News-fujaya.cc ads (scam) - Free Instructions
News-fujaya.cc ads Removal Guide
What is News-fujaya.cc ads?
News-fujaya.cc is a fake site made to scam users

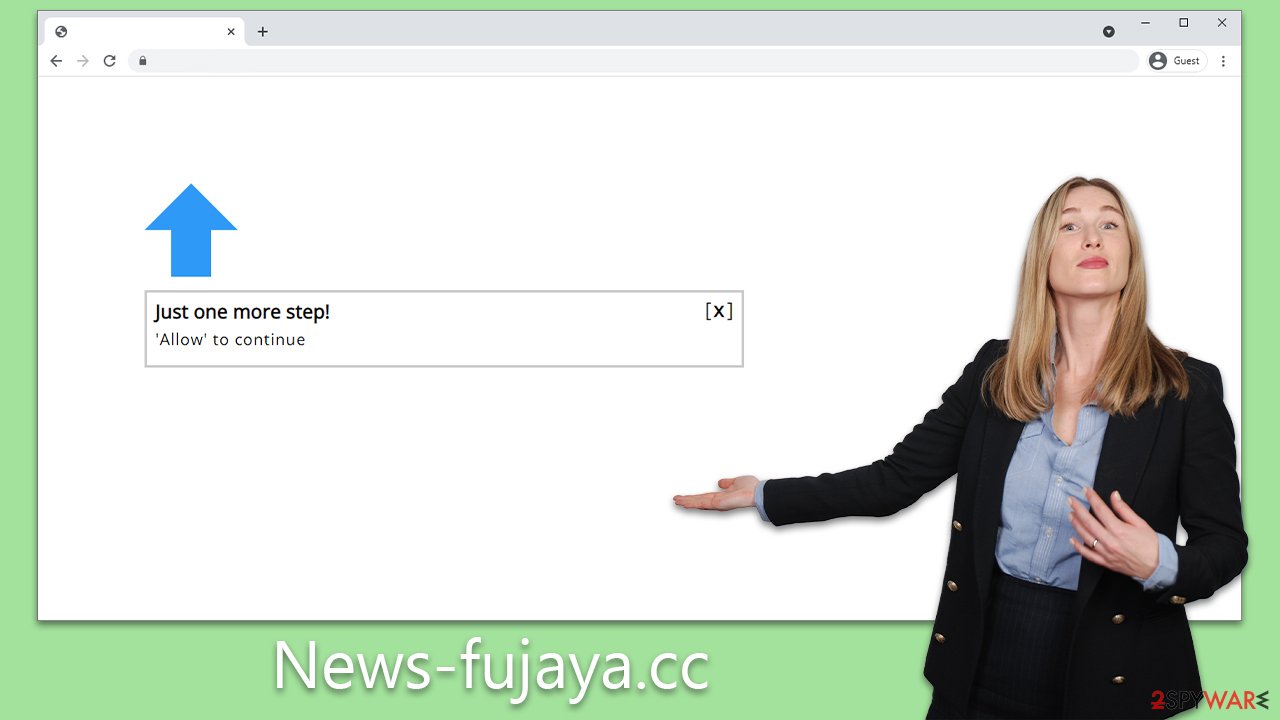
News-fujaya.cc is a dubious website that users might inadvertently encounter while navigating the internet via popular browsers such as Google Chrome or Mozilla Firefox. This site is engineered around a deceitful model, where the main objective is to illicitly profit from uninvited advertisements. These ads are programmed to overlay any active applications, ensuring maximum visibility. Through adept use of social engineering techniques, unsuspecting users are often lured into subscribing to these push notifications.
Push notifications from News-fujaya.cc pose a significant threat to both user privacy and security while online. These alerts not only consistently expose users to potentially dangerous content, making it increasingly challenging to evade tracking by these entities, but also sometimes mislead with enticing offers.
For instance, a user might receive a message claiming they've secured a high-end prize, prompting them to share personal details like their home address to claim it. By falling into this trap, they inadvertently provide cybercriminals with access to sensitive information. In some scenarios, users might even be deceived into downloading malware or other undesirable software.
| Name | News-fujaya.cc |
| Type | Push notifications, ads, scam, phishing |
| Distribution | Users start seeing intrusive pop-ups at some point after they click the “Allow” button within the site's notification prompt |
| Symptoms | Once enabled, notifications from malicious websites would bring misleading or other suspicious content to your screen. These links could lead to malware-laden, scam, phishing, or similar malicious sites |
| Risks | If you click on links provided by the website, you might end up infecting your system with malware/PUPs, disclosing your personal information to cybercriminals, or losing money for useless services |
| Removal | In order to block push notifications, access your browser settings. By running a scan with SpyHunter 5Combo Cleaner, you can check if your system is infected with malware or adware |
| Other steps | Third parties can use cookies to continue tracking your online activities, so we recommended clearing browser caches and other leftover files with FortectIntego |
Understanding the scam
Many users first become acquainted with the News-fujaya.cc name upon encountering advertisements bearing its label. Yet, their inaugural interaction with the site typically occurs unanticipatedly and is easily overlooked. There are primarily two routes by which individuals find themselves on these questionable sites:
- Adware-induced activities might result in unwarranted redirects or the appearance of suspicious ads in unusual locations. For example, while accessing a website that's typically ad-free, an intrusive pop-up or auto-executing script might reroute you to an untrustworthy site.
- Websites with a higher risk profile are often culprits for hosting malicious materials. A user might be misled into downloading and initiating ransomware, mistakenly believing it to be legitimate software. Likewise, deceptive links or “Download” prompts can lead individuals to a myriad of harmful sites.
To fortify the defenses of your digital environment, it's vital to actively screen for adware and consciously sidestep high-risk websites. Disregarding notifications from security tools jeopardizes your system's safety; thus, it's imperative to heed every warning diligently.
Understanding the scam techniques
When individuals access News-fujaya.cc, they are typically prompted to verify their age or confirm that they're not a robot – a familiar verification step for many web users. Yet, due to the sudden nature of this request, some might be caught off-guard and consequently duped.
In the absence of a clear context, users may be falsely led to anticipate an imminent action – like the playback of a video or the announcement of a prize win. To illustrate how these misleading prompts might be presented, consider the following examples:
Click Allow to watch the video
Press “Allow” bot verify, that you are not robot
Click “Allow” to win a prize and get it in our shop!
If you are 18+, click Allow
Browser verification in progress – click the button “Allow” to access
Taking undue advantage of the notification request, fraudsters sow confusion, especially among users familiar with captcha-based age verification. They further bait users with counterfeit offers, such as enticing videos or elusive rewards, to prompt action.
To reiterate, such sites offer no genuine value, and messages showcased therein ought to be disregarded. If you've inadvertently permitted push notifications from News-fujaya.cc, there's little reason for alarm. Ensure you refrain from interacting with any subsequent pop-ups to maintain your security.
Removing the malicious push notifications
Push notifications, if activated through questionable methods, might sometimes be misconstrued as evidence of a malware attack. It's pivotal to understand that push notifications always seek user approval before operating at the system level, regardless of whether this consent was deliberate.
If you've already scrutinized your system for potential threats and are confident of its integrity, the next step is to halt these intrusive notifications from surfacing in the future.
To achieve this, it's imperative to block the website URL – News-fujaya.cc – within your web browser's settings. Detailed instructions for various web browsers can be found below.
Google Chrome
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Google Chrome (Android)
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off position).
![Stop notifications on Chrome Android Stop notifications on Chrome Android]()
Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
MS Edge
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.
![Stop notifications on Edge Chromium Stop notifications on Edge Chromium]()
Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
![Stop notifications on Internet Explorer Stop notifications on Internet Explorer]()
- Locate the web address in question under Allowed sites and pick Remove.
Deleting adware and other unwanted software
After removing unwanted pop-ups from News-fujaya.cc, it's crucial to thoroughly inspect your computer system for any signs of infections. A system compromised with adware or different strains of malware often exhibits symptoms such as persistent redirects to dubious websites and an unusual uptick in ads while navigating the web.
To effectively pinpoint and eradicate these nuisances, it's recommended to employ reliable security software solutions, specifically SpyHunter 5Combo Cleaner or Malwarebytes. Utilizing such tools ensures multiple benefits. Firstly, it guarantees the optimal functioning of your system FortectIntego by weeding out any potential threats.
Secondly, it purges the system of any lurking trackers that might compromise user privacy. Moreover, this approach not only mends any damages inflicted by viruses but also proactively addresses potential stability issues, ensuring your computer runs smoothly and securely.
How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.






