Trojan Woreflint (Virus Removal Instructions) - Free Guide
Trojan Woreflint Removal Guide
What is Trojan Woreflint?
Trojan Woreflint – a security threat that might be marked by your anti-malware
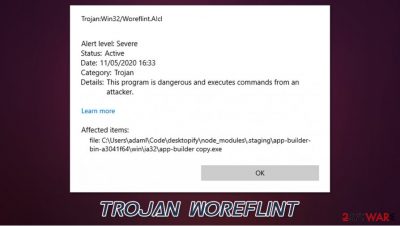
Trojan Woreflint is a malicious program that can be designed for numerous purposes. Some of its versions even represent threats such as Agent Tesla, while others can be related to browser contaminations. First spotted in early 2018, the Trojan has been detected under nine different names relating to the threat.
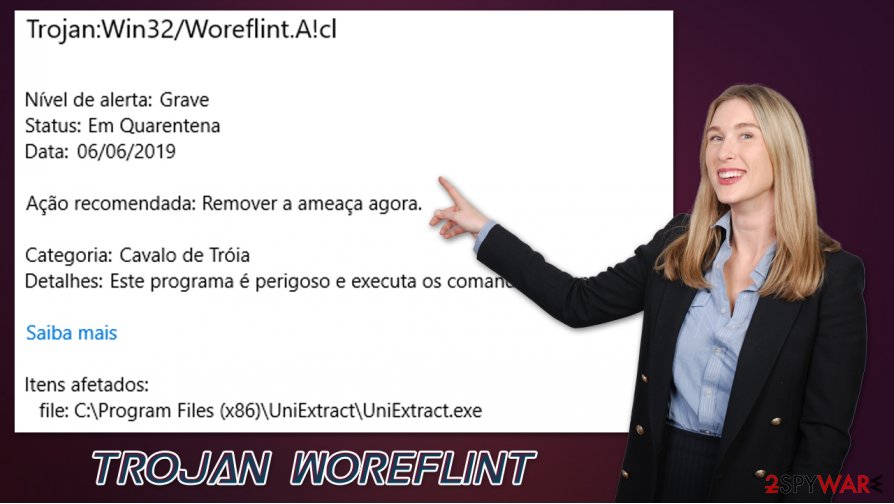
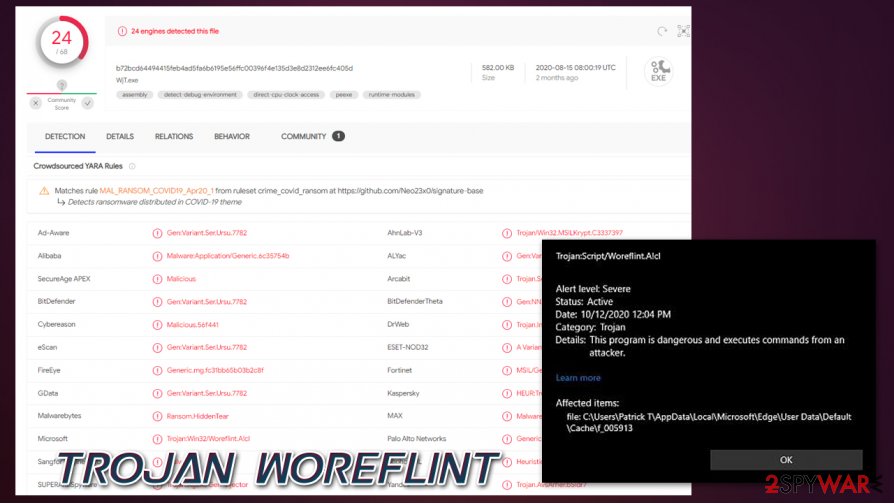
By definition, a Trojan is a type of threat installed on the machine by users who mistakenly believe that the executable file is safe to use, for example, after receiving a phishing email or when downloading an application from an insecure third-party website. Additionally, some of the Trojan versions were spotted in the web browser cache of Edge or another web browser, as users complained that Windows Defender flagged up Trojan:Script/Woreflint.A!cl there. It is also important to note that the detection name of generic, which means that some detections might be a false positive.
Regardless of which version you are dealing with – if it is not a false positive – Trojan Woreflint removal is a mandatory process to ensure that your personal information is secure and no further infections occur.
| Name | Trojan Woreflint |
|---|---|
| Type | Trojan |
| Distribution | Malicious spam emails, software cracks/keygens/loaders, pirated programs, fake updates, etc. |
| Symptoms | Anti-malware software detection popup is the only symptom you are are likely to notice |
| Dangers | Trojans can perform a variety of different functions on the system, including information theft, personal file encryption, traffic interception, proliferation of other malware, remote PC control, etc. |
| Malware removal | Perform a full system scan with powerful security software, such as SpyHunter 5Combo Cleaner |
| System fix | Malware can seriously tamper with Windows systems, causing errors, crashes, lag, and other stability issues after it is terminated. To remediate the OS and avoid its reinstallation, we recommend scanning it with the FortectIntego repair tool |
As mentioned in the introduction, Trojan Woreflint virus can represent a variety of different versions, the most commonly-encountered ones include:
- Trojan:Win32/Woreflint.A!cl
- Trojan:Script/Woreflint.A!cl
- Trojan:Win32/Woreflint.A
- Trojan:Script/Woreflint.A!rfn
- Trojan:Script/Woreflint.A!ctv
- Trojan:Win32/Woreflint!MTB
- Trojan:Win32/Woreflint.A!MTB
- Trojan:Script/Woreflint.A!MSR
- Trojan:Win32/Woreflint.AK!MTB
As evident, the main difference between these versions that a script is indicated – this is related to malicious scripts that can be encountered on various websites or after malicious executables are launched. Upon accessing a website, users might be subjected to JavaScript launched as soon as they enter. In some cases, when software vulnerabilities are not patched, Trojan Woreflint malware can be launched automatically. If you run anti-malware software, it will indicate that it stopped the threat.
The “Win32” indicates that the infection resides in a malicious program that is attempting to be launched on a Windows system. This typically occurs when users attempt to install, for example, a pirated program that has been injected with malicious code. Therefore, if such an event occurred to you, you should not hesitate and remove Trojan Woreflint virus using your security tool. In case Windows Defender is unable to delete the threat, you should employ alternative software, such as SpyHunter 5Combo Cleaner or Malwarebytes.
Some users also complained that certain games, downloaded from official sources such as Steam, might be detected as Trojan:Win32/Woreflint.A!cl. It is very unlikely that a game downloaded from an official platform would contain malicious code, so, in this case, the detection is a false positive. If you are not completely sure, you should launch a scan with an alternative security software or contact game developers/anti-malware tech support to clarify things for you.
Note: if you encounter errors, lag, BSODs, crashes, and other issues, it is likely that malware managed to penetrate some system files. In order to repair this damage, we recommend using FortectIntego – it might help you to avoid the reinstallation of a damaged operating system.
Trojans can be distributed via various means: learn to reduce the risk of infection
As mentioned previously, Trojans are not defined by their functionality but rather by methods they are distributed through. Cybercriminals are sophisticated individuals who always come up with new ways to deliver malware to users, hence infections are so prevalent. Luckily, there are several ways to reduce the risk of the infection to a minimum – here are some tips by security experts:
- Equip your system with powerful anti-malware and keep it updated at all times;
- Install Windows and other program updates regularly;
- Never allow email attachments to run a macro function on your machine;
- Do not click on links within suspicious emails – hover your mouse over to see the real destination URL;
- Use strong passwords for all your accounts;
- Do not download software cracks, keygens, loaders, or pirated program installers from torrent sites;
- Install powerful ad-block that would stop malicious scripts from being executed upon website entry.
Delete Trojan Woreflint without hesitation if it is not a false positive
When dealing with detection and Trojan Woreflint removal, it is important to note what type of actions you were performing. If you were opening an email attachment or if you were attempting to download a software crack – there is almost no doubt that the threat should be quarantined and deleted immediately.
If the pop-up came seemingly out of nowhere or during the installation of an app you know is secure, it definitively requires more investigation before you remove Trojan Woreflint. As mentioned above, you should immediately perform a full system scan with SpyHunter 5Combo Cleaner, Malwarebytes, or other alternative security tools. This should give a good idea of whether the installer is actually something you should be concerned about.
Once you remove Trojan Woreflint virus with Windows Defender or another security tool, you should also perform additional checks with the Windows repair tool FortectIntego – it should fix all the damaged Windows system files, such as registry errors.
Getting rid of Trojan Woreflint. Follow these steps
Manual removal using Safe Mode
If you are unable to delete Trojan:Win32/Woreflint.A!cl or other versions of the virus from your machine successfully, access Safe Mode with Networking and perform a full system scan from there:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Trojan Woreflint and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting trojans
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.














