Qxsearch.com (Easy Removal Guide) - Free Instructions
Qxsearch.com Removal Guide
What is Qxsearch.com?
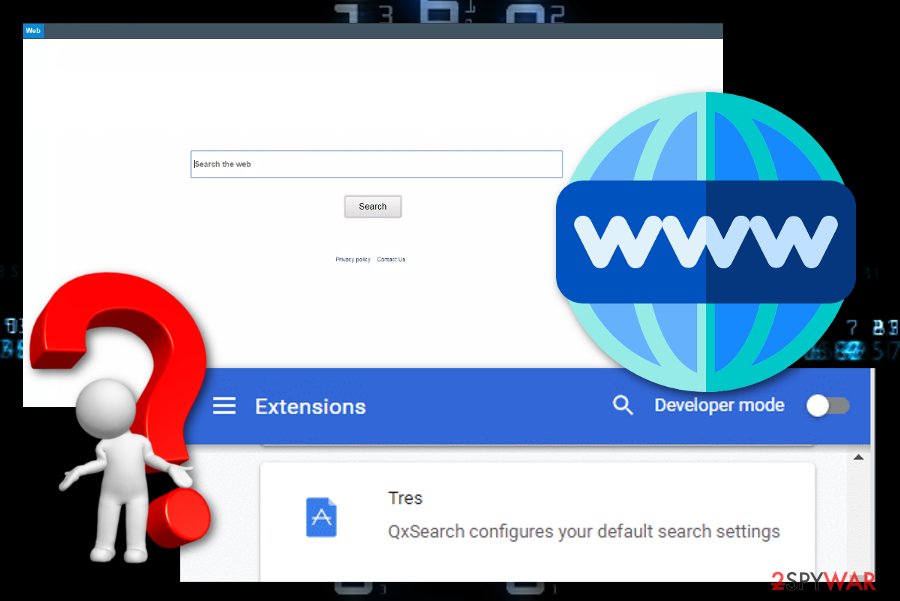
Qxsearch.com – a browser hijacker that spreads fake claims about an unsuccessful installing

Qxsearch.com, that is related to the SearchPrivacyPlus family, is a browser hijacker that asks to retry the installation process even though it was already finished. Different extensions related to Qxsearch.com virus can be discovered on the Google Chrome web store and directly downloaded to the browser. Once this happens, the PUP provides a message claiming that the extension needs to be installed again even though it is already there.[1] The goal of this suspicious activity remains currently unknown. However, cybersecurity researchers have spotted that Qxsearch.com extension modifies the browser's settings such as the default search engine, homepage, new tab URL and might relate to redirecting to affiliate sources.
| Name | Qxsearch.com |
|---|---|
| Alternative name | PUP.Optional.QxSearch |
| Type | Browser hijacker |
| Related to | SearchPrivacyPlus |
| Found on | Google Chrome web store |
| Browsers | This PUP appears mostly on Google Chrome but other browsers such as Firefox, Explorer, Edge, Safari can also be affected by the browser hijacker |
| Distribution | Besides being promoted on the Internet store, this hijacker is very likely to be met after downloading bundled software or visiting secondary networks |
| Removal | First, scan the entire system with FortectIntego. Afterward, remove the threat with the help of automatical software or manual instruction guidelines |
Qxsearch.com, also known as PUP.Optional.QxSearch,[2] is a browser hijacker that mostly appears on Windows computer systems and the Google Chrome web browser application. However, this does not mean that users of Mozilla Firefox, Internet Explorer, Microsoft Edge, or other browser apps cannot find this potentially unwanted program and its extensions on their computer.
Be aware that once your browser settings are altered by Qxsearch.com and your search engine refers to https://qxsearch.com/chrome.php?q={searchTerms}, these suspicious modifications can be reversed only if you uninstall the browser-hijacking application from your Windows computer and web browser applications entirely.
Besides these changes, Qxsearch.com might provoke redirects straightly to other affiliate domains. This technique is used to drive you towards some bogus offers and convince to purchase useless products. Nevertheless, redirects might force you to land on a malware-laden page and you might get your computer system infected with a malicious program.
In addition, potentially unwanted programs such as Qxsearch.com always find some ways how to make more money from the user's activity. Some applications display beneficial-looking adverts that promote bogus software. Others claim about false prizes and urge users to enter their personal or even banking information. However, be especially aware of this kind of activity as providing private details to random people might result in data theft.

Other apps similar to Qxsearch.com collect browsing-related information and some technical details about the user's computer system. Later on, the data is used for generating beneficial adverts and providing people with bogus offers. Sometimes, the information is handled to other parties for a bigger piece of income to be received.
Dealing with browser hijackers is not a very pleasant thing even though some of them might offer “handy features” such as fastly accessing popular networks, and so on. Do not fall for such tricks and remove Qxsearch.com from your computer system and web browsers that are filled with questionable extensions, plug-ins, add-ons, etc.
Qxsearch.com removal is a process that can be carried out with the help of antivirus software and scanning the entire computer with a tool such as FortectIntego. Also, manual instructions are available for this situation and you can view some guidelines regarding this method at the bottom of this web page. Those steps are suitable for Windows computer and various infected browsers (Firefox, Chrome, Edge, Explorer, Safari).
Distribution tactics used for promoting browser hijackers
Third-party developers aim to sneak their programs into various sources and software packages. According to specialists from Virusai.lt,[3] “bundling” is the main technique by which browser hijackers and potentially unwanted programs are easily injected into the targeted computer system.
“Bundling” happens when a software package that includes a couple or several programs is delivered together with a bogus product that often refers to a browser-hijacking app, adware, or other potentially unwanted application.[4] If the user has left the Quick or Recommended mode on, there are big chances that the rogue object will successfully reach its destination.
According to this reason, you have to make sure that the safest downloading/installing settings have been chosen. This type of configuration usually refers to Custom or Advanced. Here you will be given the capability of tracking, controlling, and declining any incoming download.
However, odd programs travel not only in bundles but they might appear through unsecured sources also. Avoiding third-party networks such as torrent websites, gambling, or gaming pages is a good option. Also, all of your activities should be followed by the protection of a reputable antimalware tool.
Removal instructions for Qxsearch.com virus
It does mind if you are an experienced user or not, you always have equal chances of uninstalling Qxsearch.com virus if the process is performed by using reputable antimalware software. Besides, these types of programs work much faster than any user might be capable of and can succeed in the elimination process in a few minutes of time.
However, if you have advanced skills and truly do believe in yourself, you can go for the manual Qxsearch.com removal option. Take a look at the end of the article and you will find some guiding instructions on how to clean suspicious content from web browsers such as Google Chrome, Mozilla Firefox, Internet Explorer, Microsoft Edge, and Safari.
One more tip we want to give you is to make sure that you remove Qxsearch.com entirely. What this means is you have to locate all potentially infectious content that the hijacker has brought to your system, browsers and get rid of it. If you do not terminate the PUP completely, there is a big chance that it will return with its activities sooner or later.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Qxsearch.com. Follow these steps
Uninstall from Windows
Windows can be cleaned from the browser hijacker and various potentially suspicious component if you follow the below-provided steps carefully:
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Remove from Microsoft Edge
Delete unwanted extensions from MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Clear cookies and other browser data:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Restore new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Disable if you found any suspicious domain.
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.

If this solution failed to help you, you need to use an advanced Edge reset method. Note that you need to backup your data before proceeding.
- Find the following folder on your computer: C:\\Users\\%username%\\AppData\\Local\\Packages\\Microsoft.MicrosoftEdge_8wekyb3d8bbwe.
- Press Ctrl + A on your keyboard to select all folders.
- Right-click on them and pick Delete

- Now right-click on the Start button and pick Windows PowerShell (Admin).
- When the new window opens, copy and paste the following command, and then press Enter:
Get-AppXPackage -AllUsers -Name Microsoft.MicrosoftEdge | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register “$($_.InstallLocation)\\AppXManifest.xml” -Verbose

Instructions for Chromium-based Edge
Delete extensions from MS Edge (Chromium):
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Clear cache and site data:
- Click on Menu and go to Settings.
- Select Privacy, search and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Reset Chromium-based MS Edge:
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.

Remove from Mozilla Firefox (FF)
Eliminate the PUP from Mozilla Firefox and reverse all questionable-looking modifications on your browser with the help of these guidelines:
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
Clean the Google Chrome web browser application from bogus extensions and add-ons. What you have to do is complete the following instructions:
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Qxsearch.com registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting browser hijacker
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Pieter Arntz. QxSearch hijacker fakes failed installs. Malwarebytes Labs. Technology information.
- ^ PUP.Optional.QxSearch. Malwarebytes Blog. Detections.
- ^ Virusai.lt. Virusai. Security and spyware news source.
- ^ What is a PUA / PUP software?. BitDefender. Support Center.





















