Search.myprivacyswitch.com virus (Free Instructions)
Search.myprivacyswitch.com virus Removal Guide
What is Search.myprivacyswitch.com virus?
Search.myprivacyswitch.com might track certain data when you browse the web
You might have noticed that Search.myprivacyswitch.com has replaced your homepage without asking – this is because you have installed a browser hijacker on your system. These infections are generally considered to be minor, although they cause significant inconveniences by disrupting browsing sessions.
These programs are distributed using a variety of different deceptive techniques, so their appearance on the computer does not necessarily depend on the user’s will. For instance, you may start seeing this web address as your homepage after the shady Privacy Switch extension is installed on your computer disguised as some software update or an additional component in your downloaded software package.
Besides, other suspicious software may come along with this hijacker, all designed to ensure that this intruder-of-a-site remains as the default search engine and the homepage of the affected PC. We will talk about the reasons for this persistence in a minute, but before we do, we would like to remind you that Search.myprivacyswitch.com removal instructions and recommendations are presented at the end of this article.
| Name | Search.myprivacyswitch.com |
| Type | Browser hijacker |
| Distribution | Software bundles, deceptive ads, third-party websites |
| Operation |
|
| Elimination | You can easily get rid of suspicious extensions manually, although scanning the device with anti-malware might be quicker |
| System fix | If security software indicates malware on your system, don't forget to fix virus damage – we recommend using FortectIntego for the job |
The easiest way to remove potentially unwanted programs is by performing a scan with security software, such as SpyHunter 5Combo Cleaner. Manual elimination is also possible – here are instructions on extension uninstallation from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Unfortunately, this might not be enough if the browser hijacker is installed as a program (Windows) or Application (Mac). If that is the case, you would have access to the Control Panel or Application sections and delete the PUP manually. For more details, refer to the section below.
Additionally, you might want to clear your browsing data if you can't get rid of the ads or redirects (you can also do it automatically with a PC repair and maintenance utility FortectIntego):
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
So what are the main reasons for the browser hijack? In fact, there is no mystery in that. Creators of the application simply want to generate easy money from affiliate advertising, and a legitimate-looking search engine seems to them as a suitable platform to implement this plan. They have the full power to control over what search results to provide and what these results will promote.
Unfortunately, creators of this hijacker mainly focus on the first part and fill the search results with a variety of sponsored content while their legitimacy, trustworthiness, or simple security remain unexplored. So, it is not uncommon to experience redirects to some obscure, infectious, and phishing-oriented sites.
We recommend staying away from web browsing while the program is still on the computer. In the meantime, you should equip your computer with proper software and remove the PUP from the computer.
PUP distribution methods explained
Search.myprivacyswitch.com usually finds its way on the computer by exploiting the inappropriate software installation settings. While installing the downloaded freeware or shareware, users often opt for the quick modes to get their hands on the desired software as soon as possible.
What they are not aware of, though, is that software downloaded off the Internet is commonly bundled with various additional components, not all of which might be useful or safe. In such a case, the quick software installer is not helpful at all. On the opposite, it automatically allows all software package components to install on the computer without allowing you to opt-out of the undesirable ones.
Thus, opting for the “Advanced” or “Custom” modes is a much safer option since it allows you to run the installation step-by-step, monitoring all the software traffic into your computer.
Fix your browser by deleting unwanted apps
If you keep on running into the Search.myprivacyswitch.com virus every time you open your browser and cannot seem to get rid of this parasite regardless of what you do, do not panic. Everything is not as bad as it might seem. Your computer is not infected with some severe cyber infection, and problems with the app's removal probably arise only because you are not using the proper techniques for this purpose.
Thus, we recommend leaving this job for the professional antivirus tool to sort out. Run a full system scan and watch as the virus defense utilities remove Search.myprivacyswitch.com files one by one.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Search.myprivacyswitch.com virus. Follow these steps
Uninstall from Windows
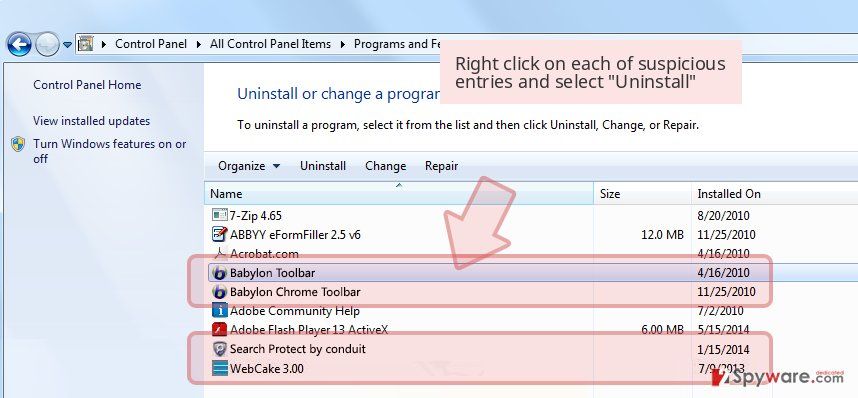
Since Search.myprivacyswitch.com is a potentially unwanted program, it is likely that it will be hiding on your computer under different names. So, when you follow the steps below, keep in mind that you will not find it labeled myprivacyswitch.com or anything similar. So stay observant and look for software that appears on your computer you do not recall.
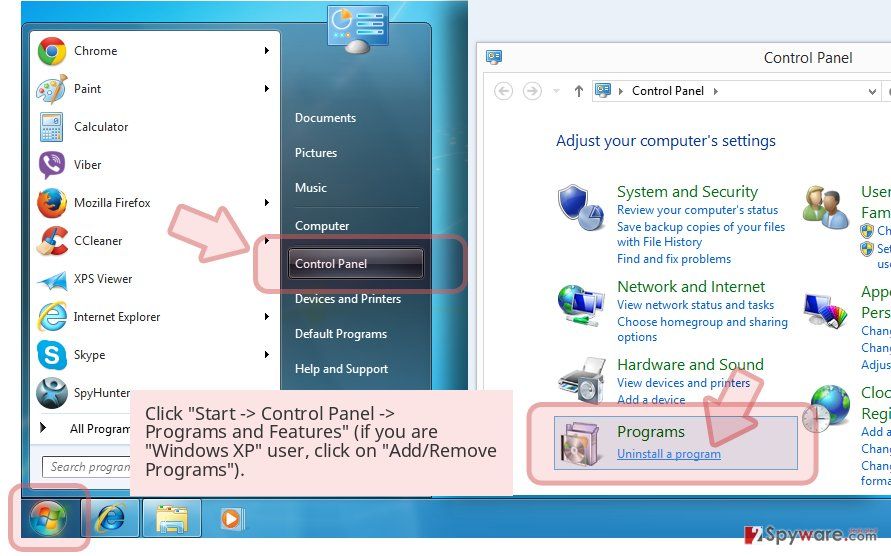
-
Click Start → Control Panel → Programs and Features (if you are Windows XP user, click on Add/Remove Programs).

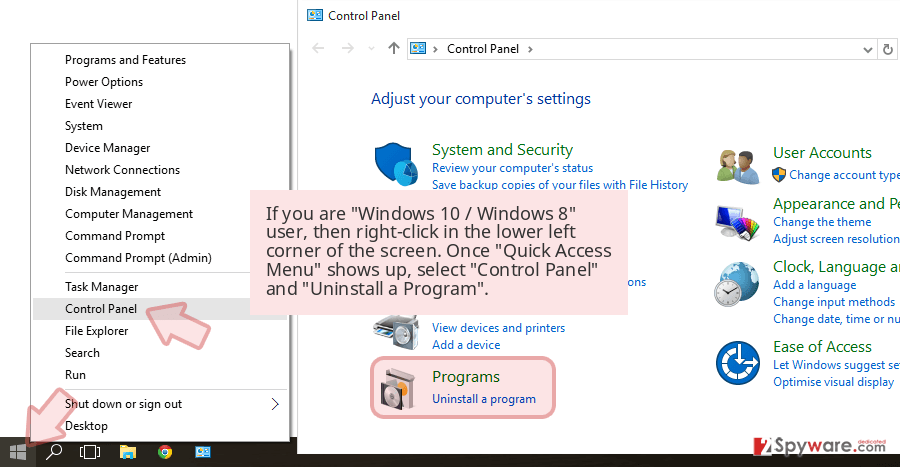
-
If you are Windows 10 / Windows 8 user, then right-click in the lower left corner of the screen. Once Quick Access Menu shows up, select Control Panel and Uninstall a Program.

-
Uninstall Search.myprivacyswitch.com and related programs
Here, look for Search.myprivacyswitch.com or any other recently installed suspicious programs. -
Uninstall them and click OK to save these changes.

Delete from macOS
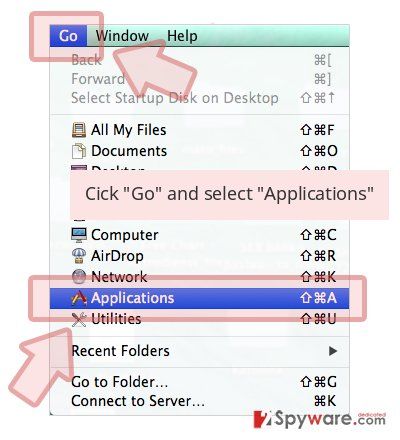
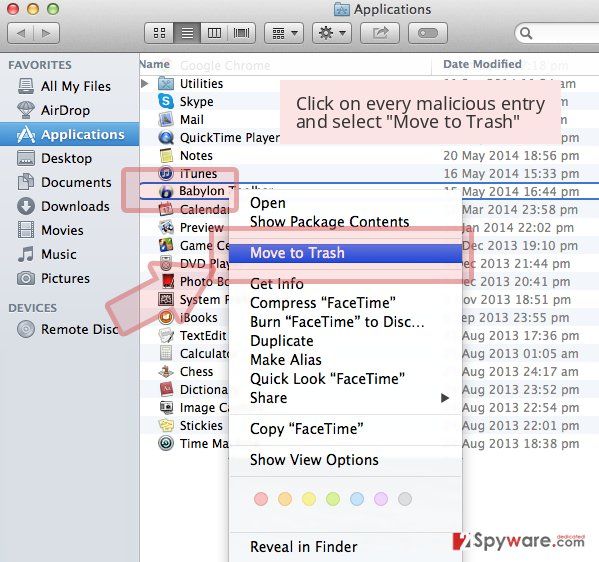
-
If you are using OS X, click Go button at the top left of the screen and select Applications.

-
Wait until you see Applications folder and look for Search.myprivacyswitch.com or any other suspicious programs on it. Now right click on every of such entries and select Move to Trash.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Search.myprivacyswitch.com registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting browser hijacker
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.