Nzqw ransomware (virus) - Recovery Instructions Included
Nzqw virus Removal Guide
What is Nzqw ransomware?
Nzqw ransomware is a dangerous virus that encrypts users' personal files
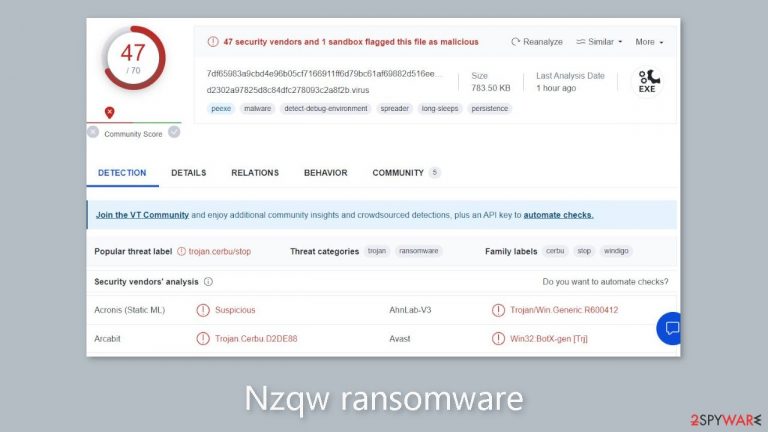
The Nzqw ransomware is a harmful program that is a member of the Djvu ransomware family. It is well known for its ability to encrypt common files located on infected computers and prohibit user access. Since it may spread through several types of malware, including trojans and information stealers, this virus is particularly difficult to discover.
Usually, when a user downloads a damaged file or opens a file attachment from an email, the device is compromised. Once the Nzqw file virus has access to a device, it can cause serious damage. It may conceal its presence by using extra pop-up components to make it appear as though the user's data is simply locked and given the .nzqw extension.
In reality, the virus encrypts the files using strong encryption techniques. The virus's authors then transmit a ransom note, demanding money in exchange for a purportedly accessible decryption tool. The likelihood of their delivering on this promise is slim, though, as they frequently disappear before giving the victim a useful tool.
| NAME | Nzqw |
| TYPE | Cryptovirus, file-locker |
| MALWARE FAMILY | Djvu ransomware |
| FILE EXTENSION | .nzqw |
| RANSOM NOTE | _readme.txt |
| RANSOM AMOUNT | $490/$980 |
| CONTACT MAILS | support@freshmail.top, datarestorehelp@airmail.cc |
| DISTRIBUTION | Malicious files can be shared via email, as well as through various online platforms that may present security risks or engage in pirating activities |
| REMOVAL | Use specialized tools that are designed to remove threats and protect against security breaches |
| SYSTEM FIX | If the infection has caused damage to parts of your machine, you can use FortectIntego to repair any issues with the system that have been caused by the corruption. |
How does ransomware spread?
Nzqw is one of the versions of the Djvu ransomware group, which is known for using a variety of malware types to spread its payload. This tactic includes sending malicious file attachments or distributing bundles of pirated software. Utilizing malware like Vidar and RedLine, the Nzqw file virus can covertly introduce its payload onto a system and start the encryption process.
Nzqw ransomware can be downloaded accidentally from torrent websites or unknowingly opened in emails that contain malicious file attachments. In order to protect yourself from potential infections, it is important to verify and carefully evaluate these files prior to downloading.
Djvu ransomware family
The Nzqw version of the Djvu ransomware family, which is extremely prevalent and has the ability to constantly improve its encryption abilities, has acquired notoriety. The most recent versions use stronger encryption methods coupled with a weekly release schedule. The virus also employs unique online IDs for each affected device, departing from earlier iterations that used standard offline keys for all devices encrypted by a specific variant. Even though the Djvu virus no longer frequently uses offline keys, attempting to decrypt these files is still a viable alternative.
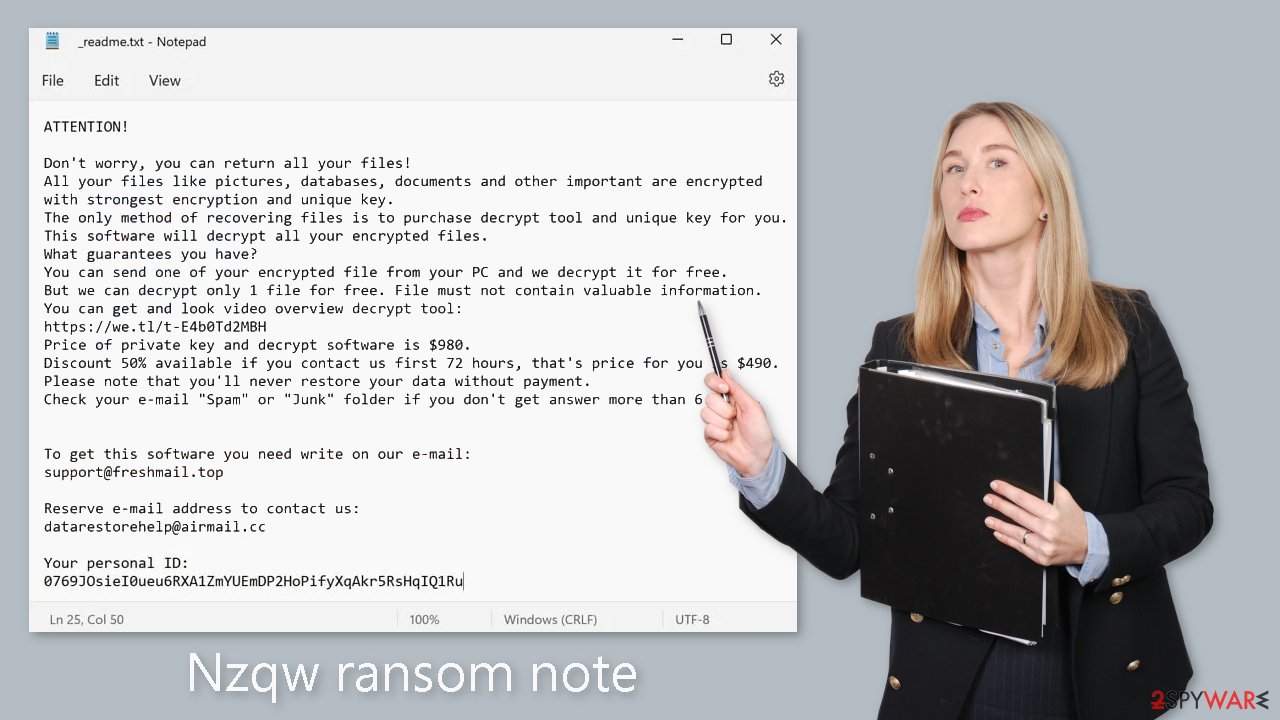
The ransom note
Nzqw ransomware drops the following _readme.txt ransom note on victims' machines:
ATTENTION!
Don't worry, you can return all your files!
All your files like pictures, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
hxxps://we.tl/t-rmxjMZAZBJ
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that's price for you is $490.
Please note that you'll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don't get answer more than 6 hours.To get this software you need write on our e-mail:
support@freshmail.topReserve e-mail address to contact us:
datarestorehelp@airmail.ccYour personal ID:
–
How can Nzqw ransomware be removed?
The Nzqw ransomware poses as a powerful and persistent threat with dangerous capabilities that have the potential to cause major harm. It becomes crucial to remove this infection in order to get your gadget working again. One effective strategy entails doing a thorough system scan using a threat detection tool like SpyHunter 5Combo Cleaner or Malwarebytes. These programs are skilled in locating dangerous files on your system, including covert Nzqw malware or other related threat components.
Through the system scan, the Nzqw file infection can be located and categorized as potentially destructive malware, at which point it can be eliminated. It's crucial to realize, though, that getting rid of the virus doesn't mean you can also decrypt it or retrieve your data after the infection. Since the virus might persist on your system and potentially encrypt fresh files it comes across or even re-encrypt previously decrypted files, causing irreparable damage, the initial focus must be on malware removal. Rapid virus removal is essential because it stops the virus from causing additional interruptions and system damage.
Decrypt .nzqw files
Consider using the Emsisoft decryptor to try and recover your data if your machine has been infected with a Djvu ransomware variant. It's crucial to recognize that this tool's effectiveness isn't general; it only applies in situations when the data was encrypted using an offline ID, indicating that the malware was unable to connect to its remote servers.
Even if your situation fits this description, the remedy calls for one of the affected parties to act as a go-between to satisfy the demands of the attackers, obtain the offline key, and then communicate it to Emsisoft's security specialists. Consequently, it might not be possible to immediately restore your encrypted files. If the decryptor confirms that your data was locked with an offline ID but is currently still unrecoverable, it is suggested to think about trying again later. A pair of files must be uploaded to the company's servers, one encrypted and the other in its original form, in order to use the decryptor.
- Download the app from the official Emsisoft website.

- After pressing Download button, a small pop-up at the bottom, titled decrypt_STOPDjvu.exe should show up – click it.

- If User Account Control (UAC) message shows up, press Yes.
- Agree to License Terms by pressing Yes.

- After Disclaimer shows up, press OK.
- The tool should automatically populate the affected folders, although you can also do it by pressing Add folder at the bottom.

- Press Decrypt.

From here, there are three available outcomes:
- “Decrypted!” will be shown under files that were decrypted successfully – they are now usable again.
- “Error: Unable to decrypt file with ID:” means that the keys for this version of the virus have not yet been retrieved, so you should try later.
- “This ID appears to be an online ID, decryption is impossible” – you are unable to decrypt files with this tool.
System file recovery
Malware has the power to cause a variety of changes in a computer's operation, including removing or corrupting DLL files, altering the Windows registry database, affecting crucial boot-up and other processes, and more. Antivirus software's effectiveness may not be enough to fix a system file that malware has adversely affected. A compromised system state may arise from this circumstance, which may cause performance issues, instability, and usability problems that may call for a full reinstallation of the Windows operating system.
We suggest the application of FortectIntego, a distinctive and patented repair method, to address these challenges. Additionally, this tool shows proficiency in handling a variety of Windows-related problems that are not caused by malware infections. These problems range from registry issues and system freezes to broken DLLs and Blue Screen errors.
Getting rid of Nzqw virus. Follow these steps
Important steps to take before you begin malware removal
File encryption is one component of a ransomware infection, which may also include credential theft, persistence mechanisms, and lateral movement. However, it is important to understand that malware may perform various changes within a Windows operating system, including persistence, scheduled tasks, registry modifications, and security feature tampering.
IMPORTANT for those without backups! →
If you attempt to use security or recovery software immediately, you might permanently damage your files, and even a working decryptor then would not be able to save them.
Before you proceed with the removal instructions below, you should copy the encrypted files onto a separate medium, such as USB flash drive or SSD, and then disconnect them from your computer. The storage device should remain disconnected after copying to prevent accidental modification or deletion. Encrypted data itself does not contain active malicious code, but only the encrypted files—not executables or scripts—should be transferred.
The instructions below might initially seem overwhelming and complicated, but they are not difficult to understand as long as you follow each step in the appropriate order. This comprehensive free guide will help you to handle the malware removal and data recovery process correctly.
If you have any questions, comments, or are having troubles with following the instructions, please do not hesitate to contact us via the Ask Us section.
IMPORTANT! →
It is vital to eliminate malware infection from the computer fully before starting the data recovery process, otherwise ransomware might re-encrypt retrieved files from backups repeatedly.
Restore Windows "hosts" file to its original state
Some ransomware might modify Windows hosts file in order to prevent users from accessing certain websites online. For example, Djvu ransomware variants add dozens of entries containing URLs of security-related websites, such as 2-spyware.com. Each of the entries means that users will not be able to access the listed web addresses and will receive an error instead.
Here's an example of “hosts” file entries that were injected by ransomware:
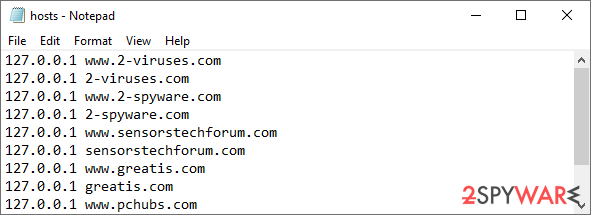
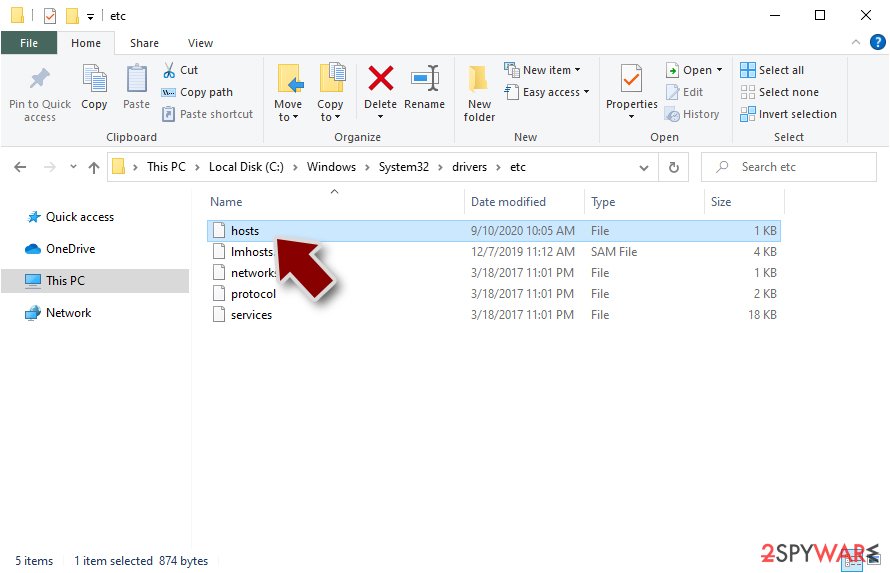
In order to restore your ability to access all websites without restrictions, you should either delete the file (Windows will automatically recreate it) or remove all the malware-created entries. If you have never touched the “hosts” file before, you should simply delete it by marking it and pressing Shift + Del on your keyboard. For that, navigate to the following location:
C:\\Windows\\System32\\drivers\\etc\\
Restore files using data recovery software
Since many users do not prepare proper data backups prior to being attacked by ransomware, they might often lose access to their files permanently. Paying criminals is also very risky, as they might not fulfill the promises and never send back the required decryption tool.
While this might sound terrible, not all is lost – data recovery software might be able to help you in some situations (it highly depends on the encryption algorithm used, whether ransomware managed to complete the programmed tasks, etc.). Since there are thousands of different ransomware strains, it is immediately impossible to tell whether third-party software will work for you.
Therefore, we suggest trying regardless of which ransomware attacked your computer. Before you begin, several pointers are important while dealing with this situation:
- Since the encrypted data on your computer might permanently be damaged by security or data recovery software, you should first make backups of it – use a USB flash drive or another storage.
- Only attempt to recover your files using this method after you perform a scan with anti-malware software.
Install data recovery software
- Download Data Recovery Pro.
- Double-click the installer to launch it.

- Follow on-screen instructions to install the software.

- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders where you want the files to be recovered from.

- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.

- Press Scan and wait till it is complete.

- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.

Report the incident to your local authorities
Ransomware is a lucrative, highly illegal business, and authorities are actively targeting ransomware operators. The level of investigation and follow-up depends on the country, the scale of the incident, and whether the attack is linked to known ransomware groups. To increase the likelihood of identifying the culprits, the agencies need information. In many cases, reports are used primarily for intelligence gathering, trend analysis, and victim support rather than immediate identification of attackers.
Therefore, by reporting the crime, you could help stop the cybercriminal activities and catch the threat actors. Reporting does not guarantee investigation or recovery of data, but it contributes to broader efforts to track ransomware campaigns. Make sure you include all the possible details, including how did you notice the attack, when it happened, etc. Relevant details may also include affected systems, ransom demands, cryptocurrency wallet addresses, and any communication with the attackers. Additionally, providing documents such as ransom notes, encrypted files, or malware executables would be beneficial.
Law enforcement agencies typically deal with online fraud and cybercrime, although it depends on where you live. Here is the list of local authority groups that handle incidents like ransomware attacks, sorted by country:
- USA – Internet Crime Complaint Center IC3
- United Kingdom – ActionFraud
- Canada – Canadian Anti-Fraud Centre
- Australia – ScamWatch
- New Zealand – ConsumerProtection
- Germany – Polizei
- France – Ministère de l'Intérieur

If your country is not listed above, you should contact the local police department or communications center.
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
