Point Dark browser extension (Free Guide) - Chrome, Firefox, IE, Edge
Point Dark browser extension Removal Guide
What is Point Dark browser extension?
Point Dark is yet another useless browser add-on that inserts ads into your searches

Point Dark is advertised as an extension that can provide a dark mode for all visited pages. While it may seem like your average app for Google Chrome or other compatible browsers, there have been reports about bad experiences from users. This is not surprising, as it is considered to be a browser hijacker – a type of potentially unwanted application that takes over the web browser to show intrusive ads and record data.
In order to do that, soon after the infiltration, the Point Dark browser hijacker changes the settings of the browser, namely, it starts promoting a suspicious search engine known as ytood.com, which the searches are redirected through. People are also often rerouted to an alternative search provider (e.g., websearches.club, although this can vary depending on your location and other factors).
The changes are not only visual, however, as users would soon notice that the alternative search results are nothing like they used to – top ones are usually filled with plenty of sponsored links and ads. These links are not organic and are simply placed there to generate ad revenue from users' clicks. There is never a guarantee that these results are accurate or even safe. Thus, we recommend refraining from clicking the ad links, as you may end up installing other potentially unwanted programs, losing money to useless services, or handing in your personal data to unknown parties.
Distribution and avoidance
While the Point Dark extension can be downloaded from the official Chrome Web Store, it is not the main distribution method used to spread it. PUP developers are well aware that most users don't pay close attention when installing freeware[1] from third-party websites, hence they use a few tricks to ensure that at least some would install the app regardless of whether they want it or not – this technique is commonly referred to as software bundling.[2]
Bundled software is a concept that originated a long time ago when Microsoft started offering additional apps with the operating system as one package.[3] Users were free to accept or decline it, and many opted to make use of the offer, as it did make a lot of sense financially.
However, this practice became quite a bit twisted over time when various third-party distributors began using deceptive methods to make users install apps they otherwise wouldn't. A good example of such is pre-ticked checkboxes which, if not unticked by the user, would result in an automatic installation of optional apps.
Thus, you should always pay close attention to the installation process of new apps, especially if you download them from freeware websites, as all of them bundle software to an extent. Always read the fine print, remove ticks from pre-ticked checkboxes, and, most importantly, always opt for the Advanced installation method to stay in control of what is being installed on the system. Recommended settings often automatically provide permission to install optional components.
| Name | Point Dark |
|---|---|
| Type | Browser hijacker, potentially unwanted application |
| Distribution | Software bundle packages, deceptive ads, fake update prompts |
| Symptoms | Unknown extension or application is installed on the system; search queries are redirected through rogue providers; search results are filled with sponsored links and ads |
| Dangers | Installation of other potentially unwanted programs or even malware, privacy risks due to information gathering practices, monetary losses |
| Removal | To remove the unwanted browser extension, you should access the settings section of your browser. You should also check for other PUPs or malware with an SpyHunter 5Combo Cleaner anti-malware |
| Other tips | After you uninstall all browser hijackers and other PUPs from your device, make sure you clean your web browsers and repair system files. The easiest way to do so is by employing FortectIntego PC repair tool |
Point Dark removal steps
Browser hijackers are not considered high-risk infections, in most cases at least. It is true that none of them would ever come close to the severity of ransomware, Trojans, or rootkits and similar threats, but it does not mean that their presence should be ignored. Not only do they distort the way users browse the web by exposing users to plenty of commercial content, but they sometimes might also put users' security and privacy at risk, as the ads might sometimes be dangerous.
Therefore, it is strongly recommended you remove a browser hijacker from your system and check for other potentially unwanted apps on the way. Likewise, there could be malicious programs running in the background without giving out any symptoms, all while performing malicious deeds in the background.
Before you proceed, please check your system with SpyHunter 5Combo Cleaner, Malwarebytes, or another security software that would check it properly and remove anything suspicious and malicious automatically.
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.
![Remove extensions from Firefox Remove extensions from Firefox]()
MS Edge
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
MS Edge (legacy)
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.
![Remove extensions from Edge Remove extensions from Edge]()
Internet Explorer
- Open Internet Explorer, click on the Gear icon (IE menu) on the top-right corner of the browser
- Pick Manage Add-ons.
- You will see a Manage Add-ons window. Here, look for suspicious plugins. Click on these entries and select Disable.
![Remove add-ons from Internet Explorer Remove add-ons from Internet Explorer]()
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
After you are done with the extension removal, we strongly recommend you perform a full system scan with powerful anti-malware software to ensure
Clean your browser
The main goal of a browser hijacker is not to provide users adequate functions in exchange for ad revenue; most PUP authors do not really care about the usefulness of their applications – some of them even promote fake features that do not actually exist, for example, “enhanced search results” are nothing more but promotional links at the top. In other words, the generation of revenue through ads becomes the centric goal of the developers.
In order to ensure that the constant flow of ads accompanies users and they actually click them, potentially unwanted applications commonly collect a variety of user data related to their web browsing activities. This guarantees that users receive ads that are more related to their interests, making them more likely to click them.
For that, third parties use various tracking technologies, including cookies, web beacons, and other elements. These are typically stored locally on users' devices. Even if you delete all the potentially unwanted apps, their trackers might remain on your device, thus it is advised to remove them. You can either do it manually as explained below or employ a powerful maintenance and repair utility FortectIntego.
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content, and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
MS Edge (legacy)
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.
![Clear Edge browsing data Clear Edge browsing data]()
Internet Explorer
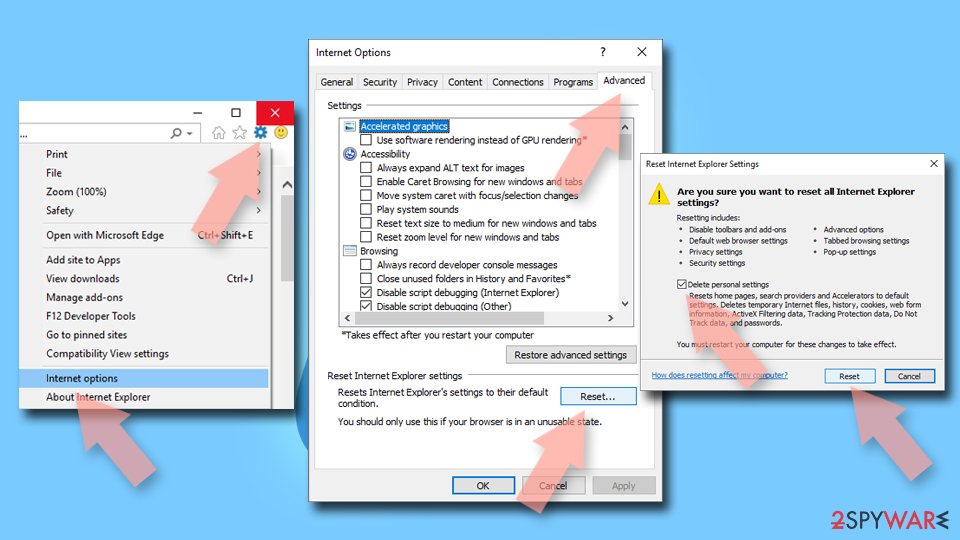
- Click on Gear icon > Internet options and select Advanced tab.
- Select Reset.
- In the new window, check Delete personal settings and select Reset.
![Reset Internet Explorer Reset Internet Explorer]()
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
Please remember to take precautionary measures when browsing the web online or installing new programs.
How to prevent from getting browser hijacker
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Tim Fisher. What Is Freeware?. Lifewire. Tech News, Reviews, Help & How-Tos.
- ^ Bundled Software. Techopedia. Professional IT insight.
- ^ Richard Yao. The Coming Wave of Bundling. Medium. Publishing platform.