Rechanque.com ads (fake) - Free Guide
Rechanque.com ads Removal Guide
What is Rechanque.com ads?
Rechanque.com ads show links to websites that offer to download potentially malicious software

Rechanque.com is a fake website that might pop up on browsers like Google Chrome, Mozilla Firefox, or MS Edge. Users remember it because it keeps showing annoying pop-up ads on their screens. This happens after users accidentally let the site send push notifications, usually because of tricky messages shown when they first visit.
Rechanque.com is known for showing poor-quality content, mostly because it works with sketchy ad networks and unwanted programs. The notifications from this site might have links to bad websites, promote fake surveys or quick money-making tricks, and wrongly warn that the user's computer has many viruses.
To avoid more problems, we suggest not clicking on the links and avoiding the websites they lead to. To stop the annoying notifications, first, make sure your computer is clean from adware, then change your browser settings following the steps below.
| Name | Rechanque.com |
| Type | Push notifications, ads, pop-ups, scam |
| Distribution | After users click the “Allow” button within the prompt upon site entry |
| Symptoms | Pop-up notifications are shown on a desktop at random times |
| Risks | Notifications sent by the site could potentially lead you to unsafe websites, which may, in turn, cause malware infections, monetary losses, or exposure of your personal information to harmful entities |
| Removal | You can stop the site from sending you notifications by following the steps below. To ensure the safety of your computer, it is advisable to scan it for adware using SpyHunter 5Combo Cleaner security software |
| Tips | After the removal of PUPs and malware, we recommend scanning the system with FortectIntego to clean browser caches and fix virus damage automatically |
Difference between pop-up ads and push notifications
Push notifications and pop-up ads are two different methods used by websites to communicate with users, but they work in different ways and have different implications, especially when they originate from malicious sites like Rechanque.com.
Push notifications are alerts that show up on your device even when you're not browsing the website that sent them. Websites must ask for your permission to send these notifications, but malicious sites like Rechanque.com use deceptive tactics to trick you into granting this permission. Once given, these sites can bombard your device with notifications containing potentially harmful links or misleading information, even if your browser is closed.
On the other hand, pop-up ads are a type of online advertising where the ad appears on your screen over the content you are viewing. Pop-ups don't require any special permissions to appear, and they only show up while you're actively browsing the site that's displaying them. However, they can be just as dangerous as push notifications if they originate from a malicious site, as they can contain harmful links or be designed to trick you into downloading unwanted software.
Removal of infections and unwanted push notifications from Rechanque.com
Identifying the origin of intrusive pop-ups can be challenging, and many users may falsely assume that their systems are infected with a virus. To guarantee maximum protection for your device, we strongly suggest scanning your system with either SpyHunter 5Combo Cleaner or Malwarebytes antivirus software. If the scan reveals the presence of adware, you should cleanse all browsers on your device and repair any potential harm using FortectIntego. Implementing these measures will help defend against future questionable activity.
After confirming that your system is clean and devoid of malware, you can refer to the instructions below to permanently eliminate ads from Rechanque.com or any other suspicious website displaying push notifications. Remember that this guide can be applied to block push notifications from any dubious website.
Google Chrome
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Google Chrome (Android)
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off position).
![Stop notifications on Chrome Android Stop notifications on Chrome Android]()
Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
MS Edge
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.
![Stop notifications on Edge Chromium Stop notifications on Edge Chromium]()
Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
![Stop notifications on Internet Explorer Stop notifications on Internet Explorer]()
- Locate the web address in question under Allowed sites and pick Remove.
Tips to avoid being scammed or infected in the future
Users often unwittingly stumble upon push notification scam websites like Rechanque.com through various means. This usually happens when they are redirected by a questionable link they encountered elsewhere on the internet. Alternatively, they might be led to these sites due to adware or other harmful software already present on their devices. Such software often infiltrates systems unnoticed, bundled with freeware, or through spam email attachments. Once a user lands on these websites, they are presented with crafty manipulation tactics designed to trick them into clicking the “Allow” button in the push notification prompt.
Scammers deploy various deceptive phrases to coax users into enabling these notifications. Some examples include:
- “Click Allow to watch the video”
- “Press 'Allow' bot verify, that you are not robot”
- “Click 'Allow' to win a prize and get it in our shop!”
- “If you are 18+, click Allow”
- “Browser verification in progress – click the button 'Allow' to access”
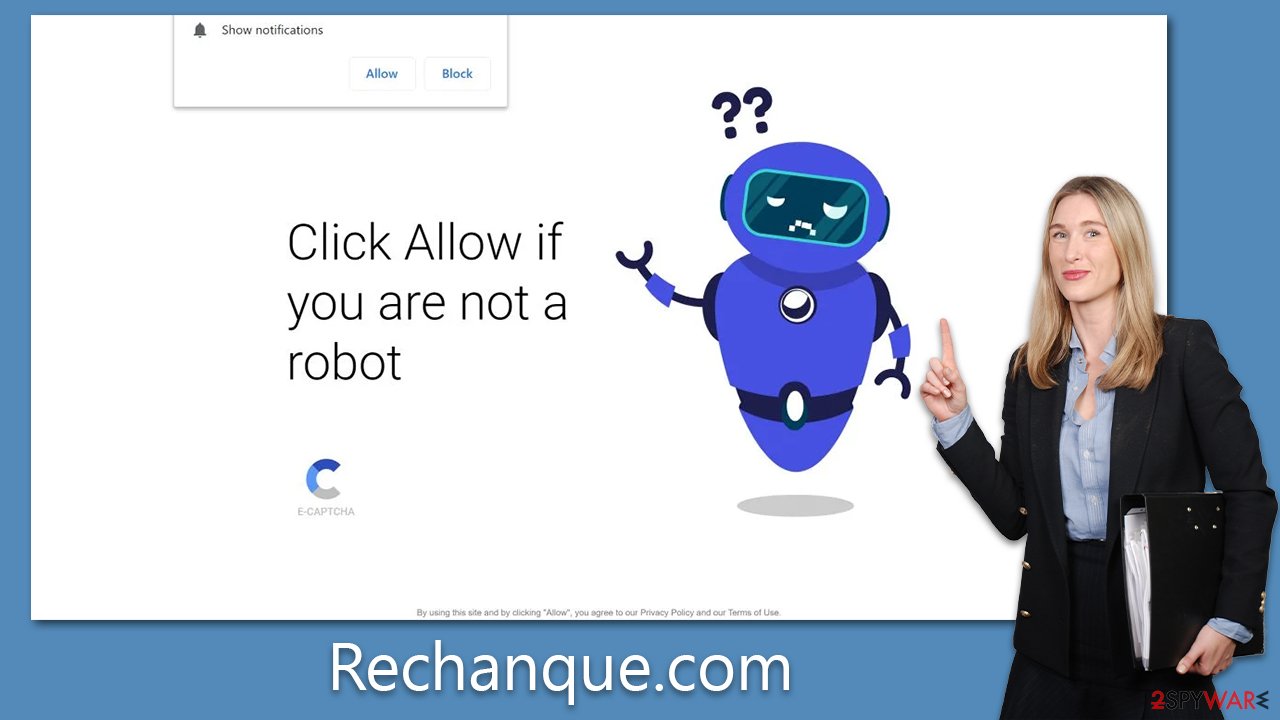
These messages appear legitimate or enticing, causing many users to fall into the trap of approving unwanted push notifications.
To avoid falling victim to such scams, there are several precautions one can take:
- Be cautious of unexpected prompts: Always be wary of websites that request you to enable notifications to access content. Legitimate websites will rarely, if ever, use such tactics.
- Mind the source: Be selective about the websites you visit and the links you click on. If a website seems suspicious or if you were redirected there without your consent, it's best to close it immediately.
- Install a reliable antivirus: Ensure you have reputable antivirus software installed on your device. Regularly scan your device for threats and keep your antivirus updated.
- Regularly update your software: Keeping your operating system and other software updated can help you stay protected from known vulnerabilities that adware and other malware might exploit.
- Avoid freeware: Many free software downloads come bundled with unwanted programs. Always download software from trusted sources and be cautious during the installation process.
By being vigilant and maintaining good digital hygiene, you can significantly reduce your chances of encountering adware and push notification scams.
How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.






