Tarmac virus (Removal Guide) - updated Nov 2019
Tarmac virus Removal Guide
What is Tarmac virus?
Tarmac virus is a password-stealing trojan virus that gets installed via fake Adobe Flash Player upgrades on macOS

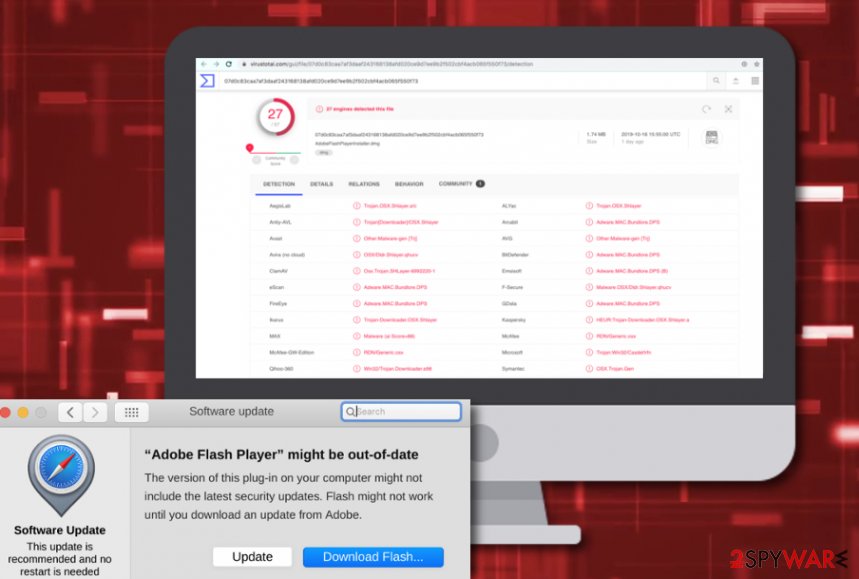
Tarmac virus (aka OSX/Tarmac) is a trojan virus that is delivered via OSX/Shlayer.D malware that is a recent version of OSX/Shlayer.[1] According to the latest research,[2] Tarmac virus is brought to macOS machines via fake Adobe Flash Player upgrades that distribute OSX/Shlayer.D. The trojan appears on the system as the 1.74 MB AdobeFlashPlayerInstaller.dmg file that is encrypted by using the SHA-256 algorithm. Nevertheless, the fake update comes signed by a non-existing person named Fajar Budiato and misuses an original Apple developer certificate coded 2L27TJZBZM. In addition, 27 AV engines find the fake Flash Player update file malicious.[3]
| Name | Tarmac virus |
|---|---|
| Also known | OSX/Tarmac |
| Type | Malware |
| Sub-type | Trojan |
| Related file | This malicious product appears on the system through the AdobeFlashPlayerInstaller.dmg file |
| OS-based | Even though Windows OS is more commonly targeted by malware developers, this time hackers decided to release a trojan that infects macOS systems |
| Distribution | The trojan virus is delivered via OSX/Shlayer.D malware that comes from the OSX/Shlayer.D family and is installed via fake Flash Player updates |
| Operations | The malware might be capable of many things such as inserting other viruses, stealing private data, mining cryptocurrency, opening potentially infectious websites, etc. |
| Removal | First, scan the system with powerful anti-virus to detect and get rid of the trojan horse. Additionally, use FortectIntego to find all modified elements and restore their health |
Tarmac virus gets downloaded to a macOS system once OSX/Shlayer.D malware connects to a C&C server. Afterward, the malicious installation process begins and executes the trojan through this directory: Player.app/Contents/Resources/Player.app/Contents/MacOS/CB61E0A8408E by using administrative rights.
Continuously, Tarmac virus tries to get the victim to type in the administrator's password and if that is done, a fake Adobe Flash Player installer is displayed via WebView. Keep in mind that the trojan virus would be able to access the macOS nevermind if the password has been entered by the user himself or not. Tarmac trojan is coded to steal passwords, other login details, and supposedly storing the data on some type of remote server.

Furthermore, there are many dangerous tasks that can be carried by Tarmac virus later on. This malware might slightly increase the power of your CPU and GPU, damage some files or software that is found on your macOS, install other viruses and infections, run multiple damaging processes in the background.
Additionally, Tarmac virus might introduce itself by harvesting the credentials and personal data that you have stored on your computer system. Afterward, the information might be used for identity theft or you might discover some private detail put up for sale on the Dark Web as this technique remains to be a great income source for some hackers.
Nevertheless, Tarmac virus might get hold of your Apple ID passwords, take screenshots, gain access to your camera or microphone, forcibly open browser windows that will prompt you to download some camouflaged products that are truly hidden malware. Also, some trojans support cryptocurrency mining activity and run a specific module to collect Bitcoin, Lite coin or another type of digital currency on the infected PC by overusing its resources, including the CPU power.
If you ever spot this trojan in your macOS, you have to react immediately and remove Tarmac virus from the computer as soon as possible. If you do not really know if the malware has been hidden on your system, you can launch a thorough checkup with FortectIntego, SpyHunter 5Combo Cleaner or similar software to find out all the issues.
Tarmac removal should be performed only by using automatic removal software, otherwise, you can cause severe to your machine or its software. Additionally, you take some risks of missing crucial infection sources. If any type of malicious component remains on the system, the trojan virus can repeatedly appear on your computer after the next startup process.
Distribution tactics of trojan viruses
Trojan infections can be easily distributed through potentially unwanted programs such as adware. These odd apps might provide you with fake Adobe Flash Player installers that are known to include malware very often. Criminals like to camouflage their malware behind different app upgrades to give it a look of legitimacy.
You should keep all of your software regularly updated and always check on official reports about recently released updates. Continuously, include a strong antimalware program on your computer so that you will be informed if some type of camouflaged malware tries to sneak into your system unnoticed.
However, there are more ways of how trojan viruses might end up on your computer. These cyberthreats can be delivered through email spam that pretends to come from a reliable banking or healthcare-related organization. The malicious payload often comes inserted in an executable or word file that is attached to the bogus email message.
Last but not least, you should be aware of p2p sources such as The Pirate Bay or eMule as here you can get various cracked software and movies for free. Some criminals are likely to misuse these websites as they lack the required security.
Elimination guidelines for Tarmac virus on macOS
Do NOT try to remove Tarmac virus or any other trojan horse, ransomware or a similar complicated threat on your own. There are numerous malicious components that can be spread all over the computer system. If you mix such a component with the legit file, you can run into more problems.
To get rid of infectious components, we recommend using SpyHunter 5Combo Cleaner or Malwarebytes. Make sure you update these apps before a scan to see if they can find the threat completely. To complete the Tarmac removal process, employ FortectIntego. Once the software finds virus damage for you you can continue with the automatical elimination.
According to experts from LosVirus.es,[4] malware such as Tarmac trojan might be able to boot up automatically during every new computer startup process. This is the main reason why it is so important to eliminate all virus-related content at once. If you leave at least one infectious object, you might experience the same malware attack once you boot your PC again.
Getting rid of Tarmac virus. Follow these steps
Manual removal using Safe Mode
Disable the malware by rebooting to Safe Mode with Networking. Use the following guide for that:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Tarmac using System Restore
To get a chance to run anti-virus, perform System Restore on your computer:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Tarmac. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Tarmac and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting mac viruses
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Joshua Long. OSX/Shlayer: New Mac malware comes out of its shell. Intego.com. About Mac security.
- ^ Taha Karim. OSX/Shlayer new Shurprise.. unveiling OSX/Tarmac. Confiant Blog. News.
- ^ 27 engines detected this file. AdobeFlashPlayerInstaller.dmg. Virus Total. File information.
- ^ LosVirus.es. LosVirus. Cybersecurity news source.





















