Sardoninir ransomware / virus (Free Guide) - Recovery Instructions Included
Sardoninir virus Removal Guide
What is Sardoninir ransomware virus?
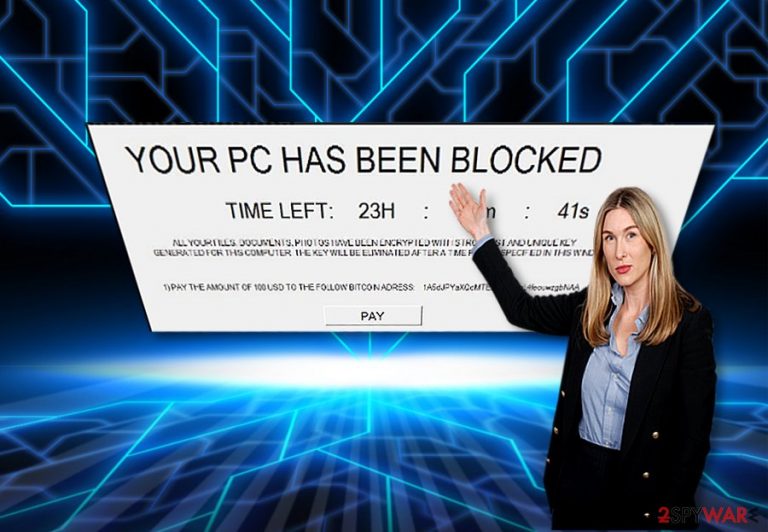
Sardoninir ransomware appends an extension to files and prevents victims from accessing them
Sardoninir virus happens to be another file-encrypting computer program[1]. It is another example of ransomware which threaten users into remitting the payment within the specified amount of time[2] – CryptoWall or WannaCry are one of the more prominent examples of such strategy.
Once installed, malware rushes to encrypt all data on the system with AES encryption algorithm, which also applies the .enc extension to the them. Suchlike files can then no longer be accessed or modified. Malware then drops a ransom note window which includes the timer of 24 hours and a demand to pay $100 worth of cryptocurrency.
| Name | Sardoninir ransomware |
| Type | File-locking virus |
| Encryption method | AES |
| File extension | .enc is appended to each of the affected files |
| Contact | safeanonym14@sigaint.org |
| Ransom demand | $100 to be paid in Bitcoin |
| Malware removal | Install powerful antimalware software and perform a full system scan |
| System fix | Once the virus is deleted, we recommend using FortectIntego to fix damaged Windows system components to avoid reinstallation of the operating system |
The ransomware market is full of vivid file-encrypting threats varying in their design, operation modes, the degree of complexity, etc. Fortunately, there are few highly destructive threats. However, they are able to wreck a serious damage worldwide. Speaking of this malware strain, it follows the basic operation pattern.
Though it is still under development, it hides its payload in spam emails[3]. After that, it encrypts the files with a strong algorithm which generates a unique complex key. It results in locking all your important data and attaching .enc file extension to each affected file.
At this stage, the ransom message appears alarming you with the elapsing clock. It instructs the victims to pay the ransom in return for the decryption key. In case you intend to contact the crooks, they provide safeanonym14@sigaint.org email address.
You might try paying the ransom but it does not give any guarantees that the crooks will return the files. On the other hand, they may just ignore your plea for mercy. The malware is still suspected to be under development so the virtual community should be vigilant. Instead, proceed to Sardoninir removal.
Ransomware distribution techniques
Ransomware authors devise new ways to break through into users’ computers. Usually, they do so by forcing them to open corrupted spam emails[4]. This is when the infection of ransomware takes over the computer. In addition, you should be aware of trojans and other sorts of malware that serve as mediators for the ransomware to enter your device.
Exploit kits often perform such a role. Therefore, you should be careful not only while browsing online but arm up with proper security applications. It would be better to combine anti-virus and malware removal utility. Update them and run the scan, the latter will help you remove all malware as well.
Sardoninir elimination guide
When it comes to crypto-malware, do not waste time and energy meddling with Sardoninir ransomware removal manually. Run the scan with SpyHunter 5Combo Cleaner and Malwarebytes. Note that they will not help you decrypt the files. For that reason, alternative solutions might be effective.
Some of them are suggested under the headline “Bonus decryption methods” below the instructions. Speaking of them, they will help you regain full control of the computer if you struggle with virus removal. On the final note, keep in mind that file-encrypting threats rapidly evolve, and the hackers tend to shift their attention to mobile devices as well[5]. For that reason, keep the system up-to-date and retain cautiousness.
Getting rid of Sardoninir virus. Follow these steps
Manual removal using Safe Mode
It is likely that the virus may prevent you to remove it and block certain system functions. In that case, follow these instructions to regain full access.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Sardoninir using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Sardoninir. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Sardoninir from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Sardoninir, you can use several methods to restore them:
What is Data Recovery Pro program?
It is the tool which is devised to help users to retrieve lost and damaged files. It is also practical in restoring deleted emails and files in data storage devices.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Sardoninir ransomware;
- Restore them.
How useful is Windows Previous Versions feature?
This function only works if System Restore is enabled. Though it is more time-consuming since you have to go through all the affected files by the virus, you might succeed in recovering some of them.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer method
This program uses shadow volume copies to recover lost data. There are no reports whether malware deletes them, so the chances to recover the files are higher.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Sardoninir and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Report: Ransomware Attacks Are Growing, Shifting Rapidly. CIO Today. Daily Briefing for Technology's Top Decision-Makers.
- ^ Harold Stark. When Attacked By Ransomware, The FBI Says You Shouldn't Pay Up. Forbes. Business, Entertainment, Lifestyle, Security.
- ^ Richard Price. Breaking: Scammers Shift to Social with New AusPost Ransomware Attack. Mailguard Blog.
- ^ Andra Zaharia. Ransomware Distribution: How One Infection Can Go Network-Wide. Heimdall Security. Computer Security News and Analysis.
- ^ Gabriela Vatu. 2016 Mobile Malware Trends: 40 Million Attacks and the Rise of Ransomware. Softpedia. Free Downloads Encyclopedia.







