Safetyapp.click ads (scam) - Free Instructions
Safetyapp.click ads Removal Guide
What is Safetyapp.click ads?
Safetyapp.click ads show fake malware alerts to make users click links and purchase software

Safetyapp.click is a deceptive website constructed by cybercriminals aiming to profit illicitly. Many users inadvertently land on this site, whether due to redirection by potentially unwanted programs or by mistakenly clicking on misleading links. To bolster its seeming authenticity, it imitates a security scan that appears to be from McAfee's anti-malware software. Within a short span, it presents fake results, giving the impression of genuine threats.
The truth is, this method is a common scam technique used by numerous deceptive websites. The objective behind Safetyapp.click is to lead users to believe their devices are compromised and subsequently coax them into purchasing security software licenses or subscribing to added services. They bank on the trust users place in what seems to be a legitimate vendor pointing out malware on their devices. Such tactics can be categorized as scareware, designed specifically to leverage individuals' fears regarding malware.
| Name | Safetyapp.click |
| Type | Scam, phishing, redirect, adware |
| Operation | Claims that the antivirus software license has expired and that the computer is exposed to various malware |
| Distribution | Compromised websites, pop-up ads, potentially unwanted applications |
| Risks | Loss of finances due to fake subscriptions; redirects to other malware-laden, scam websites; installation of potentially unwanted or malicious software |
| Removal | Make sure you scan your system with SpyHunter 5Combo Cleaner – especially if you downloaded and installed software from a scam site |
| Other tips | If you do not clean your browser from cookies and other web data, you see the unwanted ads return or data continue being tracked. Stop it with FortectIntego |
How users end up on malicious sites
One prevalent avenue through which individuals encounter harmful online content, including scams, is by visiting torrent websites, unauthorized video streaming platforms, and dubious video converters with mature content. Owing to their association with contentious or potentially illegal content, these platforms often have relaxed oversight.
Such lax environments serve as prime grounds for cybercriminals to disseminate harmful files, which, on occasion, might covertly install perilous threats like ransomware on a user's device without them realizing until adverse effects manifest. Moreover, users might be exposed to malevolent advertisements and deceptive clickable elements that direct them to scam platforms like Safetyapp.click.
In some instances, the introduction of unwanted or malicious software onto a device can be the trigger for these scam exposures. If users observe unexpected ads popping up on a majority of websites, it could be indicative of adware or other malware presence. Given that such malicious elements often sneak onto devices through crafty techniques, like software bundling, it's imperative for users to routinely inspect their systems.
Scamming techniques used
Scammers have always evolved their techniques to exploit the unsuspecting, employing a mix of technology and psychology to achieve their nefarious goals. As digital realms expand and people rely more on technology for everyday tasks, cyber threats similarly grow in sophistication, seeking to manipulate users into making rash decisions that could compromise their data or finances.
Upon visiting Safetyapp.click, users are met with a message designed to induce panic:
Scan results: 2023_TROJAN virus, password_SPY, AdSwitcher detected
- Trojan found on this PC will most likely copy and delete all data from hard drives.
- Spyware will attempt to collect logins, passwords, and banking details.
- Adware usually replaces search results with false and scammy websites.
It is highly recommended to use an antivirus immediately!
The alert's wording, which might seem overwhelmingly technical to an average user with phrases like “2023_TROJAN virus” and “password_SPY”, is intended to lend the scam an air of authenticity. This authoritative language can be disconcerting, making the user more vulnerable to the scam's intent.
The scam also paints a dire picture of impending consequences. By suggesting that user data is at immediate risk of loss, theft, or exposure to more scams, it taps into primal fears. Such a depiction is calculated to make the user believe they're under immediate threat, prompting hasty actions without thorough evaluation.
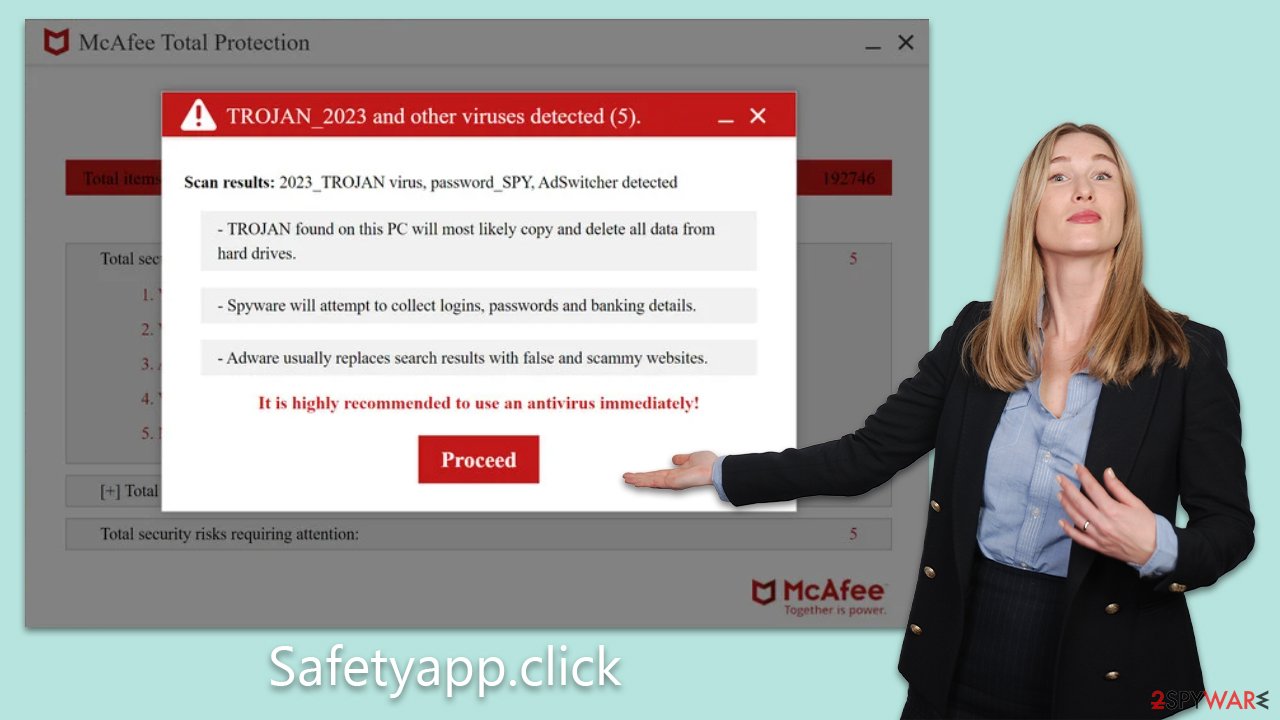
Adding to the urgency is the recommendation to act “immediately”. This pushes the user to prioritize this perceived threat, minimizing the chances they might consult someone or validate the legitimacy of the alert.
Moreover, the presentation and structure of the message are deliberately reminiscent of genuine antivirus software alerts. For many users, especially those not frequently encountering such warnings, distinguishing between real and fake becomes a challenge. This imitation further encourages users to take the message at face value.
Lastly, the scam brilliantly exploits innate human fears. Concerns of data breaches, financial losses, and identity theft are top of mind for most users. By highlighting these threats, the scam seeks to corner users into acting in the scammers' favor.
Checking the system for infections and removing Safetyapp.click ads
Upon encountering a deceptive site like Safetyapp.click, it's crucial to take immediate action to secure your system. Begin by conducting a comprehensive virus scan. Employ security tools such as SpyHunter 5Combo Cleaner or Malwarebytes to systematically and promptly eradicate any malicious entities on your device. This step is vital to ensure your PC remains unaffected by adware or malware.
While manual removal is an option, it tends to be tedious and intricate. Utilizing automated tools to purge unwanted applications streamlines the process and spares you considerable effort. Be cautious, as inadvertent removal of useful applications can result in unintended repercussions. After confirming your computer is devoid of malicious software, prioritize cleansing your browsers of cookies and other tracking mechanisms. To achieve this, you can utilize tools like FortectIntego or adopt the procedures detailed below:
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content, and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
Removing unwanted push notifications
Upon accessing Safetyapp.click, users are immediately prompted to enable push notifications. If granted permission, they are bombarded with persistent and intrusive ads.
These advertisements falsely claim system infections and aggressively urge users to install the purportedly remedial software. Moreover, they are peppered with various other deceptive messages designed to mislead and exploit. It's crucial for users to recognize the potential harm these notifications pose and to act swiftly to block them.
By denying or revoking Safetyapp.click's ability to send push notifications, users can shield themselves from these incessant misleading prompts and maintain the integrity of their browsing experience. It's always prudent to be cautious when websites solicit permissions, especially when their intentions are questionable. Follow these steps:
Google Chrome
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the URL's drop-down menu.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
![Stop notifications on Edge Chromium Stop notifications on Edge Chromium]()
- Click on More actions and select Block.
Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
How to prevent from getting adware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.








