Ordinypt ransomware / virus (Simple Removal Guide) - updated Nov 2019
Ordinypt virus Removal Guide
What is Ordinypt ransomware virus?
Ordinypt ransomware is a wiper malware that targets German users with spam email campaigns
Ordinypt ransomware is a relatively old computer infection that was first spotted back in 2017. Also known as HSDFSDCrypt and Wo Sind Meine Dateien ransomware, this virus does not not encrypt victims personal pictures, videos, music and other data, but rather replaces their names with random 14 lower and upper case characters, which permanently and irreversibly damages them. Nevertheless, cybercriminals behind Ordinypt ransomware still claim that they use AES encryption algorithm to lock data and ask to pay 0.12 Bitcoin[1] for the decryption software which most likely does not exist.
Ordinypt virus is known to be targeting German users, as it drops a ransom note Wo_sind_meine_Dateien.html, which is written in German. The malicious executables were also delivered with the help of malicious spam emails that pretend to come from job applicants, with fake .pdf files attached to them. The most recent campaign started mid-September 2019 – it targets German users with malicious attachments by “Eva Richter,” another fake job resume crafted by cybercriminals behind Ordinypt wiper. This time, hackers are trying to imitate appropriate encryption process by appending a random extension at the end of each file, for example, .NrrcR.
| Name | Ordinypt ransomware |
| Also known as | HSDFSDCrypt, Wo Sind Meine Dateien |
| Type | Wiper – all personal files are permanently corrupted |
| File extension | This ransomware does not encrypt any files on the device (despite cybercriminals claiming that the malware does precisely that using AES cipher) but rather turns their names into gibberish combinations of random 14 characters. In the newest campaign, cyberattackers are trying to imitate the behavior of ransomware by appending a random extension of 5 characters, although the malware is still programmed to destroy data instead |
| Ransom size | Malicious actors ask for 0.12 BTC for alleged decryption software. In the latest campaigns, crooks ask for 0.1473766 BTC |
| Ransom note | Initial infections used Wo_sind_meine_Dateien.html, later versions rely on [extension]_how_to_decrypt.txt ransom note |
| File decryption | Paying cybercriminals is useless, as the data gets permanently corrupted by the malware. You might have a chance by using third-party recovery tools, however |
| Malware removal | Choose reputable security software and perform a full system scan to get rid of the wiper |
| Recovery | To remediate your system and fix damage done by Ordinypt ransomware, scan it with FortectIntego |
Once inside the system, malware claims that it encrypted valuable user's information and demands 0.12 Bitcoin[1] as a ransom for the decryption tool. Instructions on how to recover corrupted files are delivered in Wo_sind_meine_Dateien.html ransom note and written in fluent German language.
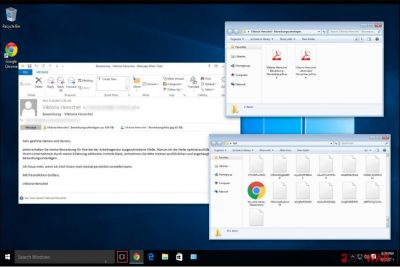
On the first time when Ordinypt was spotted spreading on the Internet, it used a fake job resume e-mail supposedly sent by Viktoria Henschel. It contains two infected attachments — Viktoria Henschel-Bewerbungsunterlagen.zip and Viktoria Henschel-Bewerbungsfoto.jpg.
One of them is a simple photo used to trick people into thinking that it is a legitimate e-mail, while another .zip file holds two executable files of the malware. Besides, hackers appended two file extensions to deceive victims that both of the .exe files are supposedly .pdf documents.
Unfortunately, Ordinypt ransomware acts more like a wiper than a real crypto virus. After being tested by NoVirus.uk[2] cybersecurity experts found that it doesn’t encrypt files. Instead, the virus replaces them with random data and deletes original copies of the documents. Shortly after, it generates the so-called encrypted file’s name from random characters and drops a random note.
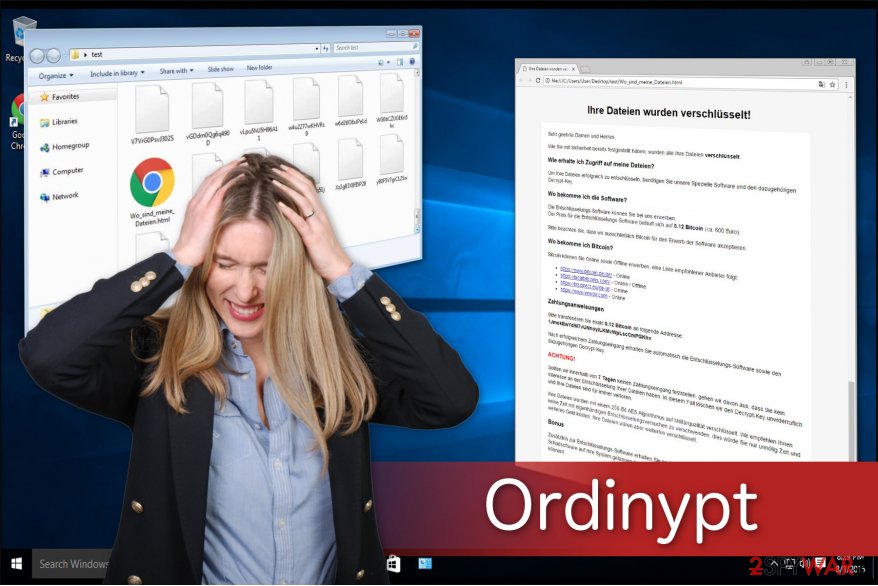
We want to inform you that there is no possible decryptor for Ordinypt virus. Thus, you shouldn’t pay the ransom since criminals only try to swindle money from their victims. Also, you can find alternative expensive decryption tools offered online, but they won’t help you to recover your files either.
Data wiper[3] is a dangerous malware, and eliminating it from your PC is the best decision. You can remove Ordinypt using powerful antivirus software. Once the malware is terminated, you should also take care of Windows system restoration with tools like FortectIntego. Finally, do not pay the attackers as malware is a wiper, and even they would not be able to recover your files. Instead, check the alternative methods we provide below.
Eva Richter spam email campaign
The newest campaign of Ordinypt uses very similar tricks for propagation as before – the malicious actors write a fake email that pretends to be a letter from a job applicant Eva Richter who is seeking employment in the firm chosen by the malicious actors. The subject line of the email reads “Bewerbung via Arbeitsagentur – Eva Richter,” followed by the subsequent body text (translated from German):
Dear Sir or Madam,
I hereby apply for the position offered by you at the Employment Agency.
The field of activity you describe corresponds especially to my career prospects. My application documents are attached.
I would be very happy about an invitation to a personal job interview.
With best regards,
Eva Richter
Attached to the email are two files:
- Eva Richter Bewerbungsfoto.jpg
- Eva Richter Bewerbung und Lebenslauf.zip
Once the .zip file is extracted, users can see Eva Richter Bewerbung und Lebenslauf.pdf.exe file, which pretends to be a resume. More vigilant users should instantly notice that it is, in fact, an executable and not a PDF file. Once it is opened, the malware will begin its data wiping process, which will completely destroy it.
Upon running the process, this variant of Ordinypt ransomware will append a random extension to each of the files located on the system – this action tries to imitate a typical data locking process by crypto-malware. Additionally, the malware will also attempt to destroy Shadow Volume Copies, although it is known that this process sometimes fails.
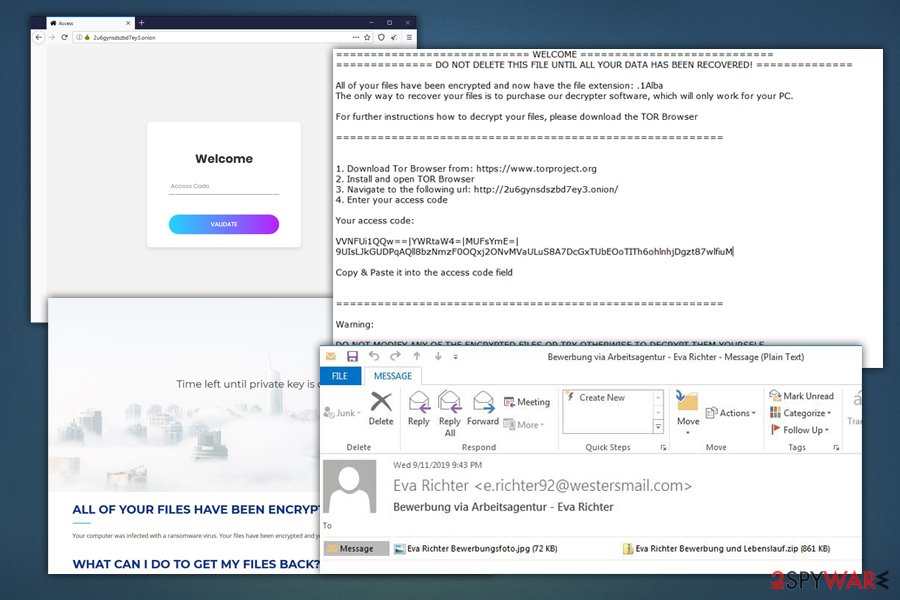
Therefore, paying criminals is not only risky but will not result in any data recovery. Because Ordinypt wiper sometimes fails to delete Shadow Copies,[4] there is a chance to restore data by using recovery software. For more information, please check the bottom section of this article.
Cybercriminals send bogus job resumes to distribute the malware
As mentioned above, the ransomware spreads via infected attachments in e-mails sent by Viktoria Henschel. It is clear that developers tried their best to make the letter look as genuine as possible. As a result, many innocent computer users opened the executable files of theWo Sind Meine Dateien virus damaged their systems permanently.
To avoid the ransomware attack, you should follow the prevention steps:
- Never open unreliable e-mail letters or attachments and pictures it contains. Instead, delete them right away and block the contact who has sent it to you;
- Always have in mind that criminals are able to hack into social media accounts and distribute malicious links. If you ever receive a suspicious message asking to click on the provided link, close the text and stay away from that user;
- Also, your friend’s account might be hijacked as well. Thus in case of any questionable messages, contact your friend in person.
However, attackers never stick to one distribution method. There are numerous cases when criminals took advantage of irresponsible computer users surfing the Internet. Therefore, we encourage you to be careful and avoid visiting unauthorized websites or clicking on sponsored ads.
The easiest way to get rid of the Ordinypt data wiper
For those who opt for a quick Ordinypt removal, we suggest an automatic elimination method by employing a security software of their choice.
In order to download it, you should reboot your computer to Safe Mode since the malware is able to block it. Afterward, run a full system scan and let it remove Ordinypt virus.
Another way to get rid of the wiper is to remove it manually. To prevent you from doing even more harm to your computer, we have prepared instructions that will help you. Make sure to follow them strictly in order not to uninstall necessary operating system files.
Getting rid of Ordinypt virus. Follow these steps
Manual removal using Safe Mode
You have to reboot your computer to Safe Mode with Networking if you want to get rid of Ordinypt ransomware. Get help from the instructions provided below:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Ordinypt using System Restore
Ordinypt might not permit to install a security software. This guide will teach you how to boot your computer to Safe Mode with the Command Prompt function:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Ordinypt. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Ordinypt from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.As mentioned above, the virus does not perform data encryption. It intentionally deletes valuable information to damage your computer. Our IT experts suggest trying to recover the removed files with a useful recovery tool that might help.
If your files are encrypted by Ordinypt, you can use several methods to restore them:
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Ordinypt and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Satoshi Nakamoto. Bitcoin. A Peer-to-Peer Electronic Cash System. Bitcoin. Open Source P2P Money.
- ^ NoVirus. NoVirus. Security and Spyware News.
- ^ Wiper. Malware. Wikipedia. The Free Encyclopedia.
- ^ Shadow Copy. Wikipedia. The free encyclopedia.





















