News-vaduza.cc ads (fake) - Free Guide
News-vaduza.cc ads Removal Guide
What is News-vaduza.cc ads?
News-vaduza.cc shows fake messages to encourage people to enable push notifications

News-vaduza.cc is a deceptive website that many users inadvertently come across when browsing less secure parts of the internet. These might include platforms offering unauthorized software downloads or streaming copyrighted materials. Additionally, having adware on one's computer might redirect users to the site without their conscious intent.
Upon visiting the website, users face a notification request. This request, seemingly benign on the surface, is paired with an image containing a persuasive message designed to encourage users to click the “Allow” button. Unfortunately, News-vaduza.cc employs misleading strategies and provides false justifications to coerce users into consenting to these notifications. Once users agree, they receive intrusive and unwarranted ads through the website's push notifications.
Such circumstances are potentially dangerous. Users are at risk of receiving deceitful messages and links, leading them to unsafe websites. These can further entice them to sign up for more notifications, download harmful software, or even inadvertently share personal information.
For the safety and security of users' digital environments, it is highly advised to avoid such untrustworthy websites. Additionally, it's imperative to follow comprehensive removal guidelines to eliminate any ads from News-vaduza.cc, as well as any potentially harmful software or adware that might have found its way onto your system.
| Name | News-vaduza.cc |
| Type | Push notifications, ads, pop-ups, scam |
| Distribution | The unwanted activity starts at some point after the Allow button is pressed within the notification prompt |
| Symptoms | Pop-up notifications are shown on a desktop at random times |
| Risks | Shown pop-ups incorporate fake notices and push scams. Links can also lead to websites filled with malware |
| Removal | Navigate to your browser's settings to halt unwanted push notifications. Subsequently, ensure your system hasn't been compromised by adware or malware by running a scan with SpyHunter 5Combo Cleaner |
| Repair & tips | You should check your system with FortectIntego to fix virus damage and remove various trackers from your browsers |
How users reach scam sites
Users often find themselves on scam websites inadvertently, exposing themselves to potential threats such as malware, phishing schemes, and other harmful content. This typically occurs through a series of clicks that ultimately lead them to insecure websites. The usual suspects behind these unwanted detours include torrent websites, social media platforms, and messaging apps, where users might impulsively click on links or download files without fully comprehending the associated risks.
Another common gateway to suspicious links and redirects is adware, a type of software notorious for bombarding users with unwanted ads or pop-ups. Adware often infiltrates a user's device through free software downloads or by enticing clicks on deceptive advertisements. Once installed, it stealthily tracks a user's online activities and redirects them to malicious destinations. In some distressing scenarios, adware can even tamper with a user's browser settings, making its removal a challenging task.
To safeguard against falling prey to malicious websites, users should exercise caution and implement several preventive measures. Firstly, they should exercise discretion when encountering links from unknown sources, particularly on social media, messaging apps, or email. Secondly, it's imperative to abstain from downloading files from untrustworthy origins or engaging in illegal content downloads through torrent sites. Thirdly, installing and regularly updating antivirus and antimalware software on their devices is vital to detect and eradicate any lurking malicious software.
Furthermore, users must be vigilant when downloading free software, as many of these downloads come bundled with adware or other undesirable software components. Careful scrutiny of terms and conditions, coupled with opting out of any supplementary offers or downloads during the installation process, is advisable. Lastly, users should diligently keep their operating systems and web browsers updated, as these updates often contain security patches that fortify defenses against malicious attacks.
Scam methods
The scammers operating behind News-vaduza.cc employ cunning tactics to catch users off guard and manipulate their unsuspecting nature. This website thrives on the element of surprise, presenting prompts that initially seem harmless. Users are often asked to verify their humanity or confirm their age, requests that appear innocuous but are, in reality, carefully crafted social engineering ploys commonly used in online scams.
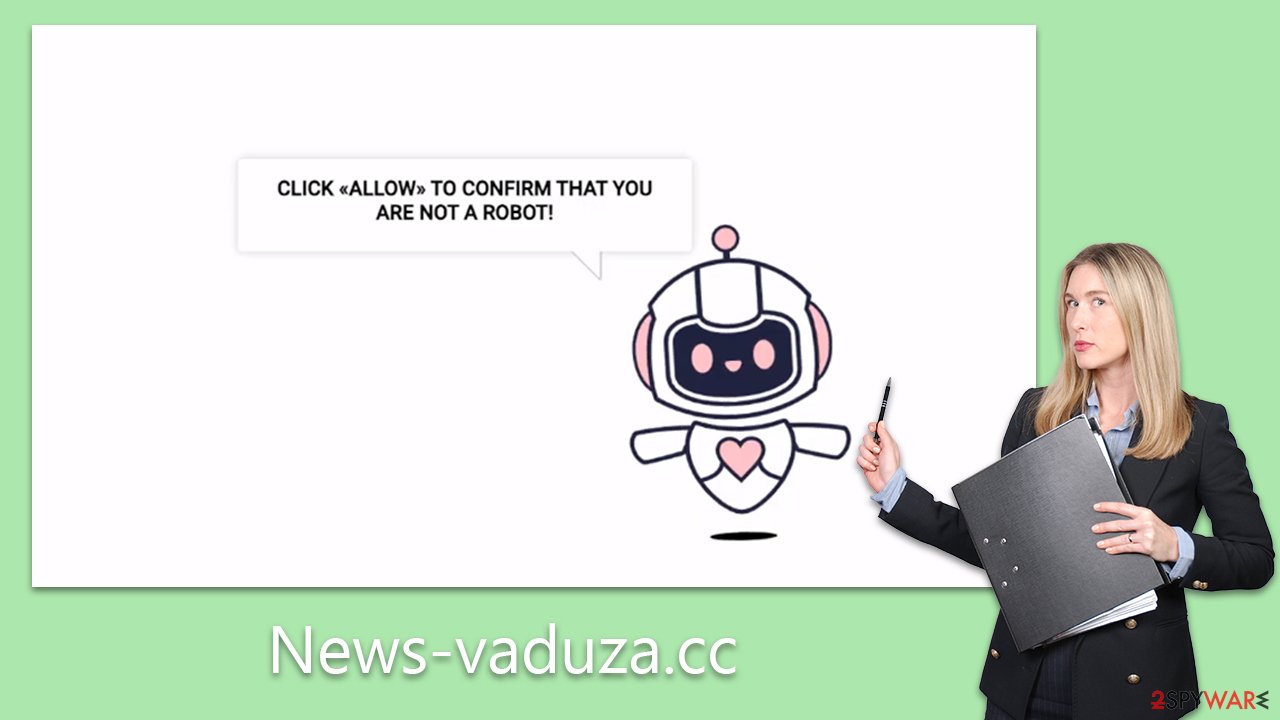
The primary objective of these scammers is to deceive users into believing that clicking the “Allow” button serves a different purpose than it actually does. To achieve this, they rely on premeditated and manipulative messages and images, which are consistently employed across various push notification scam sites. Some examples of these deceptive prompts include:
- “Click Allow to confirm that you are not a robot.”
- “Can't play this video! Perhaps your browser doesn't allow video playback. Please click the Allow button to watch the video.”
- “Your file is ready to download – press Allow to continue.”
- “Click 'Allow' to win the prize and get it in our shop!”
- “If you are 18+, click Allow.”
It's important for users to understand that granting permission to a push notification prompt essentially authorizes News-vaduza.cc to send a variety of information, including misleading links and fabricated messages, through the browser's API, as long as the browser remains active or runs in the background.
Thankfully, managing these intrusive notifications is a straightforward process once users are familiar with the steps to stop them. The following section provides a detailed explanation of the procedures to follow in order to prevent these notifications and ensure a safer and more secure browsing experience.
Removal of unwanted ads
Users encountering intrusive push notifications from News-vaduza.cc may find themselves perplexed regarding the origin of these notifications and their underlying causes. The appearance of suspicious pop-ups could lead individuals to suspect a computer virus infection, prompting them to consider using security software to scan their devices for potential threats. However, it's essential to note that push notifications can only be manually disabled through browser settings, a task that can be daunting for some users.
Nonetheless, it is crucial to initiate a thorough scan of the device to detect any lurking adware or other unwanted software that might be operating discreetly in the background, unbeknownst to the user. Malware may surreptitiously infiltrate the system during the download of repackaged software or exposure to malicious advertisements. This entire process is devious, and users may remain oblivious to the fact that their system's integrity has been compromised.
To address this issue effectively, it is highly recommended to employ robust security software, such as SpyHunter 5Combo Cleaner or Malwarebytes, to conduct a comprehensive system scan before proceeding with the removal of News-vaduza.cc ads. Additionally, utilizing FortectIntego to purge browser caches, including cookies, can play a pivotal role in ensuring that no data tracking or invasive activities continue to occur in the user's online environment.
Google Chrome (desktop)
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Google Chrome (Android)
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).
![Stop notifications on Chrome Android Stop notifications on Chrome Android]()
Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.
![Stop notifications on Edge Chromium Stop notifications on Edge Chromium]()
Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
![Stop notifications on Internet Explorer Stop notifications on Internet Explorer]()
- Locate the web address in question under Allowed sites and pick Remove.
How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.






