Tobepartou.com redirect (virus) - Free Guide
Tobepartou.com redirect Removal Guide
What is Tobepartou.com redirect?
Tobepartou.com is a redirect virus that you should swiftly remove
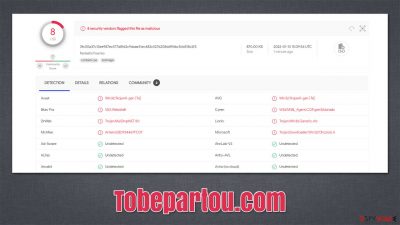
Potentially unwanted applications such as adware are relatively common, and their presence is usually considered more of a nuisance than a real threat to security and privacy. However, some symptoms might be a sign of something more sinister than usual, and Tobepartou.com redirects fall in this category. If you have experienced any suspicious activity related to it, there is likely a malicious application installed on your computer in the form of a Chrome browser extension.
In most cases, users do not see any visual changes, although the suspicious activity manifests itself in users' browsers redirecting them through the Tobepartou.com domain before reaching the destination site. This strange behavior can also be related to users being redirected to pages that they never intended to (usually scam, phishing, and similar), and their search provider might no longer be the same.
Since most people who use Chrome browsers also prefer google.com as their preferred search tool, this aspect is also altered by the infection. People reported that they are most commonly being redirected to Yahoo, Bing, or another provider instead. Search results would also no longer be generated genuinely and instead would be filled with sponsored links at the top. If clicked, these could bring to malware-laden websites.
The reason for this behavior is the “Properties” extension installed on your browser, and its elimination is not the only step you need to take in order to get rid of the infection altogether. We explain all the details related to the process below.
| Name | Tobepartou.com redirect |
|---|---|
| Type | Adware, redirect virus |
| Delivery | Software bundles, redirects from other websites, ads, malicious or repacked files |
| Symptoms | Suspicious redirects through Tobepartou.com or other websites; all the searches are redirected to an alternative provider; search results are filled with ads and sponsored links; more ads everywhere; cs_loader.exe is present on the system |
| Risks | Redirects to malicious websites can result in intrusive notifications, personal information disclosure to cybercriminals, monetary losses, installation of other potentially unwanted programs/malware |
| Elimination | For the best results, you should check for unwanted browser extensions and programs that could be installed on the system. Finally, you should scan your device with SpyHunter 5Combo Cleaner security software to ensure no malware is present |
| Additional Tips | You should remove caches and other web data after the removal of adware to prevent data tracking with the FortectIntego repair and maintenance tool. You can also repair damaged system components with it |
While most potentially unwanted applications are delivered via software bundle packages, it is not the case with this malicious extension – at least partially. Users install additional apps when they download freeware from third-party websites. The easiest way to avoid optional components is to always pick the Advanced options and remove all the offered programs and extensions.
However, everything becomes quite a bit different when users download illegal software from torrent sites, as packages from there could include all sorts of nasties, including the one that is causing these annoying Tobepartou.com redirects.
In reality, the virus is initially delivered through an ISO file which, once mounted, holds a cs_loader.exe file in it. ISO files are commonly used for pirated video games and other executable programs. If the EXE file is clicked, PowerShell is launched and special commands are automatically used, which allows the virus to download and forcefully install a browser extension under the name of “Properties” on the Google Chrome browser.
Since this happens behind users' backs, they don't even know that their browser has been hijacked by this extension. Luckily, the changes to the search settings and increased number of sponsored ads sound the alarm of many. This is actually very justified because, while the app does not directly perform very malicious actions, it might make the system vulnerable[1] to other attacks.
Thus, we recommend eliminating this infection as soon as possible. If you do this incorrectly, it might return, so we recommend you follow the steps in the below section correctly. Before you proceed with manual elimination, we recommend you perform a full system scan with SpyHunter 5Combo Cleaner, Malwarebytes, or another powerful security software.
In most cases, security software can find and remove the malicious components of the virus. However, since the main payload is disguised in an ISO file, it might not be detected,[2] so make sure you delete the original file wherever it was saved.
1. Remove the extension correctly
In order to start the Tobepartou.com removal, you need to look for the extension under the name of “Properties.” If you can't see it in the usual place in the “Extensions” section, you should access the settings section of your browser as follows:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
You should now clear your web browser's cache to make sure no malicious components remain after malware removal. This step is also recommended when removing every potentially unwanted application because it can stop cookie tracking by third parties and clearing the data would prevent various errors from occurring which might lead to session hijacking under certain circumstances
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
If you have tried to remove the “Properties” extension and failed to do so due to restrictions or it keeps returning, we recommend you reset your browser altogether. As long as you remember your Google Account (you can also use the “Forgot password” feature), all your bookmarks and saved passwords will be restored.
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.
![Reset Chrome 2 Reset Chrome 2]()
2. Get rid of the leftover files and stop the malicious scheduled task
Even after performing all the steps mentioned in the previous section, users reported that the malware managed to return, and the “Properties” extension was reinstalled. This would, in turn, return the annoying browser changes and redirect to alternative search providers. The persistence mechanisms that are used are relatively simple, however, and they can be eliminated relatively easily.
First of all, you should delete the user data within the Chrome folder for the “Properties” extension – it's located in the following directory:
C:\Users\USER\AppData\Local\Google\Chrome\User Data
Once you delete the appropriate folder, you need to get rid of the scheduled task[3] which was created by the virus. This is one of the main reasons why the malicious extension returns. Proceed with the following steps:
- Type in Task Scheduler in Windows search and hit Enter
- Click on the Task Scheduler Library and look for a task called ChromeLoader
- Right-click this task and select Delete.
How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Thomas Holt. What Are Software Vulnerabilities, and Why Are There So Many of Them?. Scientific American. Science Magazine.
- ^ 3fc00a37c13ee987ec577a8fd2c9daae31ec482c5276208ddff4bc5cb518c2f3. Virus Total. File and URL analysis.
- ^ Windows Task Scheduler. Wikipedia. The free encyclopedia.



