Speed Dial Search browser hijacker (virus) - Free Instructions
Speed Dial Search browser hijacker Removal Guide
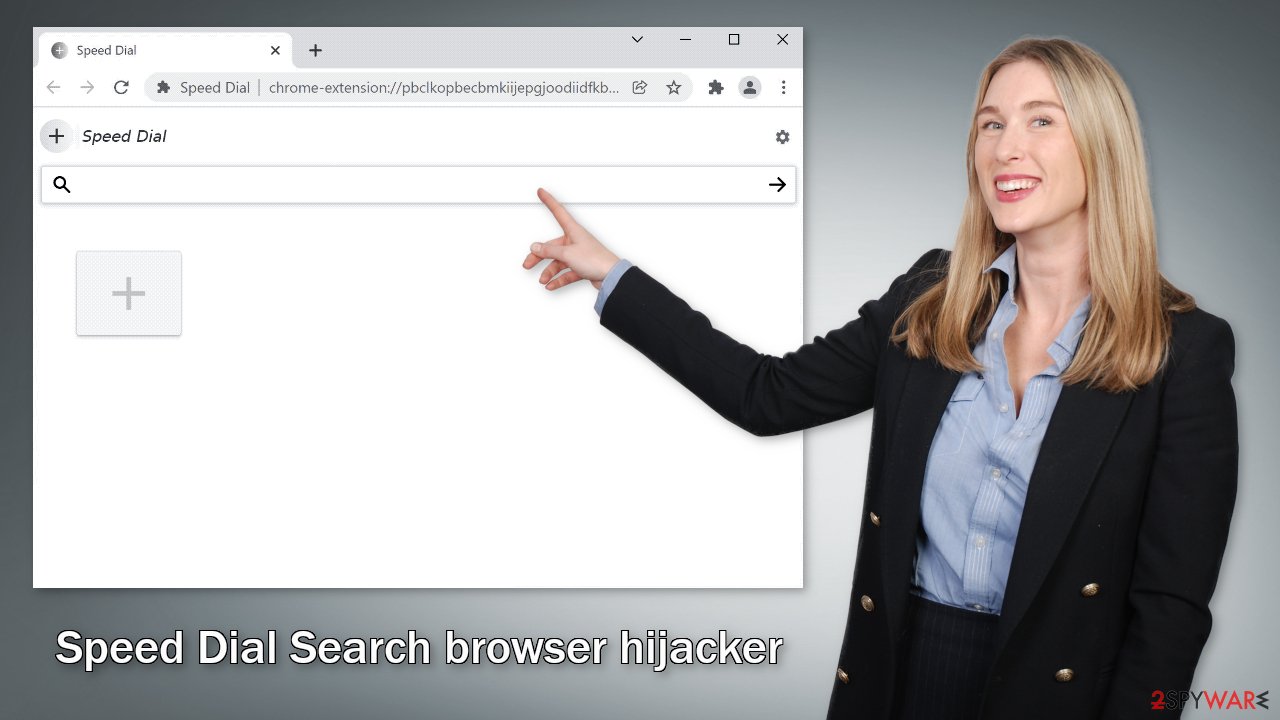
What is Speed Dial Search browser hijacker?
Speed Dial Search hijacks the browser to monetize and monitor user activity

Speed Dial Search is classified as a browser hijacker because it can change the main settings, like the homepage, new tab address, and search engine. It takes over the browsing experience by forcing users to search only through selected channels. This introduces many user privacy and security concerns.
Being in charge of the main settings gives the opportunity for browser hijackers to lead users to dangerous websites that could trick them into providing their personal information, download PUPs (potentially unwanted programs),[1] and malware. Web-based apps can start displaying ads, injecting promotional links in the search results, and promoting misinformation with fake search engines.
The extension was recorded redirecting users' queries through addonsearch.net to Yahoo. Even though Yahoo is a well-known and legitimate engine, a lot of times fraudsters add searches that are malicious and do not provide accurate results. If you experience such symptoms you should read our guide to learn more about infection methods, and the removal process.
| NAME | Speed Dial Search |
| TYPE | Browser hijacker; potentially unwanted program |
| SYMPTOMS | The main settings of the browser get changed, like the homepage, new tab address, and search engine |
| DISTRIBUTION | Shady websites, deceptive ads, software bundling |
| DANGERS | The extension may lead to dangerous websites; display misinformation, inaccurate search results; track browsing activities |
| ELIMINATION | Remove the extension by going to your browser settings |
| FURTHER STEPS | Use FortectIntego to fix any remaining damage and optimize the machine |
Distribution methods
Users usually infect themselves with browser hijackers like Speed Dial Search by browsing through shady websites that are full of deceptive ads and sneaky redirects. Crooks sometimes even create dedicated promotional websites for these browser plugins that use social engineering to convince users to download them.
You may see that often fraudsters try to make it look like the extension is recommended by Chrome or created in collaboration with a well-known company like Google. They might also write about all the non-existent functions to make it look very useful and needed.
You should never download plugins from random pages. Use official web stores or developer websites because it is the safest way you can get them. Add-ons that get listed on web stores go through a lengthy review process. However, that does not mean that you do not need to do any research.
You should always make sure that apps are safe to install and read the reviews, look at the ratings, and how many users they have. You are much better off choosing popular plugins that have plenty of feedback. You will often find that if you enter the name of a hijacker into the search, not many results pop up.
That being said, not being careful while surfing the web is not the only way users get their browsers hijacked. The symptoms can also be caused by a PUA hiding in the system. Such apps sneak into the system as bundled software from freeware[2] distribution platforms, so if you have installed anything recently, there is a big chance you may have it.
Remove the unwanted extension
You can remove browser add-ons by going to your settings. Find the list of extensions installed in your browser and remove Speed Dial Search. We show how to do that in the guide below:
If you want to avoid PUAs during the installation, always choose “Custom” or “Advanced” methods, read the Privacy Policy and Terms of Use to find out what information will be collected and what the application will be allowed to do in your machine. The most important part is to check the file list and untick the boxes next to any items that you think are suspicious or unrelated.
Keep in mind that adware[4] and other potentially unwanted programs are mostly distributed through freeware, torrent, and peer-to-peer file-sharing platforms. By getting software the legal way, you will most definitely slim your chances of getting infected. Even though it might get costly, you will most likely save in the long run by maintaining a healthy system.
How to prevent from getting browser hijacker
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Chris Hoffman. PUPs Explained: What is a “Potentially Unwanted Program”?. HowToGeek. Technology Magazine.
- ^ Freeware. Wikipedia. The free encyclopedia.
- ^ What are Cookies?. Kaspersky. Home Security.
- ^ Adware. Malwarebytes. Cybersecurity Basics.










