Tempo Search browser hijacker (fake) - Free Guide
Tempo Search browser hijacker Removal Guide
What is Tempo Search browser hijacker?
Tempo Search says that it provides the best results from the entire Internet

Tempo Search is a browser extension or a potentially unwanted program that has hijacking capabilities. It changes the most important browser settings like the homepage, new tab address, and implements a different search engine. Even though the creators claim that they provide “The best results from the entire Internet”, that is not true, and there are many much better engines so you definitely do not need it.
When the extension is added to the browser, it can track users' browsing activity like the pages they visit, links they click on, purchases they make, and more, so it is definitely not with it to trust shady individuals with this information. The data can later be sold to advertising networks that use it to further personalize ads shown to users and make them more likely to spend money through their referral links.
This add-on is created for the sole purpose of generating revenue from PPC advertising.[1] So while the hijacker is on the browser, people can experience an increased amount of commercial content like banners, pop-ups, surveys, and others. The developers of the add-on do not care about users' security or privacy so they do not filter what ads they show. Users might see some common scams appear like prize giveaways, fake software updates, etc.
| NAME | Tempo Search |
| TYPE | Browser hijacker; potentially unwanted program |
| SYMPTOMS | An extension is added to the browser; homepage and new tab address altered; a different search engine is implemented; sponsored links displayed in the results |
| DISTRIBUTION | Shady websites, deceptive ads, freeware installations |
| DANGERS | Inaccurate search results, sponsored links can lead to dangerous pages that want to get users personal information |
| ELIMINATION | You can remove an extension via browser settings or by deploying professional security software |
| FURTHER STEPS | After elimination is complete, clean your web browsers and repair system files. You can do that automatically with FortectIntego |
A closer look into the browser hijacker
It is rare for users to find these kinds of apps on their own. Most of the time they are spread on questionable websites full of deceptive ads[2] and sneaky redirects. It is common for users to add these accidentally without even noticing. Most people think that they care a lot about online safety, but when it actually comes to preserving it, few take precautionary steps.
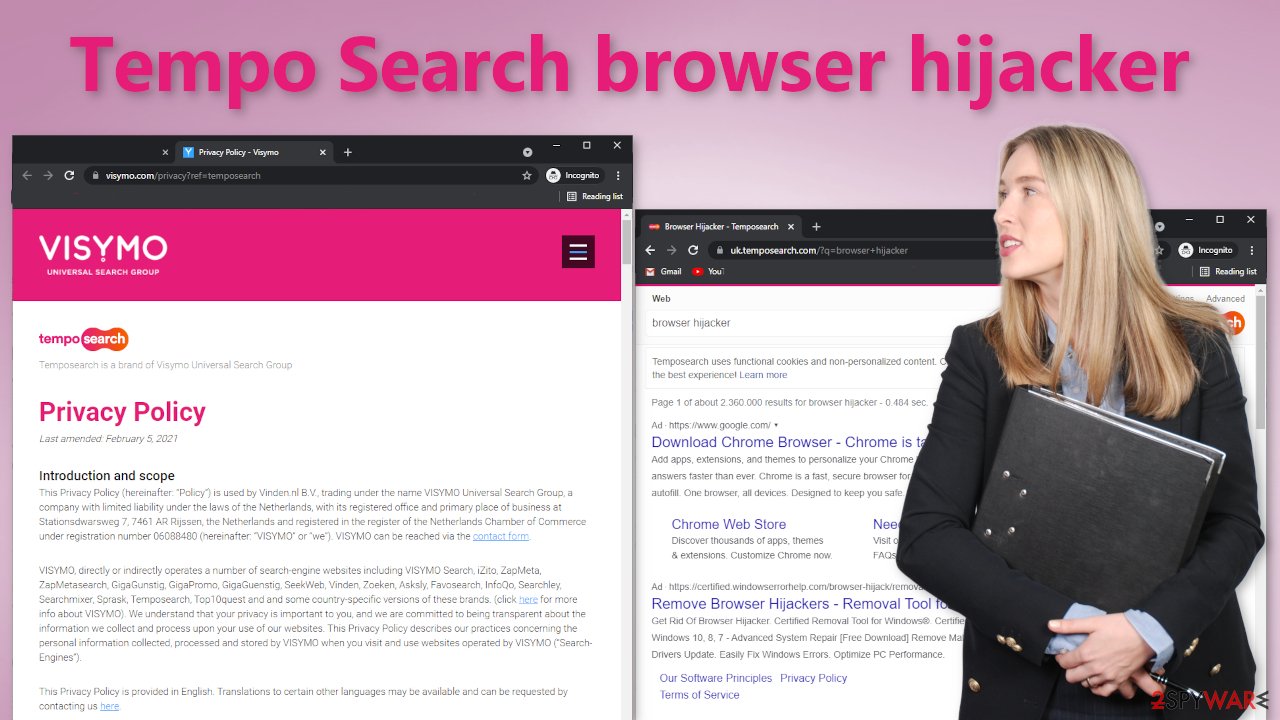
As we mentioned before, the add-on changes various settings. For example, users have their homepage set to uk.temposearch.com and are forced to search through a different engine. This way the developers can see all your search queries, and the links you click on. They create a user profile and can later provide it to third parties.
Usually, hijackers do not have their own search engines, they just implement an already existing one like Bing to just make it functional and serve its purpose, but this one is different, and the creators put in the effort to create their own engine. It does not appear to be unique in any way and does not provide any significant benefits to make it worth keeping.
If you go to the Privacy Policy of Tempo Search you will find an extensive list of things that it keeps track of. Some of those include your IP address and Internet usage data. The add-on can also gather various information with the help of cookies.[3] That is why we suggest having an optimization tool like FortectIntego in your machine that can clear your browsers automatically. Besides that, the application can fix corrupted files and serious system errors so it has a lot of benefits.
How to get rid of intruders from browsers?
Generally, browser extensions are created to provide users some benefits, like mask the location, block ads, and suspicious links, or automatically find discount coupons while shopping online. People add them when they see promotions and good reviews.
You can remove browser add-ons by going to your settings. Find the list of extensions installed in your browser and remove any suspicious ones. We show how to do that in the guide below:
How to prevent from getting browser hijacker
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ What Is PPC? Learn the Basics of Pay-Per-Click (PPC) Marketing. WordStream. Advertising Solutions.
- ^ Ben Stegner. How to Avoid Fake Ads Disguised as Fake Download Links. MakeUseOf. IT Tips.
- ^ What are Cookies?. Kaspersky. Home Security Blog.
- ^ Potentially unwanted program. Wikipedia. The Free Encyclopedia.











