Shiny Tab browser hijacker (virus) - Free Instructions
Shiny Tab browser hijacker Removal Guide
What is Shiny Tab browser hijacker?
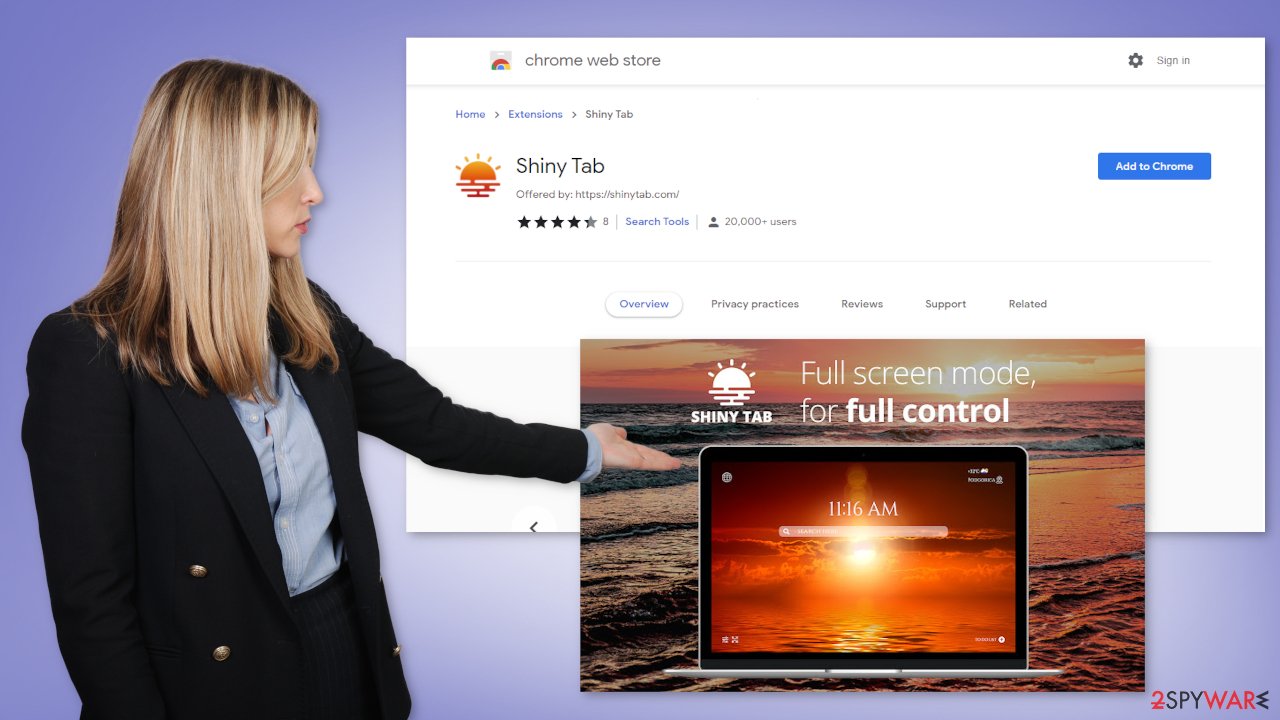
Shiny Tab pretends to improve productivity by changing the background into a sunset picture

Shiny Tab is classified as a browser hijacker because it changes the main settings, like the homepage, new tab address, and search engine. It may also collect various browsing-related data. This is all done for the purpose of generating revenue. Once an extension like this is added, it can force users to browse only through selected channels which raises many user privacy and security concerns.
When a plugin has such control of the user experience it can lead them to dangerous pages that trick people into providing their personal information or downloading other PUPs (potentially unwanted programs),[1] and even malware. The add-on can generate pop-ups, redirects, banners, and other types of commercial content which could be promoting online scams, adult and gambling websites.
| NAME | Shiny Tab |
| TYPE | Browser hijacker; potentially unwanted program |
| SYMPTOMS | The main browser settings may get changed; users might get redirected to shady websites |
| DISTRIBUTION | Unsafe websites, deceptive ads, freeware installations |
| DANGERS | The application may be collecting data about users' browsing activities; users might get redirected to dangerous websites that can trick them into providing personal information or downloading PUPs and malware |
| ELIMINATION | Remove the extension via browser settings; performing a scan with professional security tools is recommended |
| FURTHER STEPS | Use FortectIntego to clear your browsers from cookies and cache |
Distribution techniques
Shiny Tab can be downloaded from the chrome web store. Although it is rare, sometimes browser hijackers slip through the lengthy review process. The problem is that digital marketplace owners still do not know how to identify PUPs. One app could be liked by one person, and by another one considered to be a virus.
That is why it is so important to always do your research no matter what. Read the reviews, look at how many users the applications have, and what are the ratings. However, more often people infect themselves with hijackers by browsing through shady websites.
Usually, these are sites that engage in illegal activities because they are unregulated. Rogue advertising networks can place their ads there, and as a result, such pages are full of deceptive ads and sneaky redirects. People accidentally end up on promotional pages for these bogus browser extensions and download them. They get convinced by clever advertising campaigns.
Sometimes, hijacker developers claim that their product was developed in collaboration with a big tech company like Google or Apple. This makes it look legitimate and trustworthy. They also boast about usually non-existent functions that will make users' lives much easier. It is important not to get swayed by false promises and look for applications that are well known, have plenty of reviews and press coverage about them.
Unfortunately, this is not the only way people infect themselves with hijackers. That can also happen without the users' knowledge. Often this happens when people install freeware. Sites that distribute it, include additional programs in the installers that are often adware – a program that monetized user activity by generating ads and collecting data.
Remove the unwanted extension
You can remove browser add-ons by going to your settings. Find the list of extensions installed in your browser and remove the Shiny Tab. We show how to do that in the guide below:
Clear your browsers
Now that you have removed the intruder completely, it is a good idea to take care of your browsers. Websites and web-based applications can collect various data with cookies[3] and cache. That includes your IP address, geolocation, websites you visit, links you click on, and things you purchase online.
Normally, that is nothing out of the ordinary, as legitimate parties use them to personalize the user experience by showing relevant results. However, individuals that are in it only for their own gain can sell this information to rogue advertising networks and other third parties. That way you can get targeted with scam promotions which further puts you in danger.
That is why security experts recommend clearing browsers regularly. However, because it is an annoying process for many, it is left forgotten. We suggest getting a maintenance tool like FortectIntego that can get rid of cookies and cache automatically with a click of a button. Besides, this software can fix various system errors, corrupted files, and registry issues which is especially helpful after a virus infection.
How to prevent from getting browser hijacker
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Potentially unwanted program. Wikipedia. The Free Encyclopedia.
- ^ Will Dormann. Bundled Software and Attack Surface. Cmu. Carnegie Mellon University Software Engineering Institute Blog.
- ^ What are Cookies?. Kaspersky. Home Security Blog.











