up their act. Today, the max pull is about 300k bots and dropping.
Once the Mirai botnet source code has been unraveled, cybercriminals started exploiting it for multiple DDoS attacks against Internet infrastructure and websites.
Currently, there altered versions of Mirai have been spotted on the Internet. Mirai Okiru Botnet[10] is one of the examples. Experts spotted it at the beginning of 2018 by MalwareMustDie team. It targets ARC-based embedded devices running Linux operating system.
In February, FortiGuard Labs research team found another botnet dubbed OMG, which has been found selling credential access to the proxies for profit. According to experts,[11] OMG report uses the original Mirai module that kills processes, scan for vulnerabilities, use brute-force login attacks, and eventually cause DDoS attacks. However, it renders two random ports to set up 3proxy.
Thus, despite the fact that the initiators of the Mirai botnet have been arrested and jailed last year, the released source code allows crooks to keep distributing the malware worldwide.
Malware distribution explained
Since the malware exploits the vulnerabilities in the specific devices, manual tracking Mirai botnet might be a futile task. If you are about to purchase IoT device, look up its manual and identify its manufactured company. After obtaining the device, change the default password into a long code containing marks, characters, and numbers. You might also set an elaborate encryption technique to your Wi-FI or wired Internet network. Modifying security settings is a useful prevention method as well. Turn off Telnet login and employ SSH. Check your IoT manufacturer for latest updates.
Terminating Mirai malware
Though Mirai virus mainly attacks IoT devices, it is destructive to think that Windows OS or Mac OS owners users are safe from this cyber misfortune. Since the developers got determined to surprise the world with unseen hijack techniques, arming with reliable protection is of primary importance. In the case of mentioned operating systems, you can remove Mirai by using FortectIntego or Malwarebytes.
Keep in mind that the utilities have to be updated for them to work properly. In order to terminate Mirai hijack, disconnect from the internet and enter Safe Mode with networking. Further instructions will explain in detail how to do that. They will also come in handy if you cannot complete Mirai removal.
Getting rid of Mirai virus. Follow these steps
Manual removal using Safe Mode
If you suspect that Mirai worm or similar threat has invaded your device, you might enter Safe Mode and scan your system with an anti-spyware tool.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Mirai using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Mirai. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Mirai from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Mirai, you can use several methods to restore them:
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Mirai and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting malware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Alfred Ng. Three plead guilty to creating Mirai botnet used to crash web. Cnet. Software distribution, news site.
- ^ Matthew Bing. Mirai: Not Just For IoT Anymore. Netscout. Security research.
- ^ Vulnerability Details : CVE-2017-15718. CVE Details. Security vulnerability datasource.
- ^ Mirai (malware). Wikipedia. The free encyclopedia.
- ^ Eric Auchard . German internet outage was failed botnet attempt: report. Reuters. Business and Financial News, US and International Breaking News.
- ^ Michael Kan. Upgraded Mirai botnet disrupts Deutsche Telekom by infecting routers. PC World. News, tips, and reviews from the experts on PCs, Windows and more.
- ^ Security of Internet of Things Devices to Be Rated for First Time. Sputnik International. News and commentary.
- ^ Who is Anna-Senpai, the Mirai Worm Author?. Krebs on Security. In-depth security news and investigation.
- ^ Swati Khandelwal. Friday's Massive DDoS Attack Came from Just 100,000 Hacked IoT Devices. The Hacker News. Cyber security news site.
- ^ Mohit Kumar. New Mirai Okiru Botnet targets devices running widely-used ARC Processors. The Hacker News. Cyber security news site.
- ^ Jasper Manuel, Rommel Joven, Dario Durando. OMG: Mirai-based Bot Turns IoT Devices into Proxy Servers. Fortinet. Top-rated network and content security.





















