Skithemlaid.live ads (fake) - Free Guide
Skithemlaid.live ads Removal Guide
What is Skithemlaid.live ads?
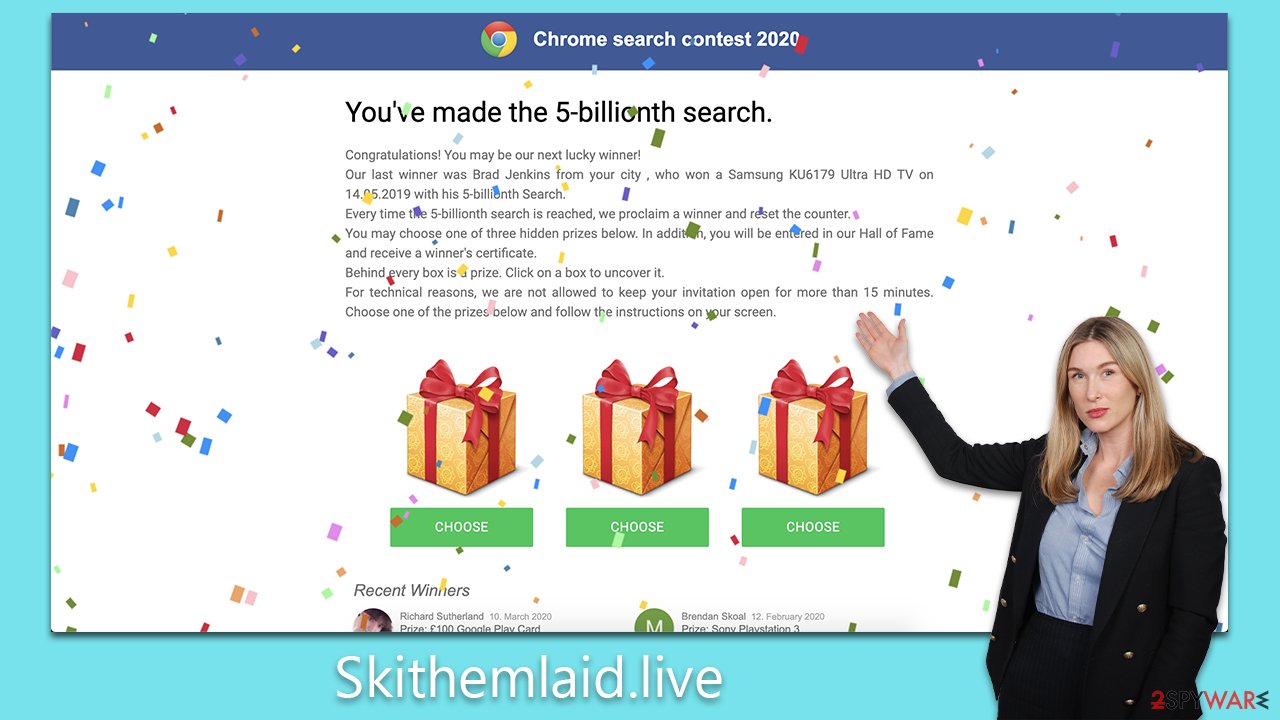
Skithemlaid.live shows fake prize winnings to manipulate users into providing their personal info
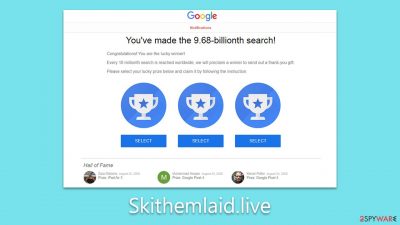
Skithemlaid.live is yet another scam website that targets unsuspecting users with fake giveaways and prizes. Similarlt to many other sites of this nature, it entices visitors with the promise of valuable gifts, only to deceive them later on. The site utilizes the appeal of winning something for virtually no effort, asking users to answer a few simple questions or “select the box” from three different choices.
However, the harsh reality is that Skithemlaid.live has no actual prizes or rewards to offer. The primary goal of these scammers is to persuade victims that they are fortunate enough to have won a prize. But when the time comes to claim the supposed reward, victims are prompted to provide personal information which can be exploited later by cybercriminals.
Furthermore, Skithemlaid.live may also trick users into downloading suspicious software, potentially exposing their devices to malware or other security risks. In this way, scammers not only gain access to personal information but also potentially compromise the security of users' devices.
Thus, please do not engage with the scam content on this page. If you have downloaded something or you see suspicious ads/redirects, we recommend checking the system for infections, as we explain below.
| Name | Skithemlaid.live |
| Type | Scam, phishing, adware |
| Operation | Claims that the user has been selected for a free gift; those who proceed to reclaim the alleged gift are asked to provide personal details |
| Distribution | Adware, redirects from other websites, malicious links |
| Dangers | The objective of gift scams is typically to steal personal user information, but scammers might also lead users to harmful or inaccurate websites. This can result in privacy risks, virus infections, and financial losses |
| Removal | To remove unwanted apps manually, you can follow our removal guide below. If the unwanted ads and other disruptive behavior do not stop, you should scan your computer with SpyHunter 5Combo Cleaner security software and delete all threats automatically |
| Tips | FortectIntego can help you when dealing with leftover adware files, for example, you can get rid of various browser trackers and fix system damage automatically |
Checking the device for infections
People rarely visit scam websites like Skithemlaid.live intentionally; however, some users take risks by exploring torrent sites, unauthorized video converters, and other potentially hazardous online locations. These sites are often riddled with malicious scripts and booby-trapped links, which can divert users from their intended destinations. This is a primary reason for unwanted redirections scam websites.
In addition to the dangers posed by these websites, adware could also be responsible for redirects to suspicious sites and an increase in the number of ads encountered while browsing the internet. Adware can infiltrate your system through deceptive software bundling, malicious downloads, or compromised websites, making it crucial to remain vigilant when installing new software or clicking on links.
To ensure your system is secure and free from adware and malware, it's essential to scan it with a reputable anti-malware tool, such as SpyHunter 5Combo Cleaner, Malwarebytes, or another trustworthy program. Regular scanning and updating of your antivirus software can significantly reduce the risk of inadvertently visiting scam sites like Skithemlaid.live and safeguard your device from potential threats.
Another good practice is removing cached data from your local device to ensure that no cookies or other trackers from these malicious websites remain. To quickly and easily delete this data, you can use the PC repair and maintenance utility FortectIntego, although manual steps are also available below.
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
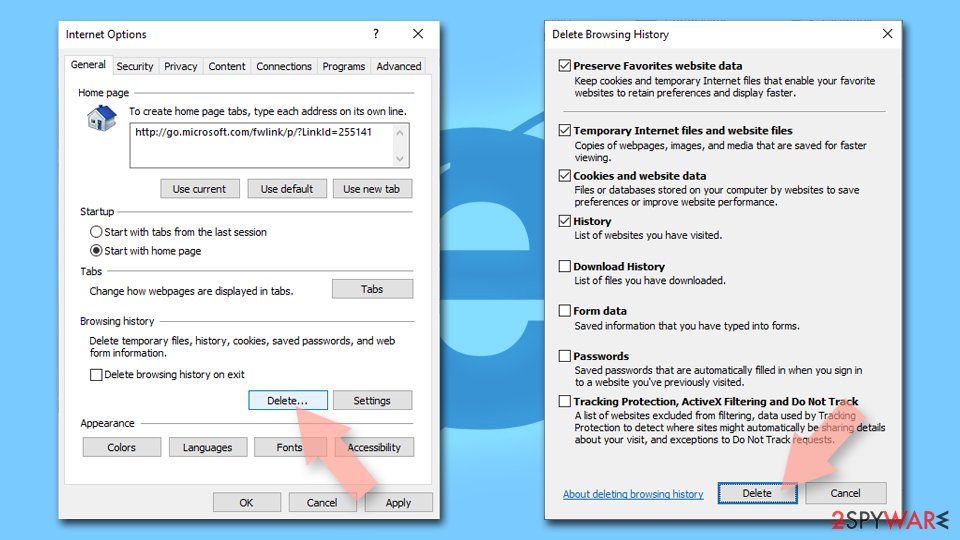
Internet Explorer
- Press on the Gear icon and select Internet Options.
- Under Browsing history, click Delete…
- Select relevant fields and press Delete.
![Clear temporary files from Internet Explorer Clear temporary files from Internet Explorer]()
Online fraud is a threat to regular computer users
Online fraud is a significant threat to internet users worldwide, posing a danger not only to their financial well-being but also to their personal information and privacy. One prevalent form of online fraud is the use of fake giveaways and similar tactics designed to exploit unsuspecting users. These schemes lure people into believing they have a chance to win valuable prizes, discounts, or cash rewards, only to end up losing substantial amounts of money or revealing sensitive data that can be misused later.
The success of fake giveaways and other online scams lies in their ability to appeal to human emotions such as greed, curiosity, or the desire for instant gratification. Scammers often create convincing and professional-looking websites, emails, or social media posts to gain the trust of potential victims. They employ urgency and scarcity tactics to pressure users into taking immediate action, leaving little time for critical thinking or verification.
Once victims are drawn in, they may be asked to make an upfront payment, provide their banking details, or share personal information under the guise of claiming a prize. In many cases, these scams can result in thousands of dollars in financial loss or the theft of valuable personal data, which may later be used for identity theft, financial fraud, or targeted phishing attacks.
The consequences of falling for online fraud can be devastating. Besides the financial losses, victims may experience emotional distress, a sense of betrayal, and a loss of trust in online interactions. Moreover, the disclosure of personal information can have long-lasting repercussions as it may be sold to other criminals or used for additional malicious activities.
How to protect yourself from scams
Skithemlaid.live is a notorious scam site that capitalizes on the allure of fake giveaways to deceive unsuspecting users. To safeguard yourself from falling prey to such scams, consider adopting the following precautionary measures:
- Authenticate the source: Be cautious if the giveaway is not featured on an official website or verified social media account.
- Look for contact details: Genuine giveaways typically provide contact information, like an email address or phone number. Before participating, reach out to the organizer to confirm the giveaway's legitimacy.
- Investigate the company or organization: Ascertain that the entity hosting the giveaway is a reputable and established business.
- Guard your personal information: Exercise caution when sharing sensitive details such as your full name, address, phone number, or credit card information, which can be exploited for identity theft.
- Avoid dubious links: If the giveaway necessitates clicking on a link, verify its authenticity and ensure it doesn't redirect to a harmful website.
By adhering to these guidelines, you can bolster your defenses against online fraud. If you suspect you've fallen victim to a scam, notify the authorities as soon as possible. Acting promptly increases the likelihood of recovering any stolen funds or items. Don't let fake giveaways deceive you; take proactive steps to protect yourself from scams like Skithemlaid.live.
How to prevent from getting adware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.