News-xowehu.cc ads (scam) - Tutorial
News-xowehu.cc ads Removal Guide
What is News-xowehu.cc ads?
News-xowehu.cc ads can lead to malicious websites
Like many other users, you could have been puzzled as to why News-xowehu.cc ads started to emerge on your desktop unexpectedly. You see these pop-ups because you gave the website permission to deliver push notifications to your computer or another device. It's normal if you can't recall providing permission because deceptive phishing[1] messages are frequently used to trick unsuspecting users into doing so.
News-xowehu.cc push notifications are extremely intrusive, as they would be shown regardless of which websites are being visited and also cover any other apps running at the time. But the most dangerous aspect of this activity is that these ads are often insecure and include phishing messages and links to malicious websites, which could get users infected with malware or make them provide their personal information.
If you are dealing with this problem, you should avoid interacting with News-xowehu.cc pop-ups and check your system for adware and other infections. Redirects to suspicious websites are often a sign of adware, so in addition to providing instructions on eliminating push notifications, we'll also show how to effectively remove all malware from your device.
| Name | News-xowehu.cc |
| Type | Push notifications, ads, pop-ups, scam |
| Distribution | After users click the “Allow” button within the prompt upon site entry |
| Symptoms | Pop-up notifications are shown on a desktop at random times |
| Risks | Various security problems due to exposure to scams, monetary losses, system infections, etc. |
| Removal | You can stop intrusive push notifications by blocking the website's URL in browser settings. It is also important to check the system for adware or other infections |
| Tips | Some remnants of apps stay in browsers and can be used for tracking. Delete these with FortectIntego, which can also fix any virus damage found on the system |
The fake messages used by scammers
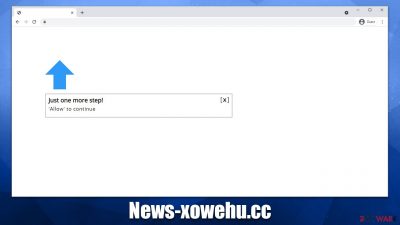
The identical words and graphics are used by thousands of websites to trick visitors into subscribing to push notification spam – they have the same layout and functionality. News-xowehu.cc, along with Thepositiveimpactnow.com, Newadsfit.com, Topmusicalcomedy.com, and many others, can use one of the following messages upon users accessing the site (note that the messages can differ in wording slightly):
- Press “Allow” to verify, that you are not a robot
- If you are 18+, click Allow
- Just one more step! “Allow” to continue
- Download is ready – click Allow to download your file
- Click “Allow” to win a prize and get it in our shop!
It is not difficult to see how some people could get misled by these statements. For example, most internet users have previously encountered verification processes such as age confirmation or selecting the correct items in a set of images. However, this is something entirely different, even though crooks are trying hard to make you believe otherwise.
Remember, the request to enable push notifications has only one function – to enable push notifications from that particular site. Regardless of what the background picture and the message claim, pressing the “Allow” button would also permit the site to deliver information via the browser's API[2] without warning.

Checking the system for adware
We urge you to scan the system for adware and other possible infections. Though it's probable that you clicked on a malicious link that led you to News-xowehu.cc, there's also a chance that adware could be causing this problem. Oftentimes, its developers utilize bundling and similar deceptive distribution methods, so the user might not even be aware of the infection. To play it safe, it's better to be cautious.
The simplest approach to guarantee that all adware and malware are located and properly removed is to scan the system using SpyHunter 5Combo Cleaner, Malwarebytes, or another potent anti-malware. Also, it is important to have a security tool running at all times, as it can serve as the best defense against dangerous ransomware[3] or other malware attacks.
We also advise protecting your privacy after getting rid of any viruses and adware. Additional little items might be installed on your device to track your internet habits and other information when you browse websites, which may put your privacy at risk. Particularly cookies are used to track the websites users visit, the links they click, timestamps, and other similar details. In some cases, even personal data may be gathered, so it's important to make sure trackers are removed at once.
We thus advise you to use FortectIntego repair and maintenance tool to make sure that your device is clear of cookies and other trackers in order to be certain that this information is no longer monitored. The app is also great at dealing with problems that could arise after malware elimination, including system crashes or errors.
Remove intrusive push notifications
News-xowehu.cc push notification subscriptions are always done unintentionally, and because the suspicious activity doesn't start until sometime later, users may completely forget the ordeal. Only after intrusive pop-ups start showing up do they realize something is wrong and begin to look for answers.
The first assumption is usually a virus infection, although this is not the case here. Push notifications only require you to click the “Allow” button within the prompt, and it does not mean that something malicious is running on your system (although it is important to check, always), so most people perform security scans in an attempt to remove pop-ups, but to no avail. That's because removal requires blocking the particular URL address within browser settings as so:
Google Chrome (desktop)
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Google Chrome (Android)
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).
![Stop notifications on Chrome Android Stop notifications on Chrome Android]()
Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.
![Stop notifications on Edge Chromium Stop notifications on Edge Chromium]()
Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
![Stop notifications on Internet Explorer Stop notifications on Internet Explorer]()
- Locate the web address in question under Allowed sites and pick Remove.
How to prevent from getting adware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Phishing attacks. Imperva. Application and data security.
- ^ Application Programming Interface (API). IBM. Cloud Learn Hub.
- ^ Ransomware. Imperva. Application and data protection.






