What is Redirector.gvt1.com, should you be worried?
Redirector.gvt1.com Removal Guide
What is Redirector.gvt1.com?
Redirector.gvt1.com – a Google-owned domain that is commonly used to deliver Chrome updates

Redirector.gvt1.com is a redirection service employed by Google for the delivery of updates and other upcoming features.[1] However, since this domain can be employed for redirection purposes, users might notice notifications or other unknown websites via their browsers. The subdomains related to the service might be involved in advertising campaigns, possibly malicious activity, so generic detection by anti-malware tools occurred often.
According to users' reports, Redirector.gvt1.com mostly appears on Chrome and Firefox or Vivaldi web browsers. The combination of fake Microsoft alerts, freezing browser windows, intrusive pop-ups takes place on the hijacked browser.[2] Your computer isn't infected if you get these alerts, but if you get redirected to advertising services, receive pop-ups, you should avoid clicking on such material, so you do not catch any malware.
| Name | Redirector.gvt1.com |
|---|---|
| The purpose | This site is a service that informs about Google Chrome updates |
| Possible issue | Originally, this software is just a redirection service used by Google itself but sometimes can be misused by third-party developers |
| Browsers | Google Chrome and Mozilla Firefox browsers, however, we cannot claim that its appearance is not a possibility on other browser apps. Some Linux and Vivaldi browser users report the issue too |
| Repair | System repair might be needed when particular files get damaged or affected by the threat or processes. Running FortectIntego might find and repair these problems |
| Detection | If you are looking for a tool that would help you to discover all bogus products that might have been included in your computer system, we recommend employing antimalware tools |
While Redirector.gvt1.com can raise many questions about its security (especially when some users reported suspicious traffic to the domain, attempted to connect to by Chrome.exe), it is unlikely to be a sign of an infection. If you see suspicious redirects, pop-ups, banners, and other types of suspicious behavior, it is likely to be related to a potentially unwanted application that has been installed behind your back.
Redirector.gvt1.com virus is a term that might be used by users who have suffered from unpleasant activities that come from this domain. Actually it is not a virus, but might be misused by a third party for malicious purposes. In case you have some suspicions, advanced security measures need to be taken while dealing with various threats.
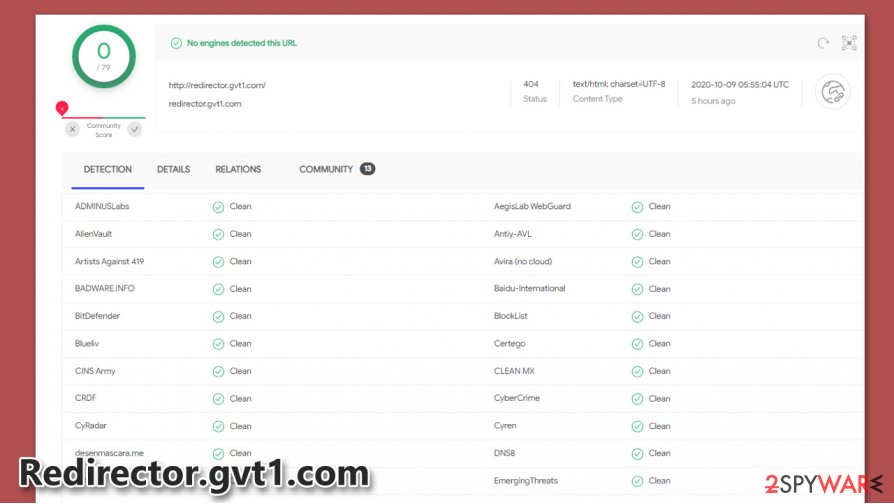
If scan results show that the domain is not safe for use and has been detected as suspicious/malicious, you should start being very cautious. Do not download suspicious files, do now click on suspicious links. Be sure that the best protection from all computer viruses is your attentiveness and safe browsing.
Detection from various antimalware programs have led to user concerns about Redirector.gvt1.com
Computer users have flooded all security forums with their concerns regarding the Redirector.gvt1.com that has appeared in their network traffic tables. A lot of bandwidth has appeared with this name and data sending inside the networks of various companies forced users to seek answers to what the domain is. It is actually a Google domain that is used for sending updates to Google products. Though the legitimacy seemed questionable, a few Antivirus programs have started detecting the unusual traffic for the Chrome.exe or Chrome_updater.exe files and have assumed its a virus, sending the files to quarantine.
Mostly concerned were the users of Avast and ESET. It seems these antivirus programs had marked the file as a virus. This has led the users to suspect the gvt1.com domain for the spread of malware. Luckily, the alarm seems to be false-positive, and the unusually large download file was related to a large package of Chrome updates.
Viruses, Adware, and other intruders appear out of mysterious places
We hope you have already found the true meaning of the gvt1.com domain and in case you see some detections in your antivirus regarding it, double-check, but do not be too worried. The risk of being infected through a legitimate Google domain is extremely low. However, we always feel it is very important for our readers to be reminded of the need of security tools and cautiousness. Stay safe online – never click on random links. Keep your security tools up to date and let them do their job. We recommend SpyHunter 5Combo Cleaner for real-time protection and FortectIntego is a great fixer for malware affected PC.
If you have been infected with an adware program, try to remember the latest sites you have visited, and the most recent downloads that were performed. According to computer experts from NoVirus.uk,[3] bogus software is very likely to get installed on your computer system if you are constantly using the Quick/Recommended mode.
This configuration should be changed to Custom/Advanced in order to secure your downloads properly. You will be able to manage all incoming objects and deselect bogus products that you do not want to see on your system. Besides, download/install all of your programs only from their official developers.
In addition, ad-supported programs can travel through third-party websites and services. For example, networks such as piracy-based ones, online-dating, gambling, gaming, porn-watching, and similar ones are vulnerable to potential threats as they lack the required protection. Due to this, adware and even malware can easily reach your computer system.
How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ [Solved] how to clean redirector.gvt1.com virus. Linux Mint. Forums.
- ^ Armadillo. Possible infection - redirector.gvt1.com. Malwarebytes forums. Topics.
- ^ NoVirus.uk. NoVirus. Security news articles.
