Special-offers-for.me ads (spam) - Free Instructions
Special-offers-for.me ads Removal Guide
What is Special-offers-for.me ads?
Special-offers-for.me is a deceptive website that causes ad spam
Special-offers-for.me does not offer anything special to users. Instead, it sends ads straight to users' screens which can lead to dangerous sites and bring many problems. People definitely do not find this website in their search results. The only way users end up on it is by clicking on deceptive ads, which cause redirects. These redirect-causing advertisements are not found on legitimate and trustworthy websites. Usually, they are placed on sites involved in illegal activity, such as illegal streaming platforms.[1]
You are probably curious what is the purpose of such websites. The reason behind it is simple – it brings money to creators. Imagine it this way: Special-offers-for.me has a way for advertisers to reach more eyes. In this case, it is by push notification feature on browsers. Because of pushing other content through their domain, the advertisers pay a fee to the website for every click generated because of their help.
This is an amazing opportunity for someone to sell more products and services and for others to earn some money on the side. The problem is, this website is not upfront about it and uses social engineering tactics to trick people into agreeing to receive advertisements. Besides, the developers do not care about the safety of users, so they do not filter the contents that go through them.
| NAME | Special-offers-for.me |
| TYPE | Push notification spam; adware |
| SYMPTOMS | Pop-up ads, banners appear on the screen even when the browser is closed |
| DISTRIBUTION | Freeware installations; shady websites; deceptive ads |
| DANGERS | Deceptive advertisements can lead to dangerous websites where users are at risk of giving away their personal information or downloading PUPs and malicious software |
| ELIMINATION | Remove website permissions via browser settings |
| FURTHER STEPS | Use FortectIntego for remediation, fix any damage left after removal |
Methods tricksters thought of to make money from you
There are thousands of websites just like this one. Some of them become inaccessible after detection, but new ones take their place. The reason for that is they are so easy to recreate because individuals responsible use a couple of different templates that work for them. These do not require much time as they are often copied and reused.
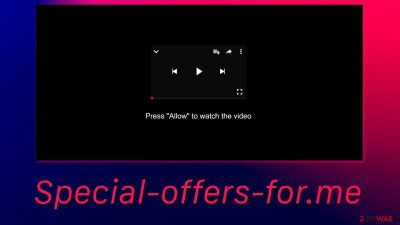
Usually, they try to look like nothing out of the ordinary by mimicking familiar tasks that users have to complete on the internet. These include captcha verifications which means pressing a button to confirm that you are not a robot and supposedly pressing the button to let the website provide users with what they want. This could be a movie people were looking to watch online or download. The website asks them to press the “Allow” button.
Probably the developers are hoping that those who rush and cannot contain their excitement will just click without reading the window or will not understand what allowing notifications means. After clicking the button, users, of course, do not receive what they were looking for. The most probable thing that happens is nothing, or they keep getting redirected to other bogus sites.
By being careless and just clicking buttons, users can infect themselves with many different websites that cause spam.
Scammers advertise too
Yes, they do. And after allowing notifications from a page such as Special-offers-for.me, you are susceptible to their manipulation that preys on human vulnerabilities. The most important thing is not to believe everything you see on the internet. If it is too good to be true – it most likely is. If someone is warning you about a threat that needs immediate action to download some tool that is supposed to help – stop. This is not a legitimate warning. Random websites cannot scan your system and decide that you are infected. Never download any software by a warning that popped up out of nowhere.
Pop-ups suggesting completing a survey to receive money or something else is fake. Making money is never easy, and there is no magic method. By the way, Google or Apple does not pick random visitors to receive prizes, so these are also ads created by scammers in order to lure out your personal information or get you to download malicious software.
If you have received pop-ups on your screen from this website, that means you were fooled. If you have pressed the accept button yourself and this website was not added by a potentially unwanted program,[2] it is your lucky day because the removal process should be easy and quick by following our step-by-step instructions:
Google Chrome (desktop):
- Open Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
![Stop notifications on Chrome PC 1 Stop notifications on Chrome PC 1]()
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Google Chrome (Android):
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).
![Stop notifications on Chrome Android Stop notifications on Chrome Android]()
Mozilla Firefox:
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click Settings button next to it.
![Stop notifications on Mozilla Firefox 1 Stop notifications on Mozilla Firefox 1]()
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
Safari:
- Click on Safari > Preferences…
- Go to Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
MS Edge:
- Open Microsoft Edge, and click the Settings and more button (three horizontal dots) at the top-right of the window.
- Select Settings and then go to Advanced.
- Under Website permissions, pick Manage permissions and select the URL in question.
![Stop notifications on Edge 1 Stop notifications on Edge 1]()
- Toggle the switch to the left to turn notifications off on Microsoft Edge.
![Stop notifications on Edge 2 Stop notifications on Edge 2]()
MS Edge (Chromium):
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.
![Stop notifications on Edge Chromium Stop notifications on Edge Chromium]()
Internet Explorer:
- Open Internet Explorer, and click on the Gear icon at the top-right on the window.
- Select Internet options and go to Privacy tab.
- In the Pop-up Blocker section, click on Settings.
- Locate web address in question under Allowed sites and pick Remove.
![Stop notifications on Internet Explorer Stop notifications on Internet Explorer]()
Second removal option
If the above removal method did not work, you might have a PUP installed. Freeware installations are the most common cause for this as the websites that distribute them use software bundling[3] to spread PUAs. Most people rush through the installation process, so they miss it. It is important to check if there are no additional programs included as a package when you download something for free.
If it is a program operating in the background without your knowledge, you will probably want to use anti-malware tools like SpyHunter 5Combo Cleaner and Malwarebytes to scan your system. It can be difficult to determine which program is responsible for unwanted behavior by yourself. Professional security tools will do this automatically and prevent such infections in the future. If you still want to proceed with the manual removal, you can look for the instructions below for Windows and macOS operating systems.
After you have successfully stopped the spam from coming, you can use FortectIntego maintenance tool to clear your browsers for better performance and privacy concerns.
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.
![Uninstall from Windows 7/XP Uninstall from Windows 7/XP]()
- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
For macOS users:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)
![Uninstall from Mac 1 Uninstall from Mac 1]()
To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
![Uninstall from Mac 2 Uninstall from Mac 2]()
How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Eden Rothstein. Illegal streaming websites spike in popularity. EagleEye. Entertainment News.
- ^ Potentially Unwanted Program (PUP. Techopedia. Dictionary. Cybersecurity.
- ^ Will Dormann. Bundled Software and Attack Surface. Carnegie Mellon University. Blog.















