Search.wikicraftpro.com virus (Removal Guide)
Search.wikicraftpro.com virus Removal Guide
What is Search.wikicraftpro.com virus?
Should you rely on Search.wikicraftpro.com search results?
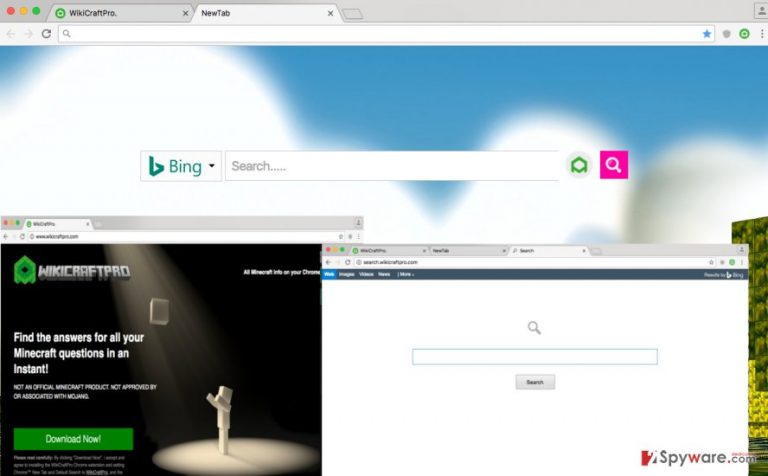
Search.wikicraftpro.com virus is a wrong term typically used to describe a browser hijacker, which spreads alongside other free programs. It can be added to the computer system after installing a free game, download manager, audio or video player, or a similar program. Once installed, this browser hijacker changes some settings in Google Chrome browser and sets Search.wikicraftpro.com URL as the homepage and default new tab page address. At the moment, this hijacker can only affect this particular Internet browser.
The intended URL appears to be a web search engine, which looks like a typical website of this kind. It provides a search box in the middle of the webpage, and you can choose what search engine do you want to use (Bing, Yahoo! Or Google). However, be aware of these search results are not the original ones and can be ALTERED! The user can use regular search, or choose to search the minecraft.gamepedia.com site. However, there are some reasons why you should not trust this search engine or even start thinking about Search.wikicraftpro.com removal, so let us list them for you.
- Search.wikicraftpro.com redirect issue. You might notice that some of the search results do not take you to desired web pages once you click them. You might experience redirects to strange-looking Internet sites, so we suggest you to be very careful while using this search engine!
- Browser crashes and system slowdowns. Do not be surprised that after installing this hijacker your browser starts to perform slower than it usually does. Your browser might start not to respond or even crash from time to time. These problems can also initiate system slowdowns and an overall decrease of computer’s performance.
- Lots of sponsored search results. It seems that this additional system application “may include and/or enable you to add Content to them.” This content might show up in a form of links to third-party advertisements, websites, buttons, gadgets, apps, and so on. Beware that such content might be insecure!
- Data collection. This browser extension is capable of collecting certain data about the computer user, including search queries made through Search.wikicraftpro.com, user’s browsing history, interaction with advertisements and so on. This data might be shared with unknown third parties afterward.
Another suspicious fact that makes us wonder about the reliability of this search engine is that it has been developed by a company (ClientConnect Ltd.) that has created infamous browser redirect viruses such as Trovi.com. We strongly recommend you to think whether you wish to use such application and the indicated search engine that it provides. If you don’t, remove Search.wikicraftpro.com using anti-malware software like FortectIntego.
How does this program spread?
Search.wikicraftpro.com hijack can happen if the computer user tends to be careless or rush to install new computer programs. Keep in mind that almost all free programs recommend installing additional programs alongside them, and if the user does not manually deselect agreements to install them, they end up being set up on user’s operating system without even notifying the computer user. To avoid that, the user just needs to adjust installation settings and set them to Custom or Advanced mode. Then, the user has to deselect all optional elements, for instance, browser toolbars, extensions, apps, and other suggested components to avoid installing them.
How to remove Search.wikicraftpro.com?
To remove Search.wikicraftpro.com virus, the user can use the anti-malware software. If one does not have it, then he/she can download one of the recommended ones that are provided below. In case the user wants to carry out manual Search.wikicraftpro.com removal, the instructions provided below might come in handy.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Search.wikicraftpro.com virus. Follow these steps
Uninstall from Windows
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Delete from macOS
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Google Chrome
Go to browser extensions and delete WikiCraftPro extension and every other browser extension that you cannot remember installing.
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Search.wikicraftpro.com registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting stealing programs
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
