Tap togo browser hijacker (virus) - Free Guide
Tap togo browser hijacker Removal Guide
What is Tap togo browser hijacker?
Tap togo is a hijacker that takes over the browsing experience by changing the main settings
Tap togo is a browser hijacker that can change the main settings, like the homepage, new tab address, and search engine. It is a useless extension that monetizes user activity by collecting data, and causing commercial content, like pop-ups, banners, and redirects to appear.
Crooks may use rogue advertising networks[1] that place ads leading to dangerous websites. As a result, people can end up on scam pages that try to trick them into providing personal information, downloading PUPs (potentially unwanted programs),[2] and even malware.
| NAME | Tap togo |
| TYPE | Browser hijacker; potentially unwanted program |
| SYMPTOMS | The main settings of the browser get changed, like the homepage, new tab address, and search engine |
| DISTRIBUTION | Shady websites, deceptive ads, software bundling |
| DANGERS | The extension may lead to dangerous websites; display misinformation, and inaccurate search results; track browsing, and collect data |
| ELIMINATION | Remove the extension by going to your browser settings |
| FURTHER STEPS | Use FortectIntego to fix any remaining damage and optimize the machine |
Distribution methods
Tap togo browser extension was discovered through fake download pages and other bogus sites that use social engineering[3] methods. As you can see in the picture below, the page tries to convince people to install a “recommended” extension. There is no name of the plugin and no information on what it is for.
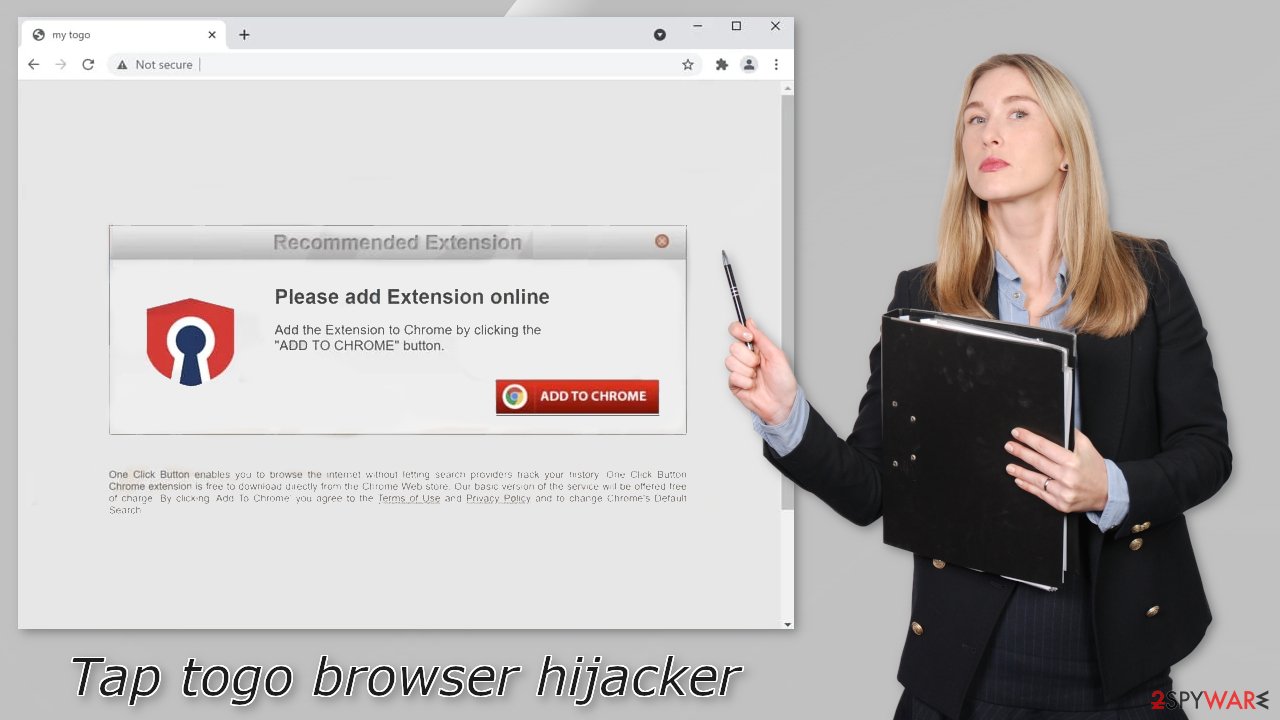
You should never download anything through such pages as they are untrustworthy. We always recommend our readers to use only official web stores. Apps that get listed there, go through an extensive review process. However, you should still do your research – read the reviews, look at the ratings and the number of users. It is best to choose those extensions that have plenty of positive feedback and thousands of users.
You should also stay away from freeware[4] distribution, peer-to-peer file-sharing platforms, and torrent websites as they are unregulated. You can never know if the software you want to install is safe to use. Fraudsters can disguise adware as “handy” tools so users would not suspect a thing.
Keep your privacy
With a browser hijacker users not only have to get used to the new layout but also be worried about their privacy. Extensions can track the user activity – IP address, geolocation, websites they visit, links they click on, and things they purchase online.
This can all be done with the help of tracking technologies like cookies. They can later be sold to advertising networks or other third parties. That is why security experts recommend clearing them regularly. Because most of the time people forget about this task or do not care about it, there is a maintenance tool, like FortectIntego that can do it automatically.
This powerful software can clear your browsers with a click of a button, as well as fix various system errors, corrupted files, and registry issues which is especially helpful after a virus infection.
Remove the unwanted extension
You can remove browser add-ons by going to your settings. Find the list of extensions installed in your browser and remove the Tap togo. Follow the guide below for instructions:
How to prevent from getting browser hijacker
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Zeljka Zorz. How does a rogue ad network function?. Helpnetsecurity. IT Insights.
- ^ Chris Hoffman. PUPs Explained: What is a “Potentially Unwanted Program”?. Howtogeek. Technology Magazine.
- ^ Cynthia Gonzalez. Top 8 Social Engineering Techniques and How to Prevent Them [2022]. Exabeam. Information Security.
- ^ Tim Fisher. What Is Freeware?. Lifewire. Internet, Networking and Security Blog.










