Shortcut virus (Virus Removal Guide) - updated Jun 2020
Shortcut virus Removal Guide
What is Shortcut virus?
Shortcut virus is the malware that hides files and replaces them using inaccessible shortcuts but can cause more damage to the OS
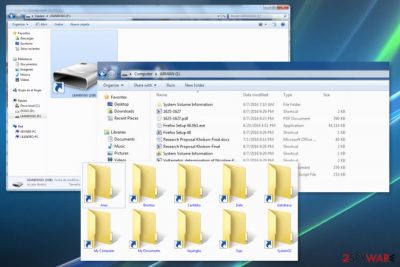
Shortcut virus is the trojan-type malware that also has features of the worm threat because it hides your files and folders, replaces them with shortcuts. Even those shortcuts look the same those files are malicious. It often targets USB Flash Drive devices or computers and converts those valid files into inaccessible forms. Actual files are not deleted, but you cannot normally use the needed file. You can remove this virus, and once that is done, you will recover your files. However, some of the users claim that it damages data permanently and that file loss is a real issue. This threat can also be called the USB Shortcut virus because it makes files unopenable and inaccessible on USB drivers mainly. Trojan hides your files and replaces them with the same name. It is easily spreadable too, unfortunately. Any link once clicked can trigger the download of the malware script and affect the operating system, all connected devices.
| Name | Shortcut virus |
|---|---|
| Type | Malware |
| Issues | This intruder has trojan and worm functionalities and can affect the machine significantly when it runs in the background for a while. It degrades system performance and affects the speed, disables or adds various features, and programs on the machine to affect the persistence |
| Symptoms | Files get altered when the virus replaced data using shortcuts with the same name. Data becomes inaccessible and can even get damaged |
| Distribution | This threat can get on the system via infected email attachments, sites that rigger malware downloads, or even other malware that is set to spread such intruders directly on the targeted system |
| Elimination | Shortcut virus removal is the process that can be difficult due to the purpose of malware and particular features the threat has, so running the full system scan on the machine using AV tools can help significantly |
| Repair | File recovery and fix for affected files can help you with the damage and further use of the computer |
Shortcut virus is a Trojan horse[1] that is designed to transform files on the corrupted device into shortcuts. Thus, it makes data inaccessible. However, the vast majority of antivirus can detect this cyber threat as a Trojan.VBS.TTE (B), Worm:VBS/Cantix.A., Troj/Agent-NXIMal/FakeAV-BW, and other names.
Shortcut malware spreads via portable devices, such as USB drives, Pen-drives, SD cards, etc. However, they might affect desktop computers and laptops. Most of the time it happens when a user connects an infected external device to the PC. Due to the operation peculiarities, security researchers excluded three main versions of the virus:
- Flash drive shortcut virus;
- File shortcut virus;
- Folder shortcut virus.
However, the latter two – File and Folder viruses – are often combined and referred to as File and Folder shortcut virus. Despite slightly different behaviors, the termination of these cyber threats remains the same. The best way to remove Shortcut virus is to employ malware removal tool and scan the device. To recover files affected in system folders after the removal procedure – rely on FortectIntego.
This version of Shortcut virus can infect USB, SD cards, or any other portable device. As soon as it infiltrates, it puts all the files stored on the device into a hidden folder. Then it creates a shortcut.exe which prevents from accessing personal data.
However, the execution of shortcut.exe may lead to even bigger problems. This Trojan horse might act like spyware or keylogger. Thus, it might collect personally identifiable or even banking-related information. Therefore, immediate Shortcut virus removal is needed.
The main features of the File and Folder Shortcut virus
This version of Shortcut malware aims at files and folders. On the affected device, it hides and replaces files with these extensions:
- shortcuts.exe;
- shortcut.lnk;
- file.ini (desktop.ini);
- shortcut.vbs.
After the Shortcut virus hijacks, it might also install other malicious software to the affected device which might pose a danger to the victim’s privacy. Thus, this malware might monitor and even steal personal information, including credit card details. 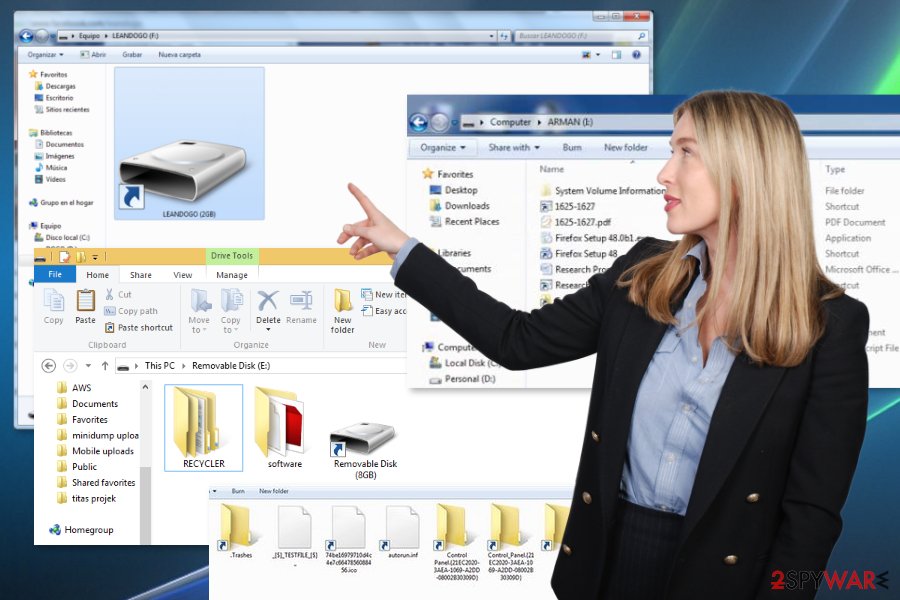
The virus takes advantage of Windows Autorun and Autoplay feature
Users can get infected with malware if they:
- do not scan an external device with an updated antivirus once they connect it to the computer;
- plug a portable device to the infected computer;
- download malicious programs or files.
Security experts from Norway[2] say that such silent virus is a popular cyber threat that spreads via USB and other external devices. When a user connects an infected device to the computer, malware exploits Windows Autorun and Autoplay feature.[3]
The virus uses a vulnerability in a way how Windows operating system handles shortcut files. Such files with .lnk extension belong to Windows and are designed to run various programs when a user clicks on it. However, this USB malware does not need victim’s click in order to be executed. It can be launched automatically.
Thus, to avoid this cyber threat, users are suggested to use reputable and updated antivirus to scan all attached external devices. Additionally, do not connect USB or other gadgets to other computers if you are not sure that they are virus-free.
Instructions for Shortcut virus termination
Nevertheless, it is recommended to remove Shortcut virus using malware removal software or security tools, such as SpyHunter 5Combo Cleaner, or Malwarebytes; there are also a few ways how you can get rid of it manually. However, if you choose manual elimination, please follow the instructions carefully. This is not the simplest threat to get rid of, so you may need some additional tips and tricks.
However, the main Shortcut virus removal method could be the full system scan using anti-malware tools. Once the threat is indicated for you, it can be deleted using the same AV detection engine. Nevertheless, you still need to repair files and system functions when the malware affects them.
The best option for such malware is to remove Shortcut virus and clean the machine fully. Anti-malware tools focus on cleaning threats from the system. Tools like FortectIntego or optimizer applications, PC repair programs can find damaged data and fix virus damage where needed.
Method 1. Delete the virus using command prompt to clear the external devices
- Go to Run.
- Type cmd and click OK button.
- Connect the infected removable drive.
- Enter this command to the command prompt window: attrib -h -r -s /s /d e:\
NOTE: instead of e: you have to write the name of the infected removable drive. - Press Enter.
- The virus should be eliminated. Furthermore, you have to copy and save necessary information from the removal drive.
- Then format a removable drive. Once it’s done, you can copy back previously saved data.
Method 2. Shortcut virus removal using Registry editor
- Open Windows Task Manager by clicking Ctrl + Shift + Esc on a keyboard.
- Go to Process tab.
- Find process .exe.
- Right-click it and choose End Process.
- Access Registry editor: Click Windows key + R and type regedit.
- Click Enter.
- In the Registry editor, navigate to this key:
HKEY_CURRENT_USER/Software/Microsoft/Windows/CurrentVersion/Run - Find odwcamszas.exe and delete it.
- Restart the computer to save the changes.
Method 3. Tweak CONFIG to eliminate Shortcut malware
- Access Temporary Files folder by entering %temp% in Run.
- Find .vbs and delete it.
- Open Run and type msconfig.
- Go to Startup Tab.
- Delete vbs.
Getting rid of Shortcut virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Shortcut using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Shortcut. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Shortcut and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting malware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Trojan horse (computing). Wikipedia. The free encyclopedia.
- ^ Viruset. Viruset. Latest cyber security and spyware news.
- ^ Mary Landesman. Disable Autorun/Autoplay. Lifewire. Tech how-to guides and tutorials.





















