Sauwoaptain.com (Simple Removal Guide) - Free Instructions
Sauwoaptain.com Removal Guide
What is Sauwoaptain.com?
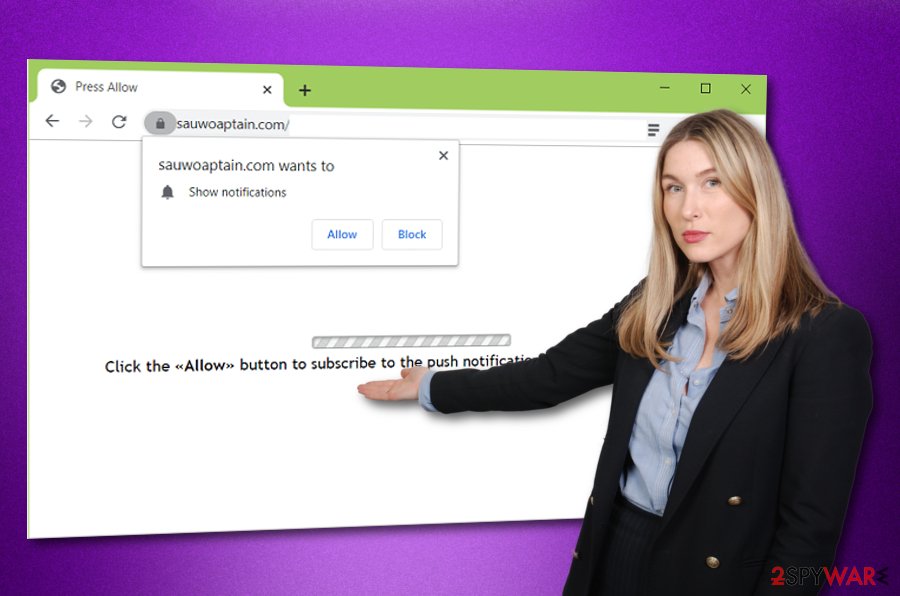
Sauwoaptain.com – adware that forces redirects to affiliate sources and pushes advertising content

Sauwoaptain.com is an adware virus that gets the user involved in various potentially unwanted activities such as advertising and redirecting. The first thing that happens is browser hijacking and bogus modifications are added to the homepage and new tab URL sections. Afterward, the adware can include extensions, HTTP cookies,[1] and plug-ins to the browser settings and also add some files/entries into the Task Manager, Registry sections. Sauwoaptain.com virus is a sneaky app that infiltrates computer systems by using a deceptive bundling technique and aims to push attractive-looking content to the users to increase the clicks on the advertisements and earn income from the pay-per-click technique.[2]
| Name | Sauwoaptain.com |
|---|---|
| Type | Adware/potentially unwanted program |
| Target | This suspicious product can target web browser applications such as Google Chrome, Mozilla Firefox, Internet Explorer, Microsoft Edge, and Safari |
| Aim | The main goal of such adware is to display as many attractive advertisements as possible and collect income from the pay-per-click technique |
| Actions | The adware can get the user involved in intrusive advertising activities, redirecting sessions. Also, the PUP can modify the browser's homepage and new tab URL section, start collecting browsing-related data |
| Distribution | Adware programs are most likely spread through third-party downloading sources such as cnet.com, softonic.com, download.com by using the “bundling” technique. Also, such apps can get delivered through infectious advertisements and hyperlinks |
| Removal | You can get rid of the adware program by employing automatical removal software or by using the manual guiding steps that have been added to the end of this article |
| Fix | If the adware program has brought some additional threats to the machine that have compromised some entries and similar objects, you can try repairing the system by using a tool such as FortectIntego |
Sauwoaptain.com, serving from the 78.140.190.78 IP, is not the app you should trust or leave lurking on your computer system. This adware can infect any type of web browser, including Google Chrome, Mozilla Firefox, Internet Explorer, Microsoft Edge, and Safari. Afterward, your browsing sessions will be likely filled with intrusive advertising posts, banner ads, and coupons.
Sauwoaptain.com virus aims to display beneficial-looking content and offer various products and services to random users. Be aware of the pop-ups that flood you from this domain as you are likely to be convinced to subscribe to a useless service or pay for a product that you do not truly need, e.g. rogue security software and other system tools.
Continuously, Sauwoaptain.com can provide you with fake reward claims and various surveys that require entering personal information, contact details, or credential data. If you give away your contacts to random people, you might get spammed with unwanted content via email or mobile phone. However, revealing personal information creates a bigger risk.
You should NEVER reveal any sensitive information to rogue developers as you cannot know where such data might be used by various hackers, your data can easily get exposed. Also, if Sauwoaptain.com convinces you to provide financial information, you can get your money easily swindled by remote hackers or be forced to pay for random services that you do not remember subscribing to.
If the advertisements from Sauwoaptain.com come in an excessive amount and start interrupting your computing work frequently, your web browsers and entire machine might start struggling from all the intense activity that is being performed. This can also touch your CPU and force the unit's power to rise over 60% and even start overheating.
Also, Sauwoaptain.com can start redirecting you to sponsored sources where additional offers and deals are provided. Even though you are most likely to land on affiliate websites, there also is a risk of ending up on a malware-laden location. This way you can easily get your computer system infected with a trojan or another type of virus.
Continuously, Sauwoaptain.com might initiate browsing data collecting by injecting tracking objects such as HTTP cookies, beacons, and pixels into your web browser app. This way the adware might be able to record information related to your latest search queries, most frequently searched offers, saved bookmarks, hyperlinks and adverts accessed, your IP address, geolocation, etc.
Afterward, Sauwoaptain.com virus developers can use such type of information for sharing it with other parties and receiving monetary benefits. Additionally, these people might generate targeted advertisements that are related to the collected data and seek to attract you by providing similar offers that you have been searching for lately.
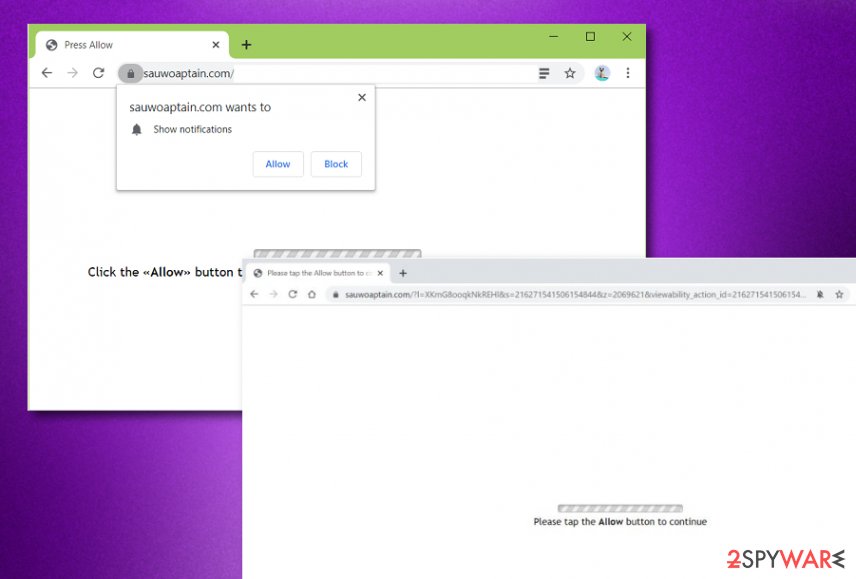
In some cases, you might receive Sauwoaptain.com pop-up ads only while you are visiting third-party websites and surfing the Internet without any proper security. Regarding this fact, downloading AdBlock[3] to your web browser might be enough to help you to get rid of the annoying incoming ads. Also, you can try removing the suspicious adware-related domain from your browser's Notifications list:
- Open the browser app that has been delivering you ads.
- Click on the three dots that you will find on your upper right.
- Access the menu and continue with Settings -> Advanced.
- Afterward, you should see the Notifications list option under Site Settings.
- Go through the entire menu until you locate Sauwoaptain.com.
- Click the remove or disable button next to the domain name.
However, if the advertising activities have got too intense, an adblocking tool might no help you here. For this purpose, you should remove Sauwoaptain.com with the help of reliable antimalware software or the manual step-by-step guidelines that we have provided for you at the end of this article. There you will learn how to clean both your OS and web browser apps.
Note that you have to complete Sauwoaptain.com removal fully. This includes eliminating all additional products that have been brought by the adware program. In case the adware has brought other threats to your computer system, you can search for possible corruption automatically. If you find some machine damage, you can try fixing things with the help of system repair software such as FortectIntego.
The most popular ways to spread adware. Avoiding tips included
Cybersecurity specialists from Virusai.lt[4] claim that adware programs mostly get delivered by using deceptive techniques such as “software bundling”. This happens when the PUP comes added to some type of freeware or shareware and gets bundled when downloading the products from third-party sources such as cnet.com, download.com, and softonic.com.
Also, the most vulnerable users are the ones who have chosen the “Recommended” installing mode as the default settings. Rather than risking to find adware on your machine one day, you should opt for the “Advanced” downloading option where you will be able to take full control of your incoming downloads, including deselecting the unwanted and bogus-looking ones.
Continuously, adware applications can get delivered through hyperlinks and various third-party advertisements. You should be careful while browsing the Internet sphere, avoid suspicious-looking websites and do not click on every location that you see. Also, you should avoid various fake software updates that can pop-up while browsing the web. If you have any concerns about a particular update, check the latest update releases on the software developer's official web page.
Another thing you should do is ensure that reliable automatical antimalware software is running on your computer and protecting its systems 24/7. Make sure that you choose a tool that includes as many protective features as possible and keep the software regularly updated, otherwise it might not operate properly or include various bugs.
The entire removal process of Sauwoaptain.com virus
You can remove Sauwoaptain.com with the help of automatical software that can complete the entire process in a few minutes of time. Choose a reliable tool and you should be happy with the results. Another way to get rid of this cyber threat is to carry out the manual guiding steps that have been provided below. There we have displayed how to clean your operating system and web browsers such as Google Chrome, Mozilla Firefox, Internet Explorer, Safari, and Microsoft Edge.
In order to succeed in the Sauwoaptain.com removal process fully, you have to eliminate all additional components that might have been added to your computer and web browsers during the adware attack, otherwise, the PUP might easily boot itself within the next computer startup process. When you get rid of the threat permanently, ensure that your computer system is protected manually and automatically for possible future attempts. Memorize all of the avoiding tips once more if needed.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Sauwoaptain.com. Follow these steps
Uninstall from Windows
To eliminate the adware from your Windows computer system, you should carry out the following guiding steps.
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Delete from macOS
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Microsoft Edge
Delete unwanted extensions from MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Clear cookies and other browser data:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Restore new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Disable if you found any suspicious domain.
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.

If this solution failed to help you, you need to use an advanced Edge reset method. Note that you need to backup your data before proceeding.
- Find the following folder on your computer: C:\\Users\\%username%\\AppData\\Local\\Packages\\Microsoft.MicrosoftEdge_8wekyb3d8bbwe.
- Press Ctrl + A on your keyboard to select all folders.
- Right-click on them and pick Delete

- Now right-click on the Start button and pick Windows PowerShell (Admin).
- When the new window opens, copy and paste the following command, and then press Enter:
Get-AppXPackage -AllUsers -Name Microsoft.MicrosoftEdge | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register “$($_.InstallLocation)\\AppXManifest.xml” -Verbose

Instructions for Chromium-based Edge
Delete extensions from MS Edge (Chromium):
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Clear cache and site data:
- Click on Menu and go to Settings.
- Select Privacy, search and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Reset Chromium-based MS Edge:
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.

Remove from Mozilla Firefox (FF)
To properly clean Mozilla Firefox after the adware attack, use these guidelines.
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
To reverse Google Chrome back to its previous position, you should apply these instructing steps.
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Sauwoaptain.com registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting adware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ HTTP cookies. Mozilla Developer. Technology information.
- ^ Pay-per-click. Wikipedia. The free encyclopedia.
- ^ What is AdBlock?. Quora.com. Relevant questions and answers.
- ^ Virusai.lt. Virusai. Security and spyware news.























