Norton Security Update Is Available Now scam (fake) - Free Guide
Norton Security Update Is Available Now scam Removal Guide
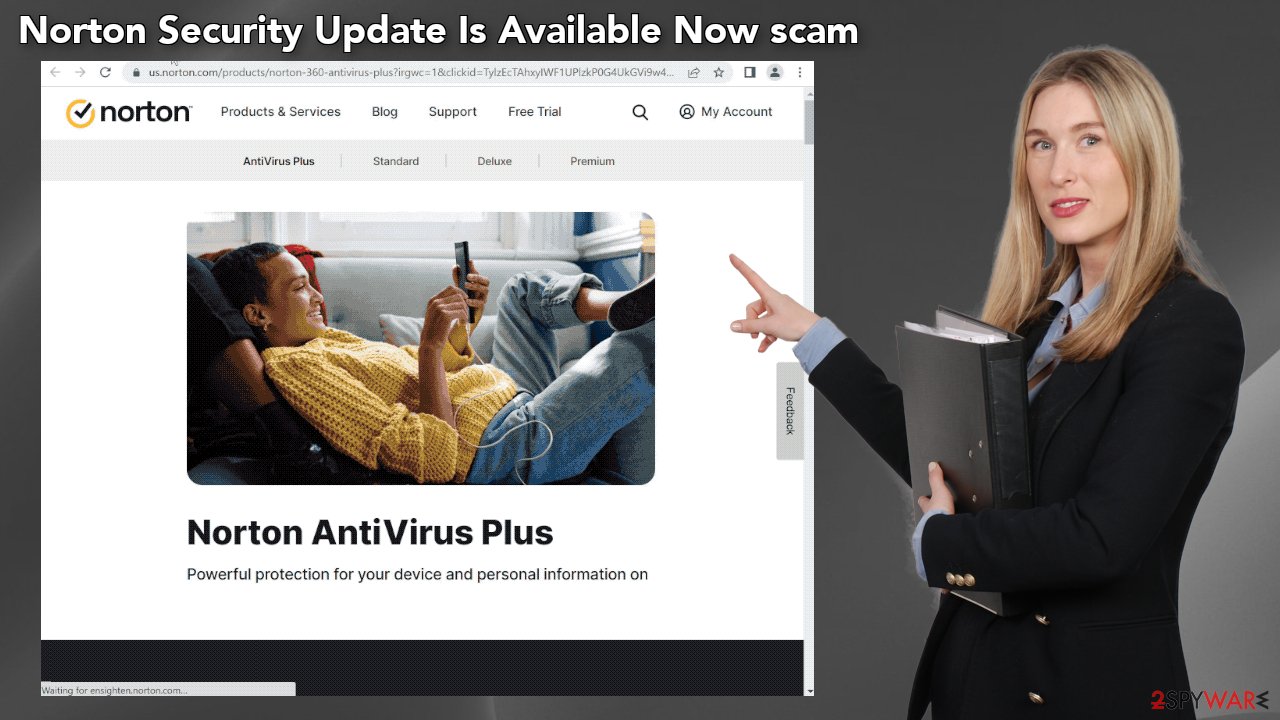
What is Norton Security Update Is Available Now scam?
Norton Security Update Is Available Now is a scam that tries to trick people into thinking their system is in danger

“Norton Security Update Is Available Now” is a deceptive message shown by crooks to fool users into providing personal information, downloading PUPs (potentially unwanted programs),[1] and even malware. It uses the name of a well-known security suite to appear legitimate. The full message reads as follows:
Norton Security 2022 Subscription Update
New update for your Norton 360 Total Protection is available on April 8, 2022.
Update now to protect your computer and prevent it from being susceptible to virus threats.
If your PC is unprotected, it can be exposed to viruses and other malware attacks.
Fraudsters use scare tactics to make people click the “Renew Subscription” button. The website also pretends to scan the system by showing a fake animation. It then “determines” that the computer is infected by multiple viruses and is in danger. You should keep in mind that websites are unable to perform any scan of your machine.
The bogus website then proceeds to redirect users to what seems like an official page of Norton security. That means that crooks might be getting a cut from every customer who clicks on their link and purchases a subscription. Using affiliate marketing in such a fraudulent campaign is certainly inappropriate and it is clear that Norton has nothing to do with it.
| NAME | Norton Security Update Is Available Now |
| TYPE | Phishing scam; adware |
| SYMPTOMS | Fake pop-up errors, security alerts, antivirus scans appear seemingly out of nowhere |
| DISTRIBUTION | Shady websites; deceptive ads, freeware installations |
| DANGERS | Fake system scans can trick people into downloading potentially unwanted programs or even malware |
| ELIMINATION | Check your browser for malicious extensions; performing a scan with legitimate security tools is recommended |
| FURTHER STEPS | Use FortectIntego to optimize your machine and get rid of any remaining damage |
Distribution methods
Online scams are rarely found through search results. Most of the time, users stumble upon them, while browsing through other shady websites. Pages that engage in illegal activities are especially dangerous since they are unregulated. Such pages are full of deceptive ads and sneaky redirects.
You should avoid clicking on random links and buttons. Think twice before clicking on the big “Download” and “Play” buttons. Make sure they are safe first. However, sometimes such sites can appear without any user input. This can happen if your browser is hijacked or you have an adware infection.
We recommend using only official web stores whenever you want to install browser extensions. Apps that get listed there go through an extensive review process. But you still do your research – read the reviews, look at the ratings, and the number of users. It is best to choose those applications that have plenty of positive feedback, and thousands of users.
Clean your browsers
Cookies[2] are small pieces of data that are used to include all sorts of settings. While they can't be malicious by themselves, they can be stolen by third parties and used for malicious purposes. Therefore, security experts advise cleaning web browsers from time to time.
Cookies can store data like your IP address, geolocation, websites you visit, links you click on, and things you purchase online. Use a maintenance tool like FortectIntego to take care of this issue automatically. Besides, this powerful software can fix various system errors, corrupted files, and registry errors, which is especially helpful after a virus infection.
Remove possible browser hijackers
The Norton Security Update Is Available Now scam might have appeared because your browser is hijacked. You can learn more about how browser hijackers operate from the articles we wrote about the most recently detected ones, like Gateway-search.net, MySearchConverters, MySearchConverters. We recommend going to your browser settings and removing all the installed extensions one by one to see if you notice any changes:
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.
![Remove extensions from Edge Remove extensions from Edge]()
MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.
![Remove extensions from Firefox Remove extensions from Firefox]()
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
The dangers of PUPs
One thing that we did not mention previously is that your machine could be infected by adware which is causing this erratic behavior. It is a type of PUP (potentially unwanted program) that can generate commercial content on your device. This can be done without any user input.
Adware is most often spread through freeware distribution platforms. They include additional programs in the installers[3] without clearly disclosing it. Usually, people just skip through the installation process to be able to test the new software as soon as possible and this is the biggest mistake.
To avoid PUPs from sneaking into your system, you should apply certain security measures. Always choose the “Custom” or “Advanced” installation methods, read the Privacy Policy and Terms of Use. The most crucial part is to inspect the file list and uncheck the boxes next to any items that seem suspicious or unrelated.
Another thing you should note is the danger of peer-to-peer file-sharing platforms, and torrent websites. They are breeding grounds for all kinds of malware because they are unregulated. The best you can do is get your software from official developer websites. Even though it might get costly, you will most likely save in the long run by keeping your system safe and healthy.
Scan the system for adware
To ensure that your system is free from intruders that could be causing Microsoft tech support scams to appear we recommend scanning your system with security software. SpyHunter 5Combo Cleaner and Malwarebytes are great options because they are proven and trusted anti-malware tools. They can detect most threats hiding in your machine, and eliminate them completely.
Manual removal can sometimes result in the renewal of infection as users fail to eliminate all the related files that are hidden in various folders. However, if you still want to do this yourself, you can proceed with the guide below:
Windows 10/8:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
Windows 7/XP:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.
![Uninstall from Windows 7/XP Uninstall from Windows 7/XP]()
- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Mac:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)
![Uninstall from Mac 1 Uninstall from Mac 1]()
To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
![Uninstall from Mac 2 Uninstall from Mac 2]()
How to prevent from getting adware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Potentially unwanted program. Wikipedia. The Free Encyclopedia.
- ^ Chris Maus. What Are Cookies and Are They Dangerous?. Qkey. Secure Online Payment Provider.
- ^ Will Dormann. Bundled Software and Attack Surface. Cmu. Carnegie Mellon University Software Engineering Institute Blog.










